Threat Intelligence Blog
Research, insights, and updates from the isMalicious team.
MCP Security Risks: Tool Poisoning, Prompt Injection, and the New AI Agent Attack Surface
Model Context Protocol integrations give agents access to tools, files, and services. That power creates new risks: tool poisoning, prompt injection, overbroad permissions, and untrusted server abuse.
LLMjacking Explained: How Attackers Abuse Cloud Credentials to Steal AI Compute
LLMjacking combines cloud credential theft with expensive AI workloads. Learn how attackers find exposed keys, abuse model APIs, hide compute costs, and how defenders can detect the pattern.
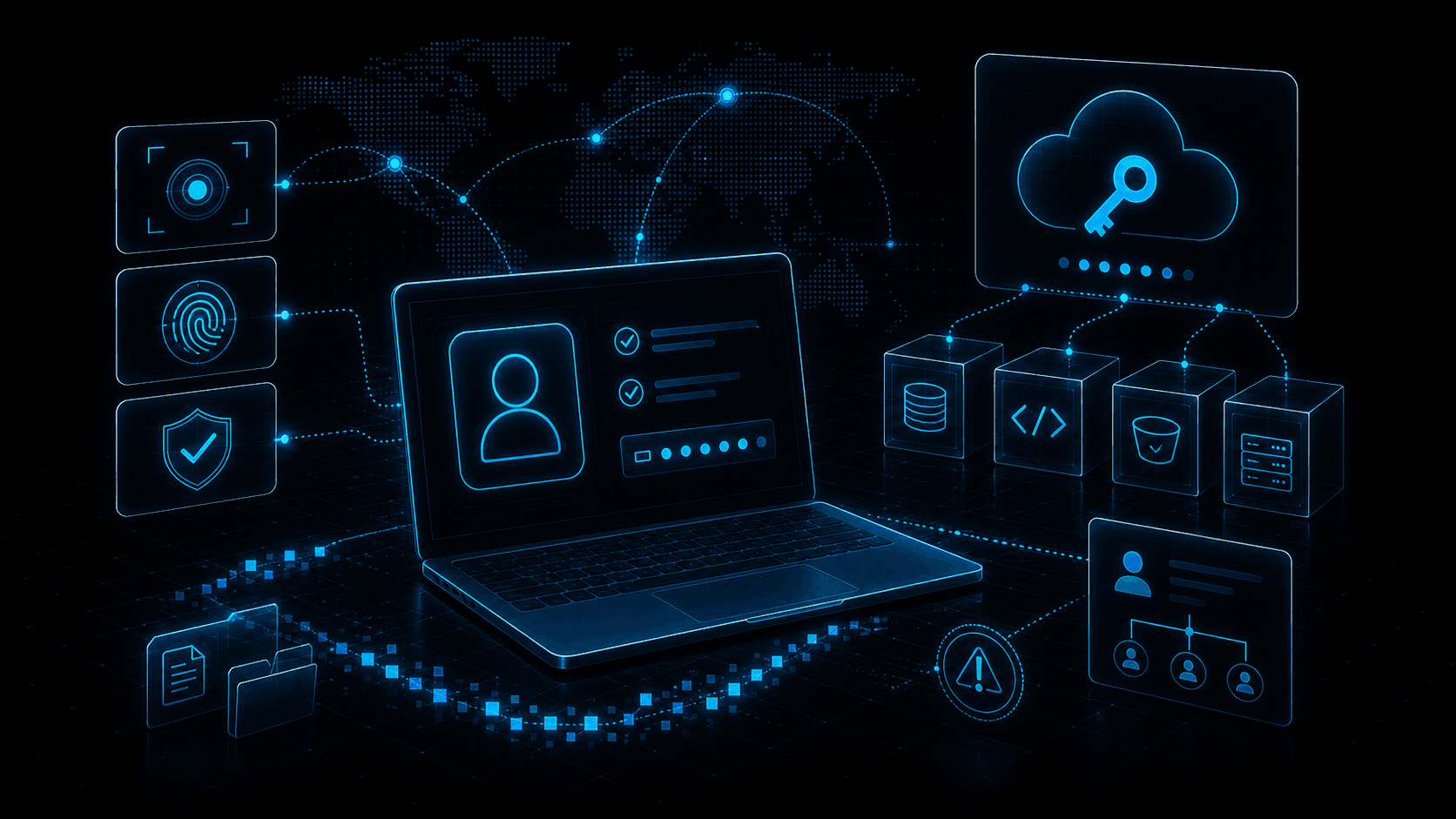
Non-Human Identity Security: API Keys, Service Accounts, and Workload Credentials in 2026
Non-human identities now outnumber users in most environments. Learn how API keys, service accounts, CI tokens, and workload credentials become attack paths and how to govern them.
OAuth Consent Phishing: Detecting Malicious App Grants Before Data Exfiltration
OAuth consent phishing tricks users into granting access instead of giving up passwords. Learn how malicious app grants work, which permissions matter, and how to detect abuse early.

Session Token Theft: Why Infostealers Bypass MFA and How Defenders Respond
Infostealers increasingly target browser cookies, session tokens, and refresh tokens. Learn why MFA is not enough, what token theft looks like, and how to detect replay.
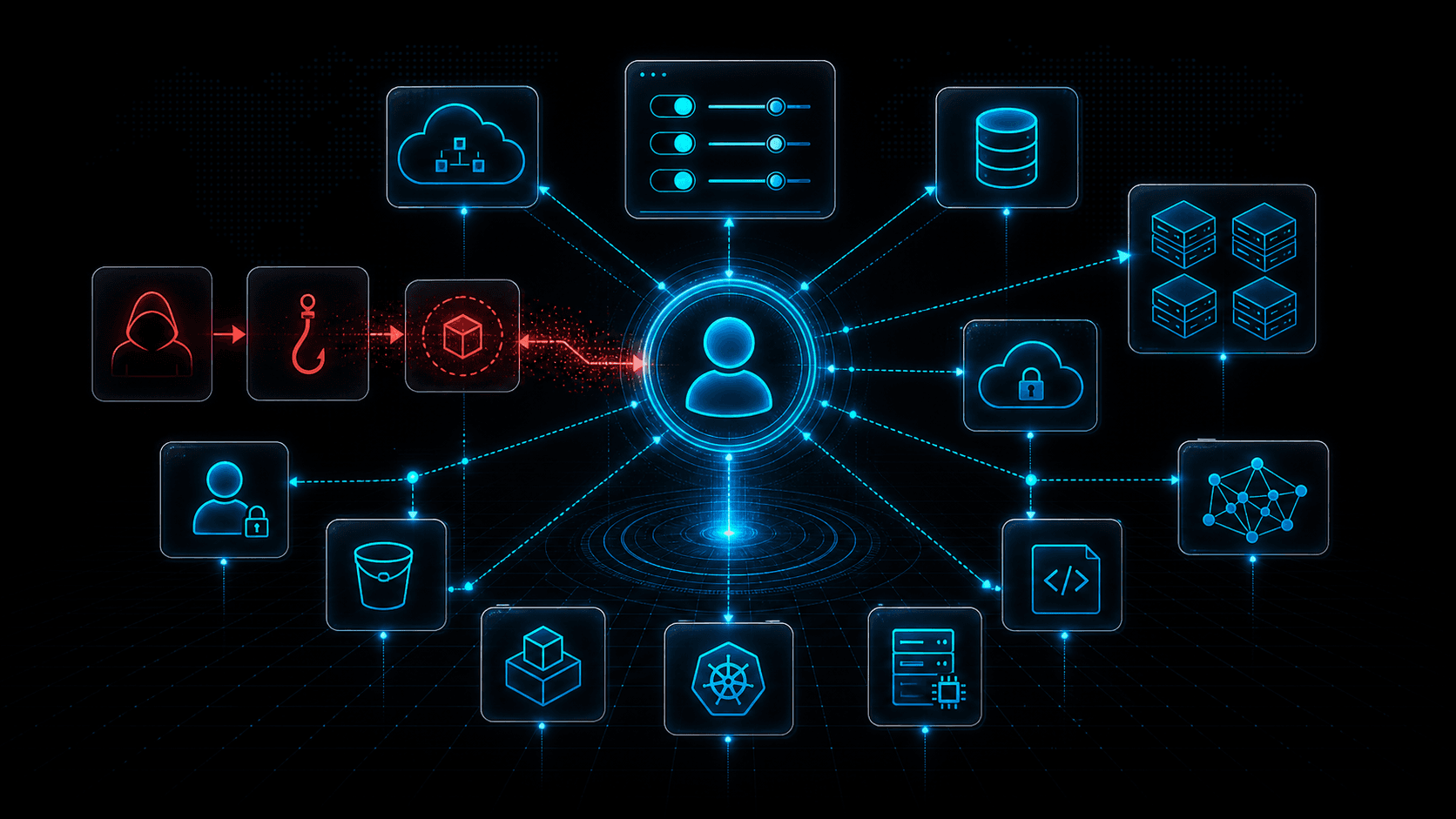
Cloud Control Plane Attacks: Why Identity Is the New Kill Chain
Cloud breaches increasingly target the control plane: identities, tokens, policies, APIs, and automation. Learn how attackers move from one credential to full cloud control.
Security LLM and Agent Workflows: When (and How) to Check Malicious Domains, IPs, and URLs Before Acting
AI assistants in SOAR, IDEs, and browser extensions can exfiltrate data or run malicious code if they fetch the wrong link. This guide gives guardrails: schema for tool calls, policy tiers, and where threat intelligence checks belong in the loop.
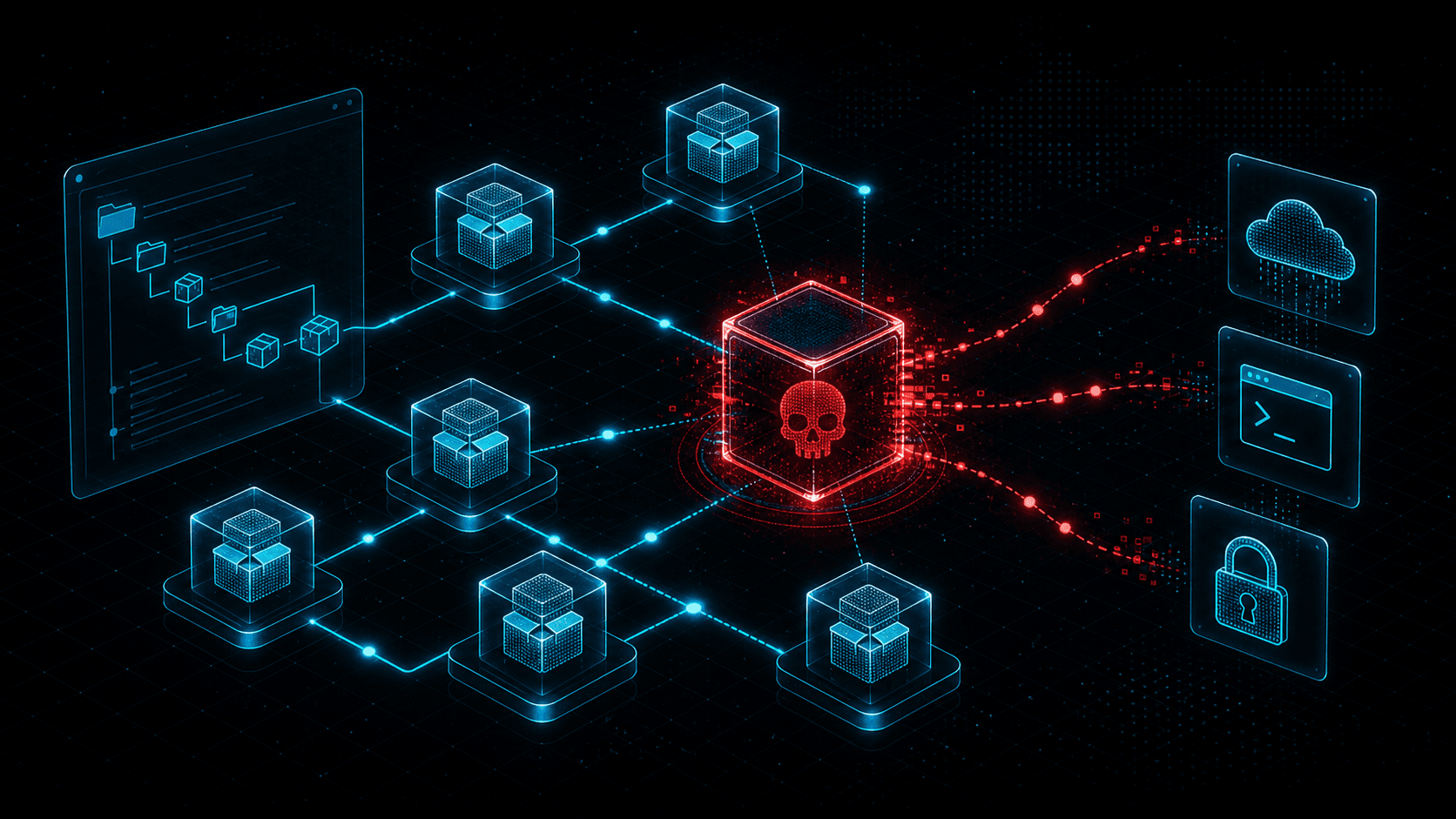
Malicious npm Packages: Detecting Open-Source Supply Chain Compromise
Malicious npm packages use typosquatting, dependency confusion, install scripts, and maintainer compromise to steal secrets and backdoor builds. Learn practical detection and response.
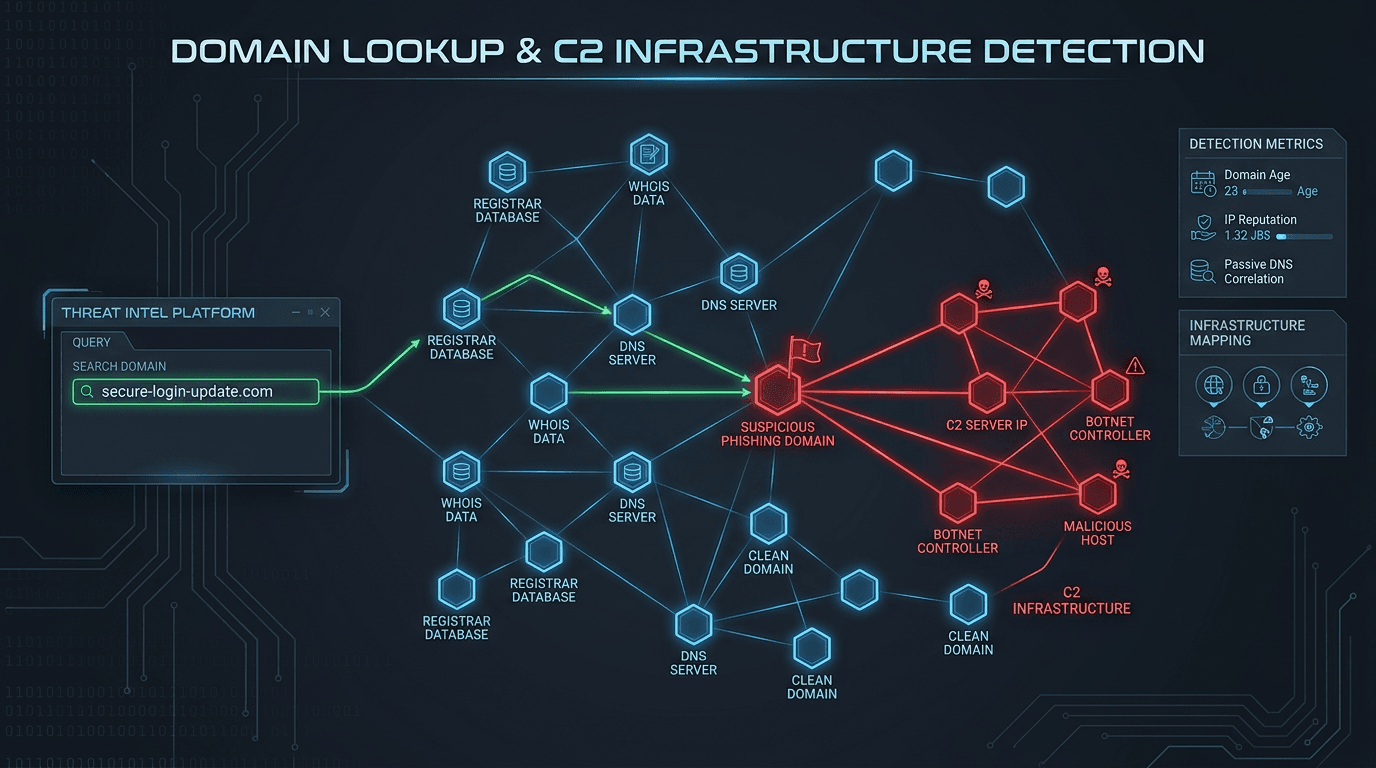
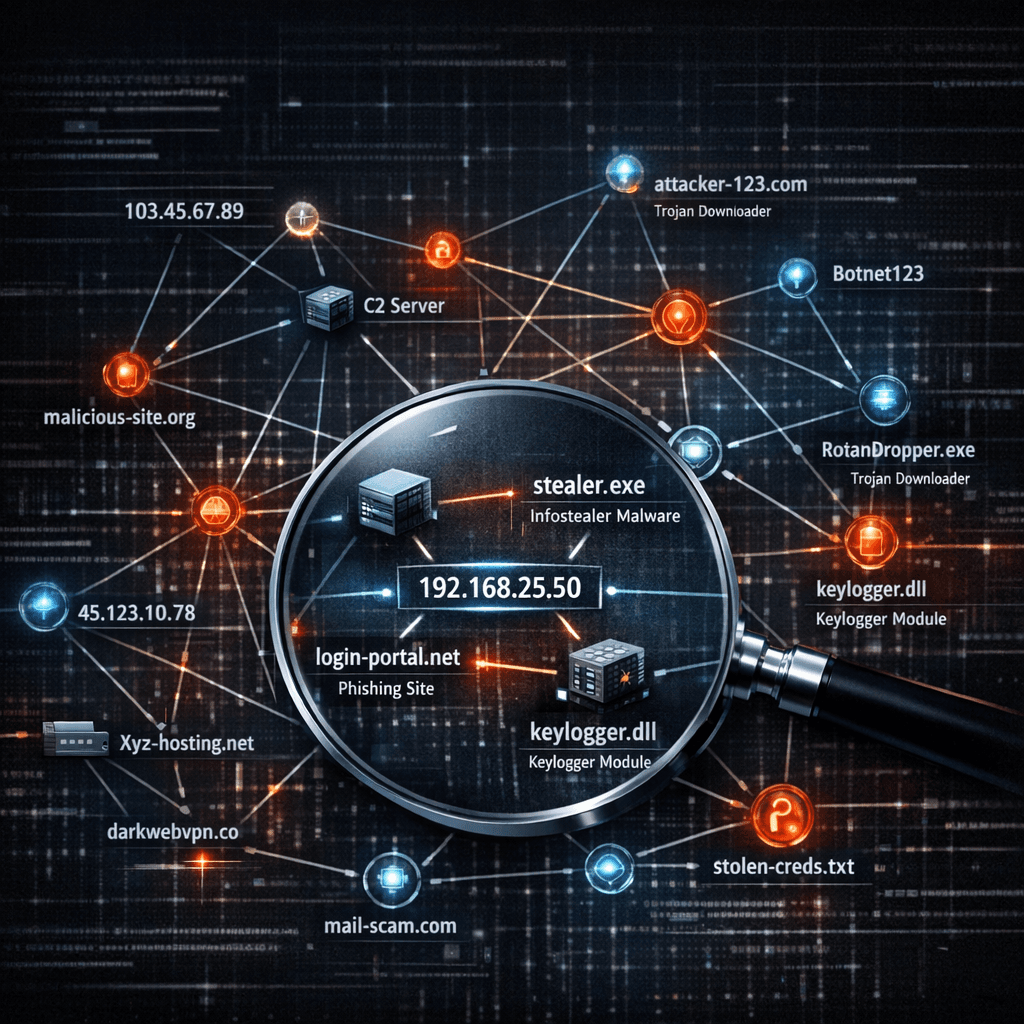
Malicious Infrastructure Clustering: How Passive DNS, TLS Certificates, and ASNs Reveal Shared Campaigns
A single C2 IP is a clue; shared signing patterns and DNS co-occurrence are a map. This guide explains how defenders cluster infrastructure without chasing ghosts—and how to document findings for IR, threat intel, and law enforcement handoffs.
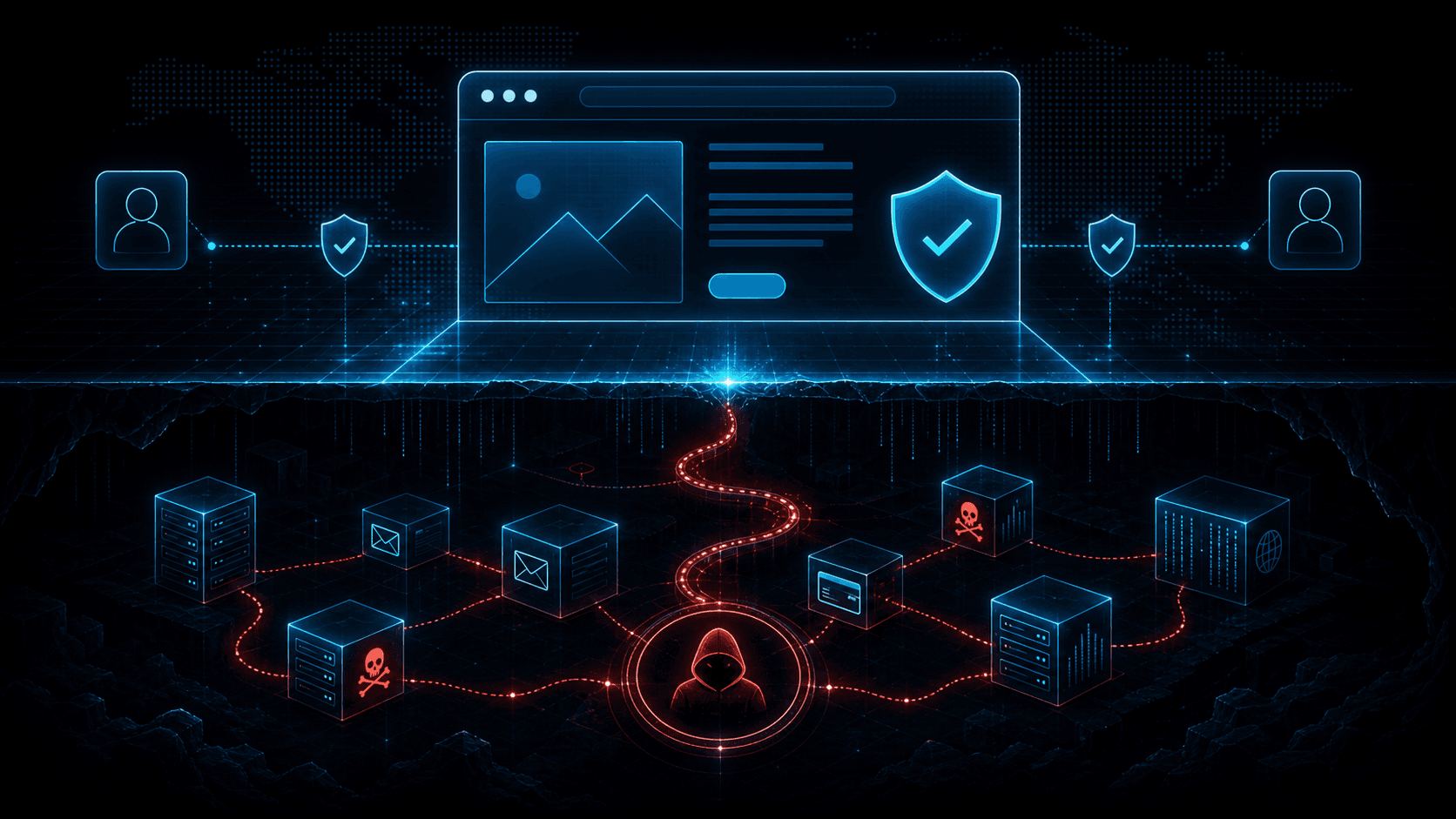
Compromised Domains in Phishing: When Trusted Sites Become Attack Infrastructure
Attackers increasingly host phishing pages, redirects, and malware on compromised legitimate domains. Learn why reputation bypass works and how to detect hidden malicious paths.

Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
Typosquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
DPRK Remote IT Worker Threat: Identity, Insider Risk, and Cloud Access Abuse
DPRK remote IT worker schemes blend fraud, identity deception, and insider access. Learn how hiring, endpoint, SaaS, and cloud controls can reduce the risk.

SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams Sane
A SOAR playbook without enrichment is a ticket printer. A SIEM with unbounded threat feeds is a bill. Here is a practical way to design enrichment for Splunk, Sentinel, or Elastic-style stacks—what to store, when to run playbooks, and what to report upward.
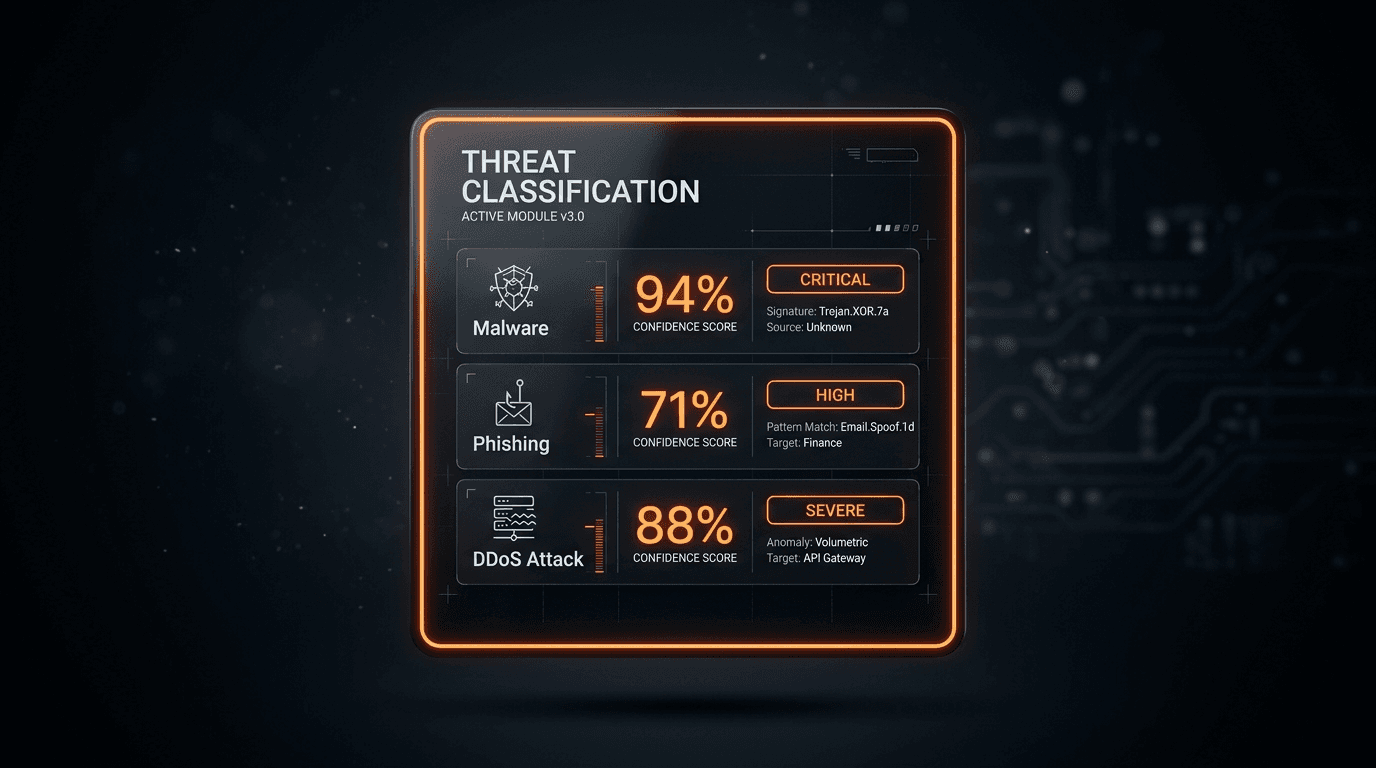
Threat Intelligence Risk Scoring: How to Calibrate Reputation, Reduce False Positives, and Defend Your Decisions
A noisy score is worse than no score. Learn what makes a reputation model trustworthy, how to combine multi-source evidence, and how to communicate uncertainty to your SOC and your executives.

Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)
Not every "datacenter" IP is malicious, and not every Tor exit is a fraudster. This matrix-style guide helps you combine IP type signals with reputation and product context for safer, explainable security decisions.
Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
ASN Reputation for Threat Intelligence: How Autonomous System Intelligence Improves Prioritization and Hunt Programs
An IP address is a snapshot; an autonomous system (ASN) is a neighborhood. Learn how to use ASN context safely for triage, fraud, and security operations—without mistaking a giant cloud for a monolithic "bad host".
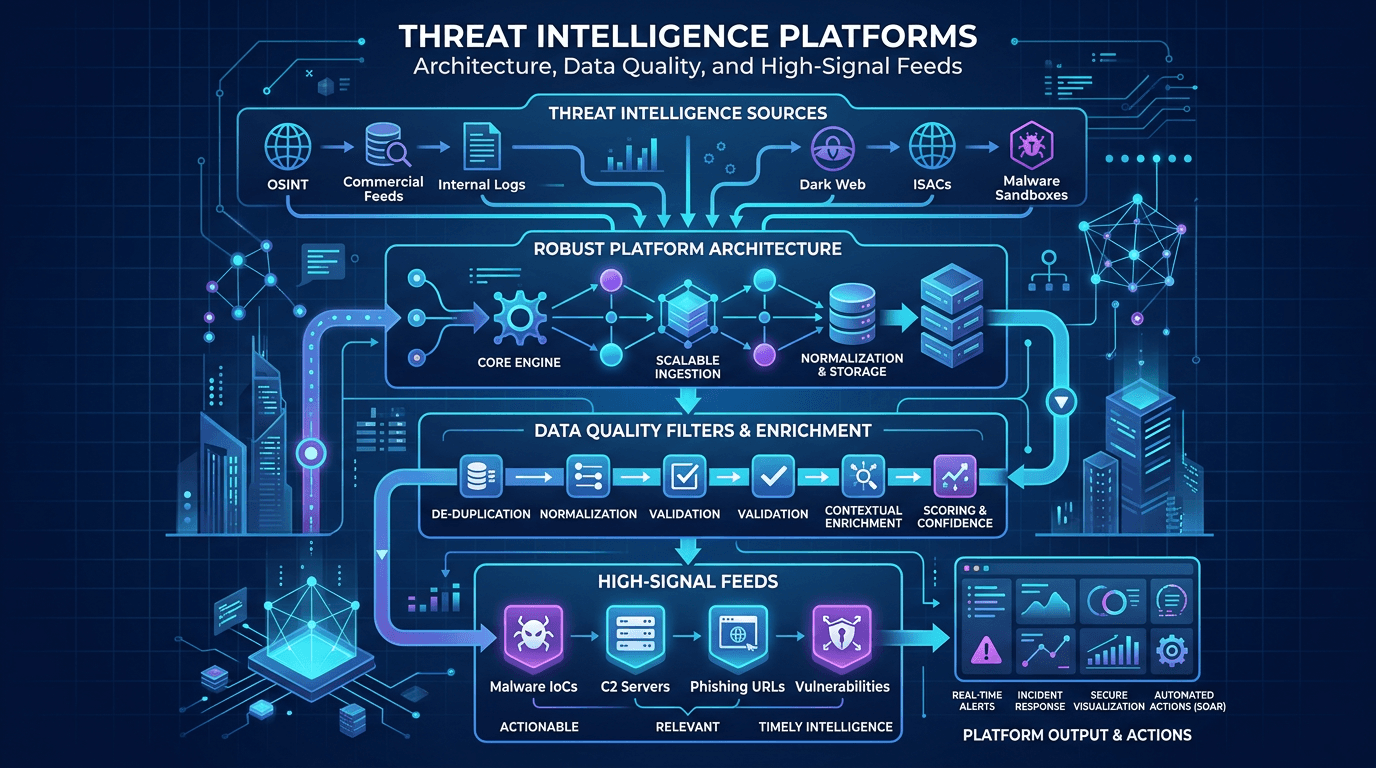
Threat Intelligence Platforms: Architecture, Data Quality, and High-Signal Feeds
Design TIPs and intel pipelines that scale: normalization, confidence scoring, deduplication, API-first delivery, and how to pair platform investments with analyst workflows.
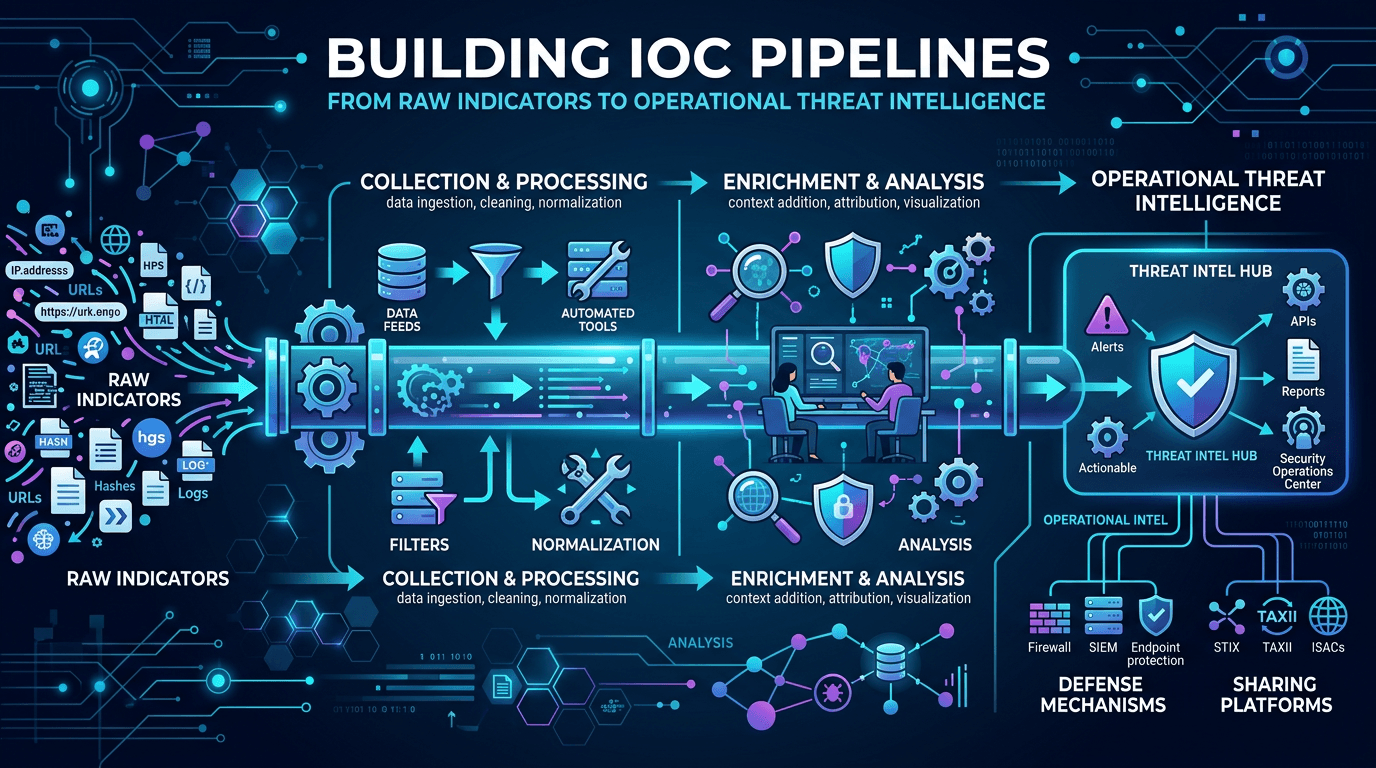
Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026
A practical engineering guide to building indicator of compromise (IOC) pipelines—ingestion, normalization, deduplication, enrichment, scoring, distribution, and feedback—to turn raw threat feeds into operational defense.
IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROI
An indicator without context is a ticket without an owner. Learn how IOC enrichment APIs work, which fields SOC teams need at each tier, and how to wire them into case management without building a data swamp.
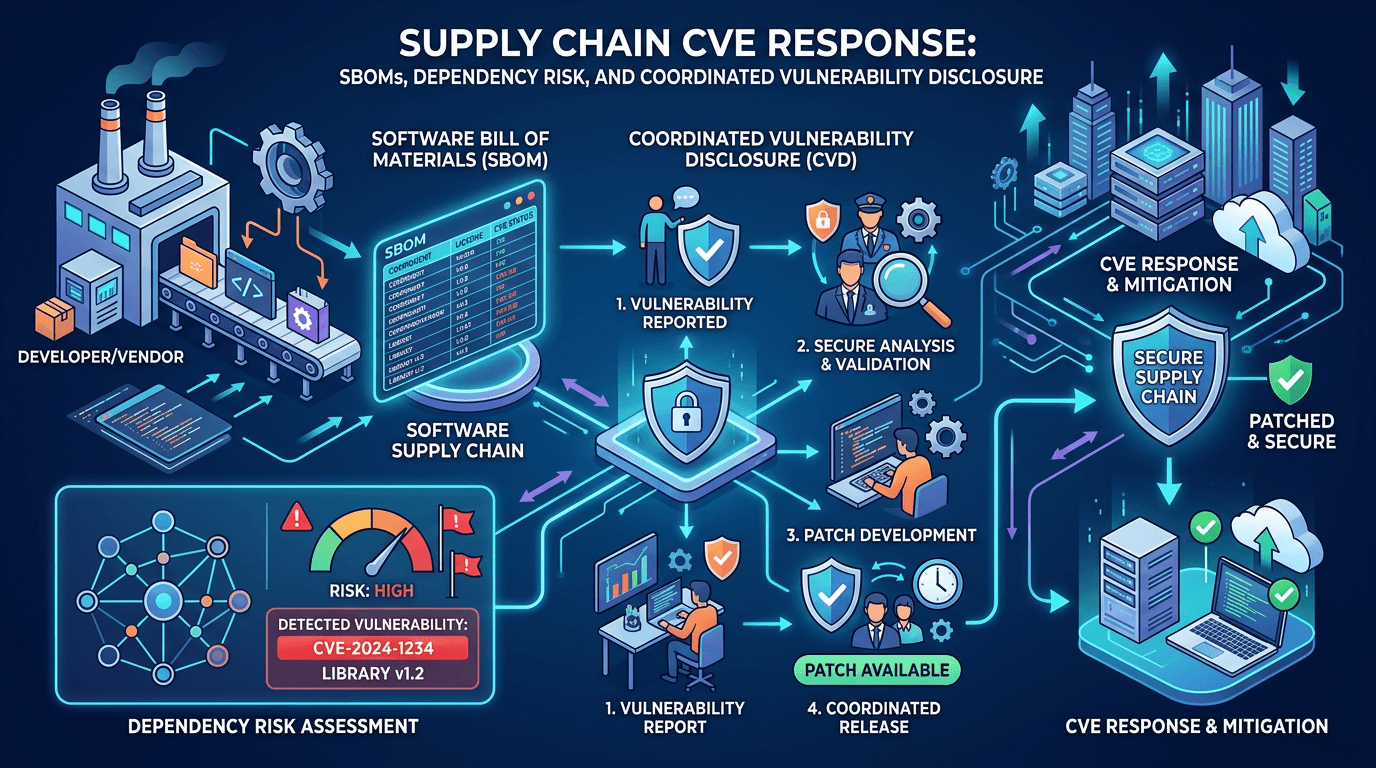
Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability Disclosure
Build a modern supply-chain security program: generate SBOMs, map CVEs to components, integrate EPSS and KEV, and coordinate fixes across vendors and open-source maintainers.
Answer-Engine Optimization for Cybersecurity: How to Get Cited by ChatGPT, Perplexity, and Claude in 2026
Traditional SEO is not enough when users ask large language models for vendor comparisons and step-by-step security guidance. Learn how to structure threat intelligence and security content so AI systems can parse, trust, and cite your brand without hype or ambiguity.
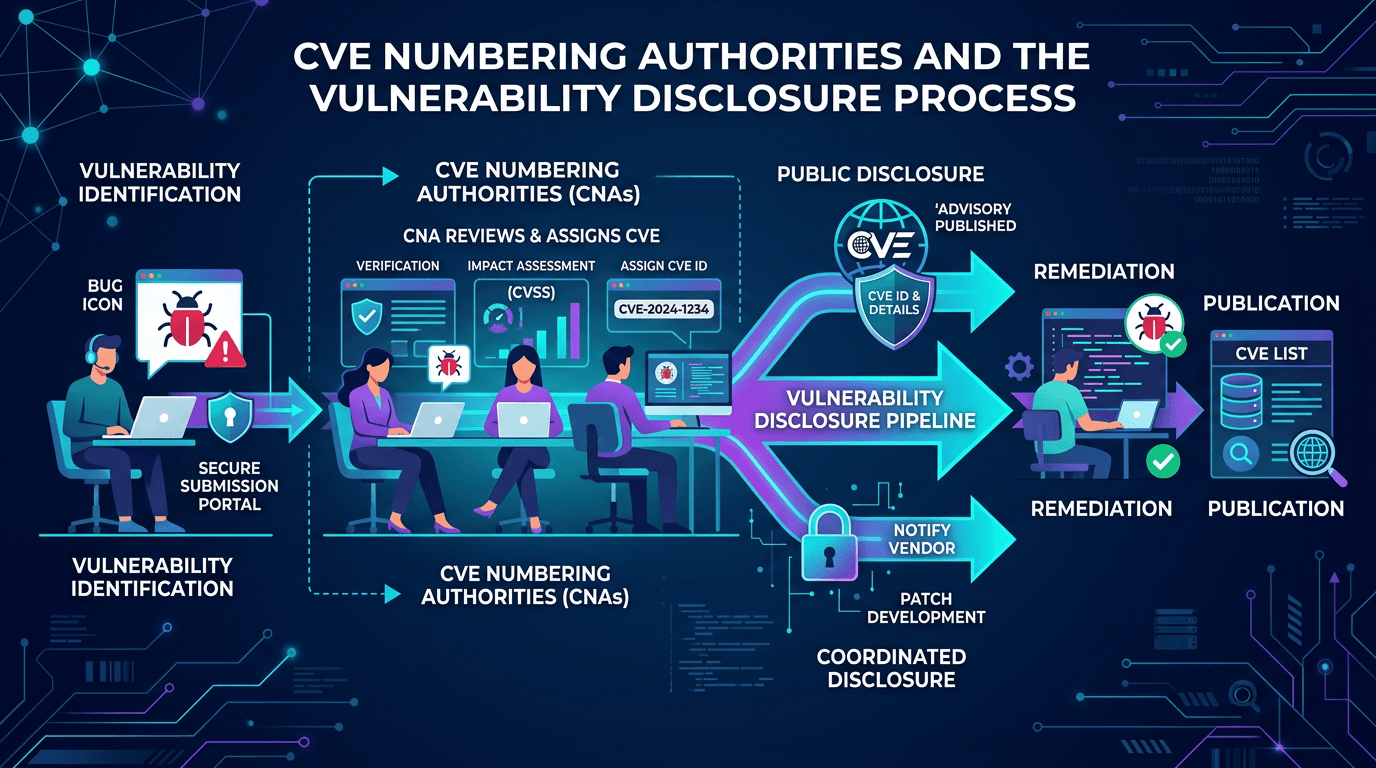
CVE Numbering Authorities and the Vulnerability Disclosure Process: A 2026 Practitioner Guide
Understand how CVEs are born—from initial vulnerability discovery through CNA assignment, coordinated disclosure, and publication—plus how this pipeline shapes defender priorities and SEO-visible vulnerability data.
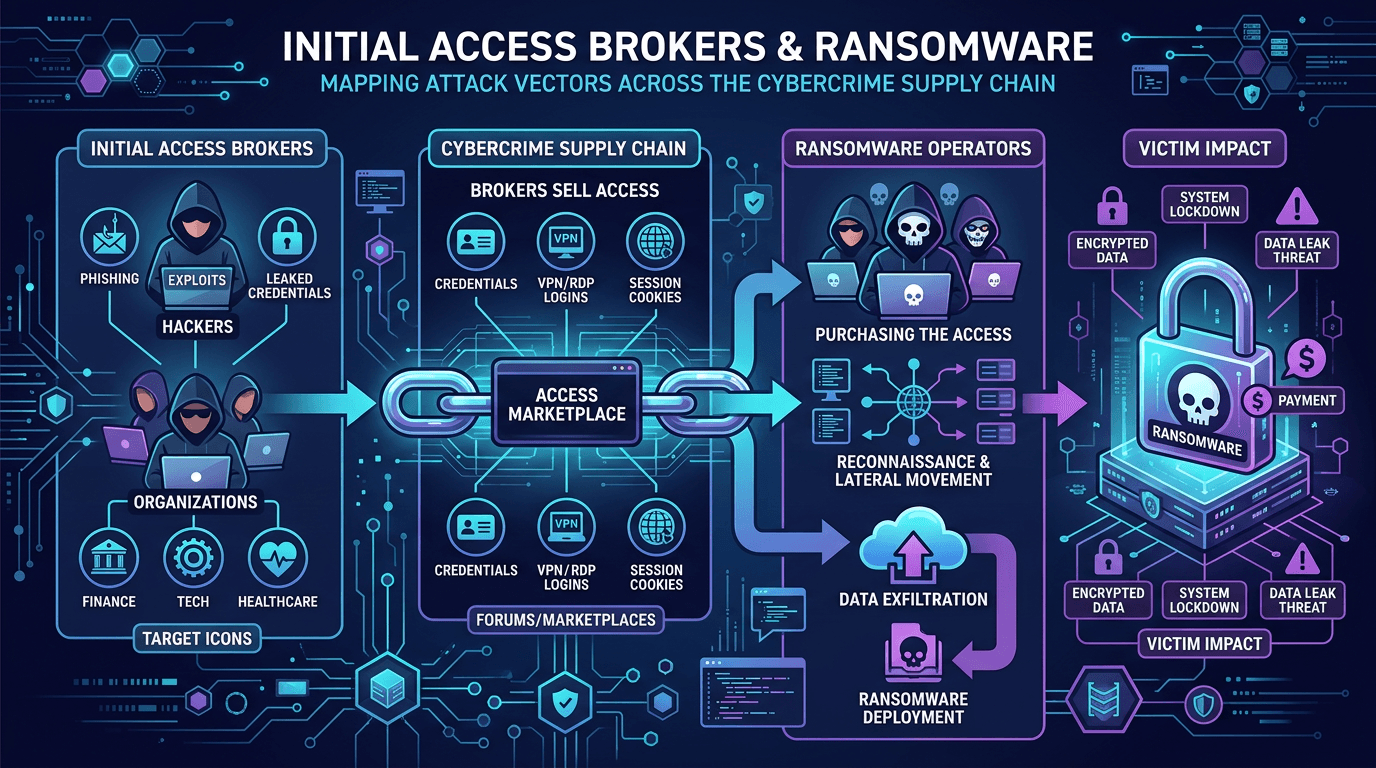
Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Understand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
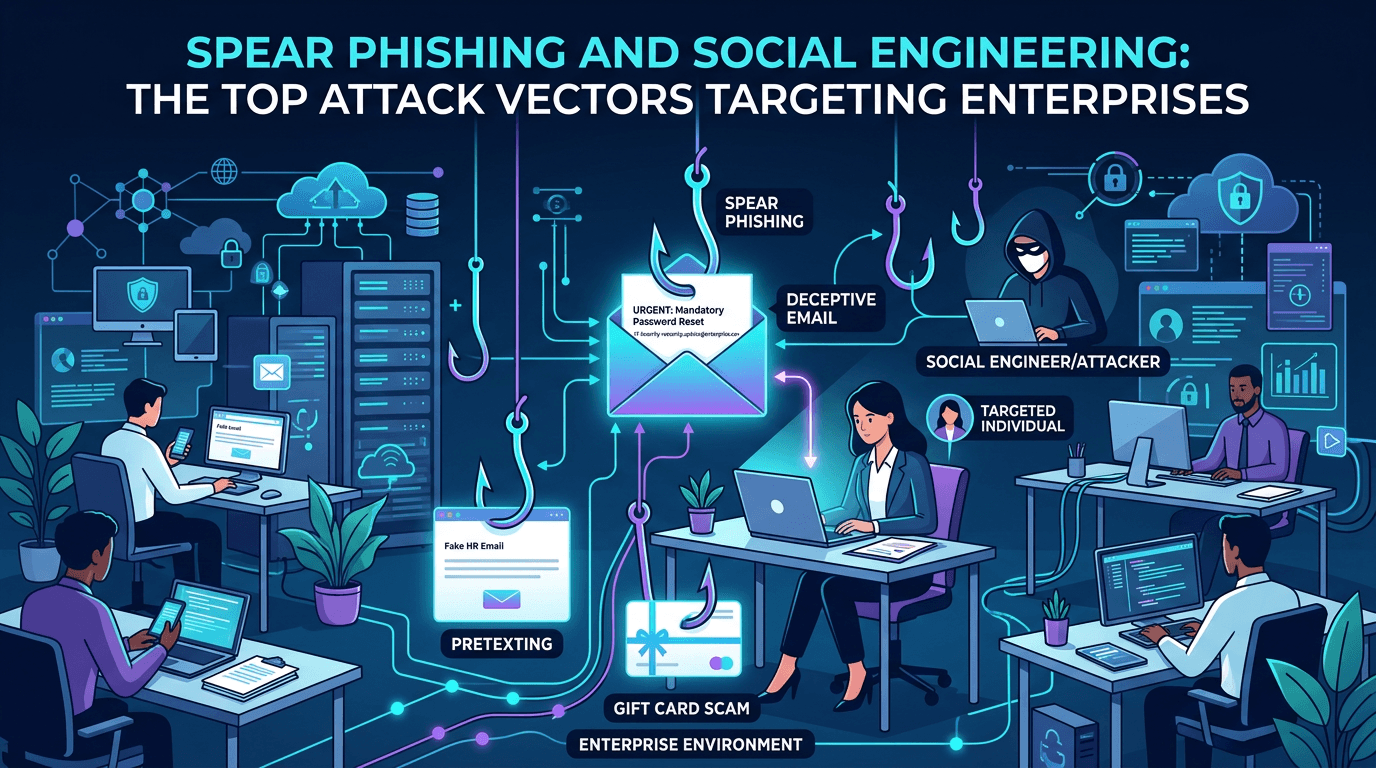
Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
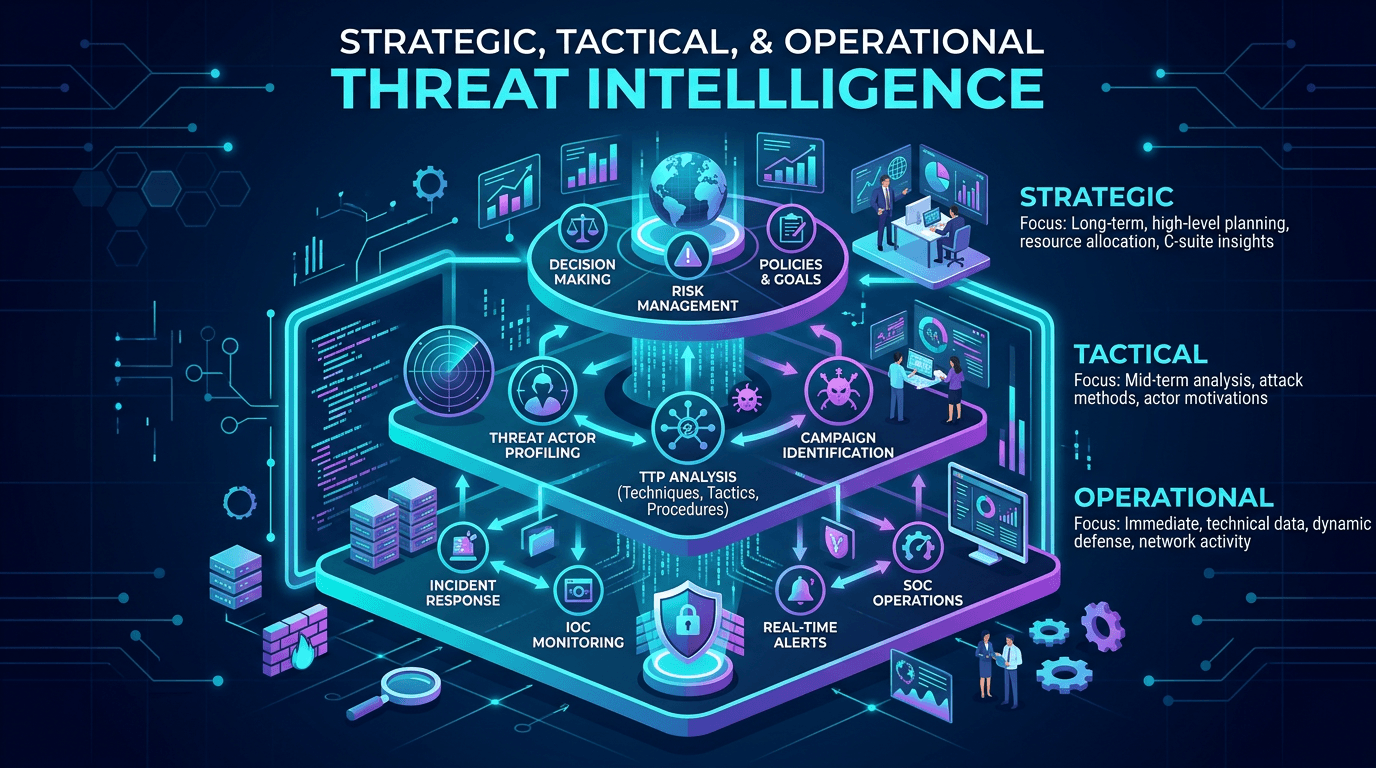
Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security Programs
Align CTI outputs with audience needs: executive risk narratives, SOC-ready IOCs, and MITRE-mapped TTPs—plus governance models that keep intelligence timely and measurable.
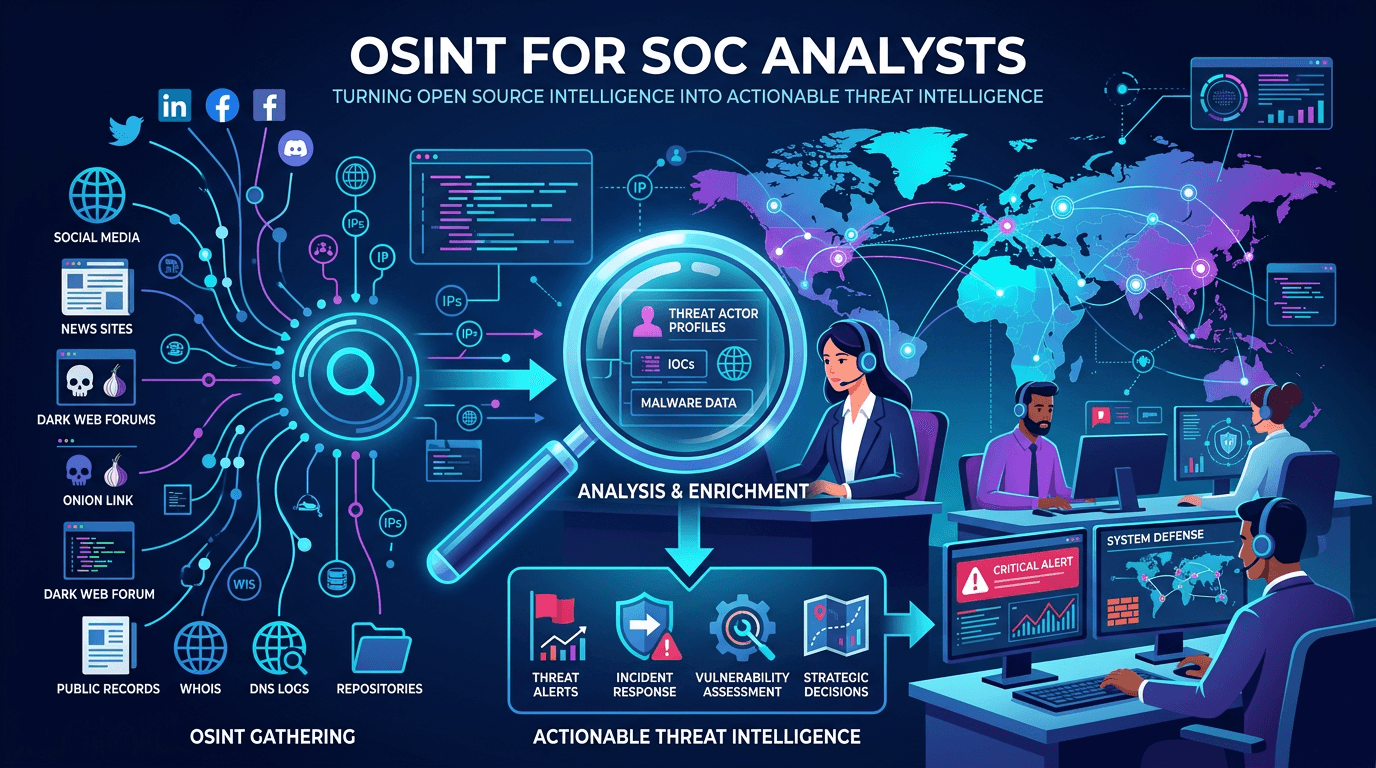
OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat Intelligence
A complete guide to open source intelligence (OSINT) for security operations—tools, techniques, workflows, and legal considerations for collecting, analyzing, and operationalizing open threat data in a modern SOC.
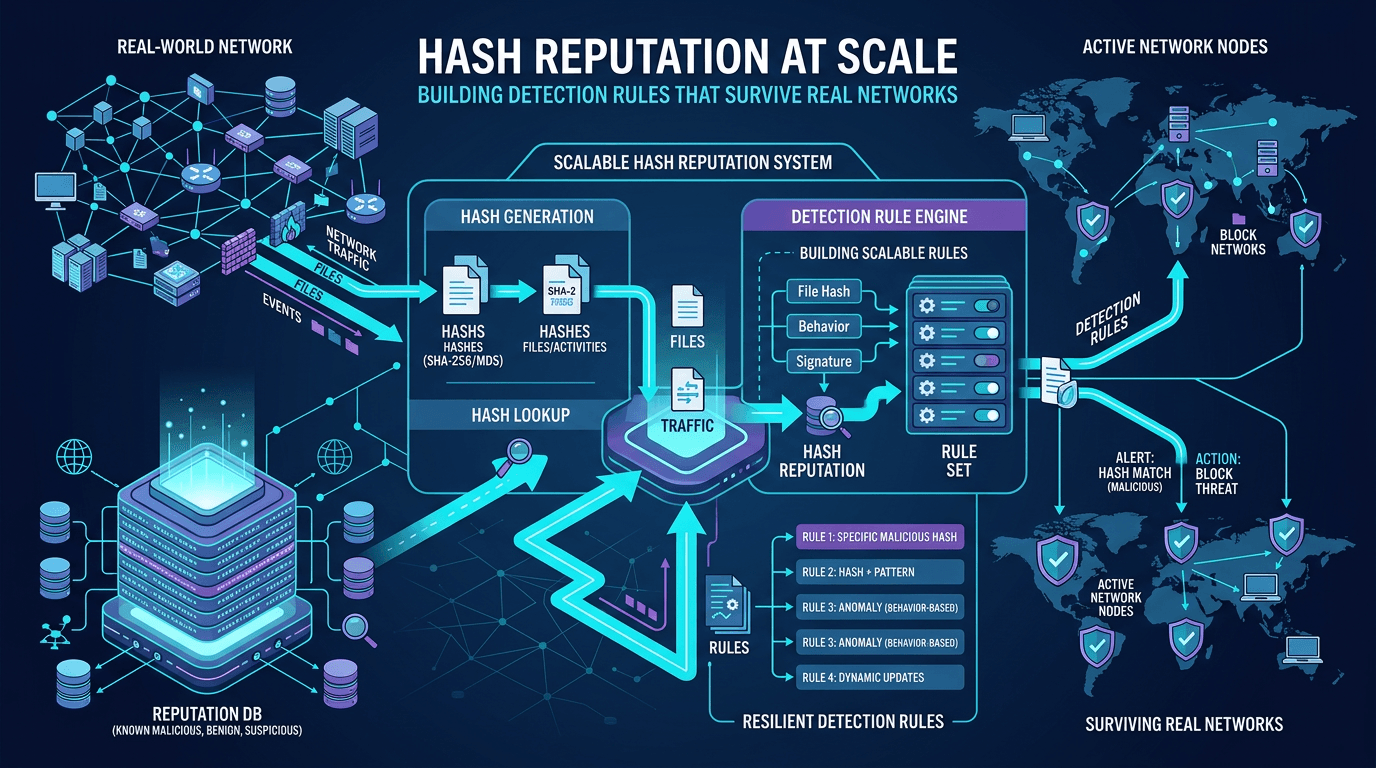
Hash Reputation at Scale: Building Detection Rules That Survive Real Networks
Move beyond one-off hash blocks: design reputation pipelines, reduce false positives, and integrate file intelligence with IP and domain context for enterprise-grade detection engineering.
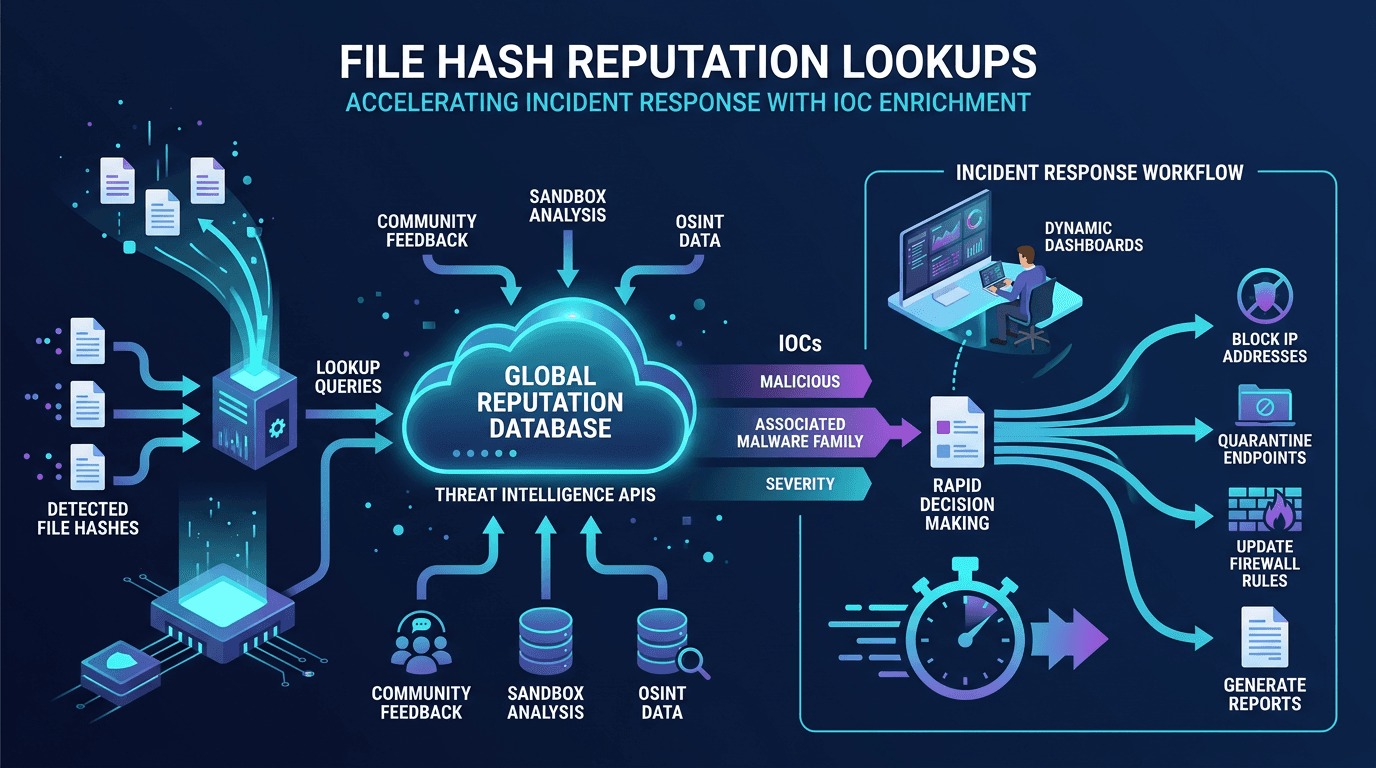
File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
A practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
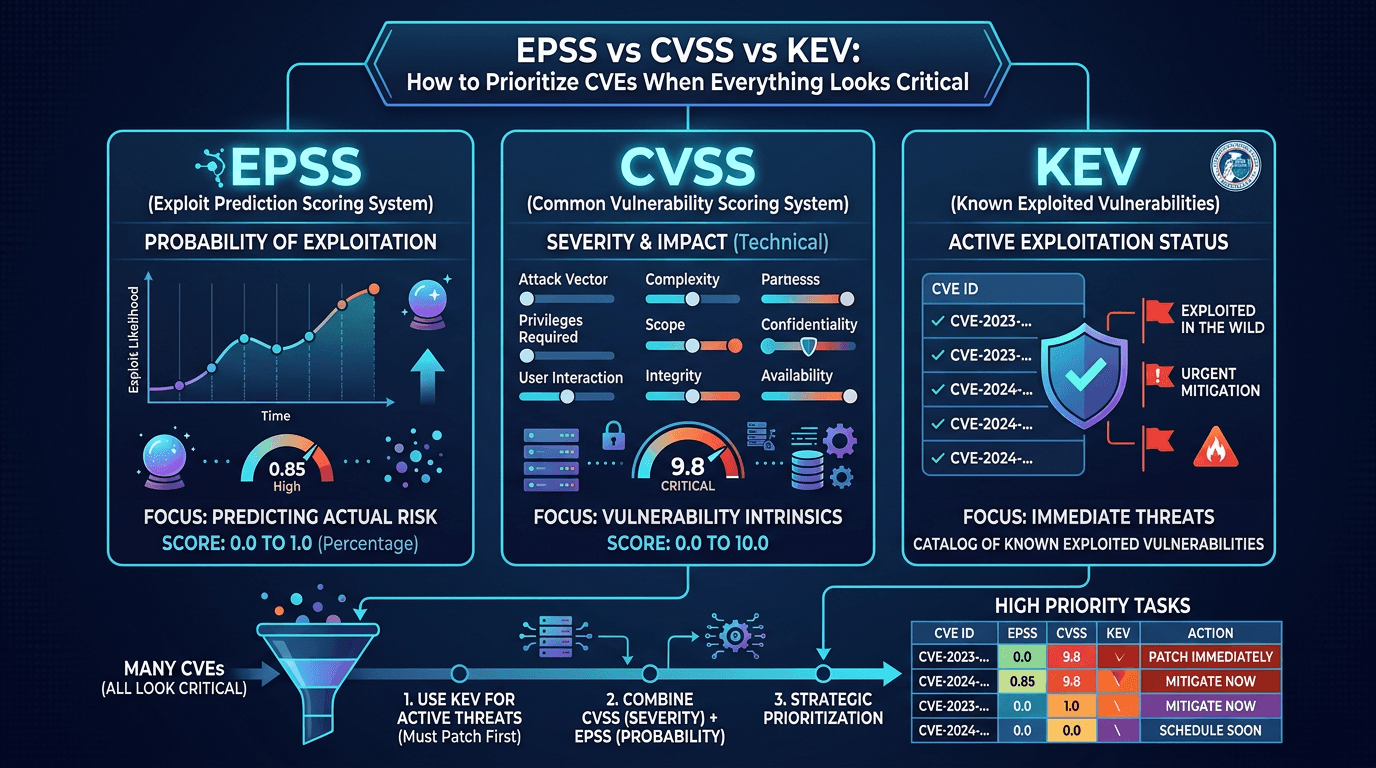
EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Cut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
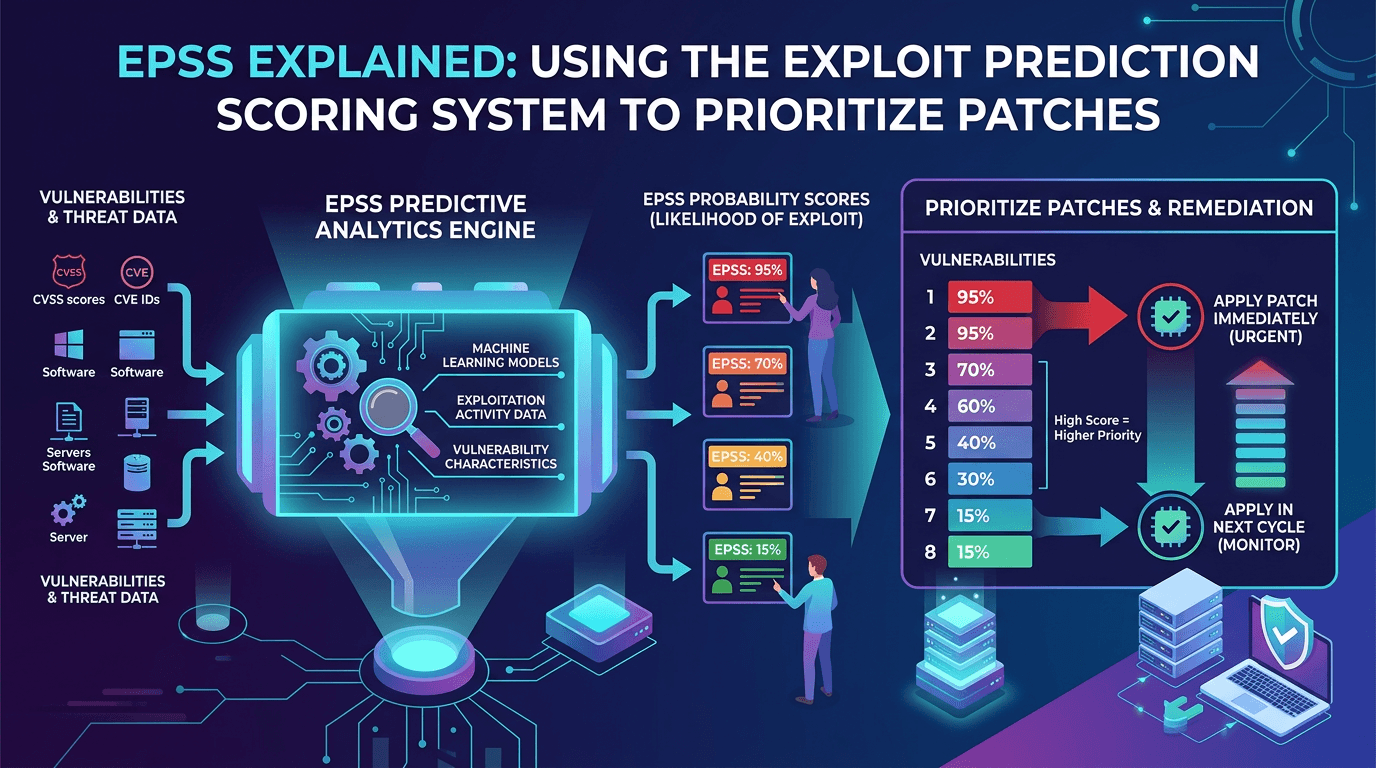
EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
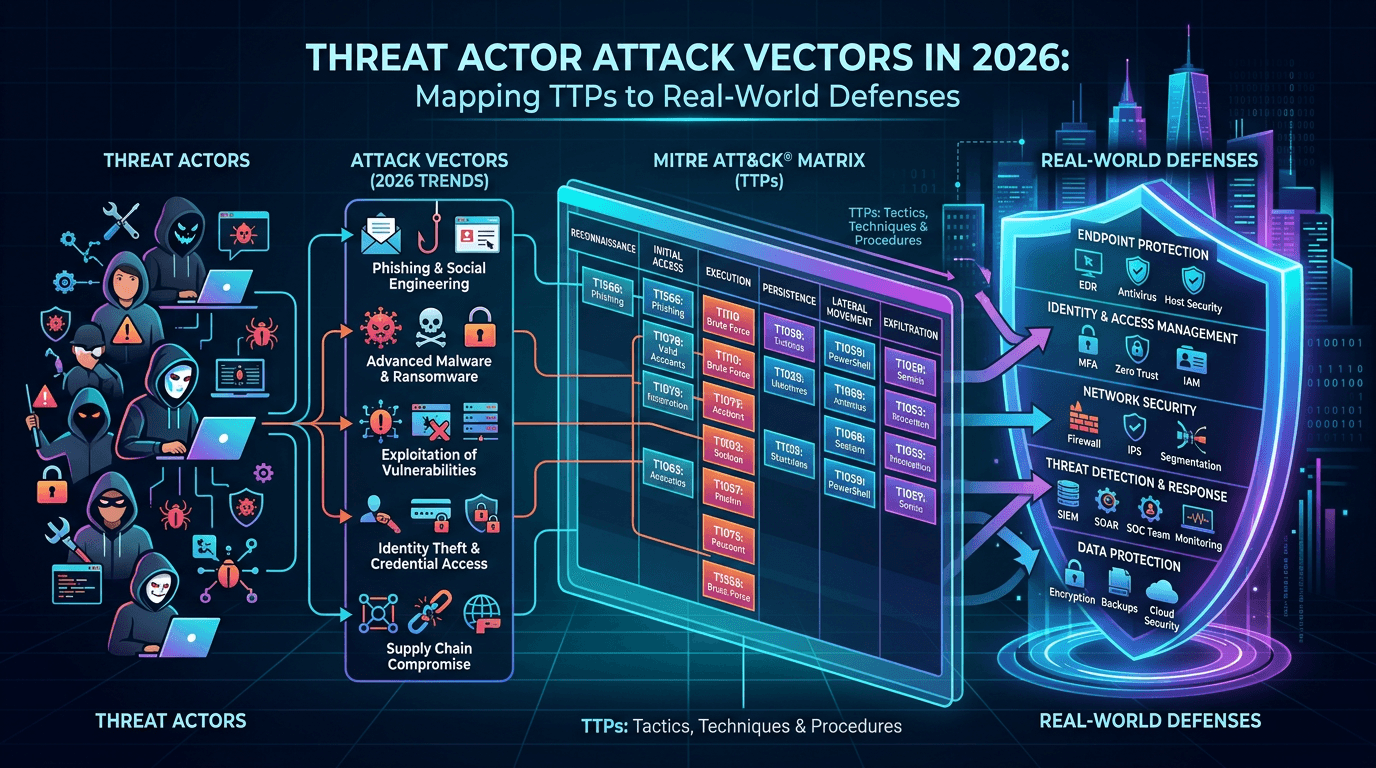
Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Explore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
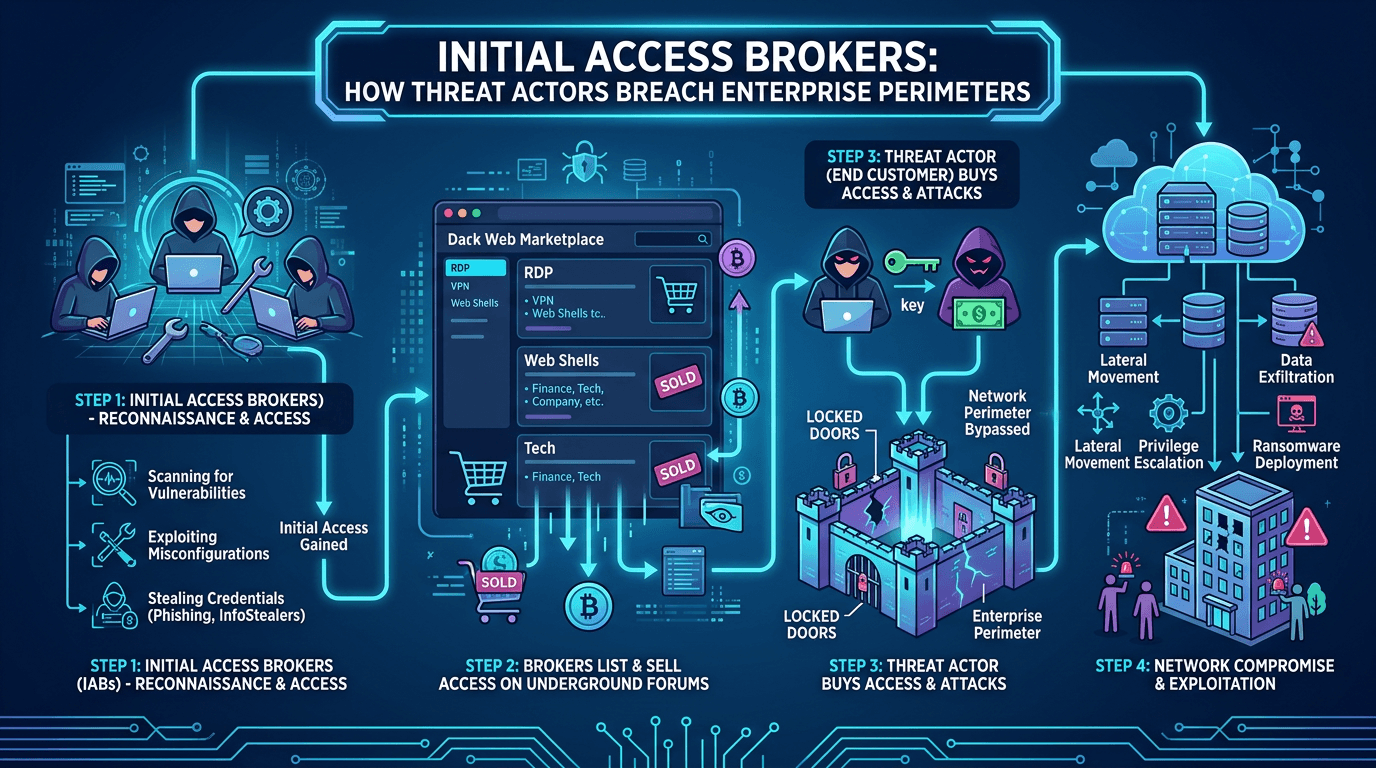
Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026
A deep dive into initial access brokers (IABs)—the cybercrime specialists who sell footholds into corporate networks—covering their techniques, pricing, detection signals, and how to defend against the top attack vectors they exploit.
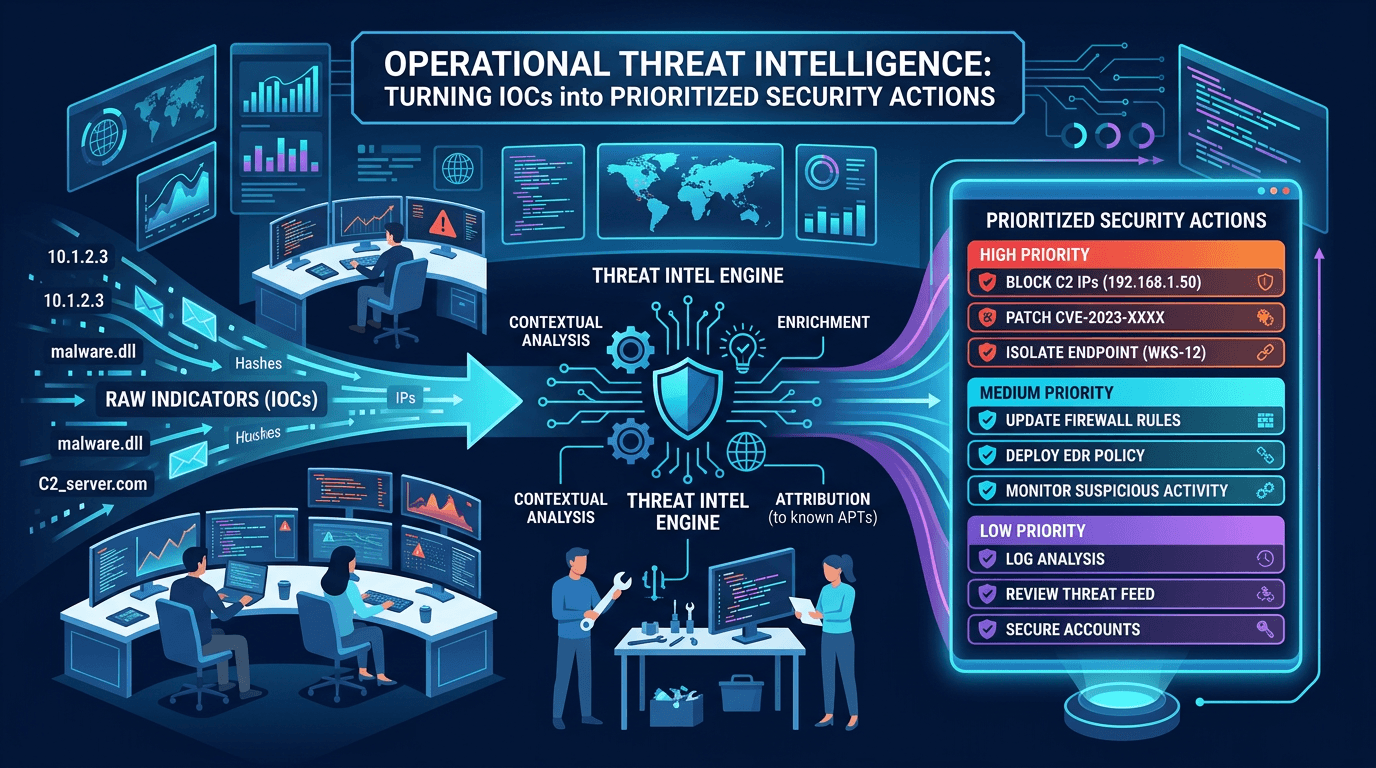
Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Define operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
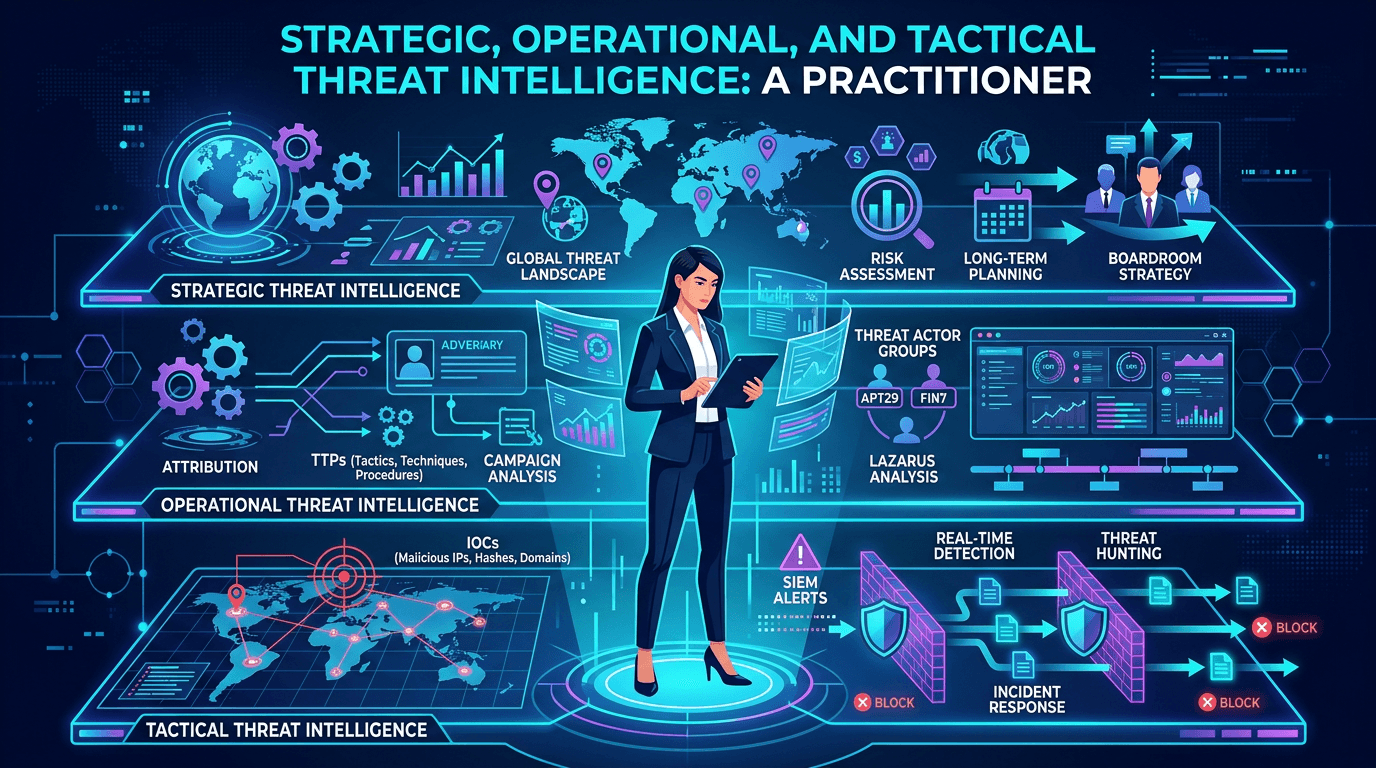
Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
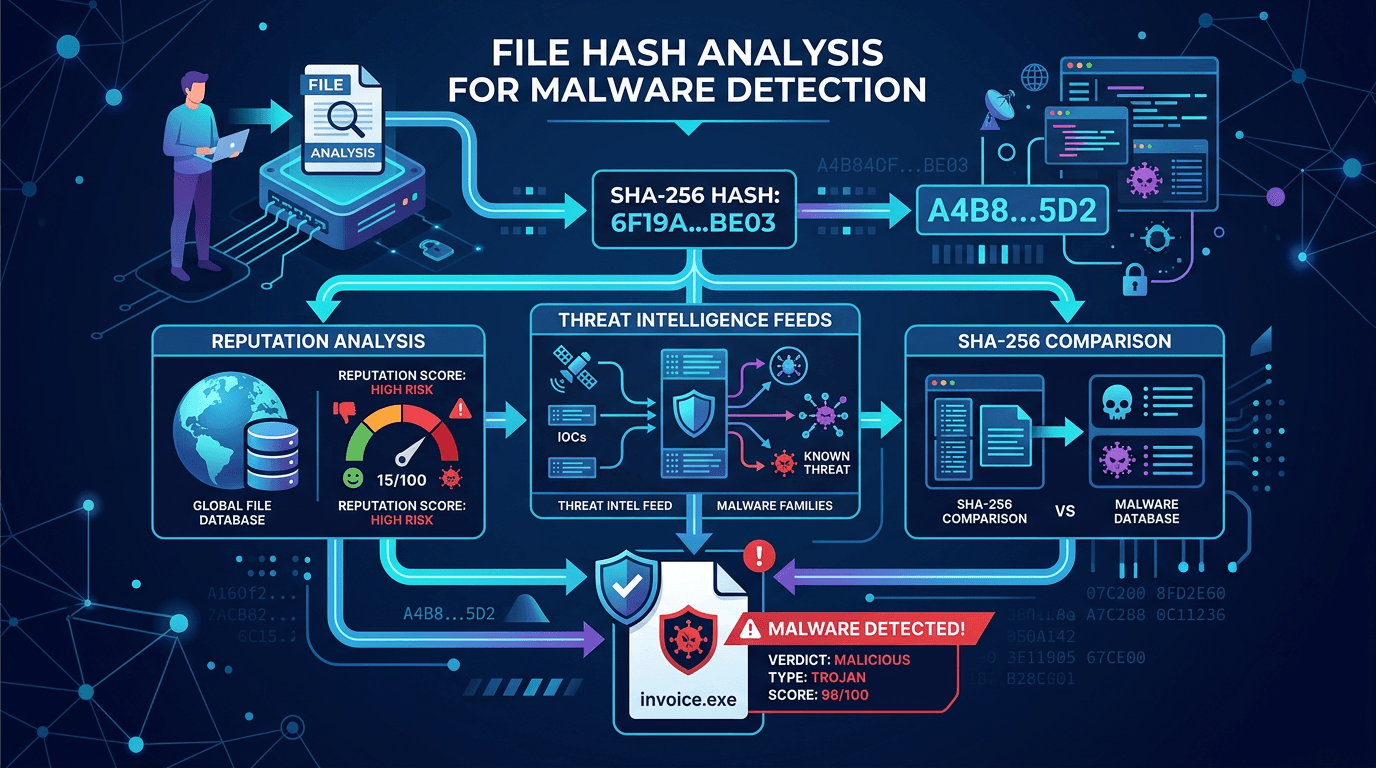
File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel Workflows
Learn how cryptographic file hashes power malware identification, why SHA-256 dominates security tooling, and how to combine hash lookups with broader threat intelligence for fewer false positives.
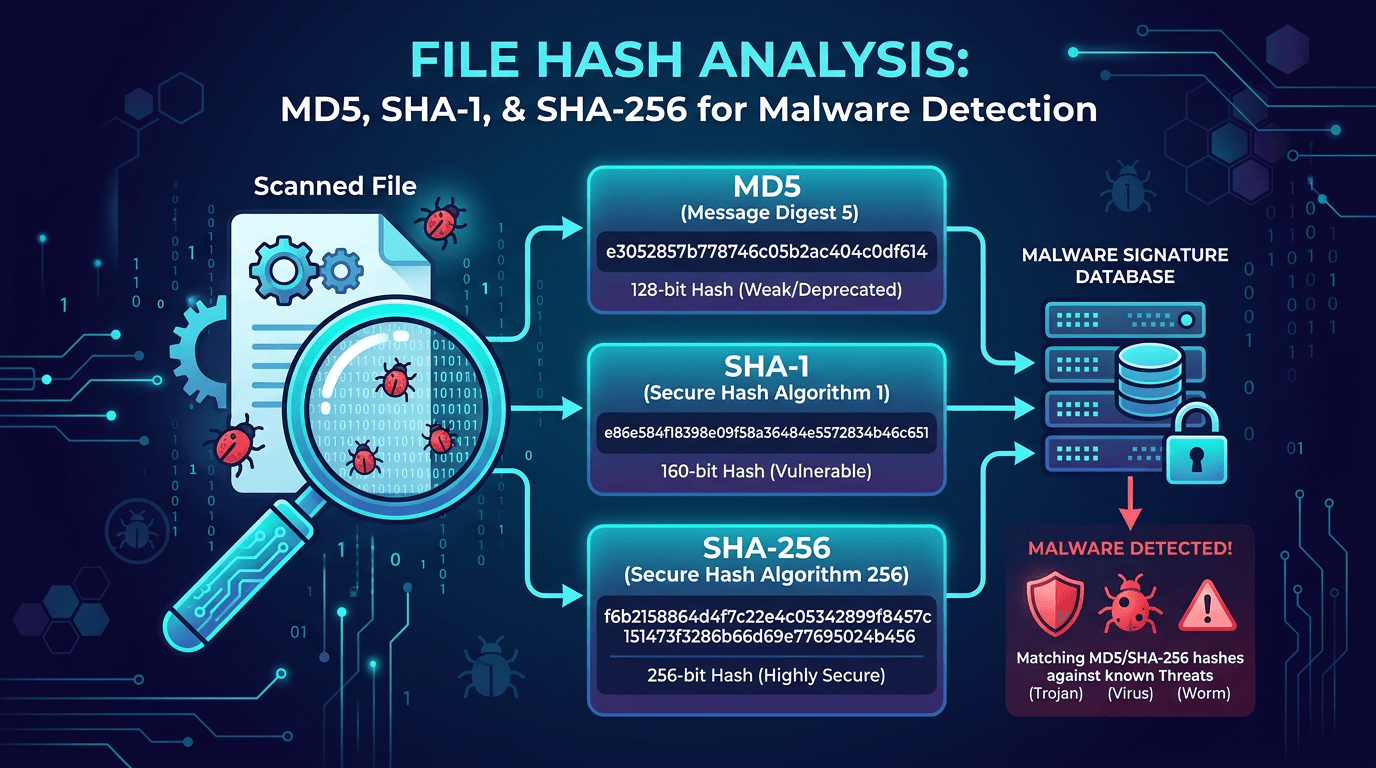
File Hash Analysis: MD5, SHA-1, and SHA-256 for Malware Detection and Threat Hunting
A practical guide to file hashes in cybersecurity—how MD5, SHA-1, and SHA-256 work, why they matter for malware detection, incident response, and threat hunting, and how to use hash lookups to enrich indicators of compromise.
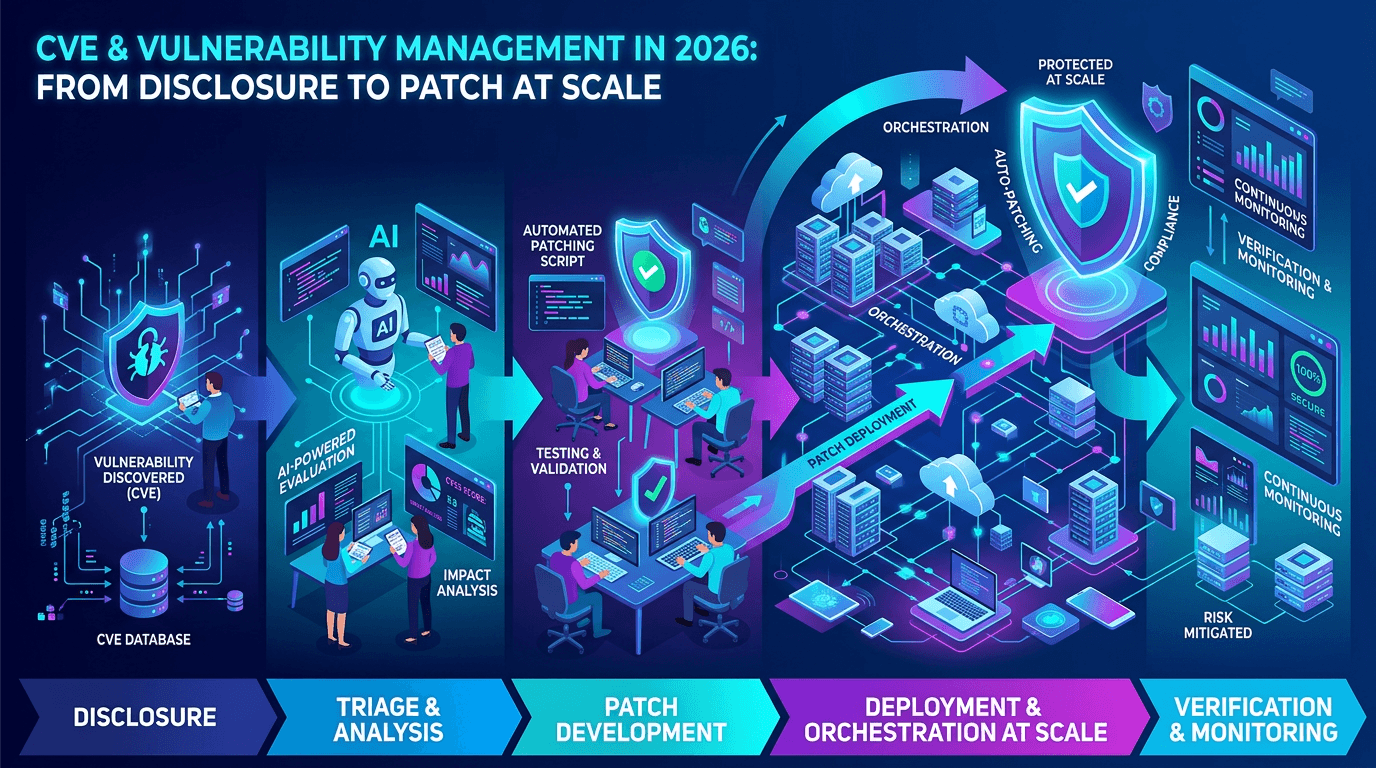
CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
A practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
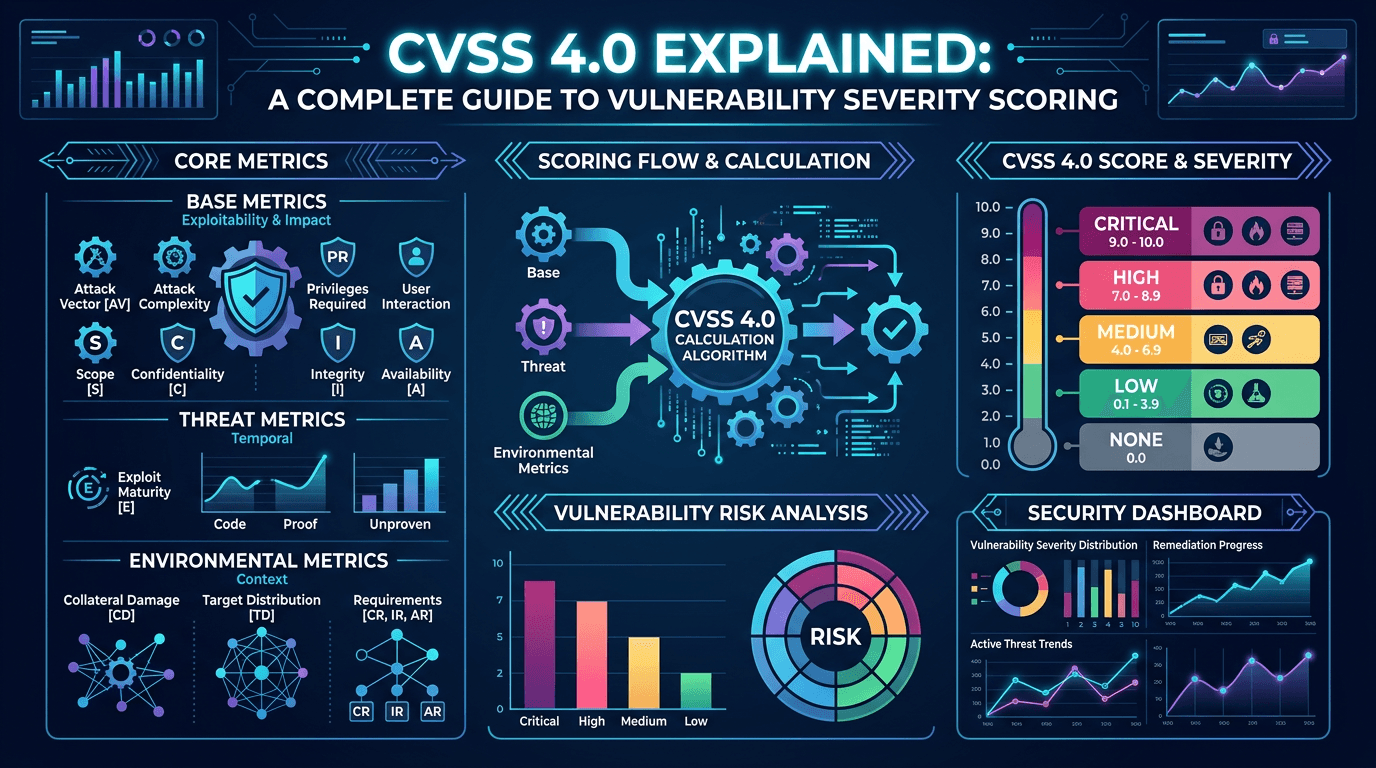
CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026
Master the Common Vulnerability Scoring System v4.0 with a practical breakdown of base, threat, environmental, and supplemental metrics—and learn how to translate CVSS into real-world risk decisions.

OSINT en cybersécurité : cadre légal et éthique
La collecte d’informations en sources ouvertes est puissante pour la CTI et l’investigation, mais elle heurte vie privée, droit d’auteur et territorialité. Repères pour les équipes qui veulent rester dans les clous.
Ransomware et double extorsion : stratégie de défense
Chiffrement plus fuite de données : la double extorsion a changé la donne pour les sauvegardes et la communication de crise. Principes de résilience, négociation et préparation réglementaire.
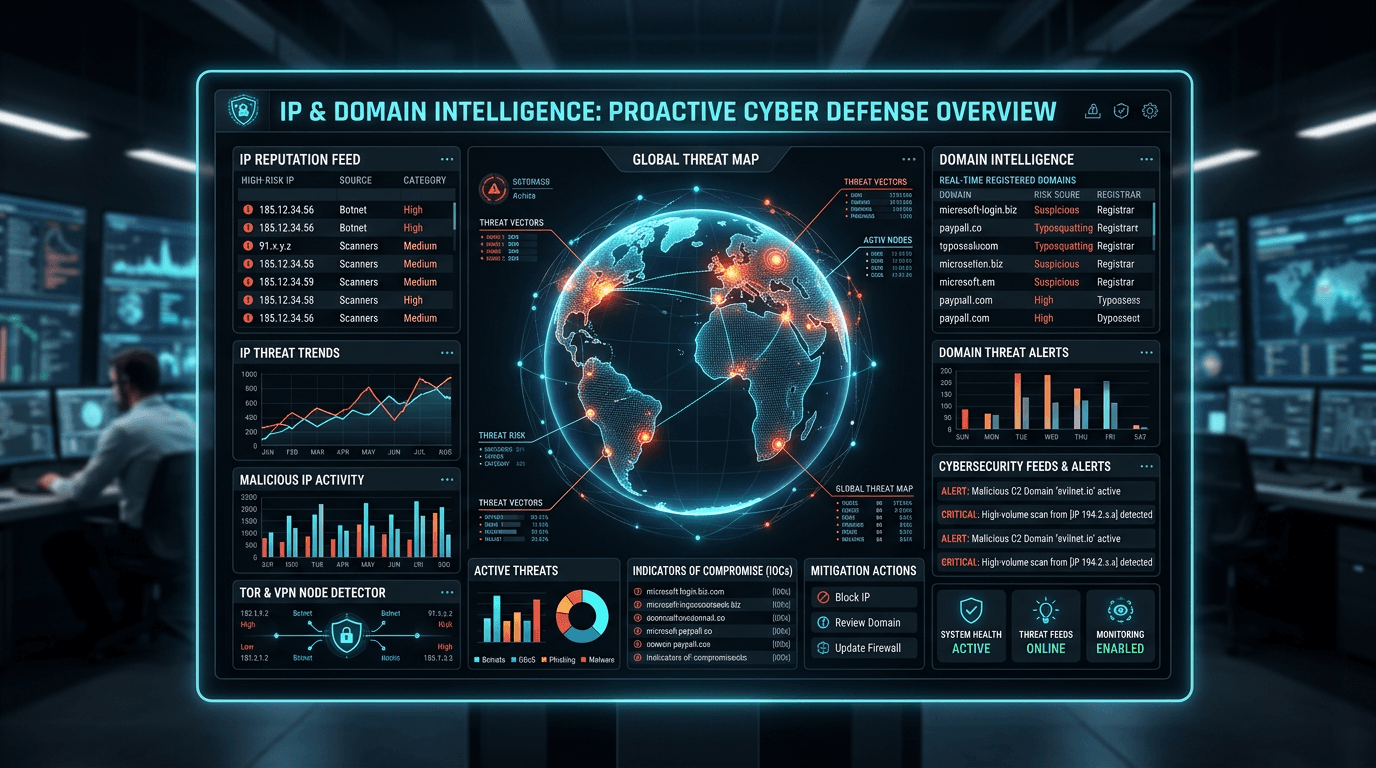
IP and Domain Intelligence: Building a Proactive Cyber Threat Defense
Reactive security leaves organizations perpetually one step behind attackers. Learn how combining IP and domain intelligence transforms your security posture from reactive incident response to proactive threat prevention that stops attacks before they start.
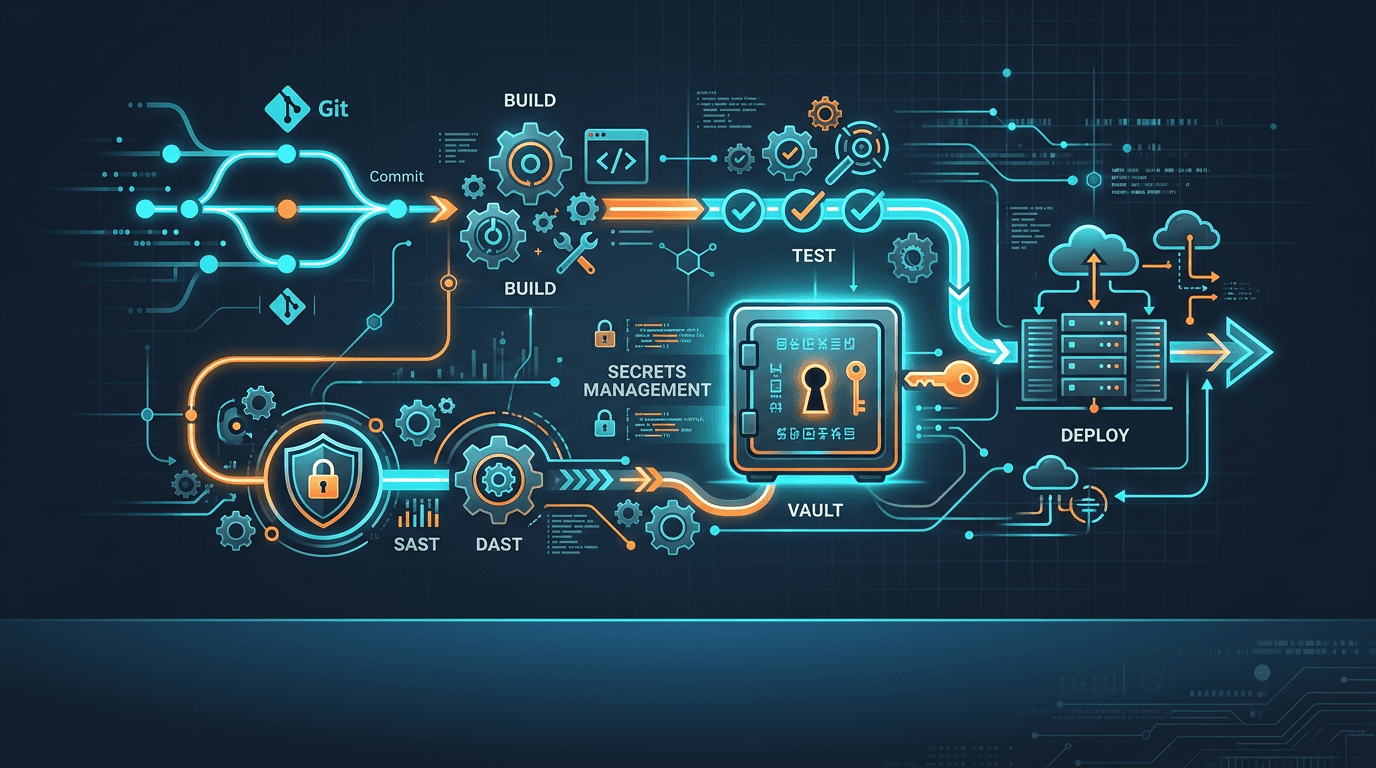
CI/CD et fuites de secrets : sécuriser vos pipelines
Clés API et jetons dans les dépôts Git, caches de build exposés, pipelines trop permissifs : la supply chain logicielle commence dans votre forge. Bonnes pratiques et contrôles minimum pour 2026.
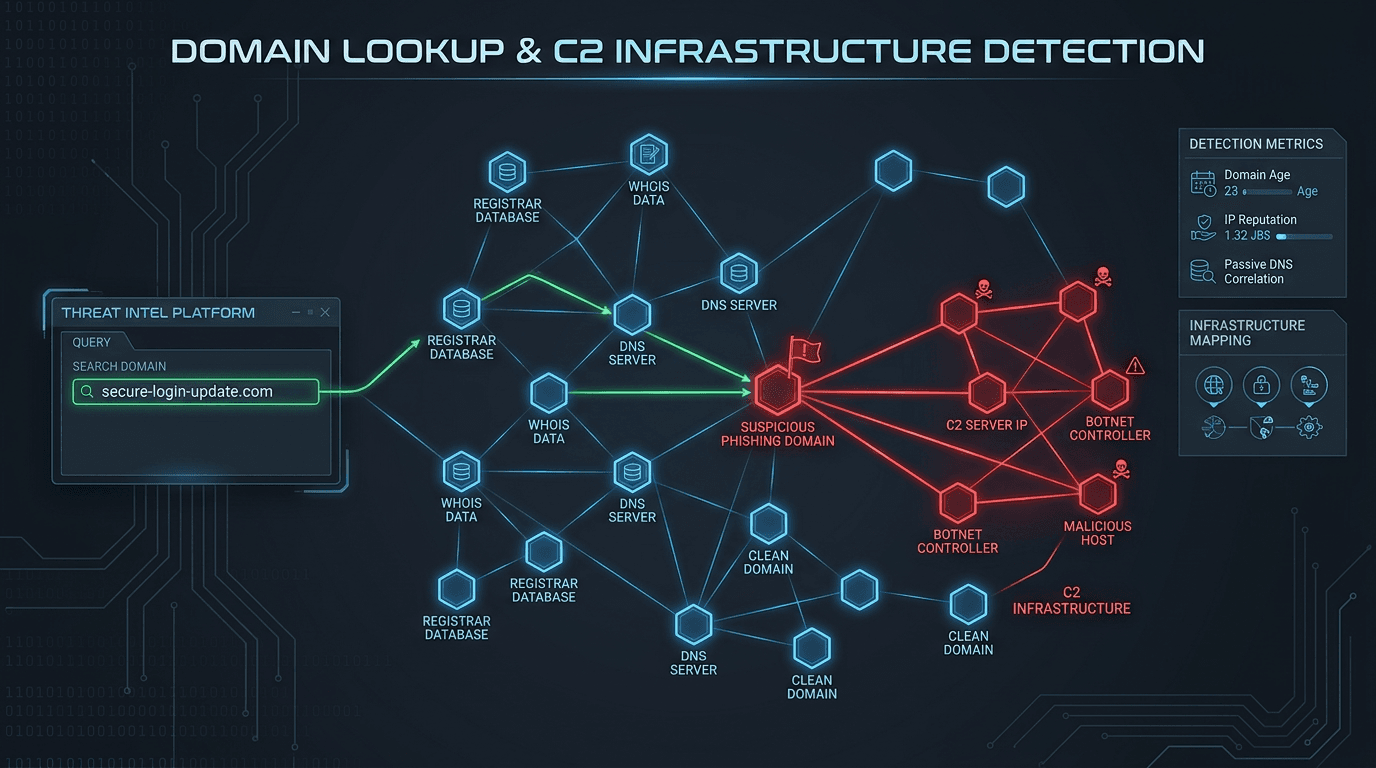
Domain Lookup for Phishing and C2 Infrastructure Detection
Phishing campaigns and malware operations depend on domain infrastructure that leaves detectable traces. Learn how advanced domain lookup techniques help security teams uncover phishing sites and command-and-control servers before they compromise your organization.
Purple team : aligner CTI, red team et détection
La purple team n’est pas un gadget RH : c’est le lieu où l’intelligence sur les menaces rencontre les tests d’intrusion et les règles SIEM. Comment structurer ces ateliers pour des résultats mesurables.
Real-Time IP Reputation Check: Stop Cyber Threats at the Network Edge
Real-time IP reputation checks give you the power to identify and block malicious actors the moment they connect to your systems. Discover how to implement automated threat detection that works at machine speed, not analyst speed.
Domain Lookup: How to Identify Malicious Websites Before They Strike
Malicious websites are the launchpad for phishing, malware distribution, and credential theft. Learn how domain lookup tools use reputation data, WHOIS analysis, and threat feeds to identify dangerous domains before your users click.
Extensions de navigateur malveillantes : un angle mort de la sécurité
Les extensions Chrome et Edge ont accès à vos pages, cookies et parfois à tout le trafic HTTP. Voici comment les attaquants les distribuent, comment les détecter, et quelles politiques IT adopter.
IP Lookup for Cyber Threat Detection: A Complete Security Guide
Learn how IP lookup works as a frontline defense against cyber threats. Discover how to use IP reputation data, threat intelligence feeds, and automated checks to block malicious actors before they reach your systems.
Métriques SOC : quels indicateurs suivre pour la cybersécurité
Un SOC efficace ne se juge pas au volume d’alertes. Voici les KPI utiles pour mesurer la détection, la réponse et l’amélioration continue — sans noyer l’équipe sous les tableaux de bord inutiles.
Injections de prompt et LLM : sécuriser vos applications en 2026
Les modèles de langage intégrés aux produits exposent de nouvelles surfaces d’attaque : jailbreak, exfiltration de données et contournement de politiques. Voici un cadre pragmatique pour architectes et développeurs.
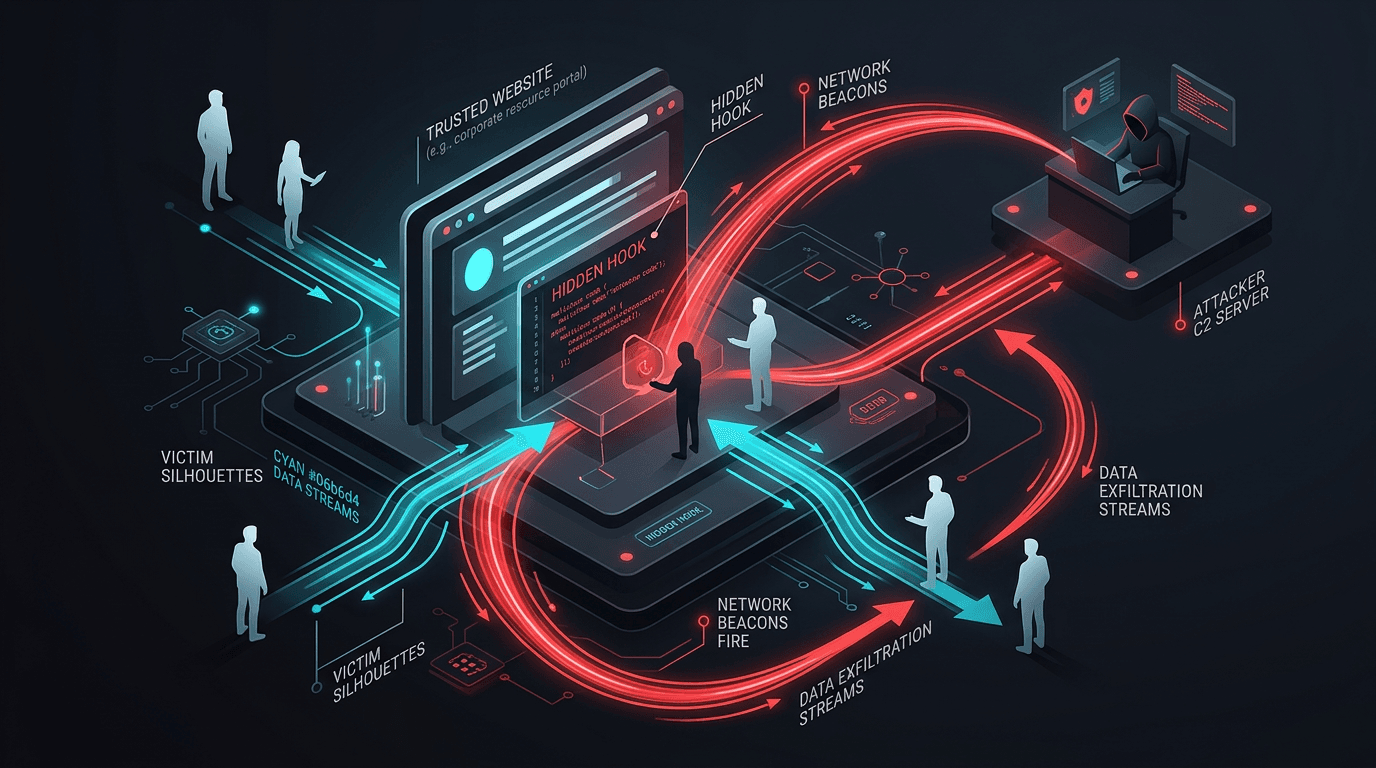
Watering Hole Attacks: Compromising the Sites Your Victims Already Trust
Instead of spear-phishing individuals, APTs infect websites their targets routinely visit. Learn how watering hole campaigns work and how to harden web supply chains and detection.
Cognitive Hacking: The Battle for Your Mind
Cognitive hacking targets the user, not the machine. It manipulates perception and decision-making through disinformation and psychological triggers.

Quishing : quand le QR code devient une arme de phishing
Les attaques par QR code (quishing) contournent les filtres e-mail et exploitent la confiance des utilisateurs. Découvrez les scénarios typiques, les signaux d’alerte et les mesures concrètes pour sensibiliser vos équipes et renforcer votre défense.
SIM Swapping and Telecom Fraud: When Your Phone Number Is the Weakest Factor
Attackers who control your mobile number can bypass SMS-based 2FA and reset passwords. Learn how SIM swap fraud works and how to reduce reliance on SMS one-time codes.

Malvertising and Search Poisoning: Threats Hiding in Plain Sight
Malicious ads and manipulated search results push users toward malware and phishing without email. Learn how malvertising and SEO poisoning work and how teams can reduce risk.
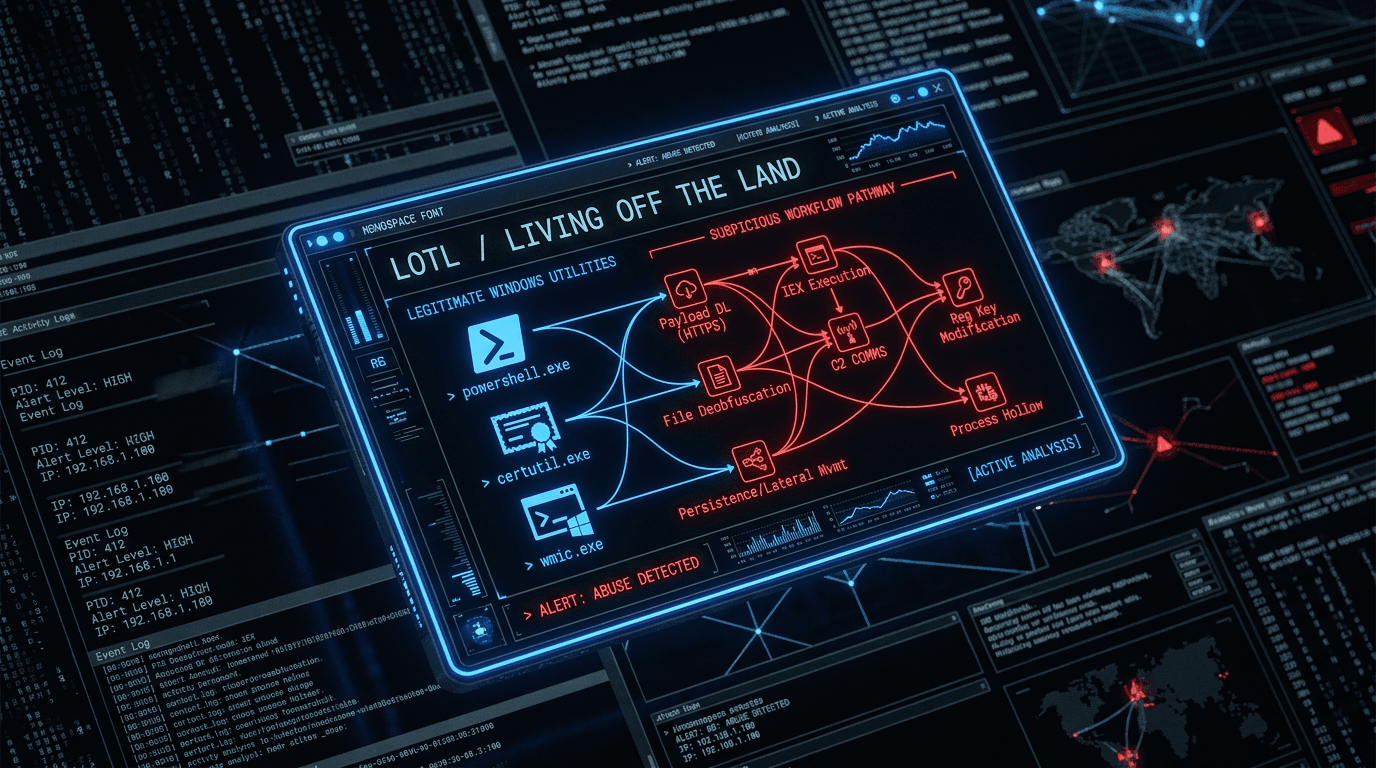
Living Off the Land (LOTL): Why “No Malware File” Still Means Breach
Attackers increasingly abuse built-in OS binaries and scripts to avoid dropping traditional malware. Understand LOTL tradecraft and what to log, detect, and hunt for.
The Splinternet: Navigating a Fragmented World Wide Web
The global internet is fracturing into regional, regulated intranets. We explore the rise of the "Splinternet" and its impact on cybersecurity and global business.
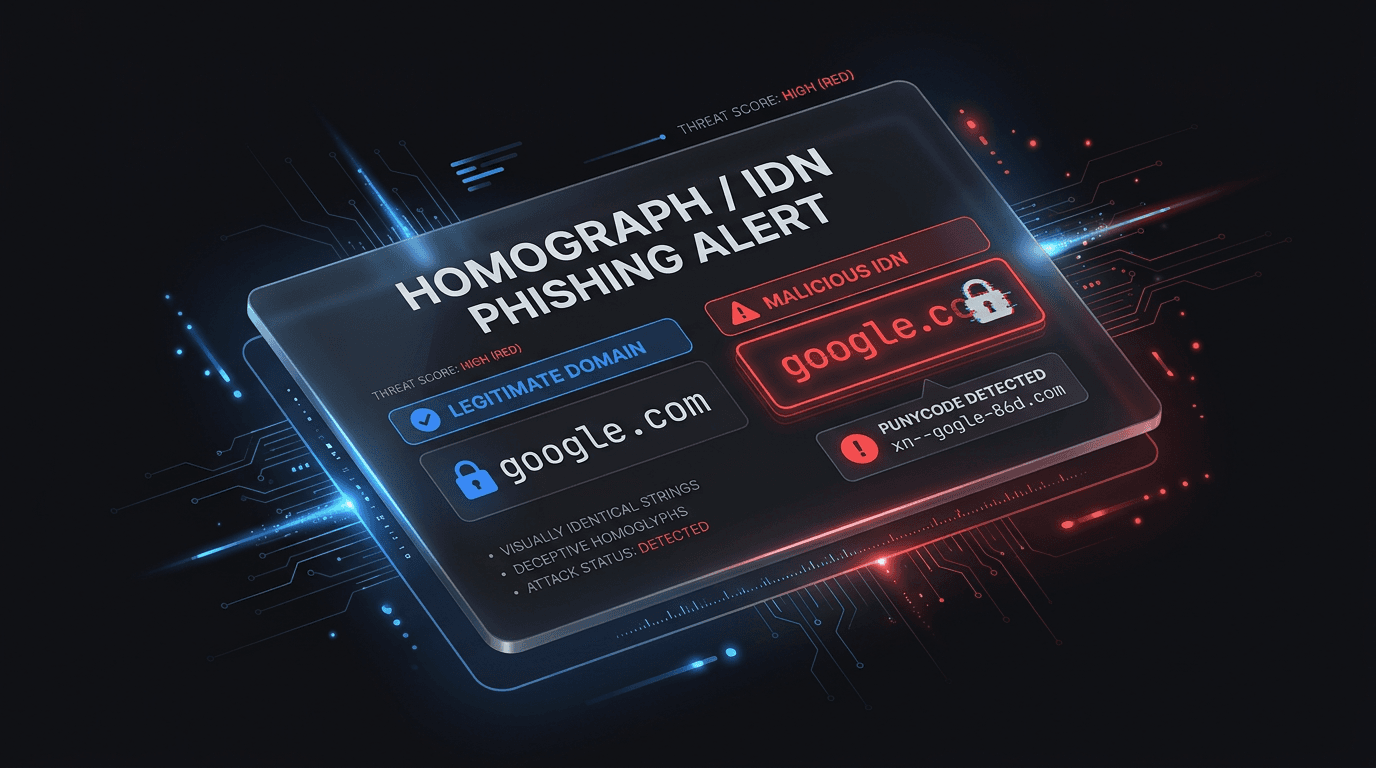
IDN and Homograph Phishing: When the Domain Looks Right But Is Wrong
Internationalized domain names and look-alike characters let attackers spoof trusted brands in the address bar. Learn how homograph attacks work and how to defend users and SOC teams.
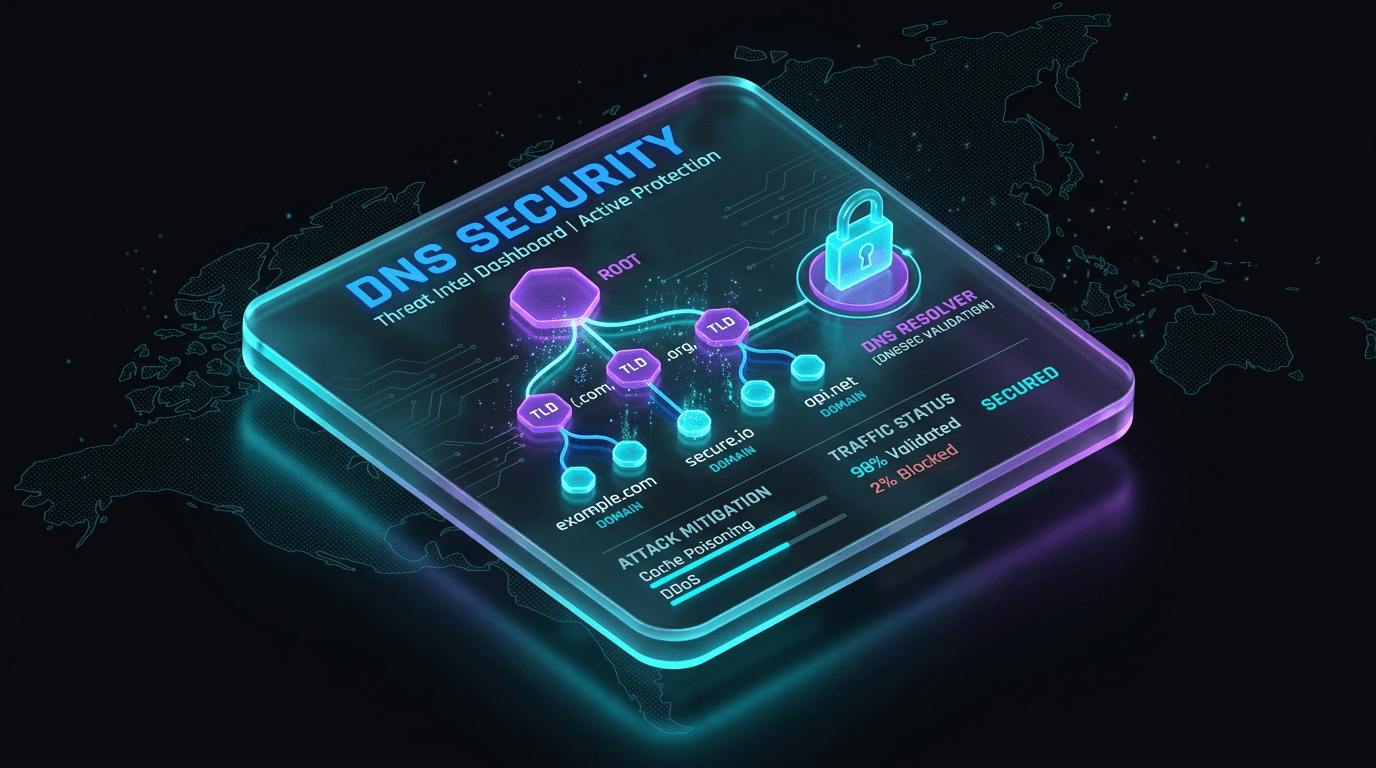
DNS Security: Poisoning, Hijacking, and Hardening That Actually Sticks
DNS is easy to ignore until it routes your users to malware. Learn how cache poisoning, hijacking, and secure DNS practices fit together.
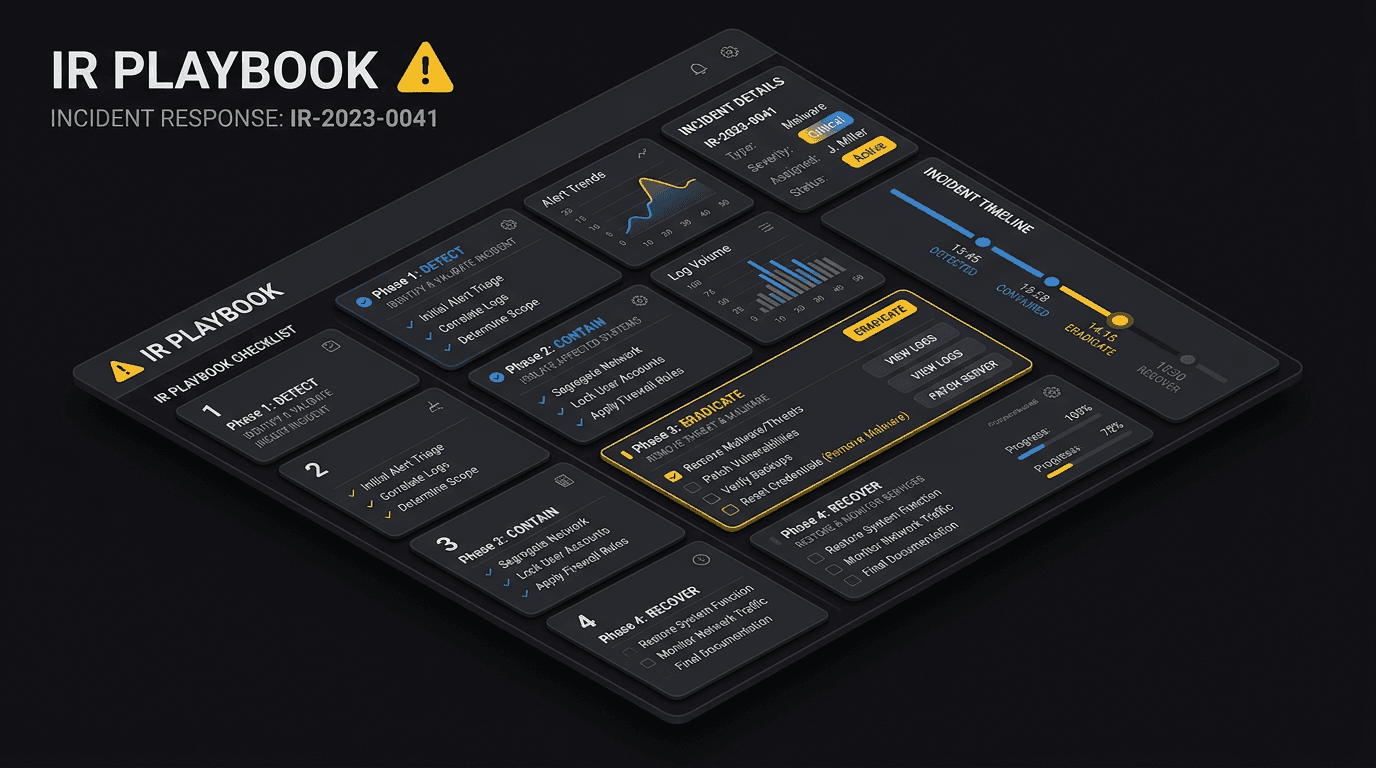
Incident Response Playbooks: Less PDF, More Rehearsal
A playbook nobody has run is fiction. Learn how to build IR phases, roles, and communications that work under pressure—and how to test them.

Steganography: Hiding Secrets in Plain Sight
Steganography hides data within innocent-looking files like images or audio. Learn how hackers use digital steganography to smuggle malware and steal data.
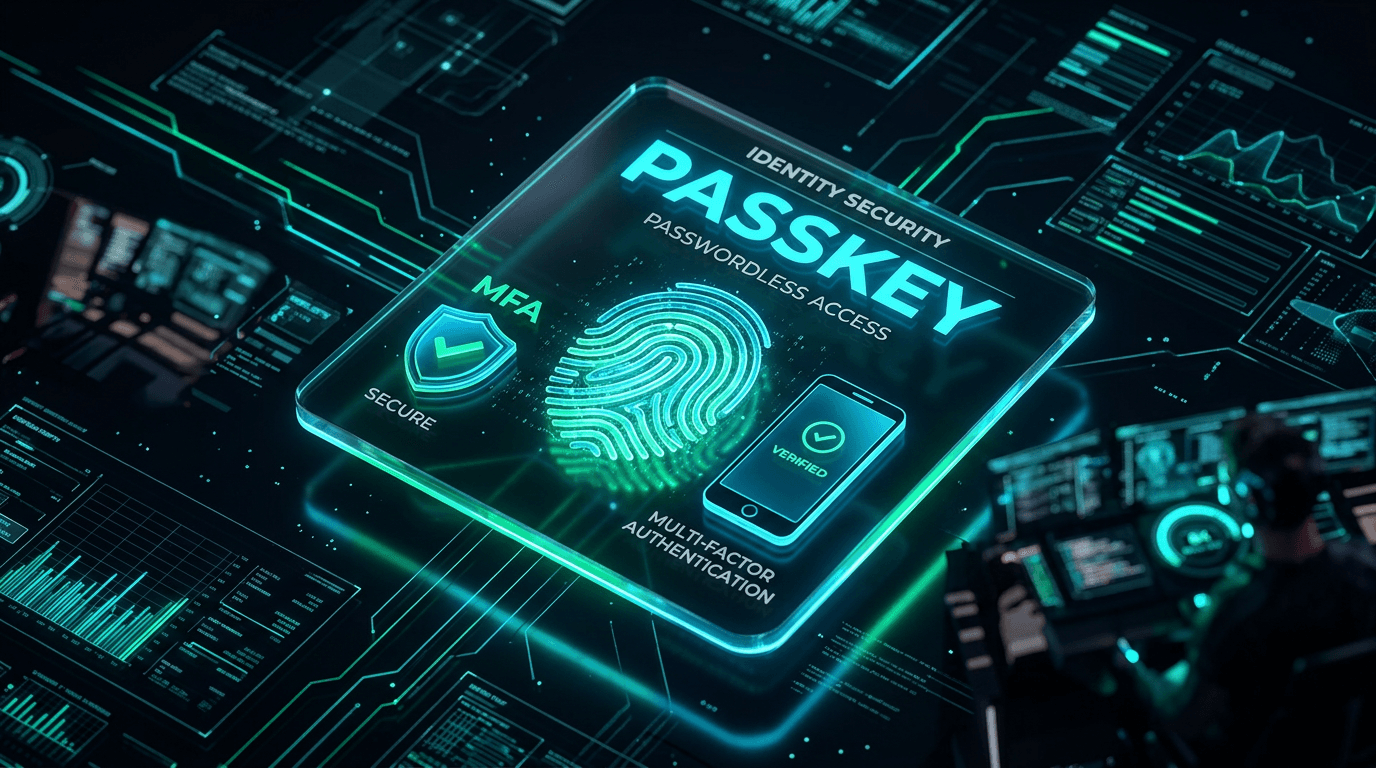
Identity Security in 2026: Passkeys, MFA, and Session Hijacking
Passwords are still everywhere, but phishing-resistant credentials and tight session controls are the real front line. Here is a practical identity roadmap.
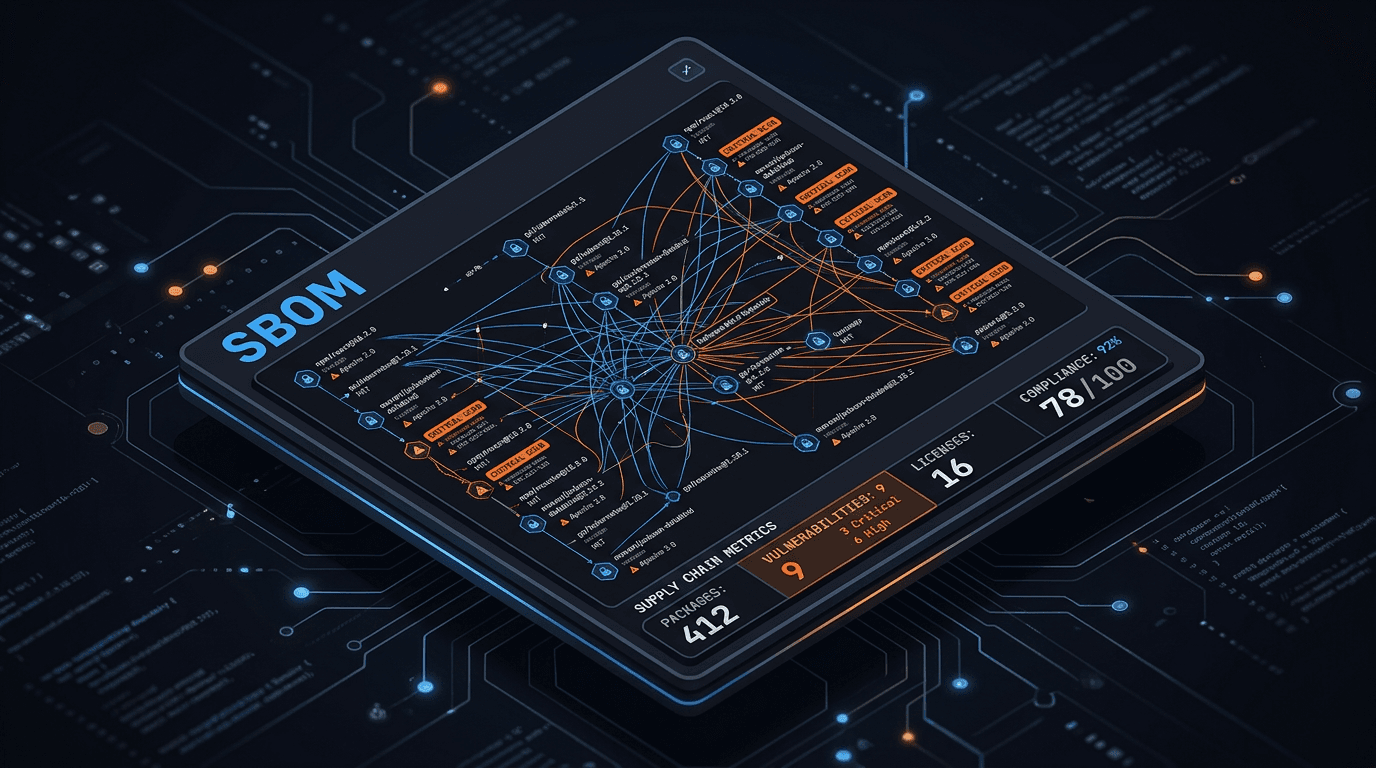
SBOM and Supply Chain Security: What Security Teams Actually Need
Software bills of materials are not paperwork for compliance alone. Learn how SBOMs reduce third-party risk and speed response when a dependency blows up.
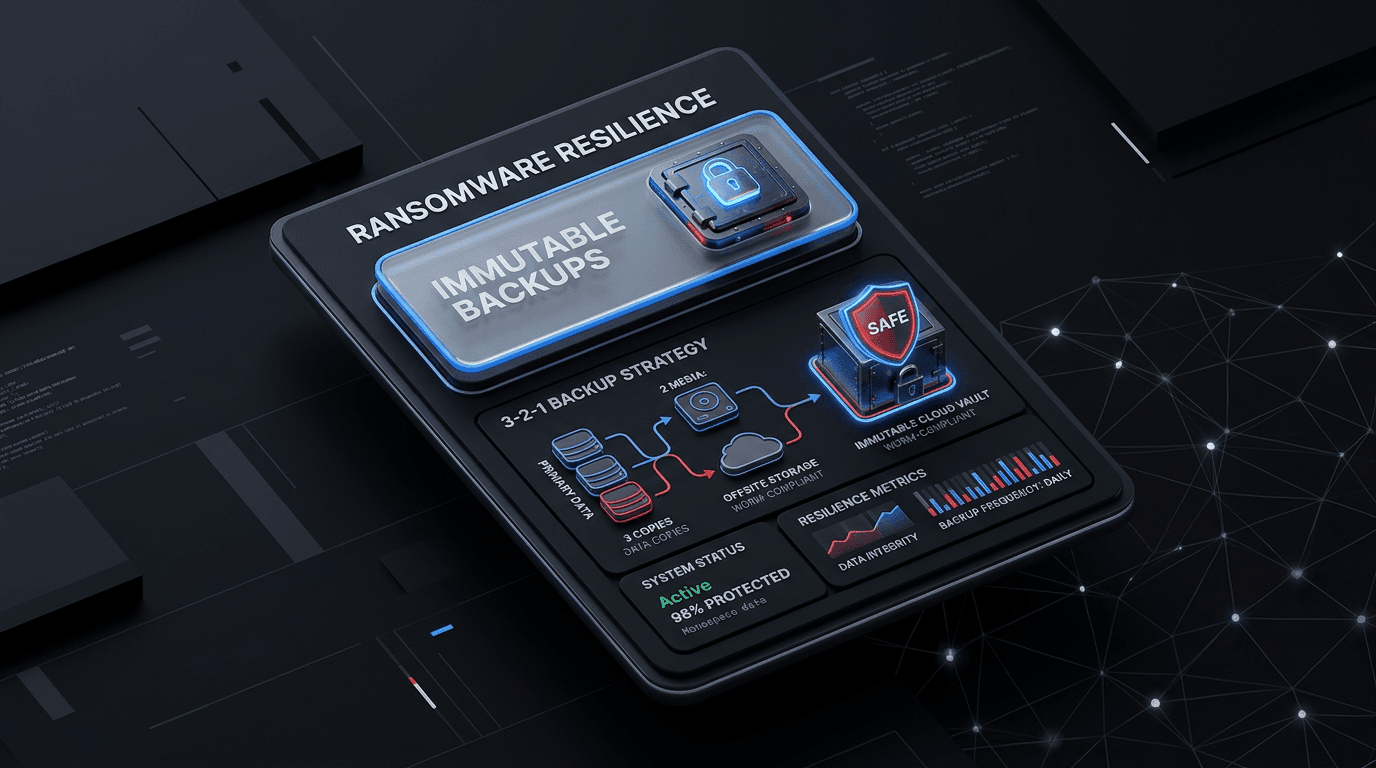
Ransomware Resilience: Why Immutable Backups Still Matter in 2026
Attackers target backups first. Learn how immutable storage, the 3-2-1 rule, and recovery drills turn ransomware from a business-ending event into a manageable incident.
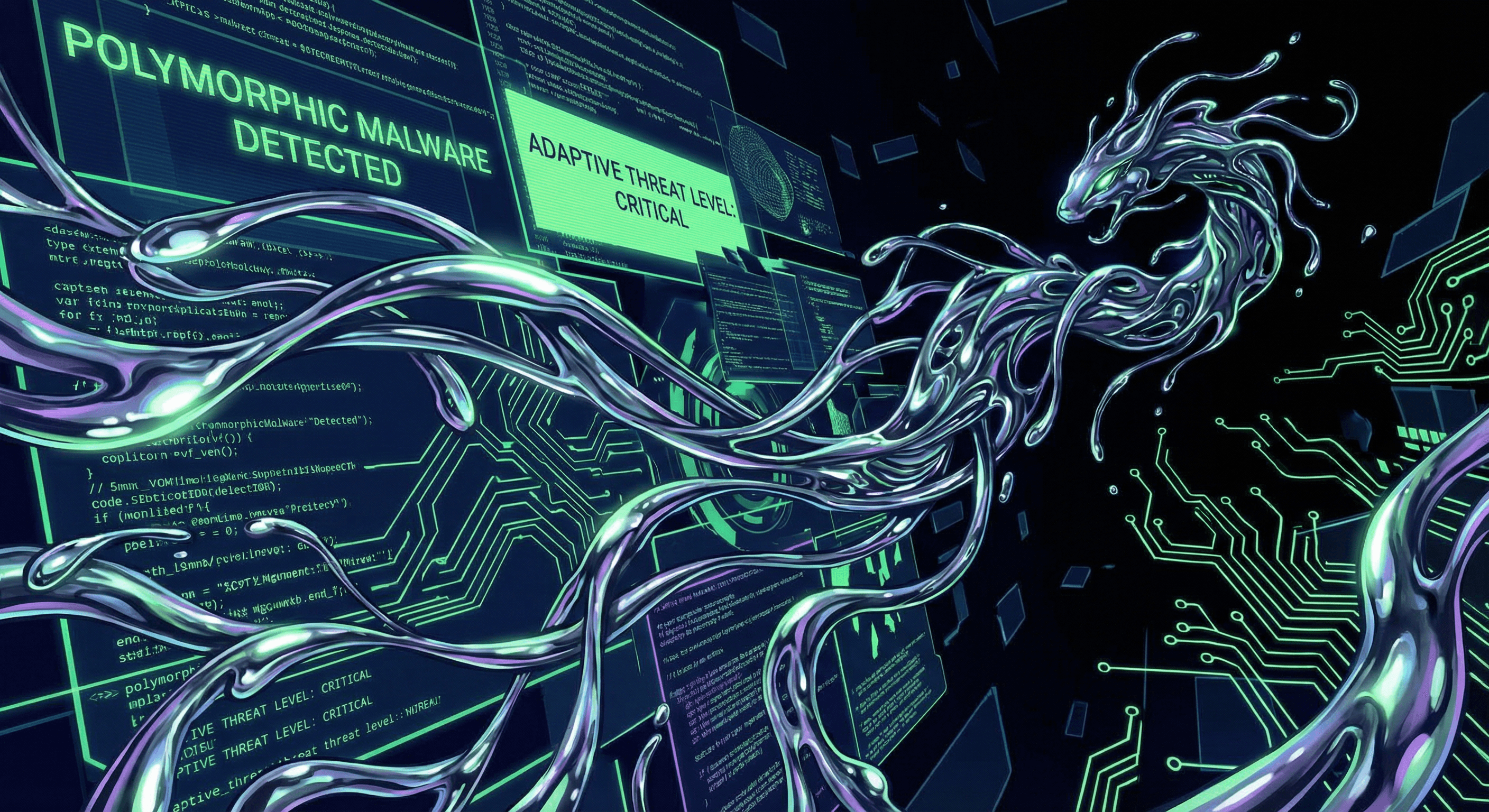
Polymorphic Malware: The Shapeshifting Code
Traditional antivirus relies on signatures, but polymorphic malware changes its code every time it replicates. Discover how this shapeshifting threat evades detection.
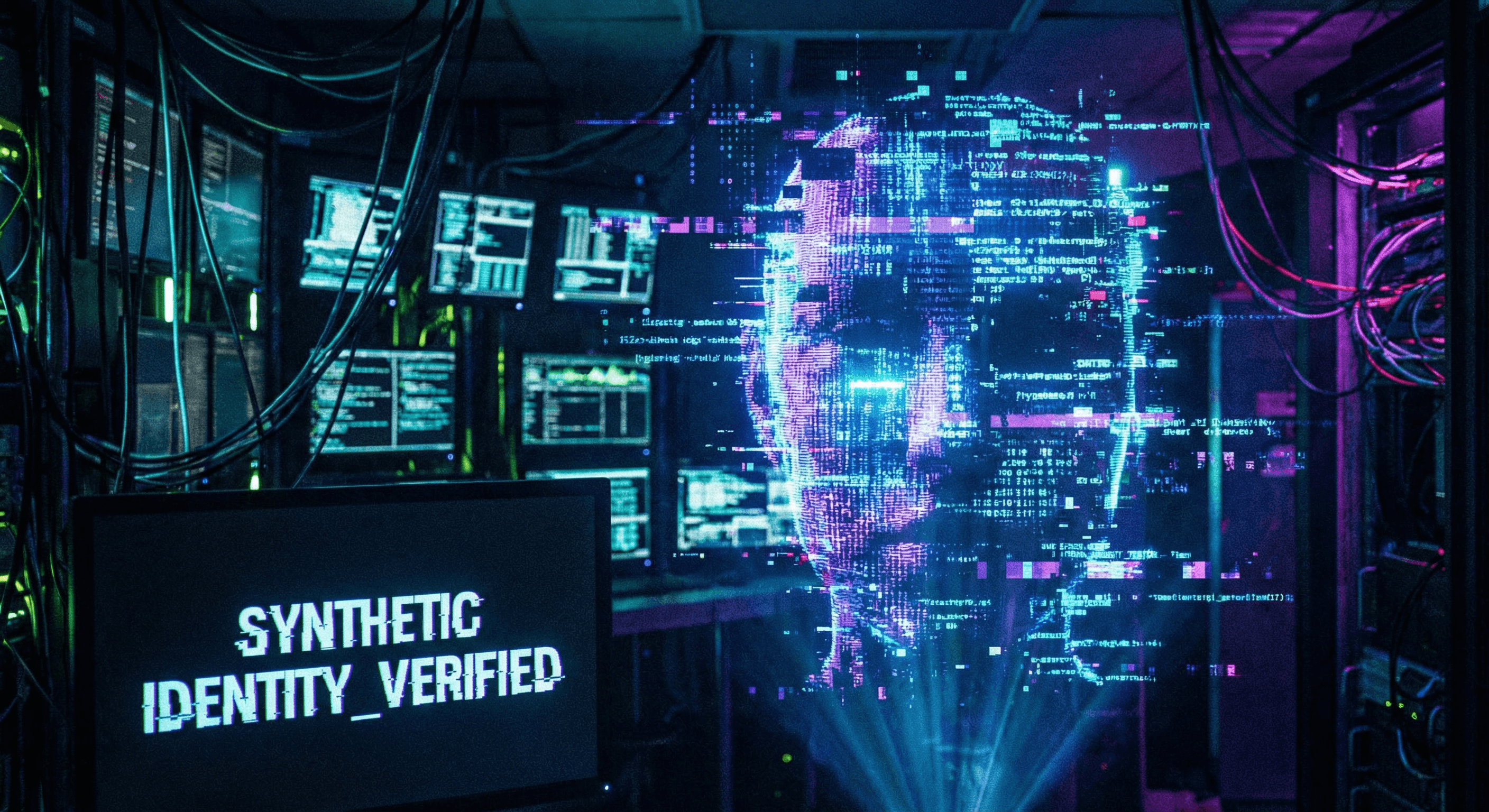
Synthetic Identity Fraud: The Ghost in the Machine
Synthetic identity fraud is the fastest-growing financial crime. Learn how criminals combine real and fake data to create "ghost" identities and how to detect them.
Preparing for Q-Day: Post-Quantum Cryptography Explained
Quantum computers threaten to break the encryption that secures the internet. Discover what Post-Quantum Cryptography (PQC) is and how to prepare for the quantum future.
Detecting the Enemy Within: Behavioral Analytics for Insider Threats
Insider threats are notoriously difficult to detect because the actor already has legitimate access. Learn how UEBA can help spot the subtle signs of malicious intent.
Botnets Explained: Is Your Computer Part of a Zombie Army?
Botnets are networks of infected devices controlled by cybercriminals. Find out how they work, what they do, and how to check if your IP is involved.
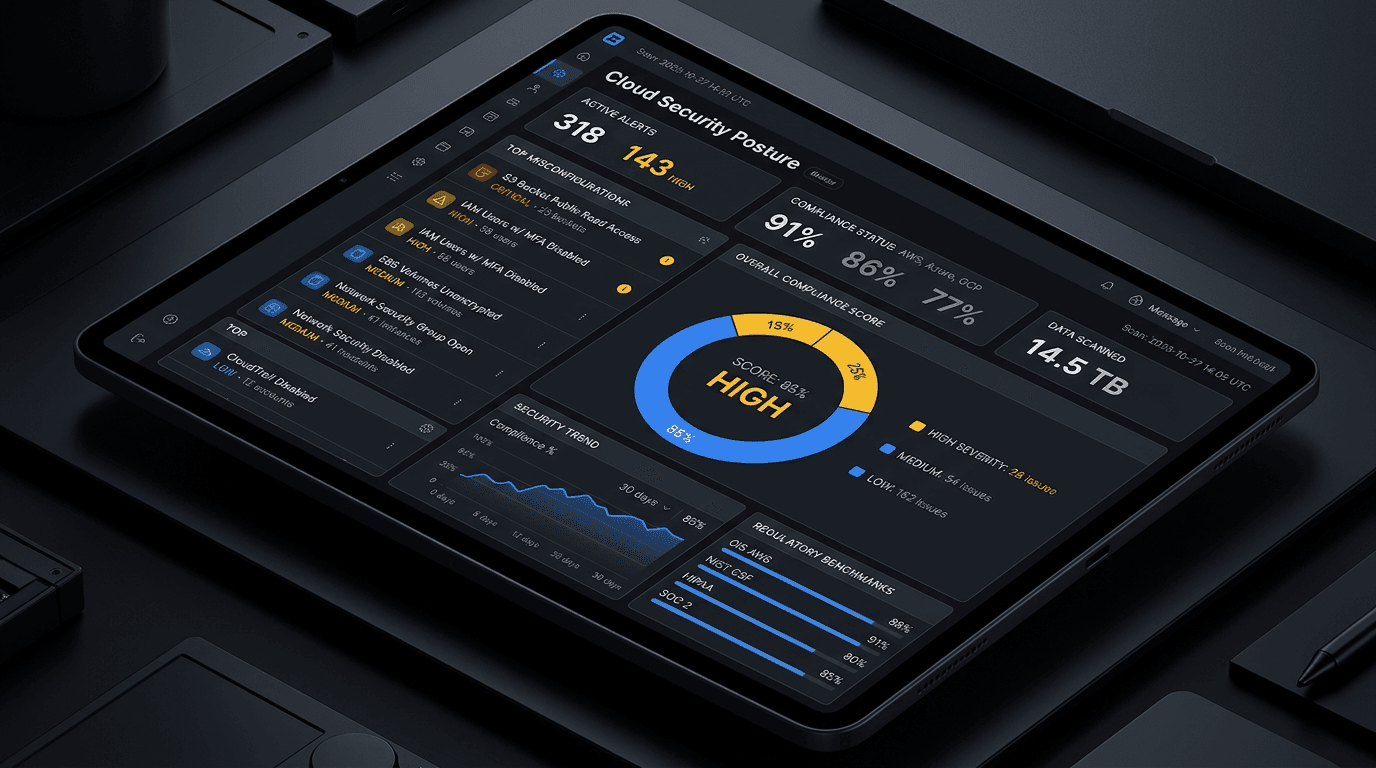
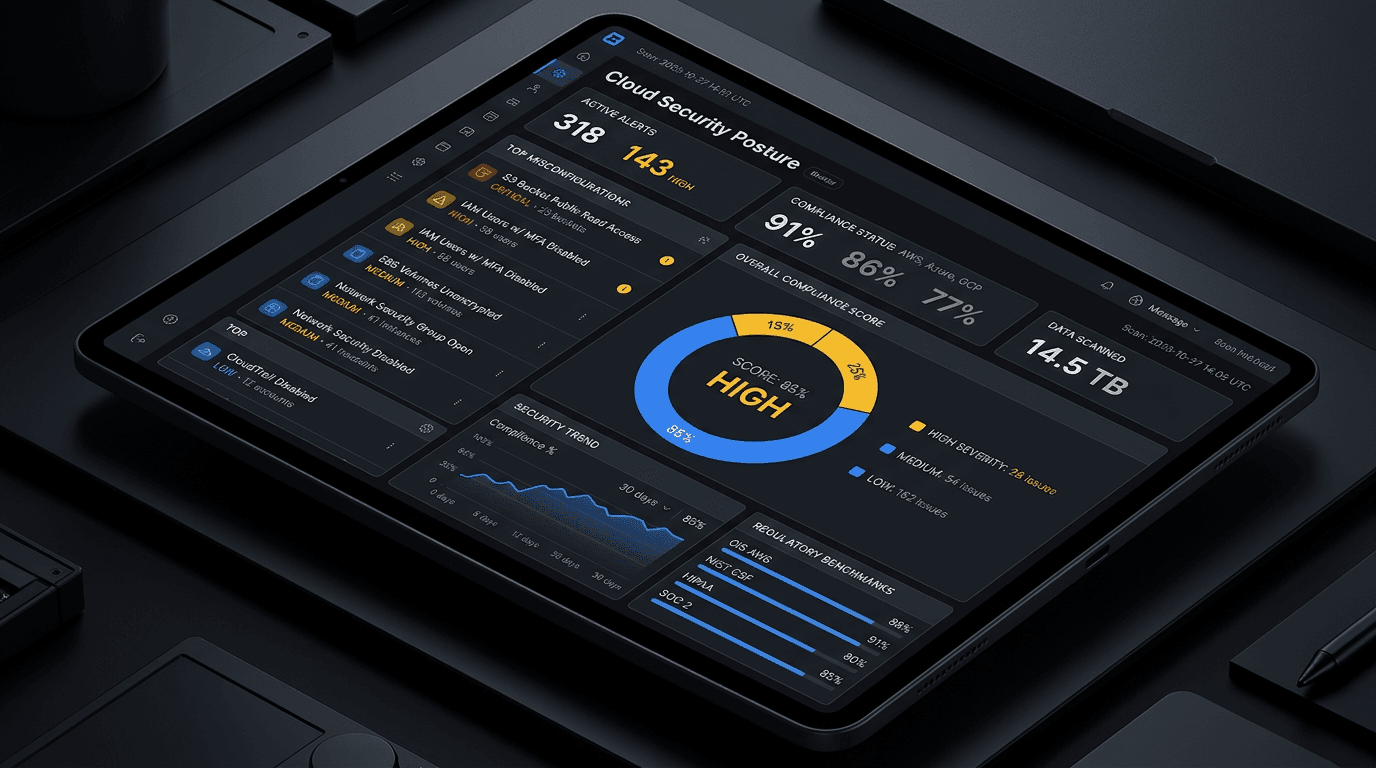
CSPM vs. CWPP: Decoding Cloud Security Acronyms
Cloud security is full of acronyms. We break down the difference between CSPM and CWPP and why you likely need both.
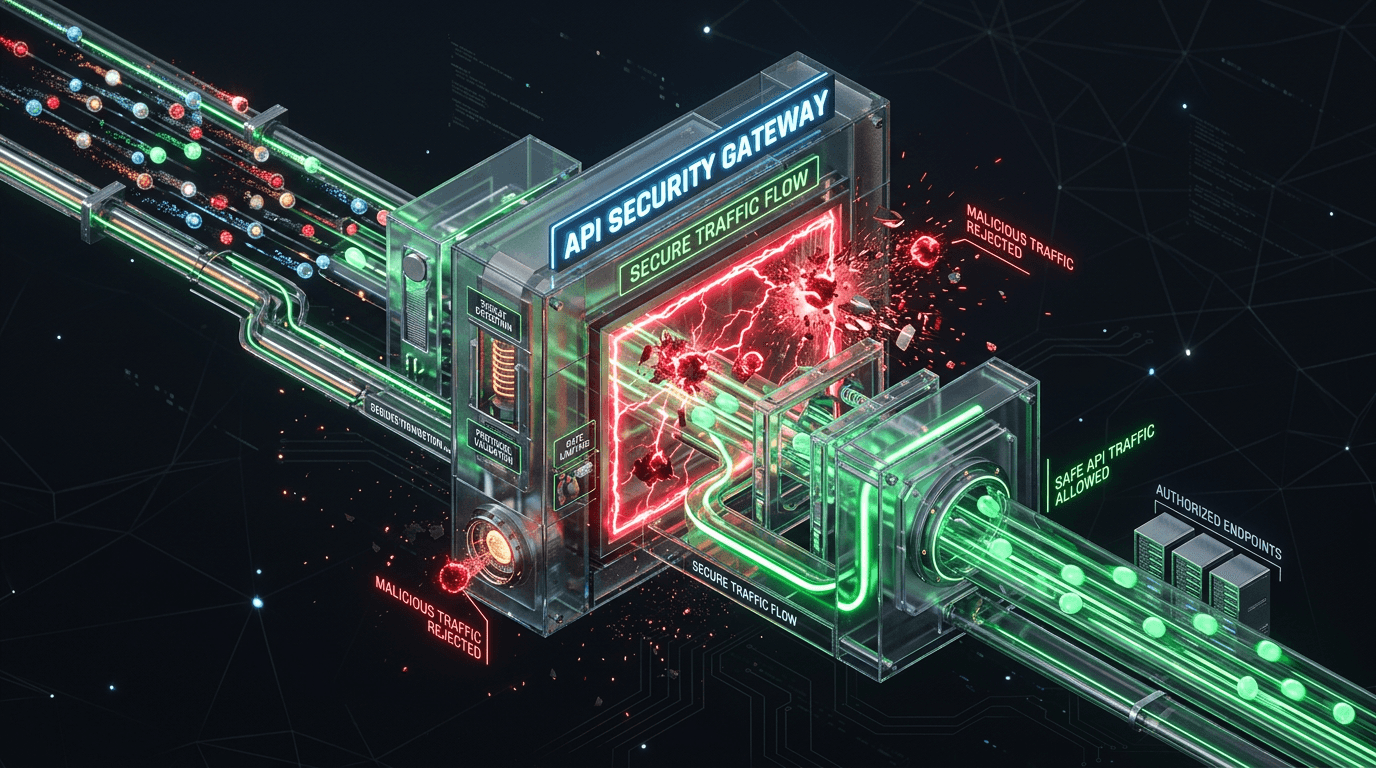
The Rise of API Attacks: Protecting the Modern Attack Surface
APIs are the connective tissue of the modern web, and they are under attack. Explore the unique vulnerabilities of APIs and how to secure them.
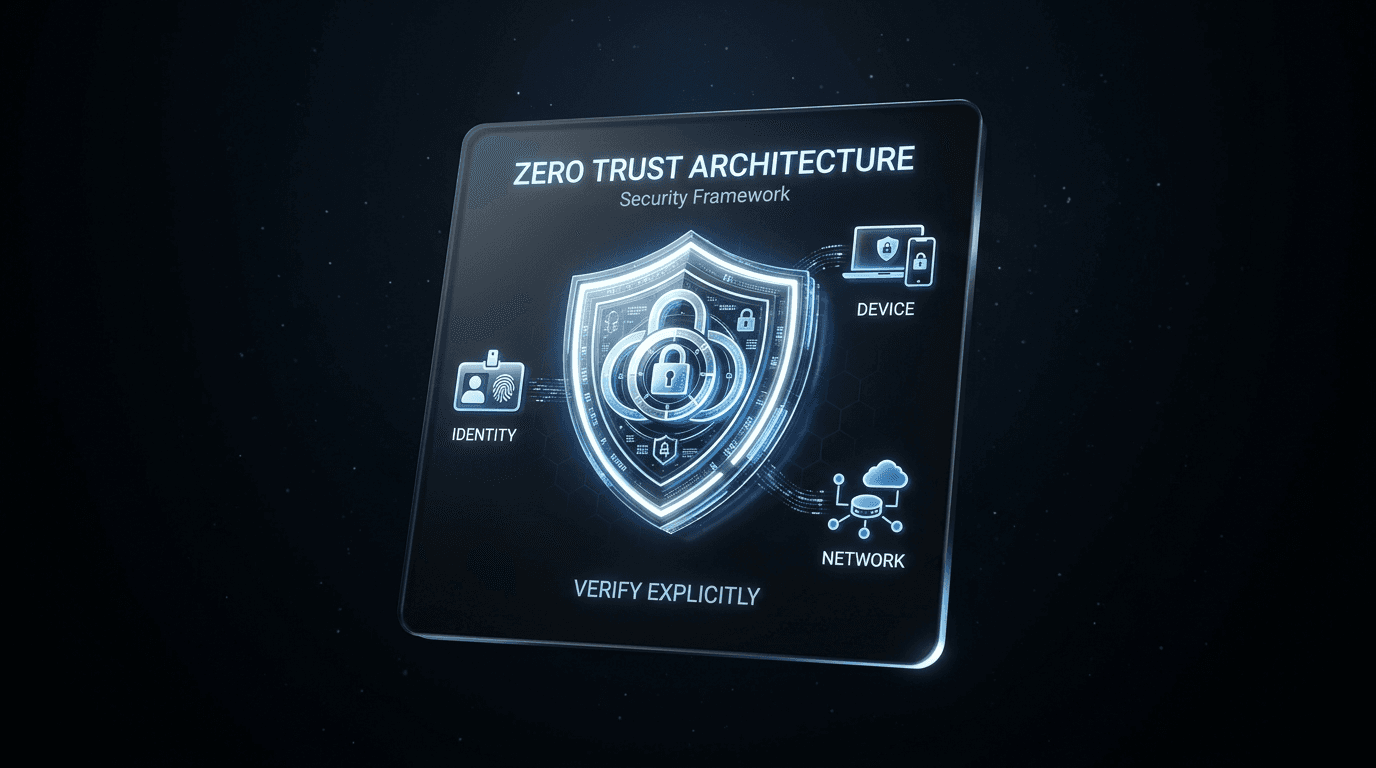
Implementing Zero Trust: Beyond the Buzzword
Zero Trust is not a product; it is a philosophy. Learn how to move beyond the marketing hype and implement a true "Verify Explicitly" architecture.
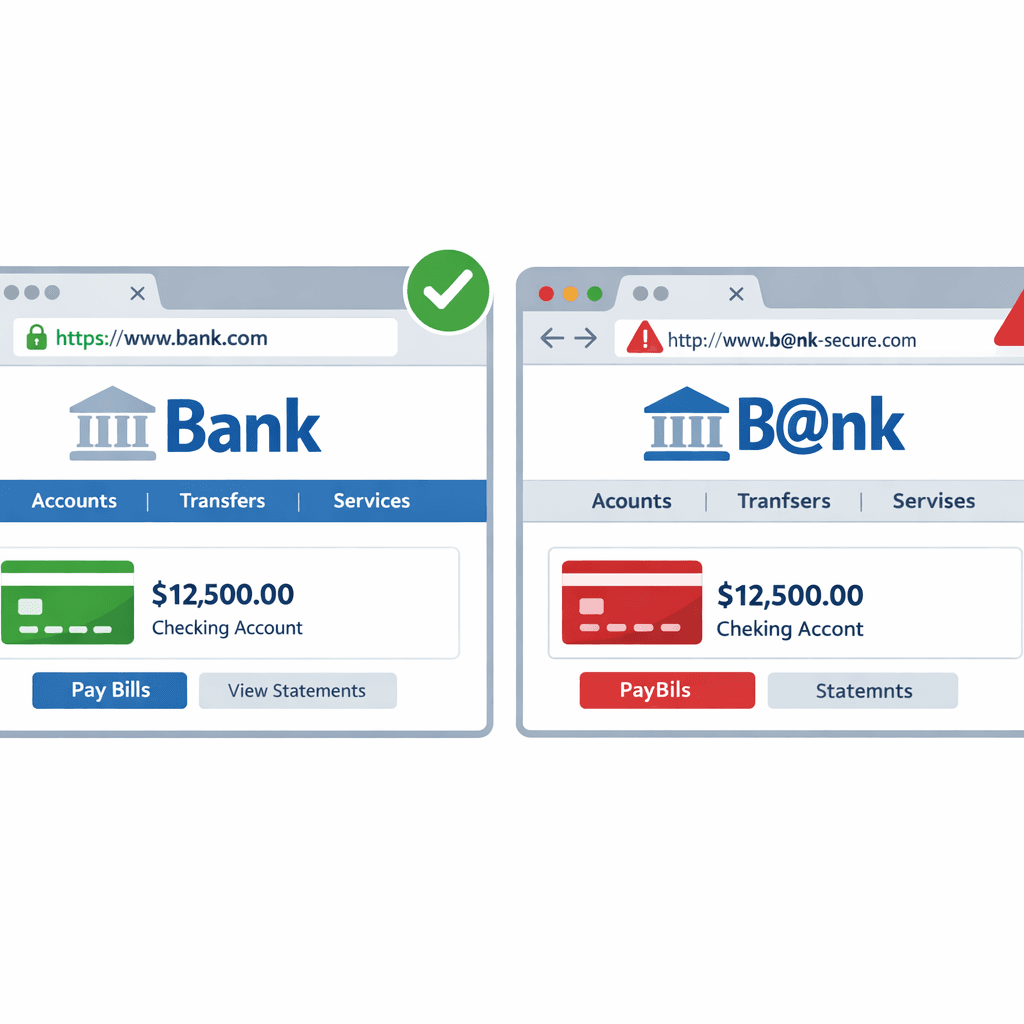
How Hackers Use "Typosquatting" to Trick You (and How to Spot It)
Typosquatting relies on your fingers slipping. Learn how attackers register look-alike domains to steal your data and how to check URLs before you click.
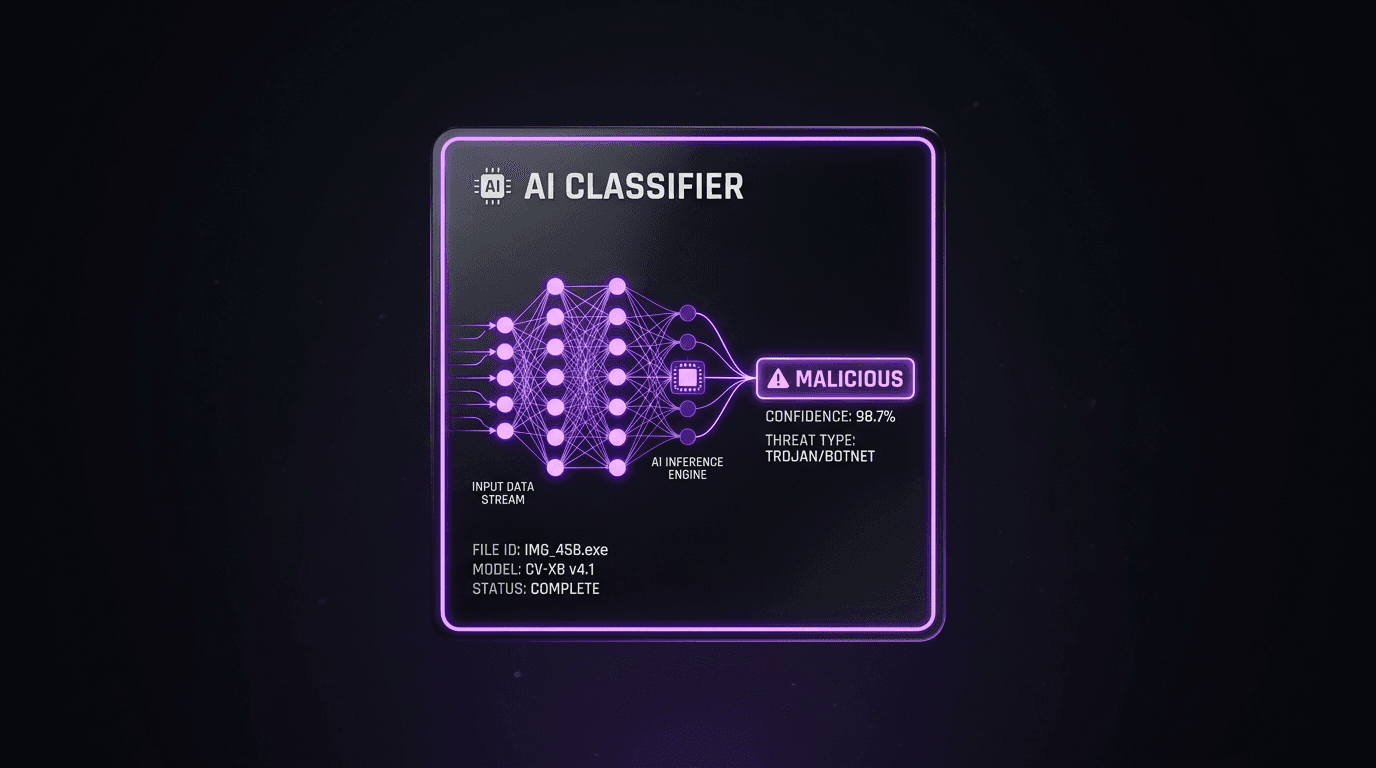
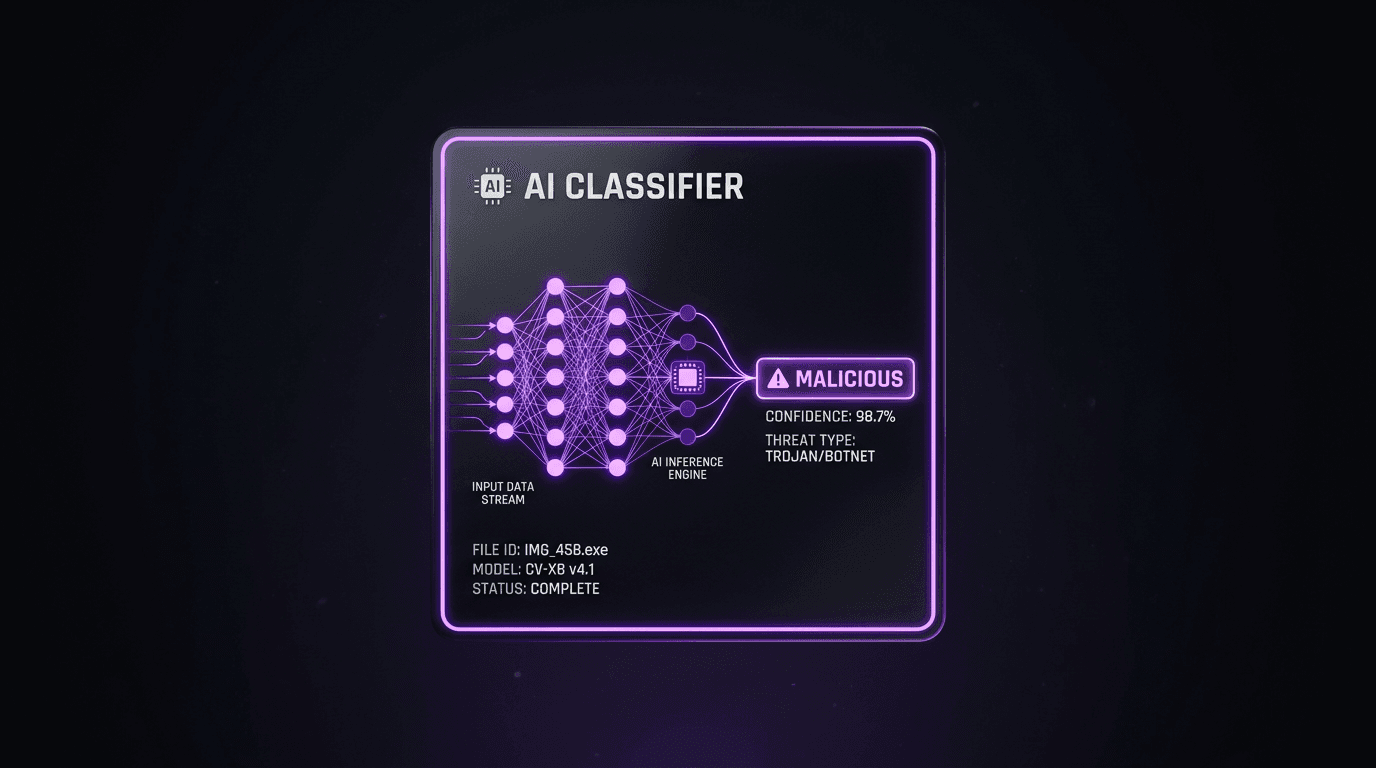
Automated Threat Classification using Machine Learning
Machine Learning is transforming how we classify threats. Discover how AI models can analyze vast amounts of data to categorize attacks instantly.
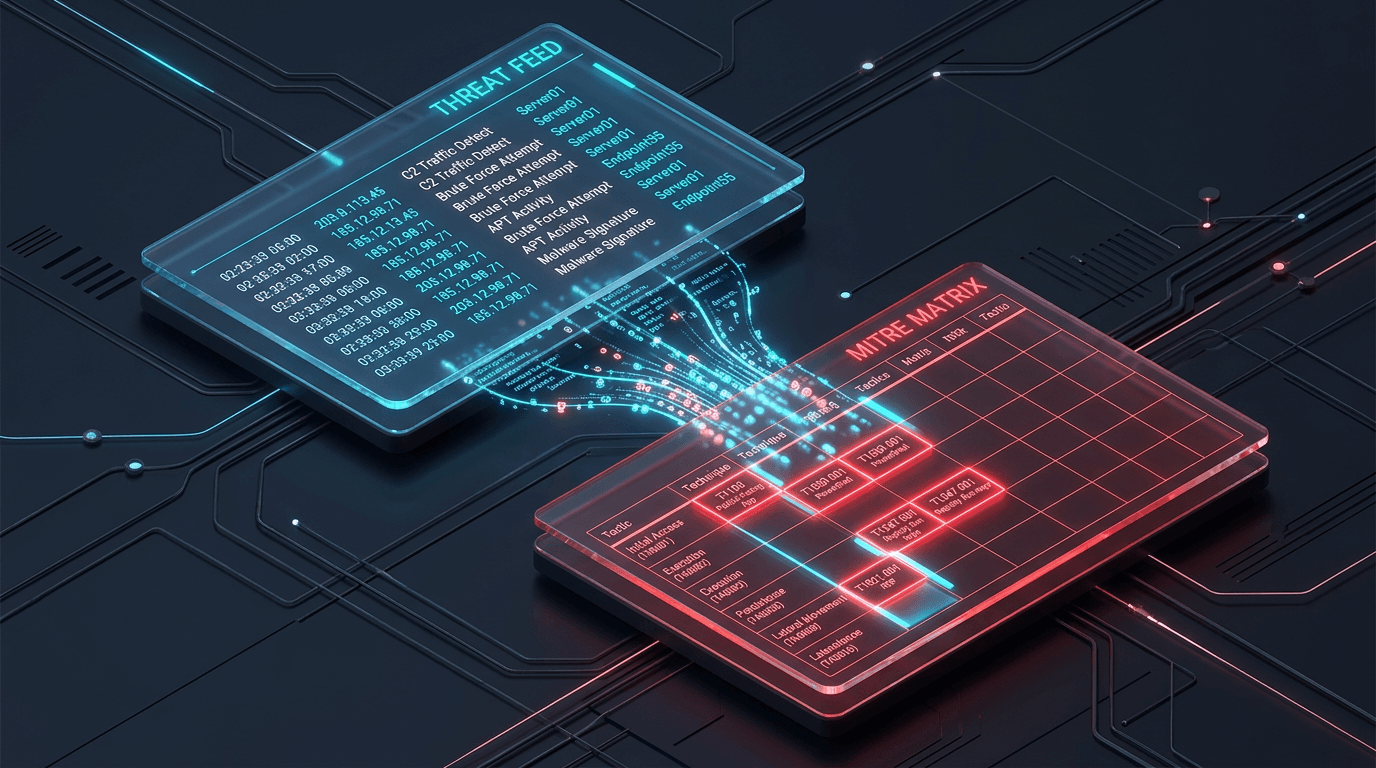
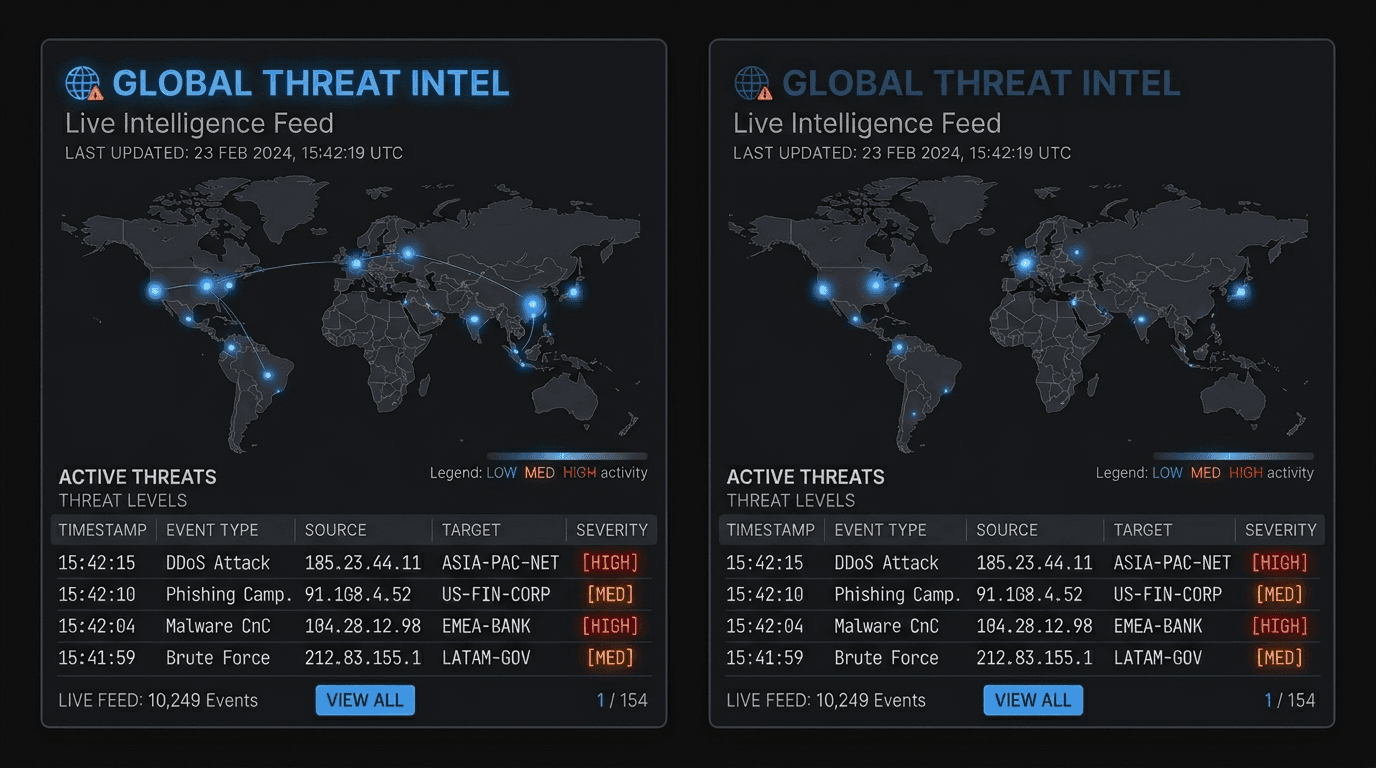
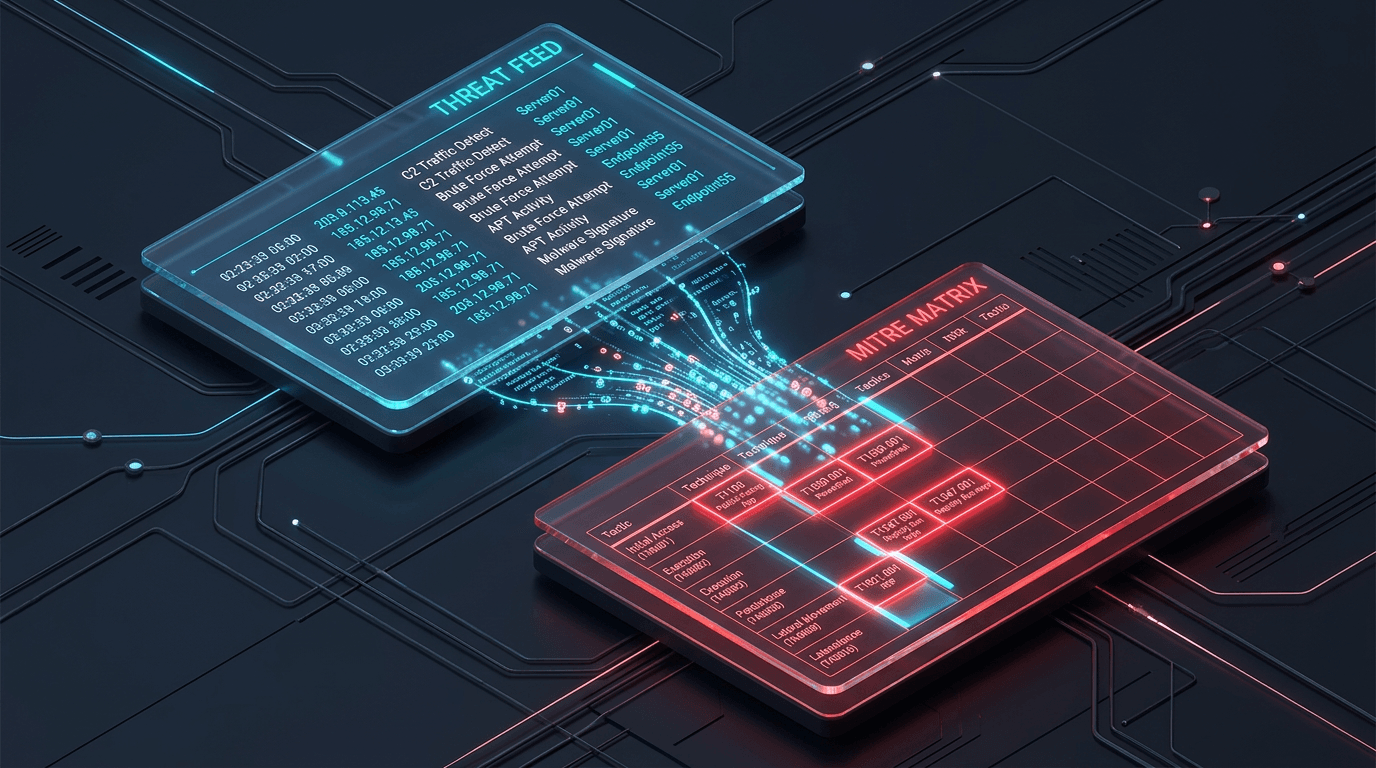
Integrating MITRE ATT&CK with Real-Time Threat Feeds
Bridge the gap between strategic frameworks and tactical defense. Learn how to map real-time threat feeds directly to the MITRE ATT&CK matrix.
The Evolution of Threat Intelligence in 2026
Threat intelligence has moved beyond simple blocklists. Explore how AI, context, and real-time integration are shaping the future of cyber defense.
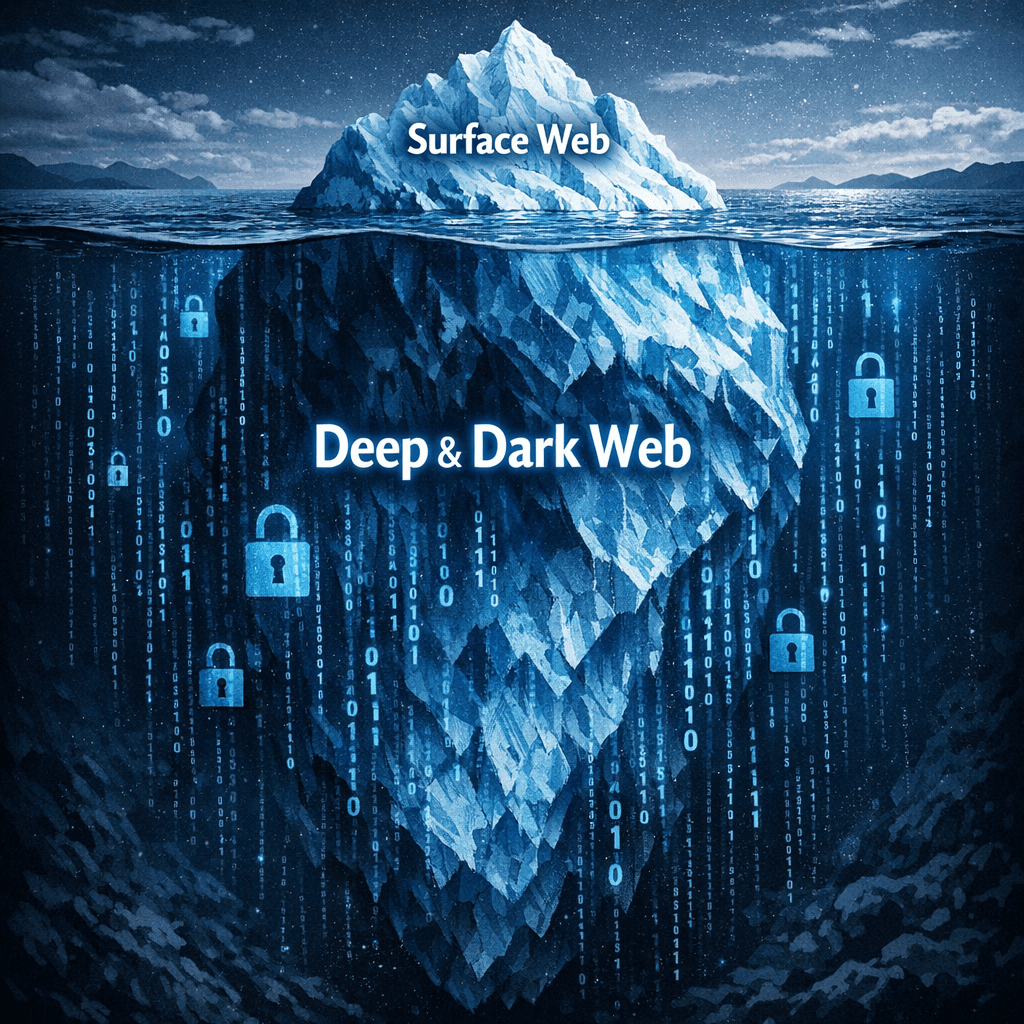
The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?
Confused by the Dark Web and Deep Web? We explain the difference and where cyber threats like stolen credentials and malware actually live.
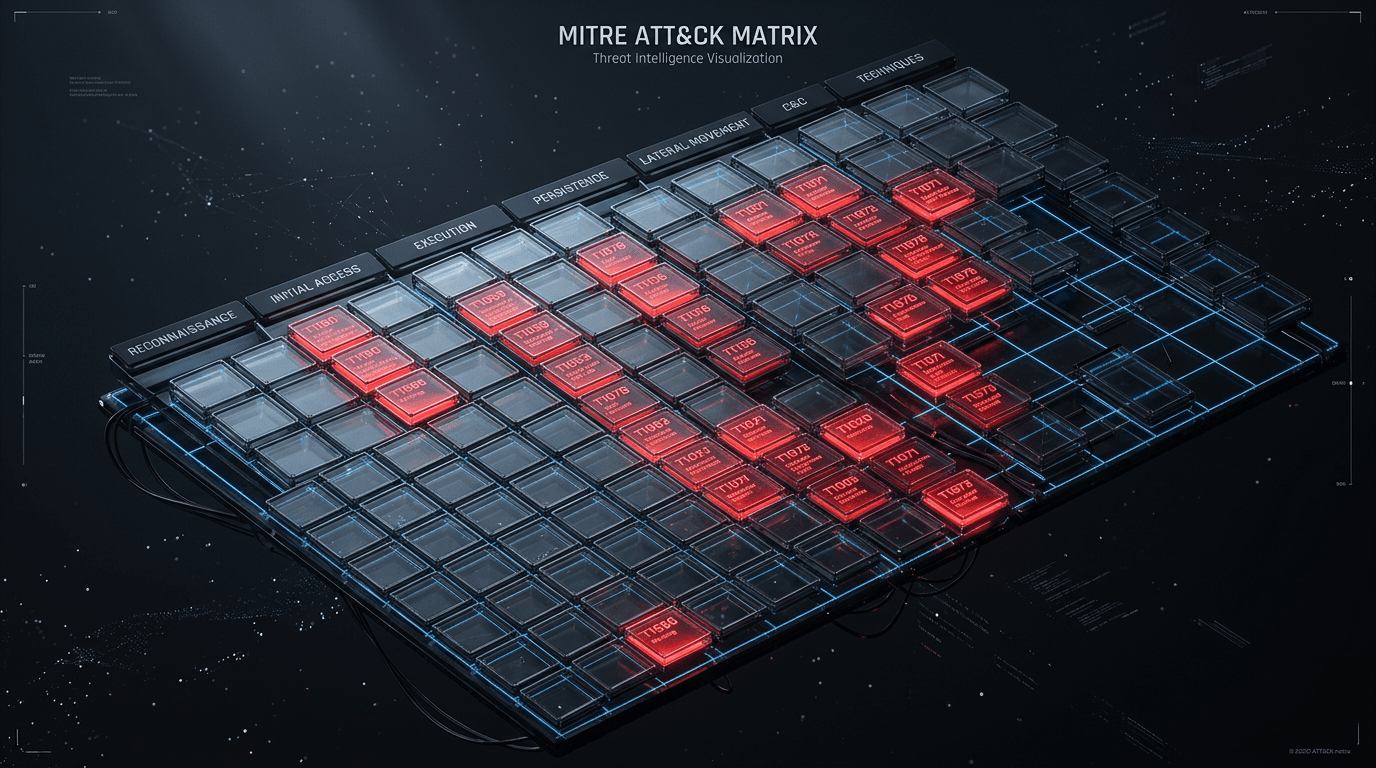
Mapping Your Defenses with MITRE ATT&CK
The MITRE ATT&CK framework is the gold standard for understanding adversary behavior. Discover how to map your defenses to specific techniques.
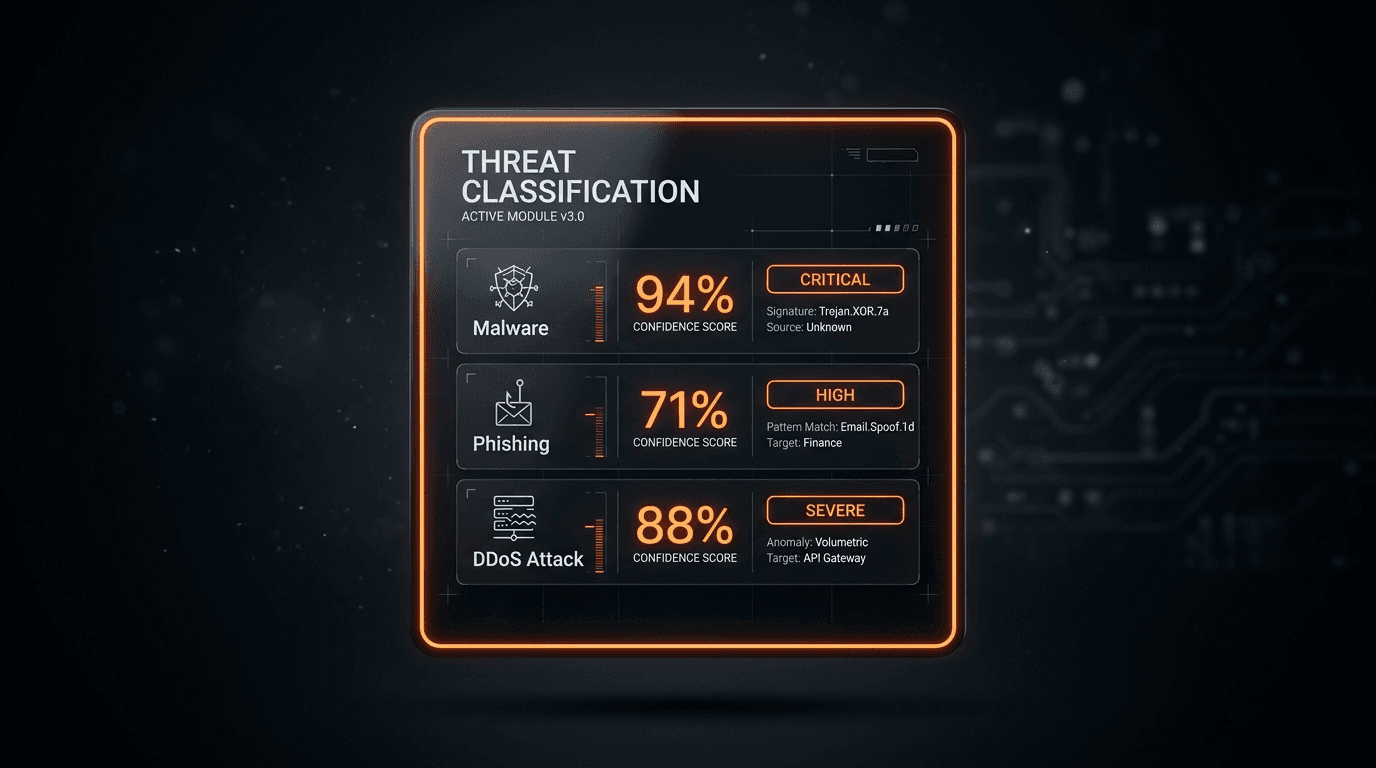
Understanding Threat Classification: A Guide for Modern SOCs
Effective threat classification is the cornerstone of a modern SOC. Learn how to categorize threats to streamline incident response and reduce alert fatigue.

Is Your Email Leaking Data? How to Check Email Reputation
Learn why email reputation matters for security and deliverability, and how to check if an email address is compromised or malicious.
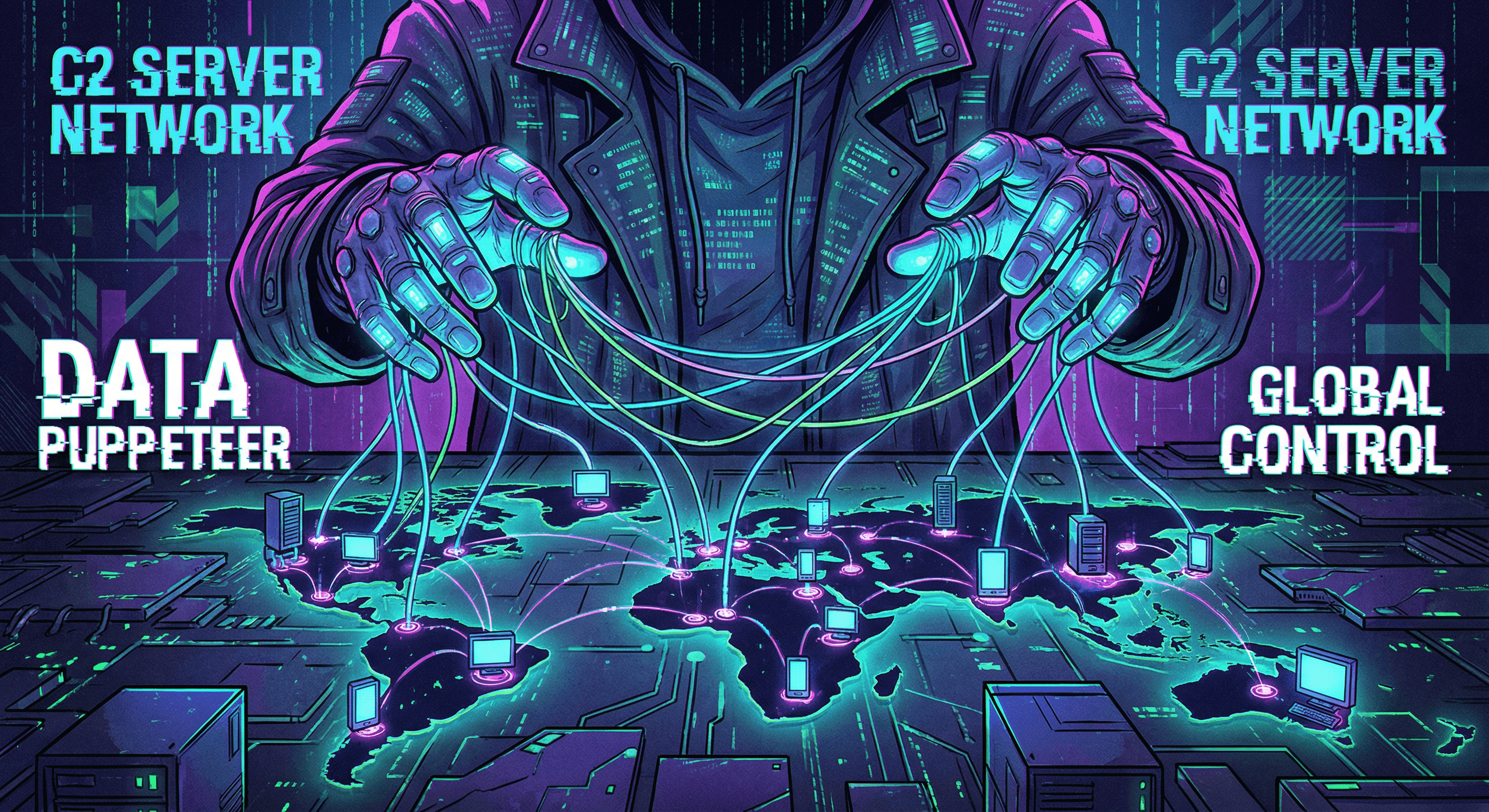
What is a C2 Server? The Invisible Puppet Masters of the Internet
Discover how hackers control infected devices using Command and Control (C2) servers and how to detect these hidden threats.
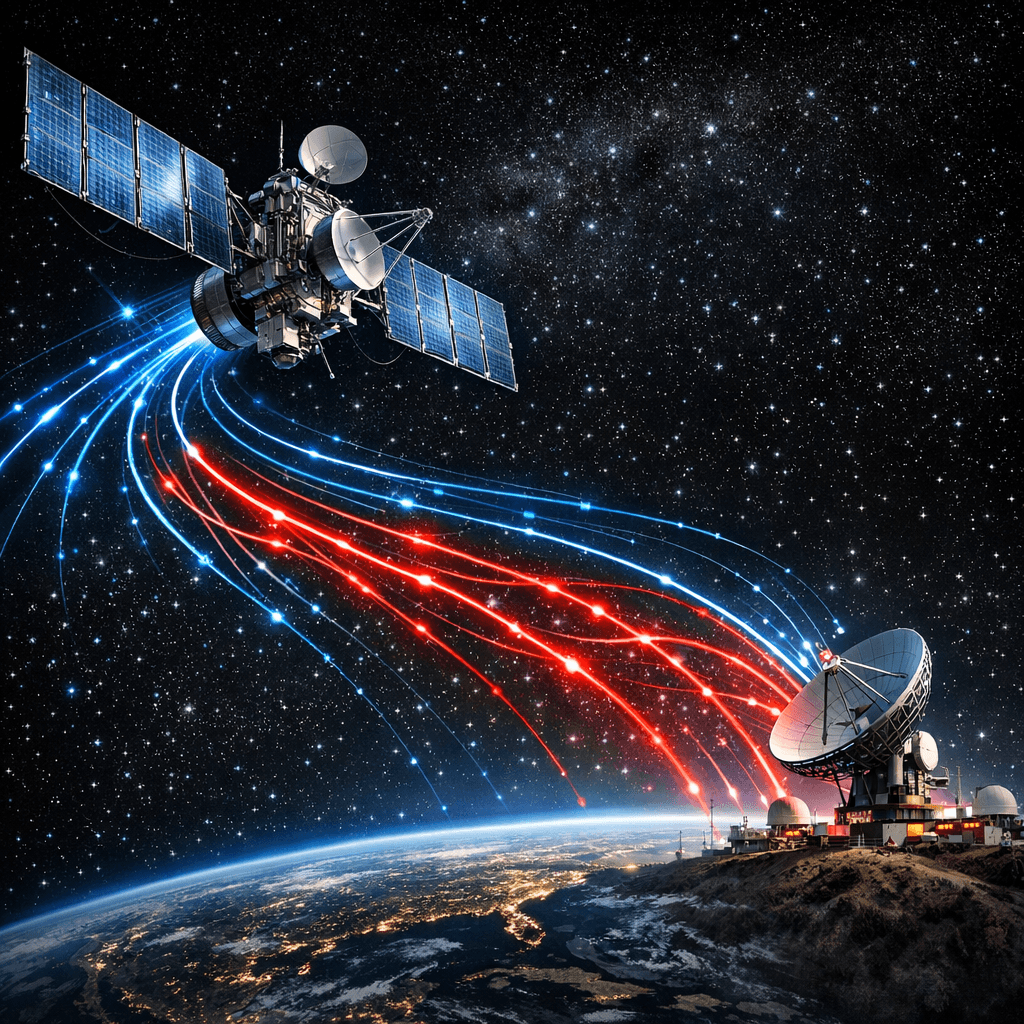
Space Systems Cyber Threats: Securing the Final Frontier
As space becomes accessible, it becomes a target. From satellite hijacking to ground station jamming, we analyze the unique threats to orbital assets and how threat intelligence secures the new space race.
Command & Control Infrastructure: Detecting C2 Traffic Before It Is Too Late
Once malware establishes a C2 channel, attackers have a persistent foothold in your environment. Understand how C2 infrastructure is built, how beacons evade detection, and how to identify malicious outbound connections using threat intelligence.
Metaverse Security: Privacy and Identity in Virtual Worlds
As the enterprise Metaverse expands, so does the attack surface. From avatar impersonation to spatial data theft, we explore the new frontier of virtual threats and how IP reputation protects digital assets.
Threat Intelligence Sharing: How Organizations Fight Back Together
No single organization can monitor every threat alone. Learn how information sharing communities (ISACs), standard protocols like STIX/TAXII, and commercial threat feeds form a collaborative shield against adversaries.
Detecting VPNs, Proxies & Tor: The Hidden Threat in Anonymized Traffic
Legitimate users rarely hide behind Tor or anonymous proxies. Discover how attackers exploit anonymization layers to bypass defenses, and how IP intelligence helps you unmask high-risk traffic in real-time.
Credential Stuffing Attacks: Why Stolen Password Lists Keep Working
Billions of breached username/password pairs are actively weaponized every day. Learn how credential stuffing differs from brute force, why it succeeds at scale, and how to stop it using IP reputation and anomaly detection.
Drone Defense Security: Mitigating Unauthorized UAV Threats
Unauthorized drones pose a threat to critical infrastructure, stadiums, and prisons. This post explores Counter-Unmanned Aircraft Systems (C-UAS), detection methods, and how strict "no-fly" zones are enforced electronically.

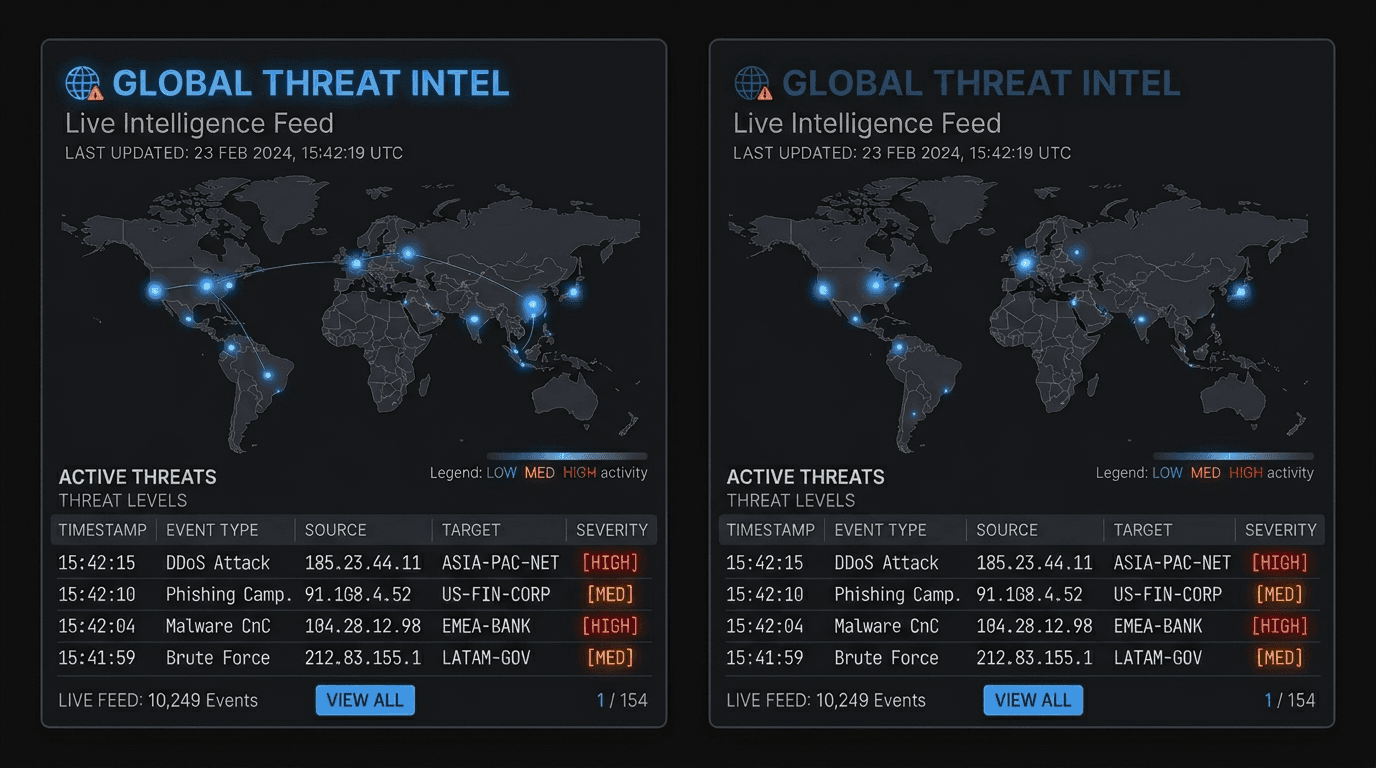
Building a Custom SOC Dashboard: Integrating Real-Time Threat Feeds
Enhance your Security Operations Center visibility. A step-by-step guide to aggregating threat data, enriching logs, and building custom security dashboards using modern Threat Intelligence APIs.

Why Your SaaS Needs to Block Disposable Email Addresses Immediately
Disposable and temporary email addresses are the gateway for fraud, spam, and abuse. Learn how implementing a robust email verification API protects your user base and improves your sender reputation.
How to Automate Malicious IP Blocking with Threat Intelligence APIs
Stop relying on static blocklists. Learn how to integrate real-time threat intelligence APIs into your firewalls and application logic to automatically detect and block malicious IP addresses before they strike.
Smart City Security: Protecting Critical Infrastructure from Cyber Attack
Connected traffic lights, sensors, and water systems create a vast attack surface in modern cities. We examine the vulnerabilities of smart city infrastructure and the cascading failures a cyberattack could cause.
Domain Reputation Scoring: The First Line of Defense Against Phishing
Not all domains are created equal. Discover how real-time domain reputation scoring helps organizations proactively identify and block phishing infrastructure, fake websites, and parked domains used by cybercriminals.

Biometric Spoofing: Defeating Authentication in an AI World
Are fingerprints and facial recognition truly secure? We explore the techniques attackers use to spoof biometric sensors, from 3D-printed faces to synthetic voice cloning.

Industrial Control Systems (ICS) Malware Trends: The OT/IT Convergence Risk
Operational Technology (OT) environments are under siege. We analyze the latest ICS-specific malware strains targeting PLCs and SCADA systems, and offer defense strategies for critical infrastructure.

Satellite Internet Security: Vulnerabilities in Low Earth Orbit (LEO)
Attack surfaces expand vertically as LEO constellations integrate with enterprise networks. This post details orbital jamming, ground station spoofing, and the lack of encryption standards in commercial satellite systems for security engineers.

Quantum Computing Threats to Encryption: A 2026 Perspective
As quantum supremacy nears, the threat to RSA and ECC encryption becomes existential. This analysis explores Post-Quantum Cryptography (PQC) migration strategies for security teams and the immediate risks of Harvest Now, Decrypt Later (HNDL) attacks.
Penetration Testing vs. Vulnerability Scanning: What's the Difference?
Often confused, these two security practices serve very different purposes. Discover when to use automated scanning and when to invest in a manual penetration test.

isMalicious vs VirusTotal: A Modern Threat Intelligence Alternative
Comparing isMalicious and VirusTotal for threat intelligence. Discover which IP and domain reputation API is right for your security stack — from pricing and features to real-time streaming and monitoring.

Building an Effective Incident Response Plan: A Step-by-Step Guide
When a cyberattack strikes, panic is your enemy. Learn how to create and test an incident response plan to ensure your team knows exactly what to do.

isMalicious vs AbuseIPDB: IP Reputation and Beyond
AbuseIPDB is the go-to for IP reputation, but what about domains and URLs? Compare isMalicious and AbuseIPDB across coverage, API features, pricing, and monitoring to find the right threat intelligence tool for your stack.

Cyber Threats 101: Understanding Online Dangers
A beginner's guide to common cyber threats. Understand malware, viruses, and hackers, and learn how to protect yourself online.

How to Check IP Reputation: Is That IP Address Safe?
Learn how to check if an IP address is malicious. A simple guide for beginners to understand IP reputation and stay safe online.

IAM Best Practices: Securing Identity and Access
Identity is the new perimeter. Discover specific best practices for Identity and Access Management (IAM) to prevent unauthorized access and privilege escalation.

Malicious Domains vs. Safe Sites: How to Tell the Difference
Can you tell a malicious domain from a safe one? Learn the key differences and tools to verify website safety instantly.
Phishing Explained: How to Check a Domain for Threats
What is phishing? Learn how to spot fake websites and check domains for threats before you enter your personal information.

Safe Browsing Guide: How to Check URLs for Hidden Threats
Don't click that link yet! Learn how to check URLs for hidden threats and ensure safe browsing on any device.

isMalicious vs AlienVault OTX: Threat Intelligence Without Vendor Lock-In
AlienVault OTX offers a free threat intelligence community, but full value requires the AT&T ecosystem. Compare isMalicious and OTX on API access, integrations, and vendor independence for your security stack.

Healthcare IoT Security: The Critical Risk to Patient Safety
Connected medical devices (IoMT) introduce life-critical vulnerabilities into hospital networks. From MRI machines to insulin pumps, this guide analyzes the unique challenges of securing legacy firmware and unpatched operating systems.

isMalicious vs Shodan: Threat Reputation vs Attack Surface Discovery
Shodan maps internet-connected devices. isMalicious checks if IPs and domains are malicious. Compare these complementary threat intelligence tools across features, use cases, and pricing to choose the right one.

The Deepfake Threat: Protecting Enterprise Security in the Era of AI
AI-generated video and audio are becoming indistinguishable from reality. Explore the rising threat of deepfakes to enterprise security and how to defend against synthetic media attacks.
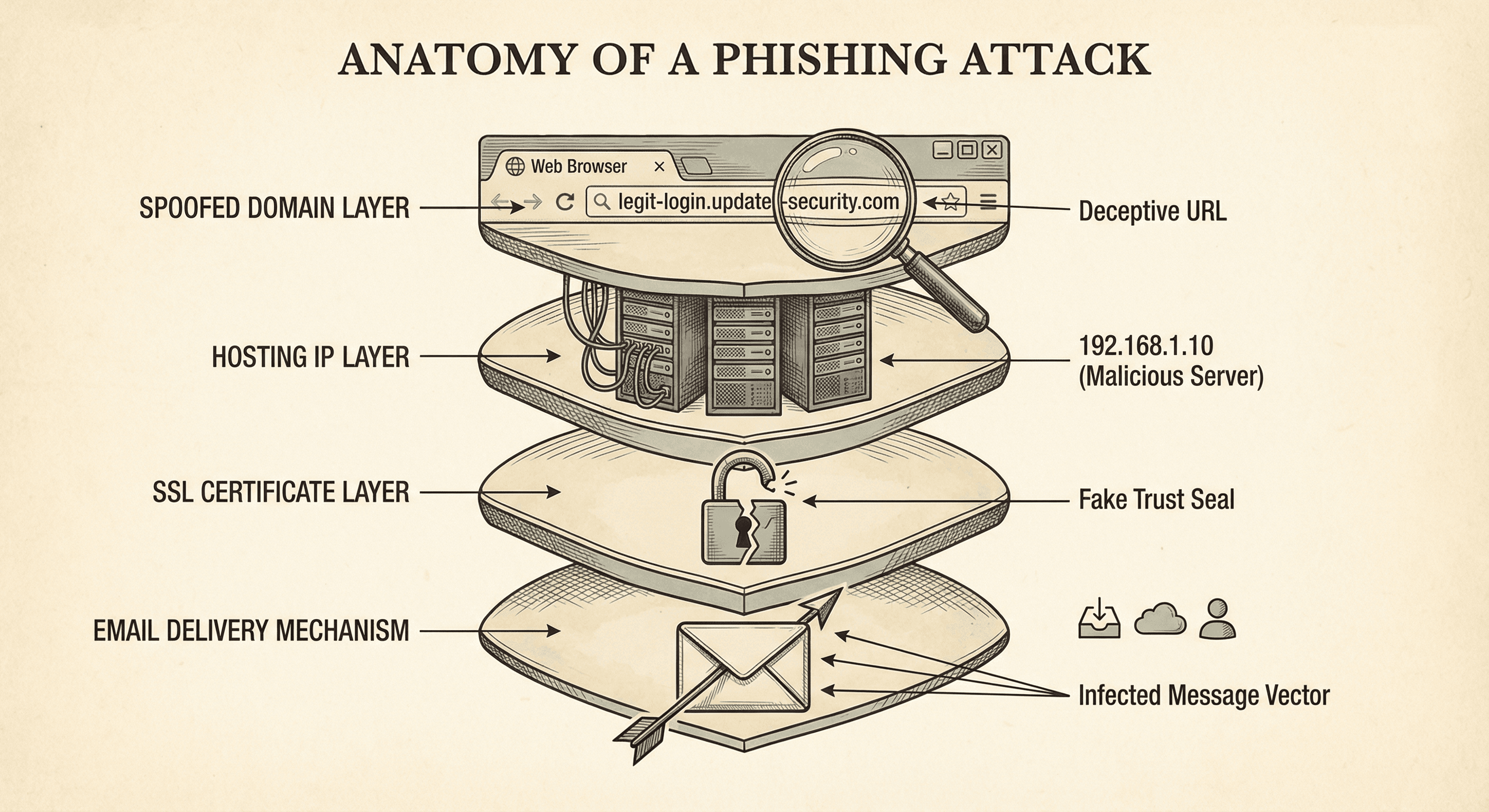
Anatomy of Phishing Infrastructure: How Attackers Build Their Trap
Peel back the layers of a modern phishing attack. From spoofed domains to SSL certificates, understand the infrastructure attackers use and how to detect it.
Automating Threat Intelligence: Speed is Your Best Defense
Manual analysis cannot keep up with machine-speed attacks. Learn how to automate threat data ingestion and response to block threats in milliseconds, not minutes.
Contextual Threat Intelligence: Moving Beyond Static Blacklists
Static IP blacklists are no longer enough. Discover the power of contextual threat intelligence—connecting IPs, domains, and behavior to see the full attack picture.
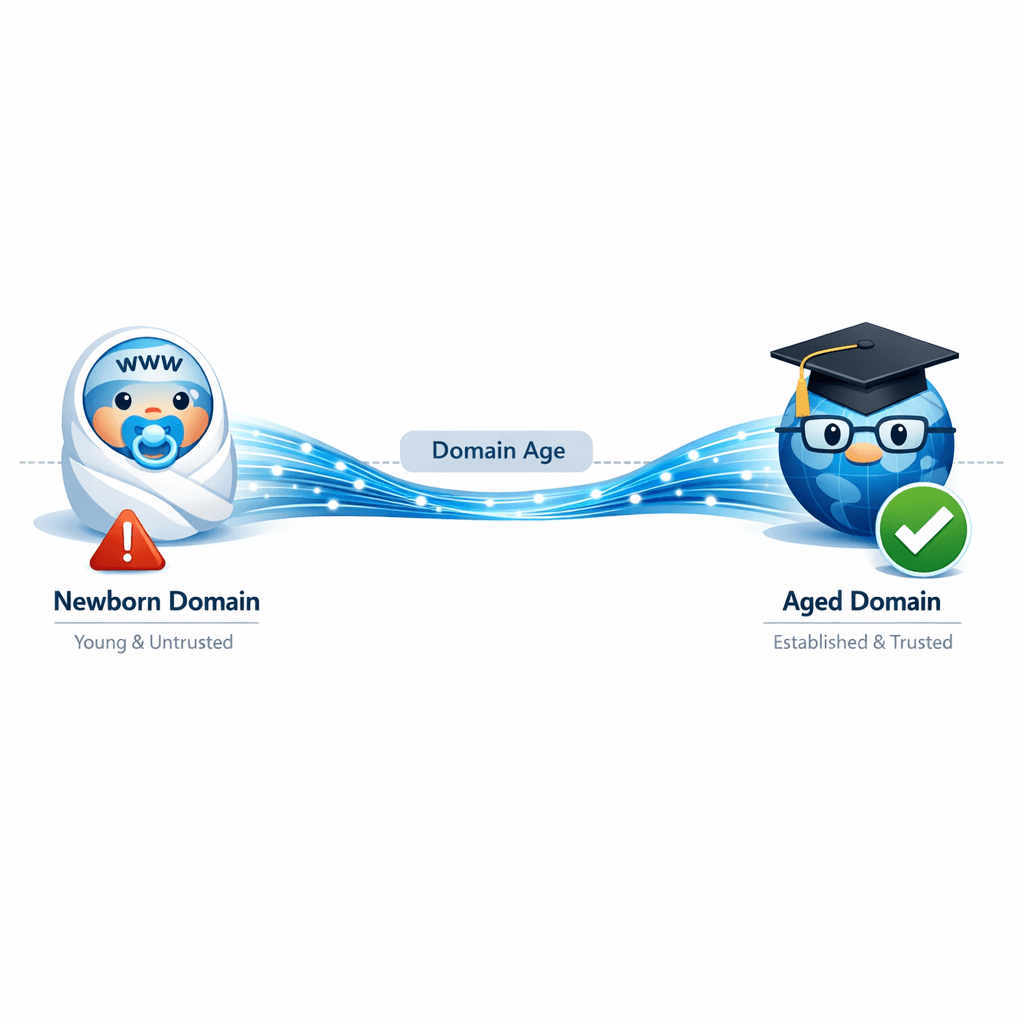
Domain Age as a Risk Indicator: Why "New" Often Means "Danger"
Newly registered domains (NRDs) are a favorite tool for threat actors. Learn why domain age is a critical signal in your threat intelligence stack and how to use it effectively.
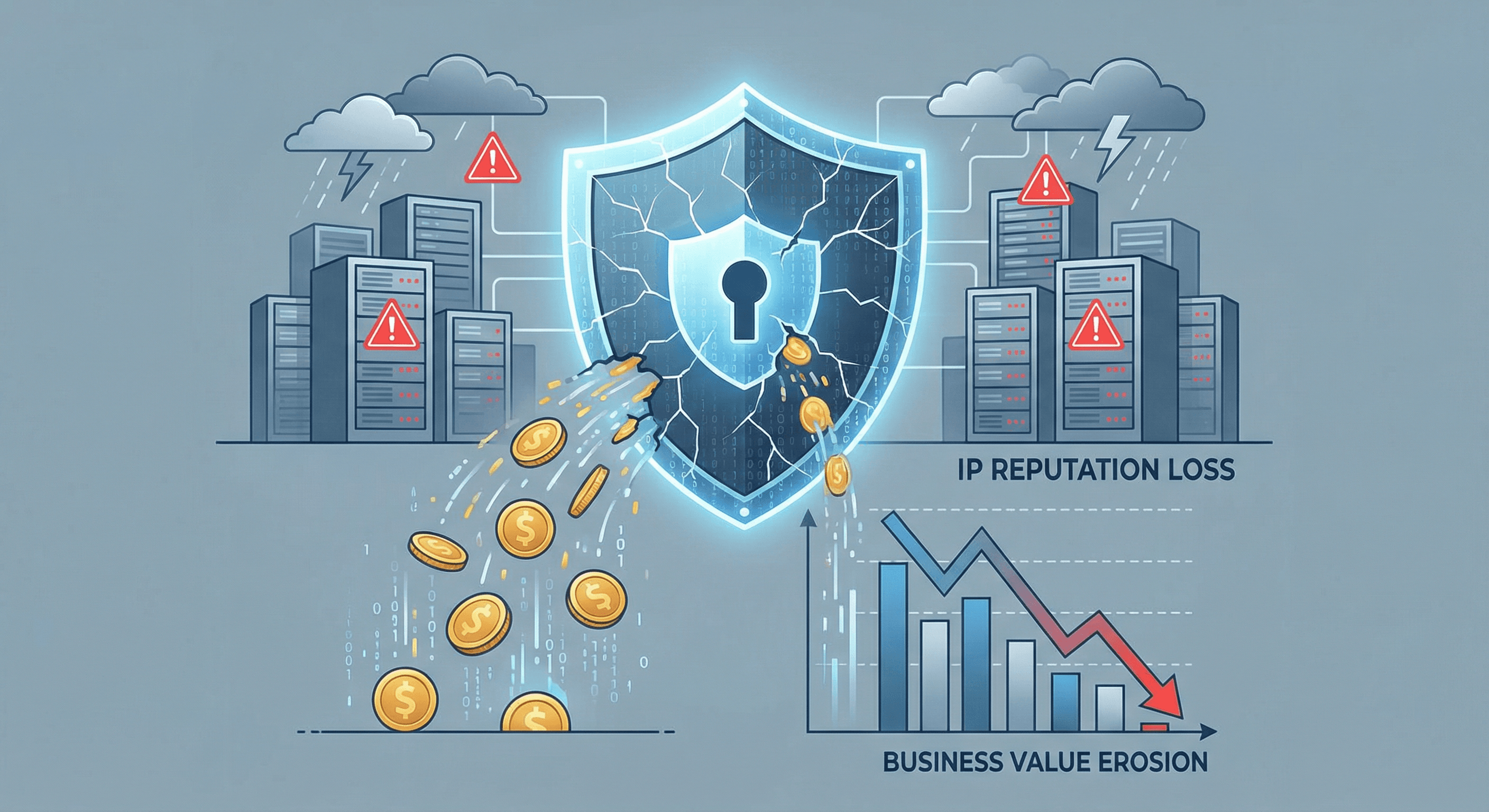
The Hidden Cost of Bad IP Reputation: Why Ignoring It Drains Your Budget
Discover how poor IP reputation impacts more than just security—it affects email deliverability, ad spend, and customer trust. Learn why proactive monitoring is a financial necessity.

Best Threat Intelligence APIs Compared (2026): The Complete Guide
A comprehensive comparison of the top threat intelligence APIs in 2026 — isMalicious, VirusTotal, AbuseIPDB, AlienVault OTX, Shodan, and URLhaus. Feature matrices, pricing breakdowns, and recommendations by use case.

Navigating Data Privacy: GDPR, CCPA, and Cybersecurity Compliance
Privacy regulations are reshaping cybersecurity strategies. Understand the key requirements of GDPR and CCPA and how to align your security program with privacy compliance.

Automotive Cybersecurity: Hacking Connected Cars in 2026
With cars becoming data centers on wheels, the attack surface expands into the powertrain, infotainment, and OTA update systems. We analyze CAN bus injection vulnerabilities and the security risks of V2X communication protocols.
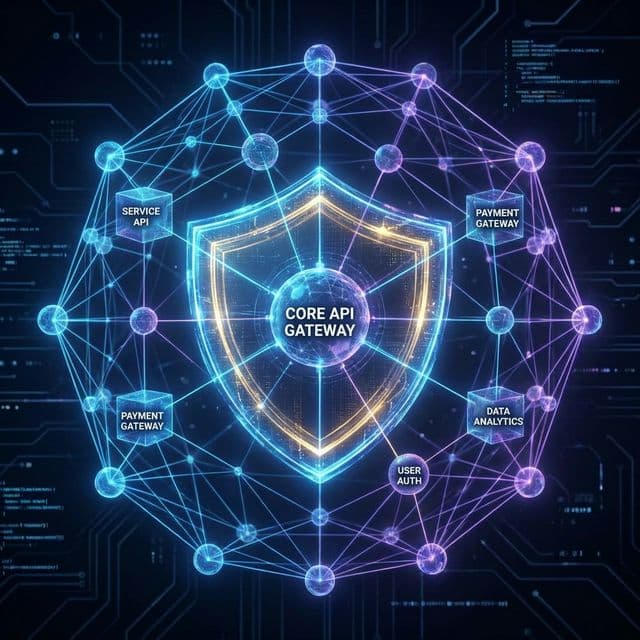
API Security Best Practices: Defending Against the OWASP Top 10
APIs are the backbone of modern applications but are often left vulnerable. Learn how to secure your APIs against common attacks like broken object level authorization and injection.

Threat Hunting: Proactive Security Detection Beyond Automated Alerts
Waiting for alerts means waiting for attacks to succeed. Learn how proactive threat hunting helps security teams discover hidden threats, improve defenses, and stay ahead of sophisticated adversaries.

Shadow IT Risk Management: Securing Unauthorized Applications and Services
Employees use unauthorized apps and services that IT cannot see. Learn how to discover shadow IT, assess risks from unsanctioned tools, and implement governance without stifling innovation.

DevSecOps: Integrating Security into the CI/CD Pipeline
Security should not be an afterthought. Learn how to implement DevSecOps to automate security testing and vulnerability scanning within your development workflow.

Lateral Movement Detection: Stopping Attackers from Spreading Through Your Network
After initial compromise, attackers move laterally to reach valuable targets. Learn how to detect lateral movement techniques, implement segmentation, and stop attackers before they reach critical assets.

IoT Security Threats: Protecting Your Smart Devices from Cyberattacks
Internet of Things devices are increasingly targeted by cybercriminals. Learn how to identify IoT vulnerabilities, secure smart devices, and protect your network from IoT-based attacks.
Insider Threat Detection: Identifying and Managing Employee Security Risks
Insider threats pose unique challenges to organizational security. Learn how to detect malicious insiders, prevent data leakage, and build an effective insider threat program.

Email Authentication: Implementing DMARC, SPF, and DKIM for Email Security
Email spoofing enables phishing and business email compromise attacks. Learn how DMARC, SPF, and DKIM authentication protocols protect your domain from being impersonated in cyberattacks.

What is EDR? A Guide to Endpoint Detection and Response
Traditional antivirus is no longer enough. Explore why Endpoint Detection and Response (EDR) is essential for modern cybersecurity and how it differs from legacy solutions.

DDoS Attack Prevention: Strategies to Protect Your Online Services
Distributed Denial of Service attacks can cripple your online presence. Learn how to identify DDoS threats, implement effective mitigation strategies, and maintain service availability during attacks.
Data Exfiltration Prevention: DLP Strategies to Protect Sensitive Information
Data theft can occur through countless channels. Learn how to detect and prevent data exfiltration, implement effective DLP strategies, and protect your organization most valuable assets from leaving your control.
Dark Web Monitoring: Protecting Your Brand and Detecting Leaked Data
Stolen credentials and sensitive data often surface on the dark web before being exploited. Learn how dark web monitoring helps detect breaches early and protect your organization from cybercriminal activities.
Container and Kubernetes Security: Protecting Cloud-Native Applications
Container environments introduce unique security challenges. Learn how to secure Docker containers, Kubernetes clusters, and cloud-native applications from emerging threats and misconfigurations.

Beyond Phishing: Modern Social Engineering Tactics
Social engineering has evolved beyond simple phishing emails. Discover the latest tactics used by attackers, including vishing, smishing, and pigmenting, and how to spot them.
Mobile App Security: Protecting iOS and Android Applications
Mobile applications are prime targets for cybercriminals. Learn about common mobile security threats and how to protect your iOS and Android apps from reverse engineering and malware.
Infostealer Malware: How Credentials End Up on the Dark Web
Infostealers harvest credentials and sensitive data from infected systems, fueling a massive underground economy. Learn how these threats operate, how to detect them, and how to protect your organization from credential theft.
CTF and Bug Bounty Toolbox: Essential OSINT for Security Research
Master the reconnaissance phase of CTFs and bug bounties with these essential OSINT tools. From IP investigation to domain intelligence, build the toolbox that helps you find what others miss.

Threat Intelligence for Small Business: Enterprise Security on a Budget
Small businesses face the same cyber threats as enterprises but with a fraction of the resources. Learn how affordable threat intelligence and smart security strategies can level the playing field.
Cryptocurrency and Web3 Security Threats
The Web3 ecosystem faces unique threats from wallet drainers to rug pulls. Learn how to identify malicious crypto domains, detect scams, and protect yourself and your users from blockchain-based fraud.
Cloud Security Threats: Protecting Multi-Cloud Infrastructure
Cloud environments face unique security challenges from misconfigurations to cryptomining attacks. Learn how to monitor cloud assets, detect threats, and protect your multi-cloud infrastructure with threat intelligence.
Bot Detection and Account Takeover Prevention
Automated bots drive credential stuffing, account takeover, and fraud at massive scale. Learn how IP reputation and threat intelligence can identify and block malicious automation before it compromises your users.
DNS Security and Threat Intelligence: Blocking Malware at the Resolver
DNS is the first line of defense against malware and phishing. Learn how protective DNS and threat intelligence blocklists can stop threats before they reach your network, with integration guides for Pi-hole, AdGuard, and enterprise DNS.

Business Email Compromise: The Multi-Billion Dollar Threat
BEC attacks cost organizations billions annually through sophisticated impersonation and social engineering. Learn how domain spoofing detection and threat intelligence can protect your organization from CEO fraud and invoice scams.
Supply Chain Attack Detection: Lessons from SolarWinds to MOVEit
Supply chain attacks have become the weapon of choice for sophisticated threat actors. Learn how to detect compromised vendors, monitor third-party risk, and protect your organization before your suppliers become your vulnerability.
AI-Powered Cyberattacks: How Threat Actors Use Machine Learning
Cybercriminals are weaponizing artificial intelligence to launch sophisticated attacks at unprecedented scale. Learn how AI-powered threats work and how threat intelligence can help you defend against them.
Enhancing Zero Trust with Malicious IP and Domain Reputation Analysis
Zero Trust security demands constant verification. Discover how integrating malicious IP and domain reputation checks strengthens your threat intelligence and prevents phishing.

How to Detect Malicious Domains and IPs: A Reputation Guide
A practical guide on detecting malicious domains and IPs using reputation data. Learn to spot phishing threats and secure your applications with real-time threat intelligence.

Proactive Threat Defense: Monitoring Malicious IP and Domain Reputation
Shift from reactive to proactive cybersecurity. Learn how monitoring malicious IP and domain reputation helps identifying threats early and stopping phishing attacks before they succeed.
Why Checking Malicious Domain and IP Reputation is Critical for Threat Prevention
Learn why monitoring domain and IP reputation is essential for cybersecurity. Discover how to detect malicious threats, prevent phishing attacks, and leverage threat intelligence to protect your infrastructure.
Ransomware Detection and Prevention: A Comprehensive Defense Strategy
Learn how to detect ransomware threats before they encrypt your data. Explore proven prevention techniques, early warning signs, and how threat intelligence can protect your organization from costly ransomware attacks.
SSL Certificate Security: Identifying Vulnerabilities and Misconfigurations
SSL certificates are crucial for secure web communications, but misconfigurations and vulnerabilities can expose your users to serious risks. Learn how to identify, assess, and fix SSL certificate security issues before attackers exploit them.
Zero-Day Vulnerabilities: Detection, Response, and Threat Intelligence
Zero-day vulnerabilities pose one of the greatest cybersecurity challenges. Learn how to detect exploitation attempts, respond effectively, and leverage threat intelligence to protect your organization from unknown threats.
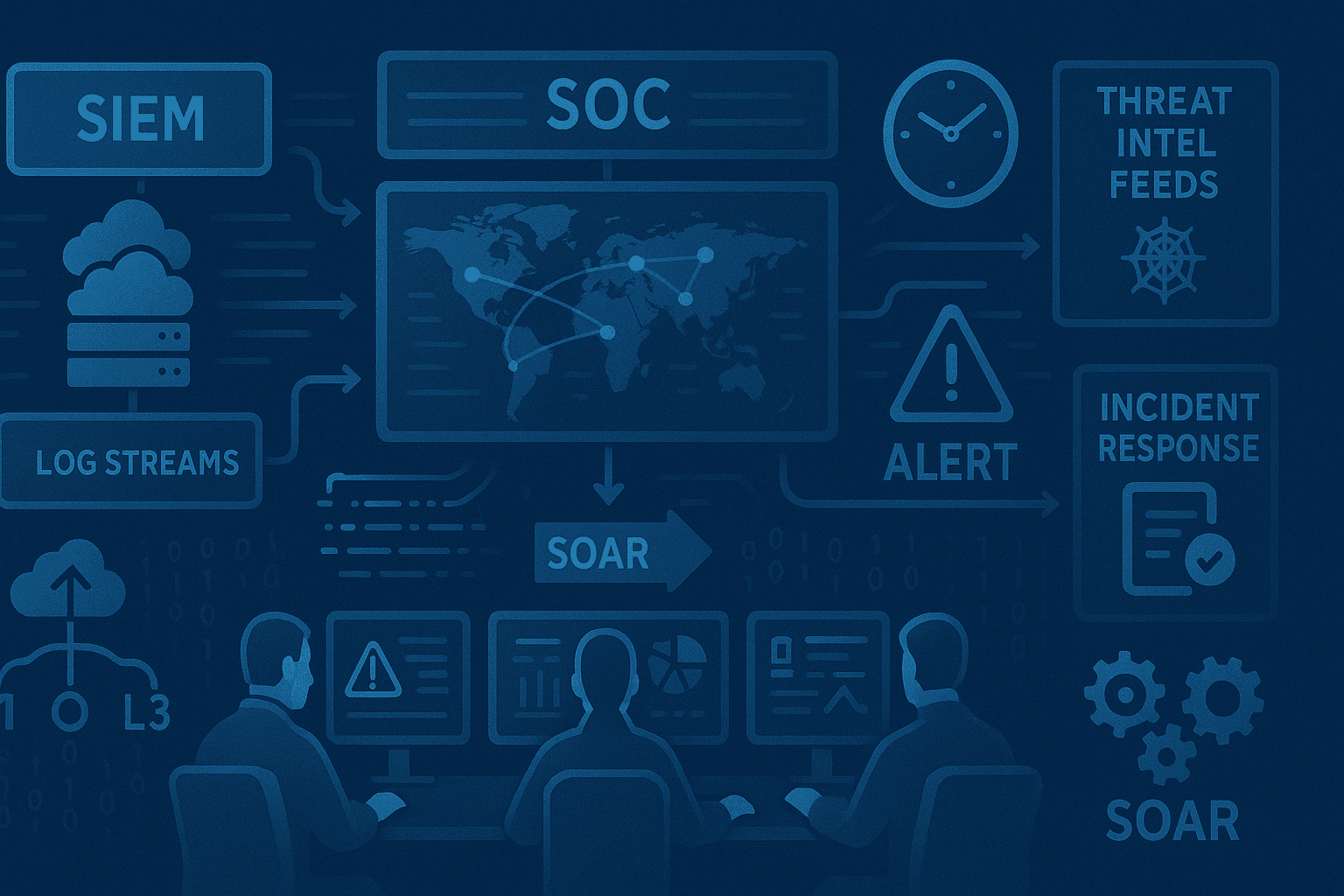
Building a Modern SOC with Threat Intelligence: A Practical Guide
Learn how to build an effective Security Operations Center (SOC) powered by threat intelligence. Discover essential tools, processes, and best practices for detecting, analyzing, and responding to cyber threats in real-time.
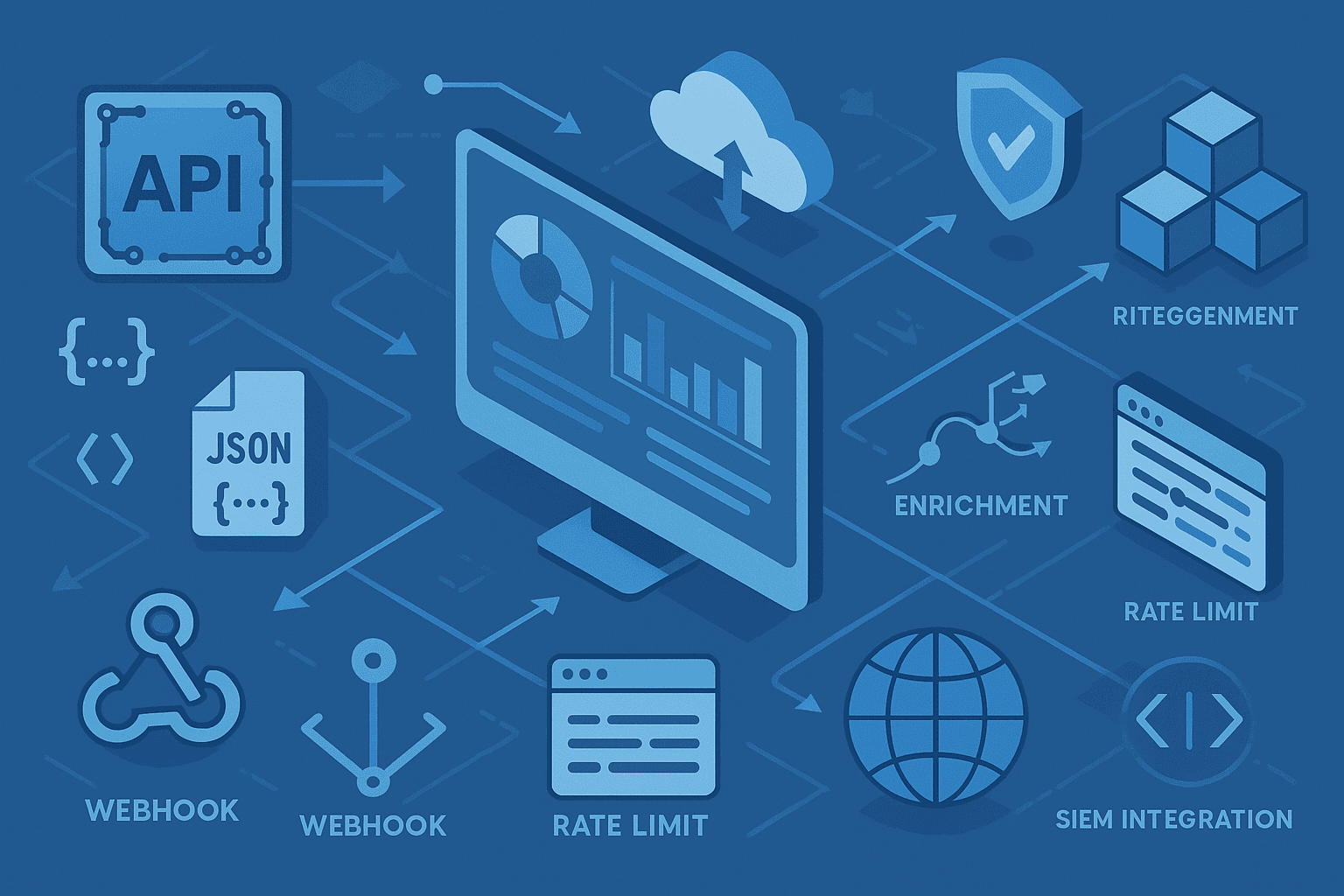
API Integration for Threat Intelligence: Automate Your Security
Discover how integrating threat intelligence APIs can transform your security infrastructure. Learn best practices for automated threat detection, real-time monitoring, and seamless integration with your existing systems.
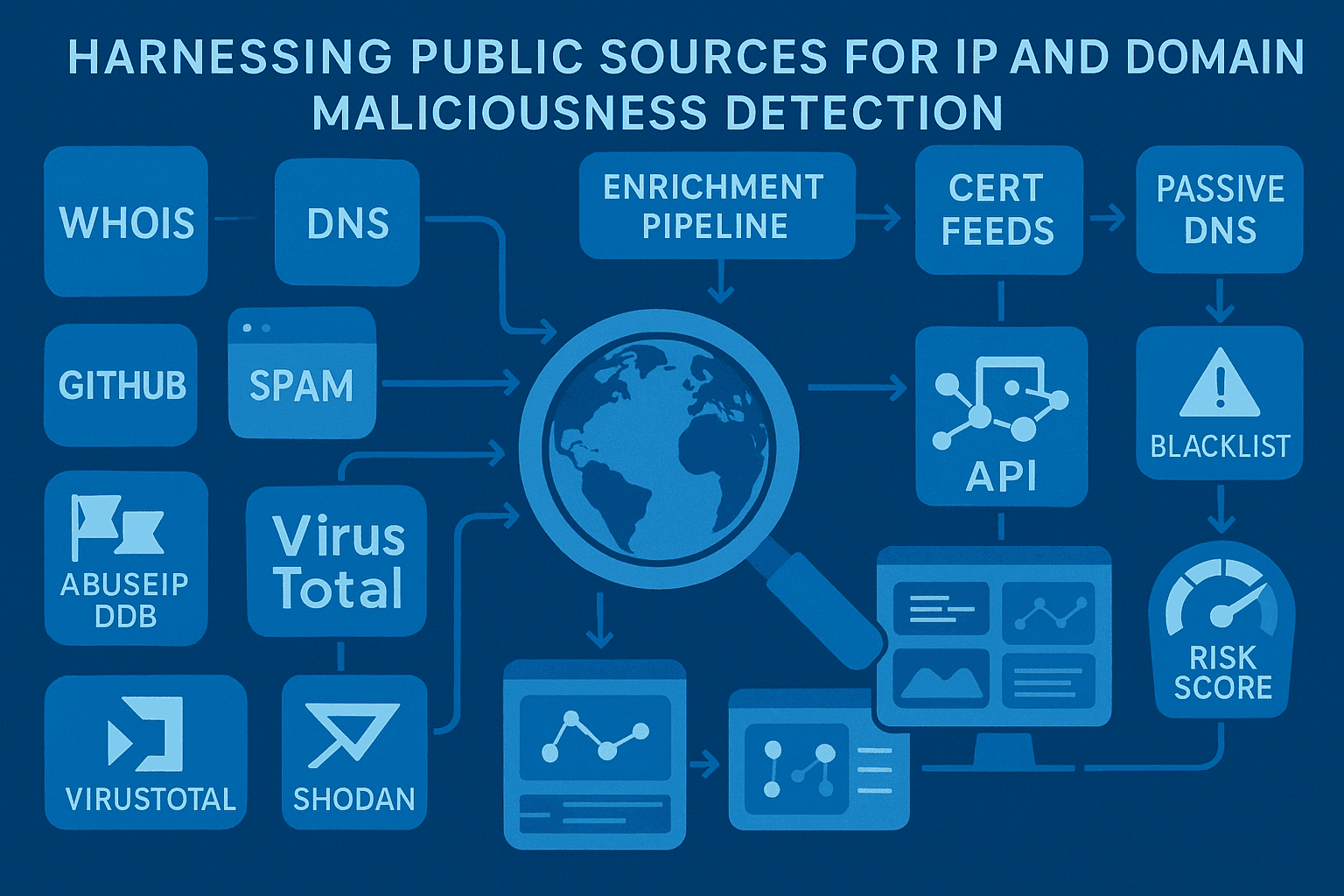
Harnessing Public Sources for IP and Domain Maliciousness Detection
Learn how public sources like IP sets and blocklists can enhance your cybersecurity defenses by providing actionable insights into IP and domain maliciousness. Discover how to integrate these resources into WAF solutions like Fortinet and Imperva.
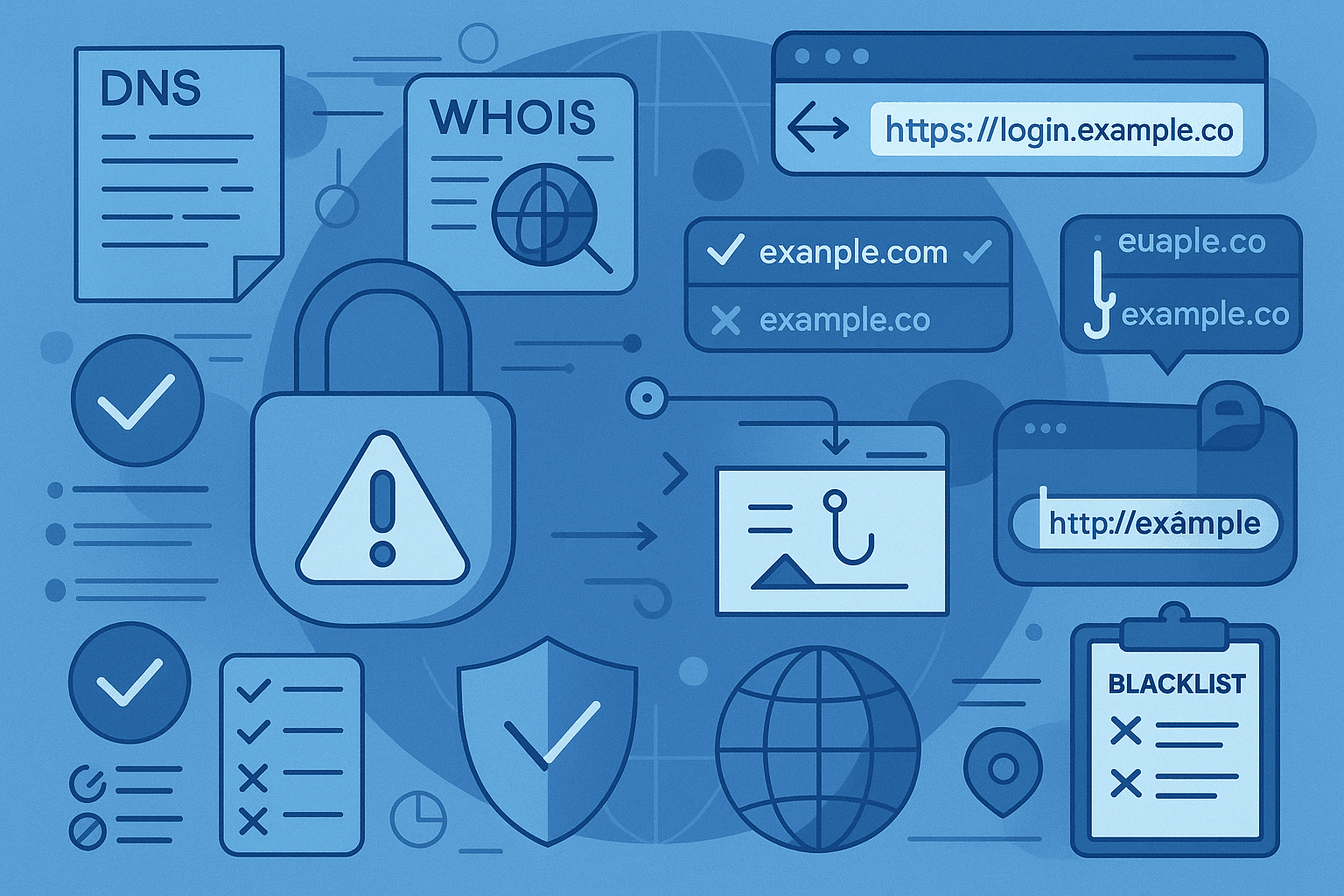
Detecting malicious domain names: a guide to safer browsing
Explore the world of domain name maliciousness and learn how to identify, assess, and protect against harmful domains. Discover tools and techniques to safeguard your online presence.
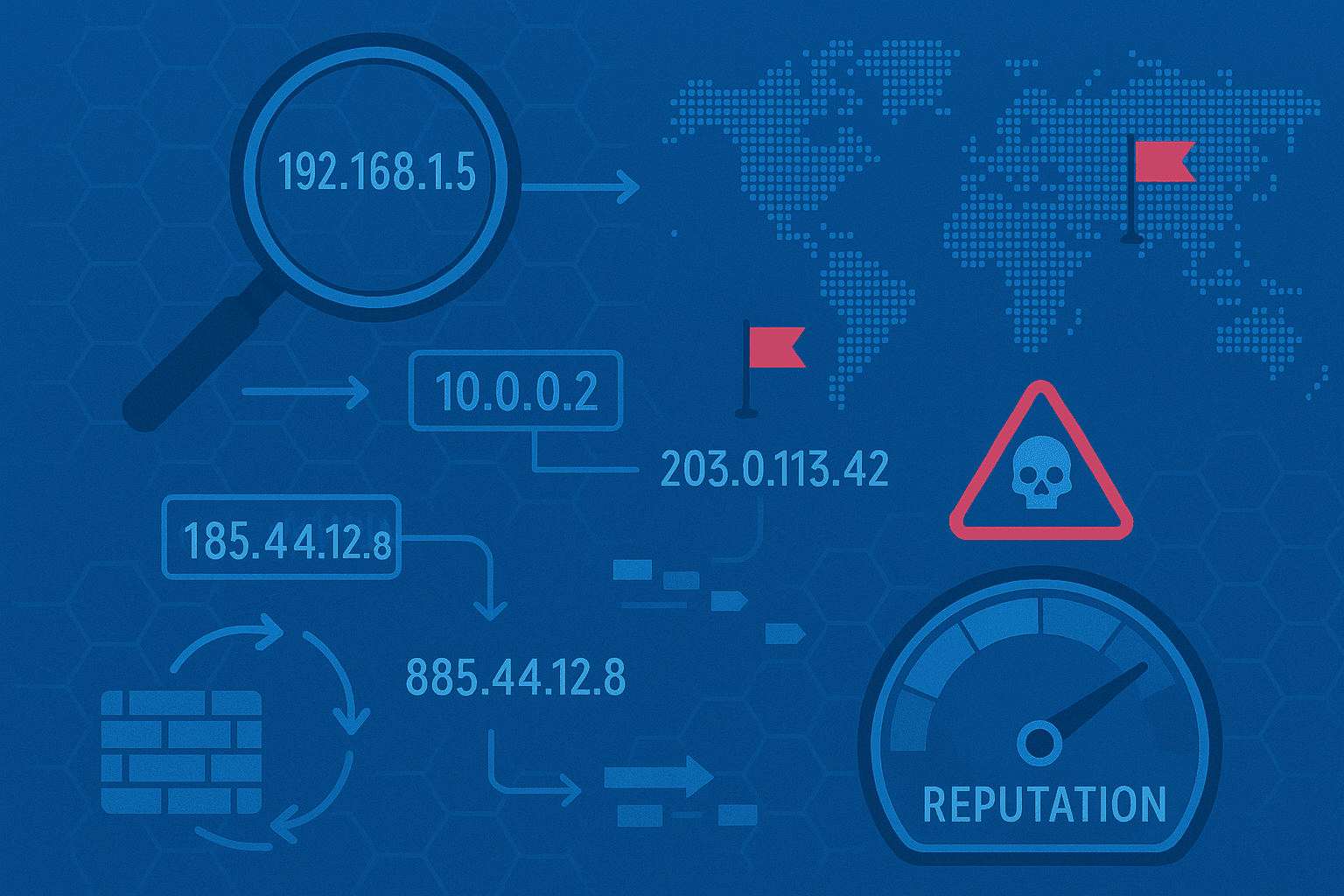
Understanding IP Maliciousness: A new way to protect your network.
Discover how assessing the potential maliciousness of an IP can safeguard your systems against cyber threats. Learn about the indicators, methods, and tools that help identify malicious IPs and take proactive measures.
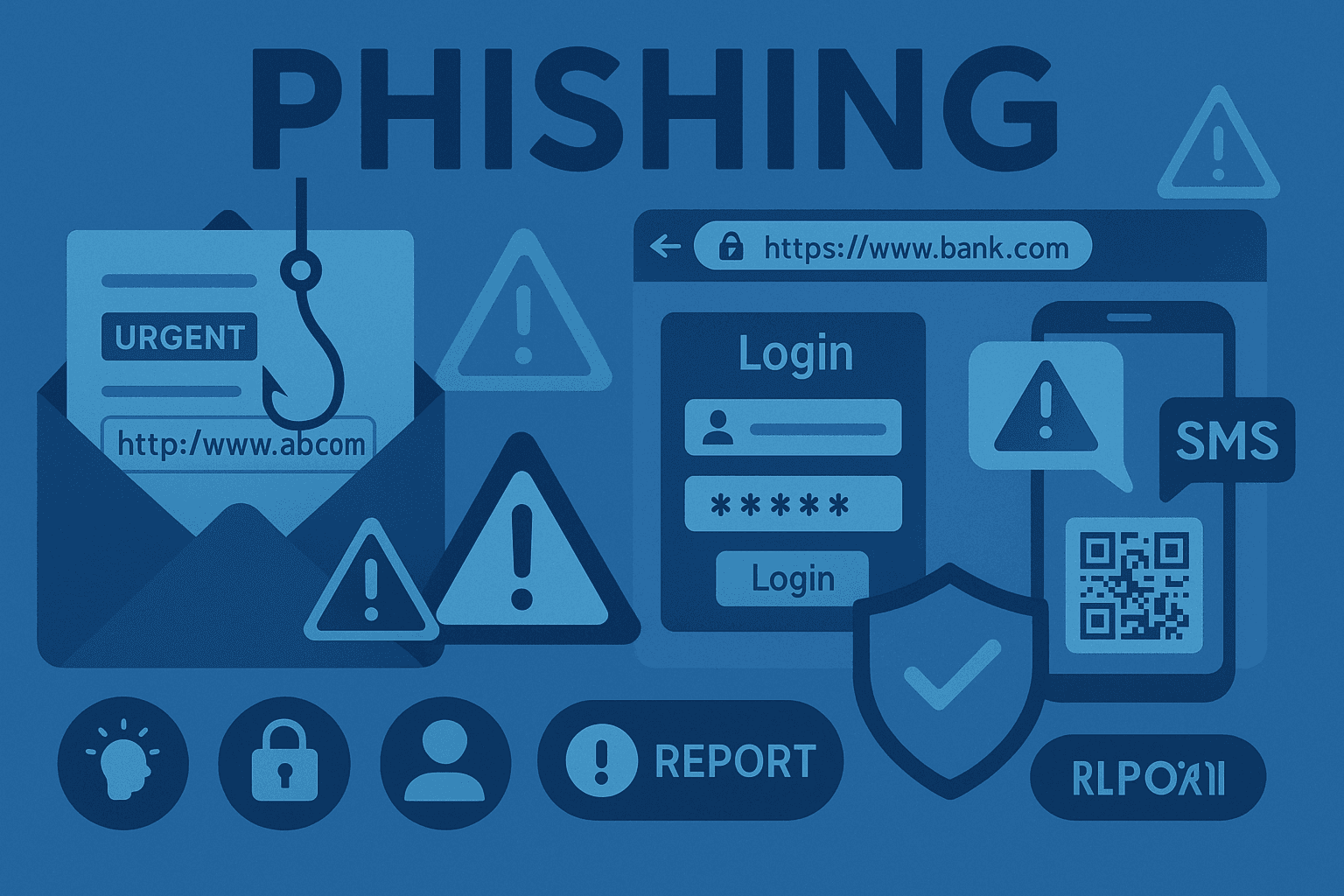
Understanding phishing and how to stay protected
Phishing is a growing cybersecurity threat that tricks individuals into providing sensitive information. Learn how to identify phishing attempts and implement strategies to stay safe online.
Expert Threat Intelligence Analysis
Our blog features in-depth analysis from our threat research team. Each article is backed by real data from our analysis of millions of malicious domains, IPs, and URLs across the global threat landscape. Topics include ransomware campaigns, phishing techniques, malware distribution networks, and emerging threat trends. We publish actionable intelligence that security teams can immediately use to improve their defenses.
Practical Security Guidance
Beyond threat analysis, we share practical guidance for security practitioners. Our tutorials cover API integration, SIEM configuration, threat hunting techniques, and building effective threat intelligence programs. Whether you're a SOC analyst, security engineer, or CISO, you'll find content tailored to your role and experience level.
Stay Ahead of Emerging Threats
The threat landscape evolves constantly. Our blog keeps you informed about the latest attack techniques, newly discovered vulnerabilities, and emerging threat actors. Subscribe to our newsletter for weekly digests of the most important developments in cybersecurity.
Subscribe to Our Newsletter
Weekly threat intelligence insights delivered to your inbox.