How Hackers Use "Typosquatting" to Trick You (and How to Spot It)
Typosquatting relies on your fingers slipping. Learn how attackers register look-alike domains to steal your data and how to check URLs before you click.
The Art of the Typo
Have you ever typed gogle.com instead of google.com? Hackers count on it. Typosquatting (or URL hijacking) is a technique where attackers register domains that are very similar to popular websites, hoping you'll make a mistake.
Common Typosquatting Tactics
- The Missed Key:
facebok.com(missing 'o'). - The Fat Finger:
twitter.comvstwiiter.com(keys near each other). - The Wrong Extension:
amazon.netinstead ofamazon.com. - The Combo:
apple-support.com(adding words to look official).
The Danger
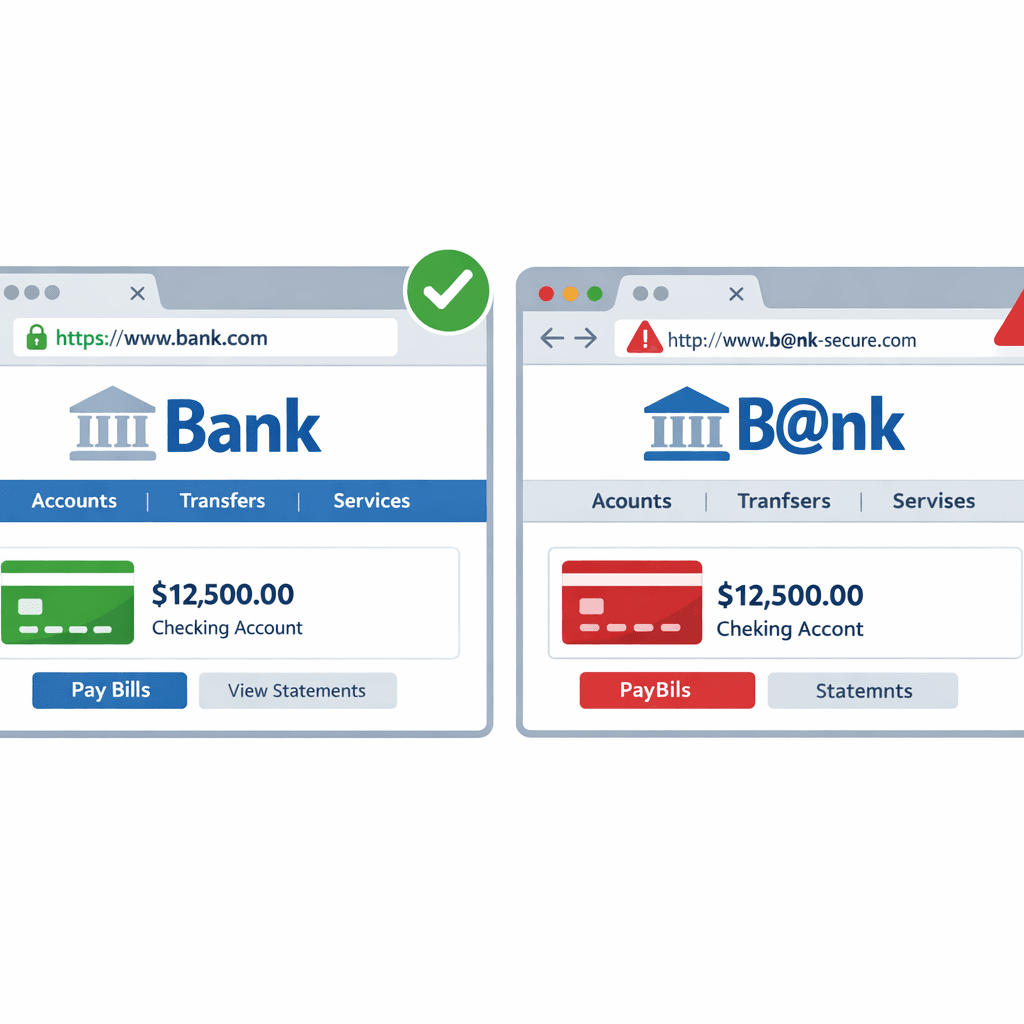
If you land on a typosquatted site, it might look exactly like the real thing.
- Phishing: You enter your login details, and the hacker captures them.
- Malware: The site automatically downloads a virus to your computer.
- Ad Fraud: You are bombarded with spammy ads.
How to Spot a Fake Domain
- Check the URL: Look closely at the address bar. Is it
microsoft.comorrnicrosft.com? - Use a URL Scanner: Before clicking a link in an email, copy and paste it into our URL Scanner. We'll tell you if the domain is suspicious or malicious.
- Bookmark Important Sites: Don't type your bank's URL every time. Use a bookmark to ensure you always go to the right place.
Your eyes can be tricked, but data doesn't lie. Always verify the domain before you trust the site.
Related articles
 May 4, 2026Security LLM and Agent Workflows: When (and How) to Check Malicious Domains, IPs, and URLs Before Acting
May 4, 2026Security LLM and Agent Workflows: When (and How) to Check Malicious Domains, IPs, and URLs Before ActingAI assistants in SOAR, IDEs, and browser extensions can exfiltrate data or run malicious code if they fetch the wrong link. This guide gives guardrails: schema for tool calls, policy tiers, and where threat intelligence checks belong in the loop.
 May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud TeamsTyposquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
 Apr 11, 2026IP and Domain Intelligence: Building a Proactive Cyber Threat Defense
Apr 11, 2026IP and Domain Intelligence: Building a Proactive Cyber Threat DefenseReactive security leaves organizations perpetually one step behind attackers. Learn how combining IP and domain intelligence transforms your security posture from reactive incident response to proactive threat prevention that stops attacks before they start.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker