Contextual Threat Intelligence: Moving Beyond Static Blacklists
Static IP blacklists are no longer enough. Discover the power of contextual threat intelligence—connecting IPs, domains, and behavior to see the full attack picture.
For years, the standard defense against malicious traffic was the blacklist. If an IP was bad, it went on a list. Firewalls downloaded the list and blocked the IP. Simple.
But today's threat landscape is too dynamic for static lists. IPs rotate, legitimate sites get compromised, and attackers use residential proxies to hide in plain sight. To stay ahead, analysts need Contextual Threat Intelligence.
The Problem with Binary Decisions
A binary "Good/Bad" decision fails because it lacks nuance.
- Shared Hosting: An IP might host 100 legitimate websites and 1 phishing site. Blocking the IP blocks everyone.
- Compromised Devices: A residential IP might be part of a botnet today but clean tomorrow after the user runs an antivirus scan.
- Ephemeral Infrastructure: Cloud IPs change hands in minutes. A blacklist updated daily is already obsolete.
What is Context?
Context answers the "Why?" and "How?" behind an indicator.
- Associated Domains: What domains are resolving to this IP right now? Are they high-risk?
- ASN/ISP: Is this IP belonging to a consumer ISP (Verizon, Comcast) or a cloud provider (AWS, DigitalOcean)? A login attempt from a cloud server is suspicious; a login from a residential IP is normal.
- Behavioral History: Has this IP been seen scanning ports? Brute-forcing SSH? Or just sending spam?
- Passive DNS: What used to be here?
The Graph Approach
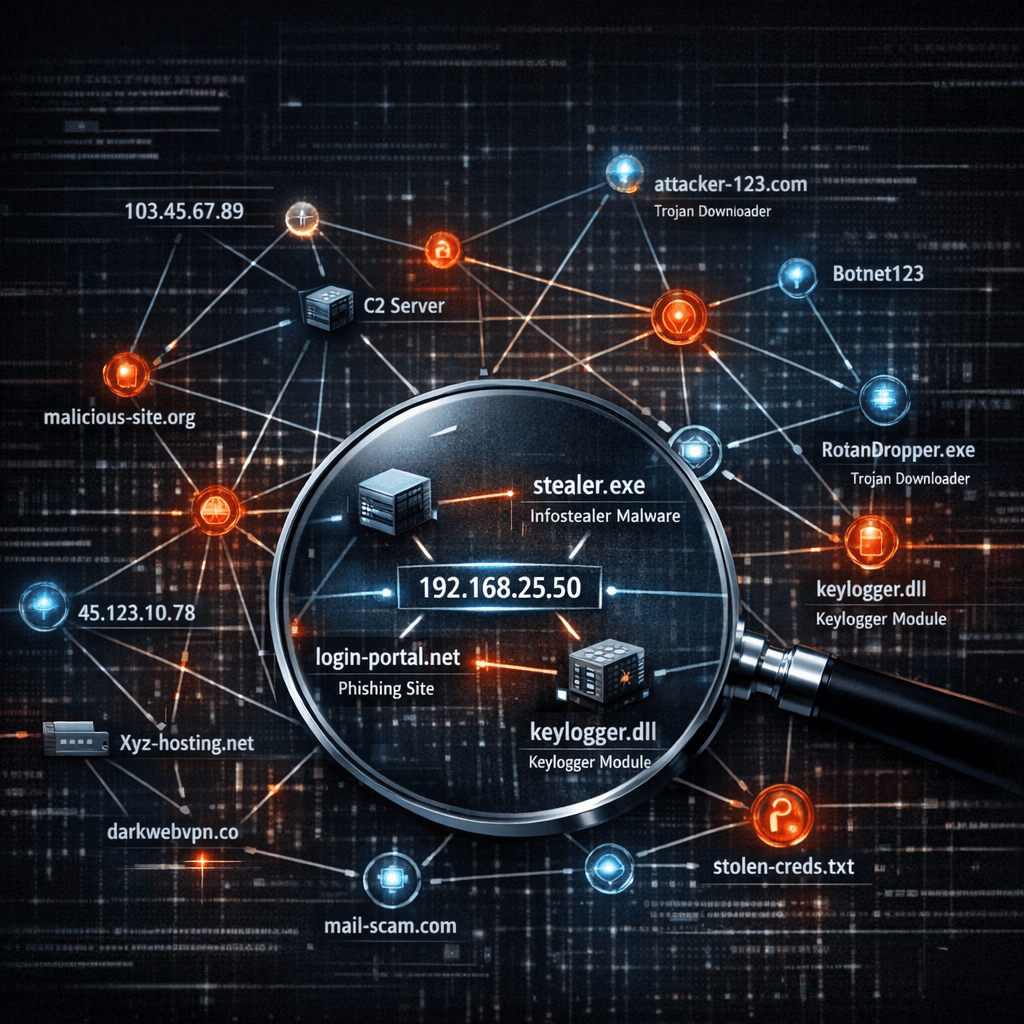
Imagine threat intelligence not as a list, but as a graph.
- Node A: Malicious File Hash
- Node B: C2 Domain
- Node C: Hosting IP
By seeing the connections, you can pivot. "This file talks to this domain, which resolves to this IP." Now you can block the IP proactively, even if it hasn't attacked you yet.
Leveraging isMalicious for Context
isMalicious doesn't just give you a "Yes/No." It provides the metadata you need to make intelligent decisions.
- Confidence Scores: How sure are we?
- Threat Types: Is it a scanner? A bot? A phisher?
- Geolocation: Does it match your user's expected profile?
Conclusion
Stop playing whack-a-mole with static blacklists. Embrace contextual intelligence to understand the nature of the threat, not just its address. This reduces false positives and catches sophisticated attacks that slip through simple filters.
Related articles
 May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams Sane
May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams SaneA SOAR playbook without enrichment is a ticket printer. A SIEM with unbounded threat feeds is a bill. Here is a practical way to design enrichment for Splunk, Sentinel, or Elastic-style stacks—what to store, when to run playbooks, and what to report upward.
 Apr 30, 2026Threat Intelligence Risk Scoring: How to Calibrate Reputation, Reduce False Positives, and Defend Your Decisions
Apr 30, 2026Threat Intelligence Risk Scoring: How to Calibrate Reputation, Reduce False Positives, and Defend Your DecisionsA noisy score is worse than no score. Learn what makes a reputation model trustworthy, how to combine multi-source evidence, and how to communicate uncertainty to your SOC and your executives.
 Apr 26, 2026Threat Intelligence Platforms: Architecture, Data Quality, and High-Signal Feeds
Apr 26, 2026Threat Intelligence Platforms: Architecture, Data Quality, and High-Signal FeedsDesign TIPs and intel pipelines that scale: normalization, confidence scoring, deduplication, API-first delivery, and how to pair platform investments with analyst workflows.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker