The Splinternet: Navigating a Fragmented World Wide Web
The global internet is fracturing into regional, regulated intranets. We explore the rise of the "Splinternet" and its impact on cybersecurity and global business.
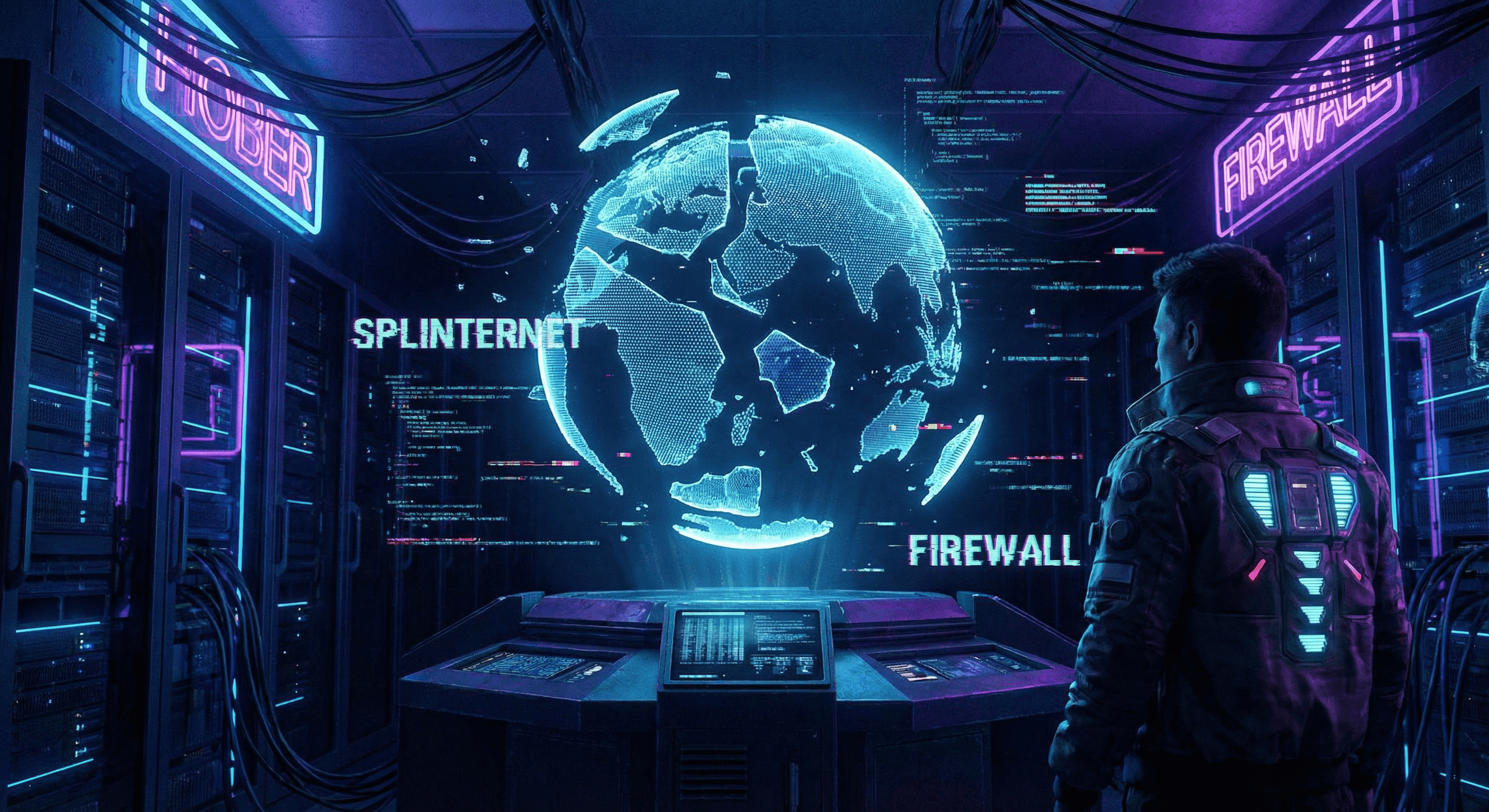
The End of the Global Village?
The vision of a single, open internet is fading. Governments are increasingly building digital borders—firewalls, censorship systems, and data localization laws—creating a fragmented Splinternet.
Drivers of Fragmentation
- National Security: Countries want to control their information space and protect critical infrastructure from foreign cyberattacks.
- Data Sovereignty: Laws like GDPR (Europe) and others require citizen data to be stored locally, complicating global cloud architecture.
- Censorship: Regimes restrict access to foreign news and social media to control the narrative.
Cybersecurity Implications
- Compliance Nightmares: Security teams must navigate a patchwork of conflicting regulations.
- Blind Spots: Threat intelligence sharing becomes harder across digital borders.
- Balkanized Infrastructure: Companies must build separate stacks for different regions (e.g., "China stack" vs. "Global stack").
Navigating the Divide
- Geo-Blocking: Using IP Intelligence to route traffic and enforce regional restrictions.
- Localized Threat Intel: Understanding that threats in one region (e.g., specific malware) may not be relevant in another.
Related Reading
Related articles
 May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams Sane
May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams SaneA SOAR playbook without enrichment is a ticket printer. A SIEM with unbounded threat feeds is a bill. Here is a practical way to design enrichment for Splunk, Sentinel, or Elastic-style stacks—what to store, when to run playbooks, and what to report upward.
 Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network Edge
Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network EdgeReal-time IP reputation checks give you the power to identify and block malicious actors the moment they connect to your systems. Discover how to implement automated threat detection that works at machine speed, not analyst speed.
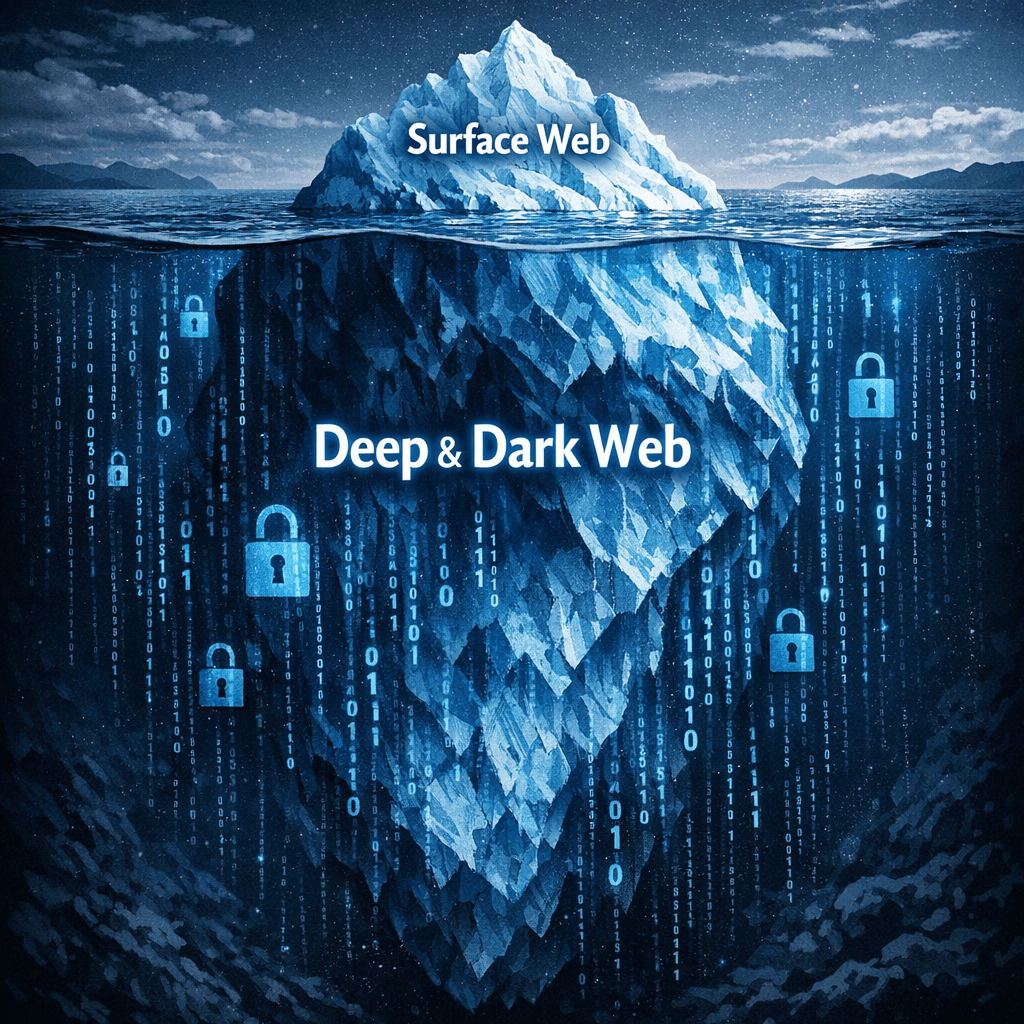 Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?
Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?Confused by the Dark Web and Deep Web? We explain the difference and where cyber threats like stolen credentials and malware actually live.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker