Anatomy of Phishing Infrastructure: How Attackers Build Their Trap
Peel back the layers of a modern phishing attack. From spoofed domains to SSL certificates, understand the infrastructure attackers use and how to detect it.
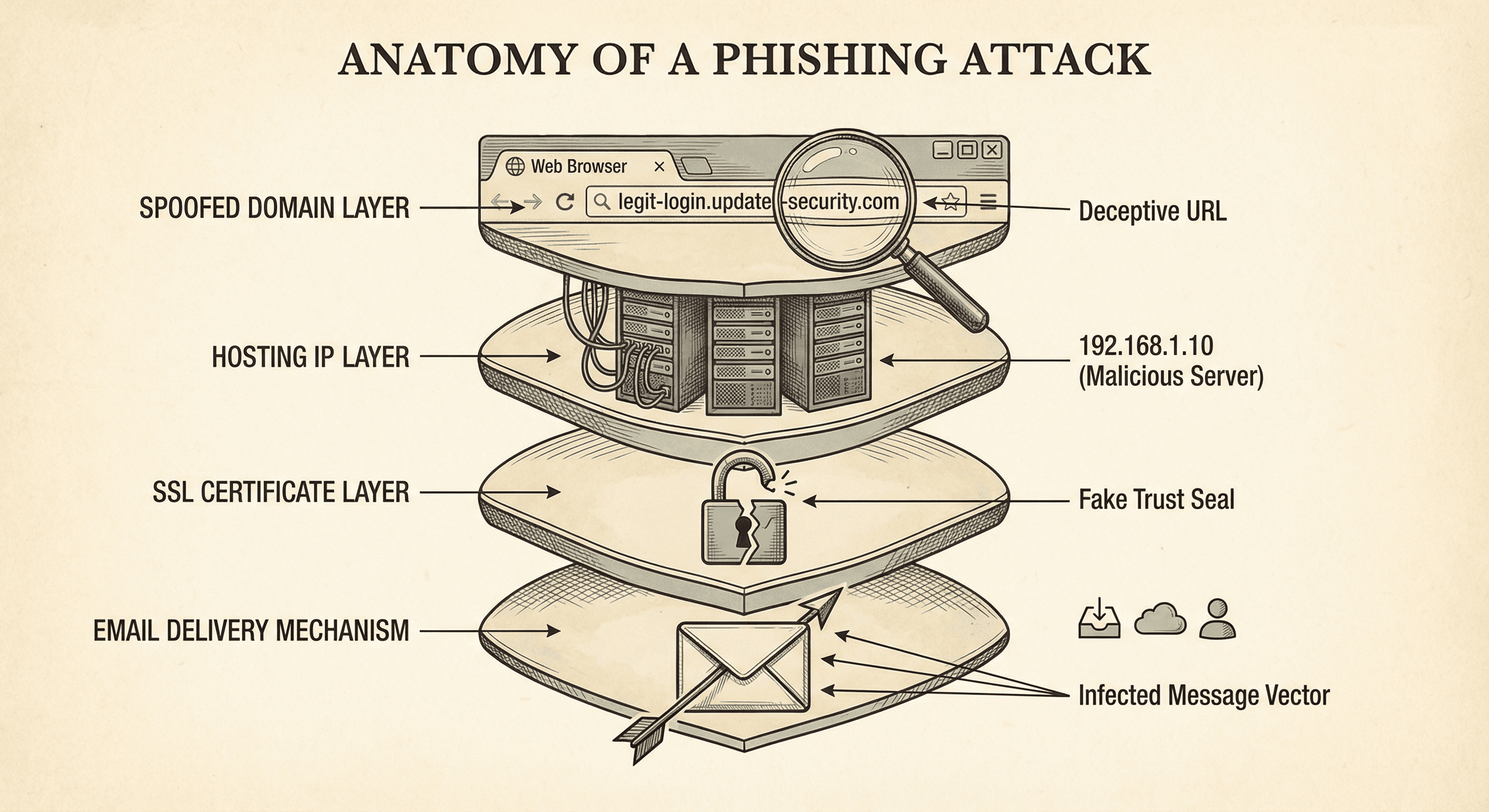
Phishing isn't just a deceptive email; it's a complex web of technical infrastructure designed to bypass filters and fool users. To stop it, you need to understand how it's built. Let's dissect the anatomy of a modern phishing campaign.
Layer 1: The Domain (The Mask)
It starts with the lookalike. Attackers use:
- Typosquatting:
g0ogle.cominstead ofgoogle.com. - Combosquatting:
paypal-secure-login.com. - TLD Abuse: Using cheap TLDs like
.xyz,.top, or.club.
Detection Tip: Look for fuzzy matches against your brand name and monitor newly registered domains that contain your keywords.
Layer 2: The Hosting (The Ground)
Where does the fake site live?
- Compromised CMS: Attackers hack a vulnerable WordPress site and hide their phishing page in a subdirectory (
legit-site.com/wp-content/uploads/login.html). This leverages the good reputation of the hacked site. - Bulletproof Hosting: Providers that ignore abuse reports.
- Cloud Functions: Hosting static pages on Azure Blobs or AWS S3 buckets to use the trusted reputation of Microsoft or Amazon domains.
Detection Tip: Analyze the IP reputation and hosting provider. High-risk ASNs are a red flag.
Layer 3: The Certificate (The Lock)
The green padlock is no longer a sign of safety. Thanks to free automated CAs like Let's Encrypt, 80%+ of phishing sites now have valid SSL certificates.
Detection Tip: Don't trust the padlock. Inspect the Certificate Transparency (CT) logs. A certificate issued for a suspicious domain is an early warning sign, often appearing before the spam email is even sent.
Layer 4: The Delivery (The Hook)
This is the email or SMS. It often uses:
- Spoofed Headers: Making the email look like it came from an internal executive.
- Open Redirects: Links that start with a trusted domain but redirect to the malicious one (
google.com/url?q=http://evil.com).
Disruption Strategy
You can't just block the email. You need to dismantle the infrastructure.
- Report the domain to the registrar.
- Report the hosting to the ISP.
- Submit the URL to Safe Browsing lists (Google, Microsoft).
Conclusion
Phishing is an infrastructure play. By monitoring domains, IPs, and certificates, you can spot the construction of the trap before your users step into it. Tools like isMalicious give you the visibility to see these layers and block them at the network level.
Related articles
 May 10, 2026AI-Enabled Device Code Phishing: How OAuth Tokens Became the New Credential Theft Target
May 10, 2026AI-Enabled Device Code Phishing: How OAuth Tokens Became the New Credential Theft TargetDevice code phishing turns a legitimate OAuth flow into a token theft path. Learn how AI-assisted lures, Entra ID abuse, and session token replay change phishing detection in 2026.
 May 2, 2026Compromised Domains in Phishing: When Trusted Sites Become Attack Infrastructure
May 2, 2026Compromised Domains in Phishing: When Trusted Sites Become Attack InfrastructureAttackers increasingly host phishing pages, redirects, and malware on compromised legitimate domains. Learn why reputation bypass works and how to detect hidden malicious paths.
 Apr 10, 2026Domain Lookup for Phishing and C2 Infrastructure Detection
Apr 10, 2026Domain Lookup for Phishing and C2 Infrastructure DetectionPhishing campaigns and malware operations depend on domain infrastructure that leaves detectable traces. Learn how advanced domain lookup techniques help security teams uncover phishing sites and command-and-control servers before they compromise your organization.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker