Space Systems Cyber Threats: Securing the Final Frontier
As space becomes accessible, it becomes a target. From satellite hijacking to ground station jamming, we analyze the unique threats to orbital assets and how threat intelligence secures the new space race.
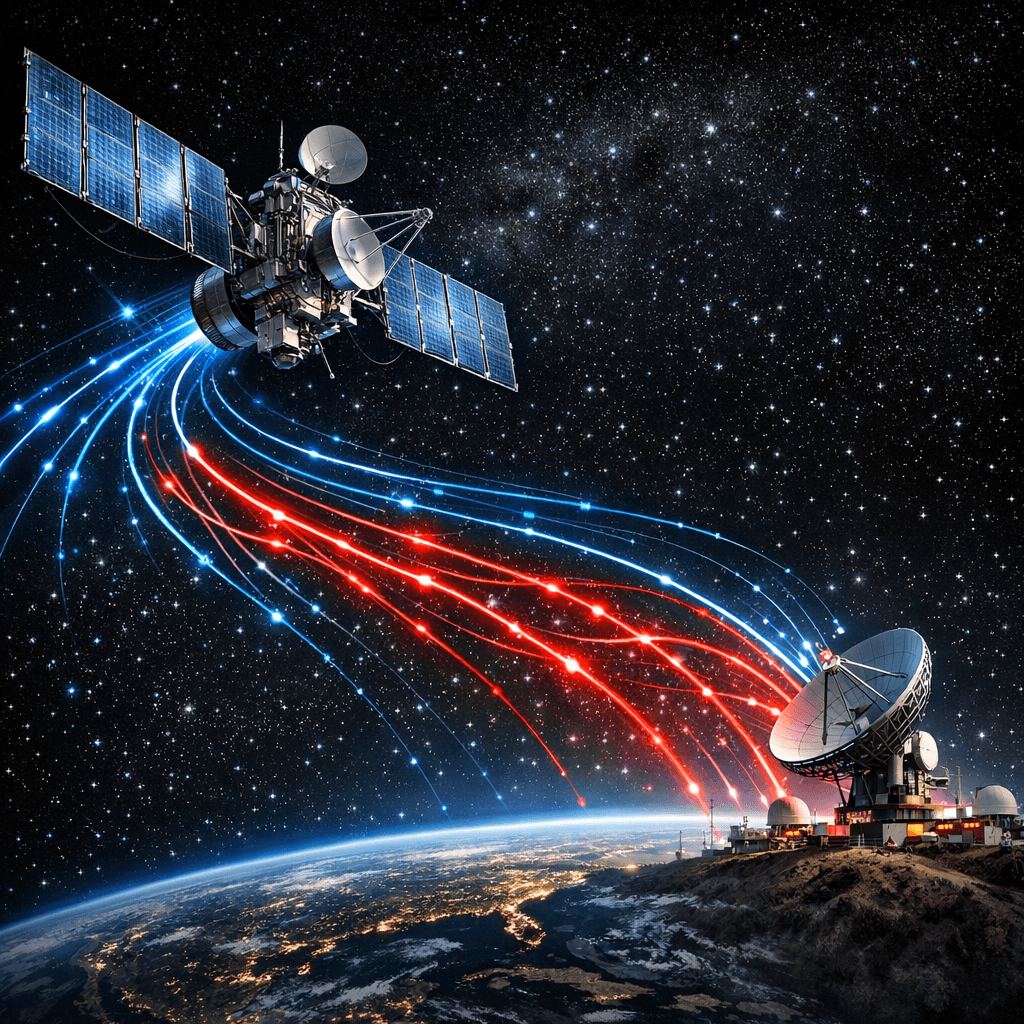
The Orbital Attack Surface
The democratization of space via LEO constellations and CubeSats has expanded the attack surface vertically. Space assets, once obscure, are now critical infrastructure for global internet and navigation.
Jamming, Spoofing, and Hijacking
Attackers target the weakest link: the RF communication channel.
- Uplink Jamming: Overwhelming the satellite's receiver with noise to disrupt control commands.
- GPS Spoofing: Broadcasting fake GPS signals to drift satellites off course or disrupt ground-based navigation.
- Man-in-the-Middle: Intercepting unencrypted downlinks to steal imagery or telemetry data.
Securing the Ground Segment
The ground station is often the entry point for attackers.
- Endpoint Security: Hardening ground control computers against commodity malware prevents lateral movement.
- Identity & Access Management: Implement strict MFA and least privilege for satellite operators.
Threat Intelligence for Space Operations
Protecting space assets requires vigilance on Earth.
- Ground Station Geolocation: Monitor outbound connections from mission control. Traffic to an IP geolocated in a sanctioned nation is a critical threat level indicator of insider threat or compromise.
- IP Reputation Defense: Attackers often use known C2 infrastructure to probe satellite networks. Blocking connections to low reputation IPs prevents initial access.
- Cross-Domain Intelligence: Correlate physical space anomalies (e.g., unexpected maneuvers) with cyber indicators (e.g., brute force attempts from suspicious IPs) to detect coordinated attacks.
IsMalicious Strategy
Space is the ultimate high-stakes environment. Integrating IP reputation and geolocation data into your Security Operations Center (SOC) provides the necessary context to defend assets in orbit.
Related articles
 Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network Edge
Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network EdgeReal-time IP reputation checks give you the power to identify and block malicious actors the moment they connect to your systems. Discover how to implement automated threat detection that works at machine speed, not analyst speed.
 Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?
Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?Confused by the Dark Web and Deep Web? We explain the difference and where cyber threats like stolen credentials and malware actually live.
 Feb 12, 2026Cyber Threats 101: Understanding Online Dangers
Feb 12, 2026Cyber Threats 101: Understanding Online DangersA beginner's guide to common cyber threats. Understand malware, viruses, and hackers, and learn how to protect yourself online.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker