Smart City Security: Protecting Critical Infrastructure from Cyber Attack
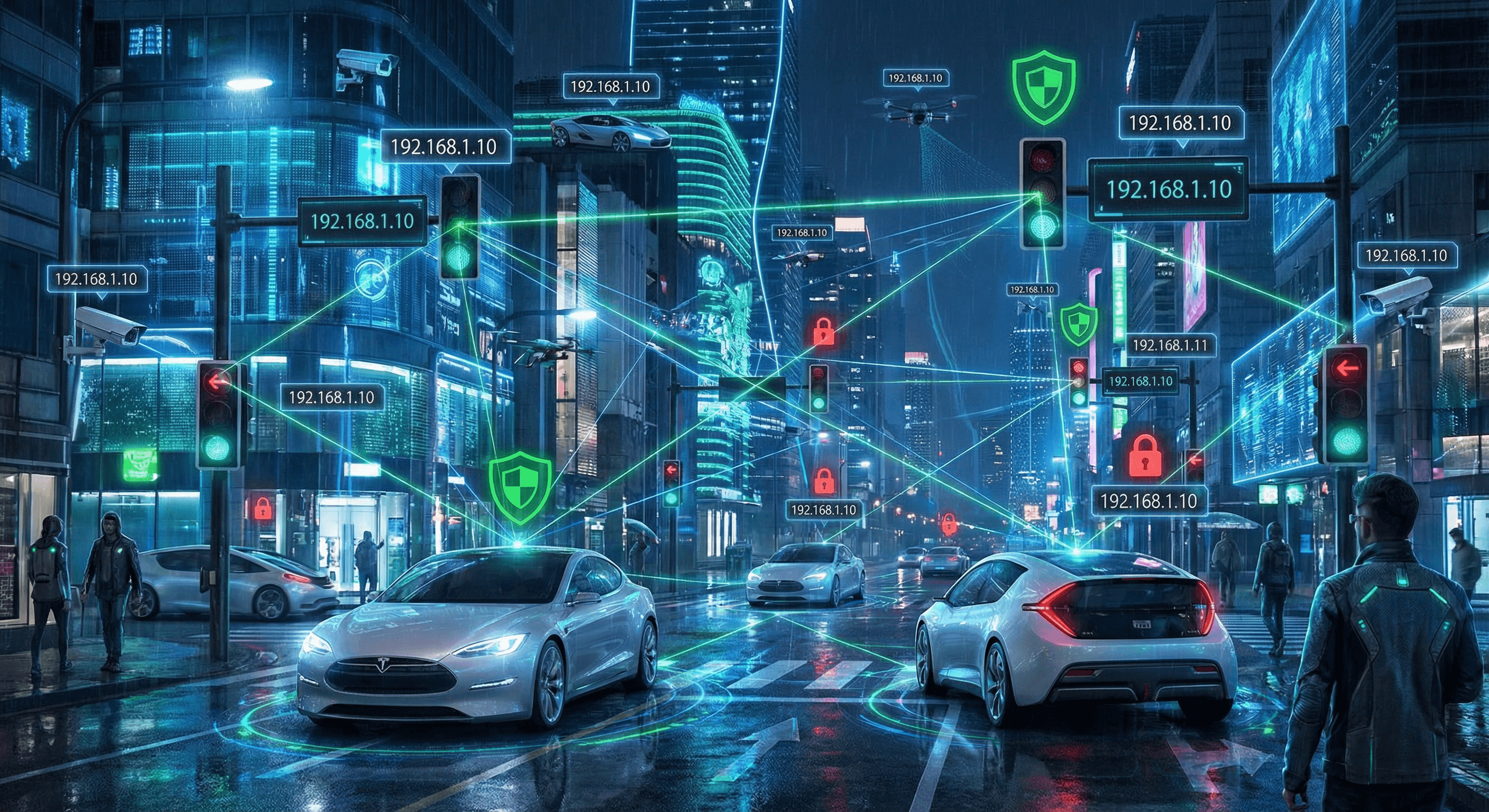
Connected traffic lights, sensors, and water systems create a vast attack surface in modern cities. We examine the vulnerabilities of smart city infrastructure and the cascading failures a cyberattack could cause.
The Connected Metropolis
Smart city initiatives promise efficiency and sustainability, but they also connect 20th-century infrastructure to the internet. Traffic lights, street cameras, water pumps, and environmental sensors are now IP-enabled, often without adequate security.
Weaknesses in Smart Infrastructure
- Traffic Signal Manipulation: Researchers have shown that insecure traffic controllers can be manipulated to create gridlock or facilitate accidents.
- Water Treatment Plant Attacks: Attackers targeting Human-Machine Interfaces (HMIs) can alter chemical levels in water supplies, posing a direct threat to public health.
- Surveillance Camera Hijacking: With default credentials and unencrypted video streams, attackers can spy on citizens or use cameras as botnets for DDoS attacks (Mirai variant).
Securing the Digital Urban Fabric
Smart city projects must prioritize security by design:
- Network Segmentation: Isolate critical infrastructure (water, power) from public Wi-Fi and administrative networks.
- Strong Authentication: Eliminate default passwords. Implement Multi-Factor Authentication (MFA) for administrative access.
- Resilience Planning: Design systems to fail safely. If the internet connection is lost, traffic lights must revert to a safe default state, not chaos.
Network Intelligence for Urban Resilience
Smart cities generate massive data volumes, but security teams must focus on the metadata.
- Threat Level Monitoring: An unexpected spike in outbound traffic from a municipal water pump to an unknown IP indicates a critical threat level.
- Domain Reputation: Smart meters should only communicate with vendor-verified domains. Any DNS request to a domain with a low reputation score (e.g., recently registered, known malware host) must be blocked at the ISP level.
- Geofencing: Critical infrastructure has no business communicating with servers in geopolitical conflict zones. Strict geolocation rules can prevent data exfiltration.
Related articles
 Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks CriticalCut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
 Feb 11, 2026Healthcare IoT Security: The Critical Risk to Patient Safety
Feb 11, 2026Healthcare IoT Security: The Critical Risk to Patient SafetyConnected medical devices (IoMT) introduce life-critical vulnerabilities into hospital networks. From MRI machines to insulin pumps, this guide analyzes the unique challenges of securing legacy firmware and unpatched operating systems.
 Feb 3, 2026IoT Security Threats: Protecting Your Smart Devices from Cyberattacks
Feb 3, 2026IoT Security Threats: Protecting Your Smart Devices from CyberattacksInternet of Things devices are increasingly targeted by cybercriminals. Learn how to identify IoT vulnerabilities, secure smart devices, and protect your network from IoT-based attacks.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker