523
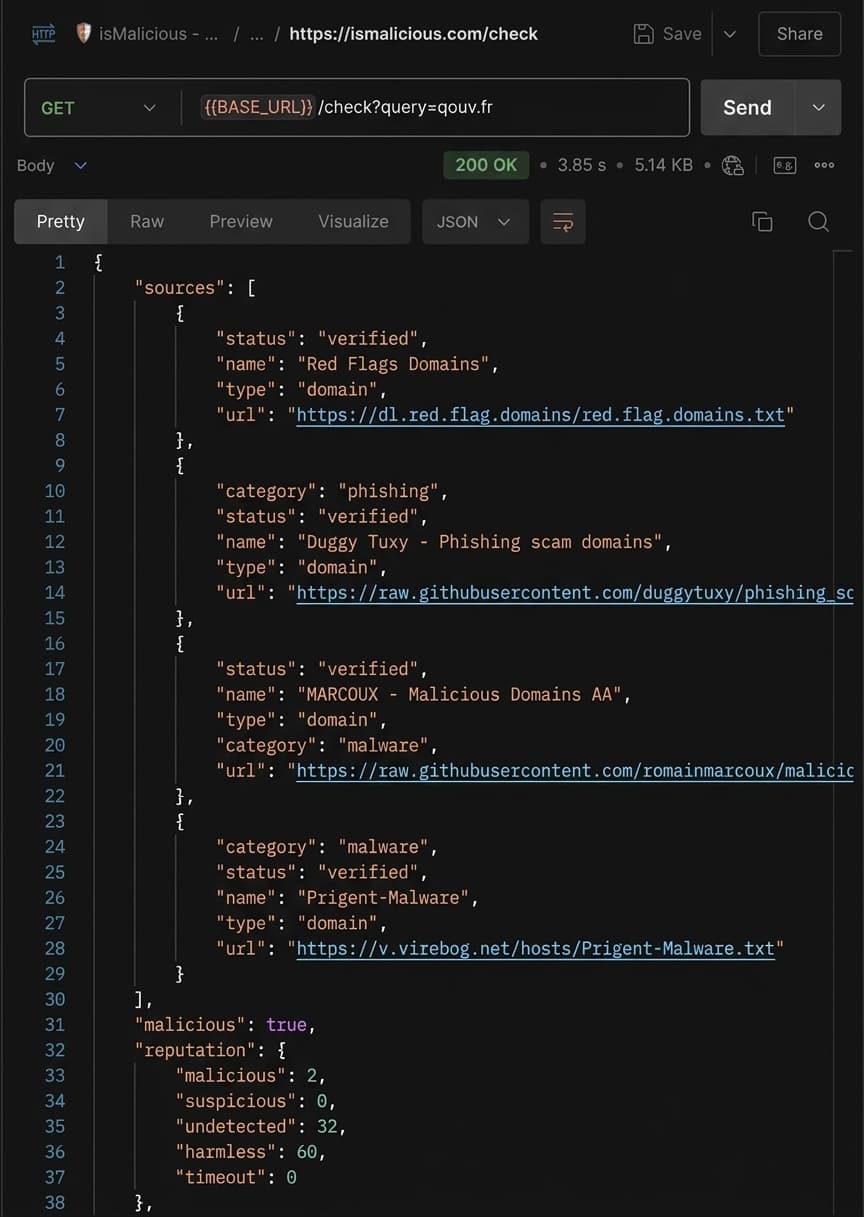
Source Checks
Configured feeds are reliability-weighted so SOC teams can see why a verdict was produced.
Check any IP, domain, URL, file hash, or CVE against 500M+ threat indicators aggregated from 500+ sources — through a REST API, dashboard, or real-time stream. Free API key, no credit card required.
Known C2 infrastructure linked to Emotet campaigns. Active phishing operations across 23 domains. High confidence from 12 intel sources.
523
Source Checks
Configured feeds are reliability-weighted so SOC teams can see why a verdict was produced.
24/7
Real-Time Updates
Continuous monitoring and database refreshes ensure you always have the latest threat intelligence.
500M+
Threat Records
250M IPs, 200M domains, 50M hashes, and more malicious entities tracked across the globe.
80%
Faster Detection
Identify threats faster than traditional methods, reducing response time and potential damage.
A sample from our live feed. Registered users see the full picture.
Aggregate data from Shodan, GreyNoise, AbuseIPDB, community threat feeds, and 500+ more providers. One query, comprehensive results — no juggling multiple platforms.
LLM-generated summaries transform raw enrichment data into actionable intelligence with context-aware threat narratives tailored to your environment.
Automatically map IOCs to MITRE ATT&CK techniques based on threat tags and enrichment findings. Accelerate triage and build structured threat models.
Real-time threat intelligence aggregated from industry-leading providers, community feeds, and proprietary detection engines.




The most comprehensive threat intelligence database, continuously refreshed from 500+ verified sources.
45M+ phishing domains and credential harvesting sites. Detect fake login pages, brand impersonation, and social engineering attacks in real-time.
120M+ malware distribution IPs and domains. Block ransomware, trojans, viruses, and zero-day malware before they infect your systems.
100M+ malicious IP addresses involved in DDoS attacks, brute force attempts, botnet C2 servers, and network abuse.
28M+ invasive advertising networks, unwanted software promotions, and aggressive marketing domains that degrade user experience.
67M+ tracking domains, analytics scripts, and surveillance networks. Protect user privacy and comply with GDPR requirements.
Comprehensive vulnerability intelligence including CVEs, exposed services, weak SSL certificates, and security misconfigurations.
Every threat is verified across multiple intelligence sources. Our cross-referencing system eliminates false positives and provides confidence scores for each detection.
Unlike static blocklists updated weekly, our database receives hourly updates. New phishing sites, malware domains, and malicious IPs are added within minutes of discovery.
Beyond simple blocklists, get rich threat intelligence including geolocation, ASN data, WHOIS information, SSL certificates, and historical behavior patterns.
Sub-100ms response times, 99.9% uptime SLA, and unlimited scalability. Our cybersecurity API integrates seamlessly with firewalls, SIEM systems, and custom applications.
Enterprise-grade threat intelligence CLI built for maximum performance. Deploy in air-gapped environments, integrate with your CI/CD pipeline, or run automated security checks at scale.
# Update threat intelligence database from 500+ sources
$ ismalicious update
Database update started.
Fetching source 1 of 500 - 00:01.234s
Fetching source 2 of 500 - 00:00.987s
...
Fetching source 500 of 500 - 00:00.823s
Cleaning false positives...
Loaded 2,000,000 legitimate domains
Removed 1,234 false positives
Database update completed in 05:23.456s
# Check a domain
$ ismalicious get malicious-site.ru
Found entry: malicious-site.ru
Categories: malware phishing c2 botnet
# Docker deployment
$ docker run -v $(pwd)/data:/app/data ismalicious/cli updateRun threat intelligence checks completely offline with local JSON databases. No internet dependency once synchronized — perfect for air-gapped environments.
ismalicious get domain.comAutomatically fetches and combines data from 500+ threat intelligence sources. A single command updates your entire local database with the latest threats.
ismalicious updateAdvanced curation using Cloudflare Radar and top-1M domain lists. Removes legitimate domains automatically to ensure zero false positives in your threat database.
Auto-cleans during updateSmart regex-based extraction supporting domains, IPv4, and IPv6 addresses. Handles multiple formats and categorizes entities by threat type automatically.
Supports all IP/domain formatsBuilt for maximum speed and efficiency. Optimized with parallel processing and minimal memory footprint — processes millions of entities in minutes.
Processes millions of entitiesNative binaries for Linux, macOS, and Windows. Docker images available for containerized deployments and seamless CI/CD pipeline integration.
docker run ismalicious/cliEach threat tagged with specific categories: malware, phishing, botnet, C2, and more. Enables precise filtering and threat-specific response workflows.
JSON output with categoriesEnterprise license validation with online verification and offline grace periods. Flexible licensing for team and air-gapped deployments.
Secured with license.txtBuilt-in performance monitoring with --debug flag. Track fetch times, processing speeds, and database operations for optimization and troubleshooting.
ismalicious --debug updateIPs, domains, hashes, URLs aggregated continuously
NVD, CISA KEV, EPSS, GHSA, CERT-FR, OTX, and more
Stream API and webhooks for sub-second propagation
Get started with basic threat intelligence. Perfect for individuals and small projects.
Ideal for professionals and small businesses requiring more robust protection.
Comprehensive solution for organizations with advanced security needs. Custom limits and maximum protection.
Shadow AI is the new shadow IT: fast adoption, weak visibility, and serious data leakage risk. Security teams need discovery, domain intelligence, policy, training, and monitoring.
AI-enabled threats are being mapped into ATT&CK language, but mapping is only useful when it drives enrichment, detection, triage, and response workflows.
Cyber incidents are no longer always contained to systems and data. As extortion crews add physical threats, responders need ransomware intelligence, safety escalation, IOC enrichment, and executive-ready evidence.
Alert fatigue is not a staffing problem alone. SOC teams need better evidence, source quality, confidence bands, and enrichment workflows that turn noisy alerts into defensible decisions.
YellowKey made a quiet assumption loud again: encrypted endpoints still need vulnerability intelligence, asset context, and incident workflows. Here is how to respond when a last-resort control becomes a live risk.
Les données CVE deviennent plus puissantes lorsqu’elles alimentent API, dashboards, SIEM, alerting et workflows de remédiation avec un contexte complet.