What is a C2 Server? The Invisible Puppet Masters of the Internet
Discover how hackers control infected devices using Command and Control (C2) servers and how to detect these hidden threats.
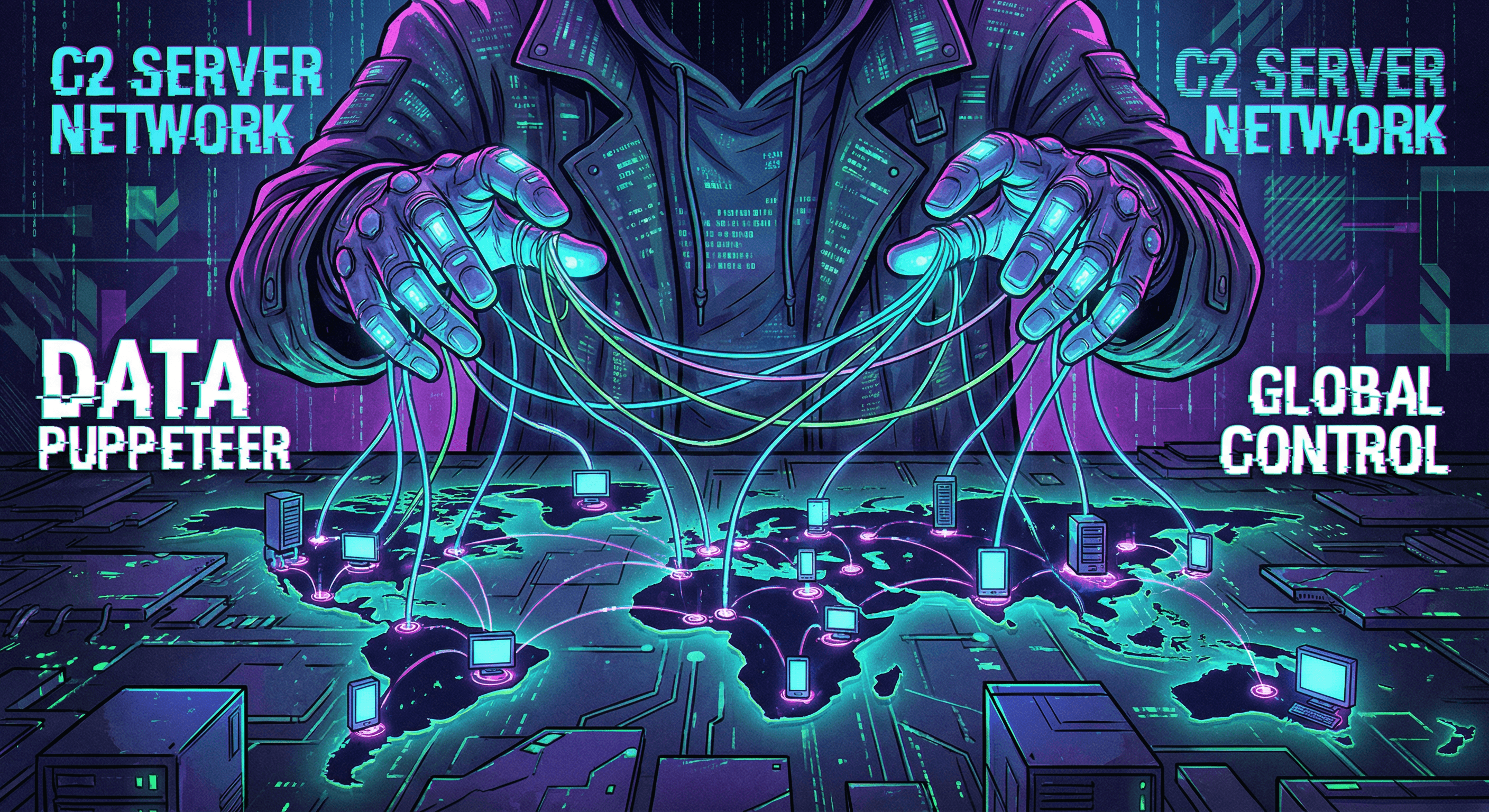
The Silent Controllers
In the world of cyber threats, malware often gets all the attention. But malware is just a soldier; the Command and Control (C2) server is the general giving the orders. Understanding C2 infrastructure is crucial for anyone looking to secure their network against advanced threats.
How C2 Servers Work
A C2 server is a computer controlled by an attacker that sends instructions to systems compromised by malware. Think of it as a "puppet master."
- Infection: A user accidentally downloads malware (e.g., via a phishing email).
- Callback: The malware secretly contacts the C2 server to signal it's ready.
- Command: The attacker sends commands back—steal data, encrypt files (ransomware), or attack other networks.
Why C2 Detection is Hard
Hackers are clever. They hide C2 traffic using:
- Common Ports: Blending in with normal web traffic (HTTP/HTTPS).
- Domain Generation Algorithms (DGA): Rapidly switching domain names to avoid blacklists.
- Social Media: Sometimes using legitimate sites like Twitter or GitHub to post commands.
Detecting C2 Traffic with IsMalicious
You can't always stop the initial infection, but you can cut the communication line.
- Check IP Reputation: Use our IP Scanner to see if an IP address your device is contacting is a known C2 node.
- Monitor DNS Requests: Look for strange, random-looking domain names.
- Analyze Traffic Patterns: Regular "heartbeat" signals often indicate a bot checking in with its master.
Cutting off the C2 server renders the malware useless. Stay vigilant and keep checking your network traffic for these invisible strings.
Related articles
 May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams Sane
May 1, 2026SIEM and SOAR Threat Intelligence Enrichment: Workflows, Field Mapping, and the Metrics That Keep Teams SaneA SOAR playbook without enrichment is a ticket printer. A SIEM with unbounded threat feeds is a bill. Here is a practical way to design enrichment for Splunk, Sentinel, or Elastic-style stacks—what to store, when to run playbooks, and what to report upward.
 Apr 30, 2026Threat Intelligence Risk Scoring: How to Calibrate Reputation, Reduce False Positives, and Defend Your Decisions
Apr 30, 2026Threat Intelligence Risk Scoring: How to Calibrate Reputation, Reduce False Positives, and Defend Your DecisionsA noisy score is worse than no score. Learn what makes a reputation model trustworthy, how to combine multi-source evidence, and how to communicate uncertainty to your SOC and your executives.
 Apr 29, 2026Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)
Apr 29, 2026Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)Not every "datacenter" IP is malicious, and not every Tor exit is a fraudster. This matrix-style guide helps you combine IP type signals with reputation and product context for safer, explainable security decisions.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker