Compromised Domains in Phishing: When Trusted Sites Become Attack Infrastructure
Attackers increasingly host phishing pages, redirects, and malware on compromised legitimate domains. Learn why reputation bypass works and how to detect hidden malicious paths.
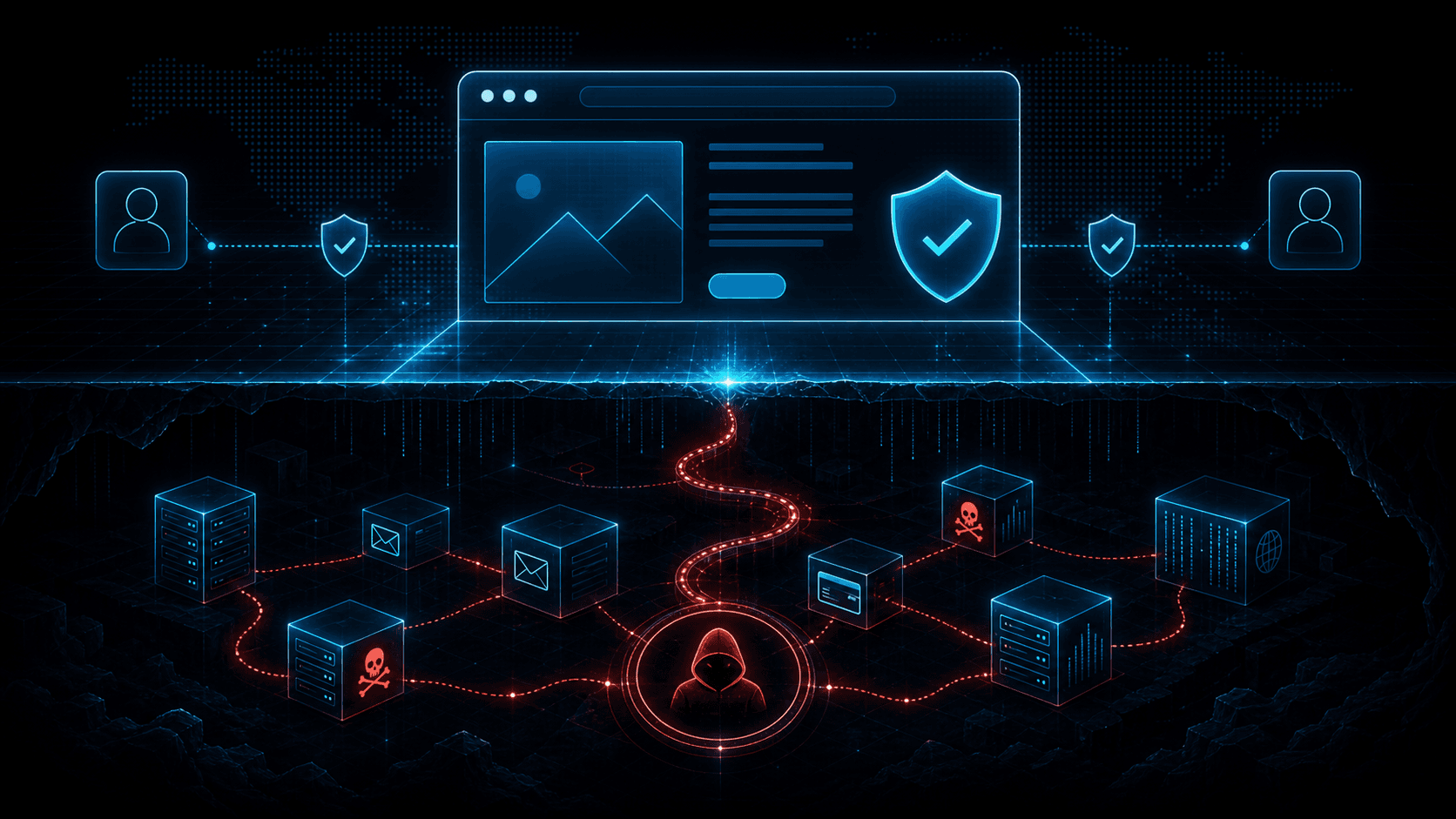
Short answer: A trusted domain can host an untrusted page. Compromised domains let attackers bypass simple reputation checks by hiding phishing kits, redirects, and payloads under legitimate websites. Defenders need URL-level, path-level, redirect, and hosting context.
Many security controls treat domain age and reputation as positive signals. That makes sense: a domain registered ten years ago with normal traffic is usually less suspicious than a domain created this morning. Attackers know this, so they compromise legitimate websites and host malicious content inside them.
The domain may belong to a small business, school, nonprofit, abandoned WordPress site, vendor portal, or personal blog. The organization that owns it may have no connection to the phishing campaign. But to a victim and to some filters, the URL begins with a familiar, long-lived domain.
This is reputation bypass. The attacker borrows trust instead of building it.
How Compromised Domains Are Used
Attackers use compromised domains in several ways:
- Hosting full phishing pages under hidden paths.
- Hosting redirectors that send victims to final phishing kits.
- Serving malware payloads.
- Hosting fake invoices or document viewers.
- Injecting malicious JavaScript into existing pages.
- Creating subdirectories that mimic trusted brands.
- Using open redirect vulnerabilities.
- Staging images and assets for phishing emails.
Sometimes the compromised site is only one hop in a chain. The email link points to a legitimate domain, which redirects through another host, which lands on a phishing page. Each hop complicates analysis and takedown.
Why Domain-Only Reputation Fails
Domain-level reputation is useful but incomplete. A domain can contain both benign and malicious content. Blocking the entire domain may break legitimate traffic. Allowing the entire domain may permit the malicious path.
Attackers exploit this tension. A phishing URL under legitimate-site.example/wp-content/uploads/secure-login.html may inherit the domain's good reputation. If the scanner only checks the root domain, it may miss the specific path.
Defenders need deeper analysis:
- Full URL reputation.
- Path and filename patterns.
- Redirect chain inspection.
- Hosting IP reputation.
- Page content and form behavior.
- Certificate and DNS changes.
- Historical sightings.
- Relationship to known campaigns.
For an infrastructure breakdown, see Anatomy of Phishing Infrastructure and Domain Lookup for Phishing Detection.
Common Compromise Sources
Compromised domains often come from ordinary web hygiene failures:
- Outdated CMS plugins.
- Weak admin passwords.
- Exposed admin panels.
- Stolen FTP or hosting credentials.
- Abandoned sites.
- Vulnerable upload forms.
- Misconfigured storage buckets.
- Compromised web developers or agencies.
Attackers prefer sites where malicious files can remain unnoticed. Small sites with little monitoring are attractive. So are sites with many upload directories, old plugins, or weak hosting isolation.
Detection Signals
Hunt for:
- New suspicious files in upload directories.
- Login forms on pages that should not have authentication.
- Brand names in unexpected URL paths.
- Base64 or obfuscated scripts in pages.
- Redirects to newly registered domains.
- Traffic spikes to obscure paths.
- External reports for URLs under your domain.
- Search engine warnings.
- Certificate issuance for unexpected subdomains.
For inbound protection, scan full URLs in emails and chat messages. Resolve redirects safely. Check each hop. Enrich both domains and IPs. A trusted first domain followed by a suspicious final host is still dangerous.
Response for Site Owners
If your domain is compromised:
- Take the malicious content offline.
- Preserve copies for investigation.
- Patch the vulnerable CMS, plugin, or upload path.
- Rotate hosting, CMS, FTP, and admin credentials.
- Review web server logs for upload and access patterns.
- Check for additional hidden files.
- Submit cleanup requests to browsers and blocklists if flagged.
- Monitor for reinfection.
Do not remove only the visible phishing file. Attackers often leave backdoors or additional droppers.
Response for Defenders Receiving the URL
If your users receive links to compromised domains, avoid a binary "good domain or bad domain" decision. Analyze the exact URL and redirect chain. Block the malicious path where possible. If the site continues serving malicious content, block the domain temporarily and document business impact.
Report to the domain owner, hosting provider, and relevant safe browsing channels. Include exact URLs, timestamps, screenshots, and payload hashes if available.
URL-Level Analysis Workflow
A mature workflow starts with the full URL, not the root domain. Preserve the original link exactly as received, including path, query string, fragment, and any URL encoding. Attackers often hide payload routing in parameters or use multiple encoded redirects to confuse scanners.
Resolve the redirect chain in a sandbox. Record each hop, status code, destination, hosting IP, certificate, and page title. Some phishing infrastructure serves benign content to scanners and malicious content to victims, so test with care and avoid interacting with credential forms.
Compare the path to the legitimate site's normal structure. A bank-themed login page under a small manufacturing company's upload directory is suspicious even if the domain is old. Look for recently modified files, unfamiliar directories, and filenames that mimic common document-sharing patterns.
Enrich every domain and IP in the chain. The first domain may be legitimate, but the final host or intermediate redirector may have known malicious history. Reputation should be applied to the chain, not only the first click.
Business Continuity Decisions
Blocking compromised legitimate domains can be tricky. A university site, vendor portal, or customer domain may host one malicious path and thousands of benign pages. Blocking the root domain could disrupt business. Allowing everything could expose users.
Use layered decisions. Block the exact URL first when possible. Block suspicious paths or redirect patterns if the platform supports it. Temporarily block the full domain when active exploitation is broad, the site serves malware, or path-level blocking is not reliable.
Document the reason for each block. When users ask why a known partner domain is blocked, analysts should be able to explain that a specific path or redirect chain was malicious. Clear documentation reduces pressure to prematurely allow risky traffic.
Monitoring Your Own Domains
Organizations should monitor their own domains as possible attack infrastructure. Search for unexpected paths in web logs, sudden traffic to obscure files, outbound reports from security vendors, and new web shells. Monitor certificate transparency for unexpected subdomains. Watch for files uploaded outside normal deployment workflows.
If your domain appears in phishing campaigns, response is not only cleanup. It is also brand protection. Victims may associate the attack with your organization even if you were also a victim. Fast takedown, transparent communication, and post-cleanup monitoring help preserve trust.
Metrics to Track
Track compromised-domain URLs by source, time to detect, time to block, time to report, and time to cleanup confirmation. For inbound defense, track how often phishing links use compromised legitimate domains versus newly registered domains. This helps tune controls away from domain-only decisions.
Track redirect-chain verdicts too. If most malicious links rely on two or three hop chains, invest in tooling that safely resolves and analyzes those chains before delivery.
Analyst Pitfalls
Do not assume that a clean root domain means a clean URL. Do not assume that HTTPS means safety. Do not ignore query parameters. Do not stop after the first redirect. Do not rely only on screenshots because some pages change by geography, user agent, or time.
Most importantly, do not punish the victim owner of a compromised domain without evidence. Many small organizations become unwilling hosts because of neglected CMS software. The goal is cleanup and protection, not blame.
30-Day Detection Upgrade
In the first week, update email and chat security rules to preserve and analyze full URLs, not only root domains. Ensure logs store the original link and the final redirected destination.
In the second week, add redirect-chain analysis for suspicious links. Even if full automation is not available, analysts should have a repeatable sandbox workflow for resolving chains safely.
In the third week, tune allowlists. Old broad domain allowlists are dangerous when compromised domains are common. Replace broad allows with business-specific rules, path constraints, or safer exceptions where possible.
In the fourth week, measure how many suspicious links use compromised legitimate domains. This metric helps leadership understand why domain reputation alone cannot carry the program.
Defensive Content Signals
Compromised pages often look slightly wrong. Brand assets may be loaded from unrelated hosts. Forms may submit to strange endpoints. JavaScript may be obfuscated. The page path may contain random strings, upload directories, or brand names unrelated to the domain owner.
Automated scanners should capture these features. Human analysts should learn to read them quickly. The best decisions combine page content, hosting context, redirect chain, and historical reputation.
Takedown Collaboration
When reporting a compromised domain, be precise and helpful. Include exact URLs, evidence, timestamps, source emails, redirect chains, and any payload hashes. A small site owner may not have a security team. Clear reporting increases the chance of fast cleanup.
If the domain owner does not respond and the site continues harming users, escalate to hosting providers, registrars, and safe browsing programs. Keep records of outreach so business stakeholders understand the response path.
SEO Poisoning and Compromised Domains
Compromised domains also support search poisoning. Attackers inject pages that target popular software, invoices, tax forms, AI tools, or breaking-news queries. Because the host domain may already have search history, malicious pages can sometimes gain visibility faster than a brand-new domain.
Defenders should treat unexpected indexed pages under their domains as a security signal. Search for strange titles, spam keywords, foreign-language pages, and directories that do not match the site. A compromised domain can harm both users and brand trust before anyone reports a phishing email.
For inbound defense, remember that users may arrive through search results, not only email. Browser protection, DNS filtering, and URL scanning should evaluate final landing pages and downloads even when the initial click came from a search engine.
Data to Preserve
Preserve the original URL, redirect chain, page HTML, scripts, downloaded files, hosting IPs, certificates, screenshots, and timestamps. If the page changes later, this evidence helps incident responders and takedown teams understand what happened.
Evidence preservation also helps tune controls. If analysts can compare the malicious HTML, redirect behavior, and hosting infrastructure across cases, they can write better detections than "domain is bad." Over time, those patterns reveal reusable kits, common redirect services, abused CMS paths, and infrastructure clusters that individual URL reports would miss.
That learning loop is where reputation becomes durable defense.
It also improves takedowns.
Threat Intelligence Takeaway
Compromised domains prove that reputation must be contextual. Domain age and historical trust are not enough when a single path can become malicious.
isMalicious helps enrich full URLs, domains, hosting IPs, and related infrastructure. When a trusted-looking link appears in a campaign, reputation context across the chain helps defenders decide whether to allow, block, or investigate.
Frequently asked questions
- Why do attackers use compromised domains for phishing?
- Compromised domains inherit existing trust, age, backlinks, and reputation. Email and web filters may be less suspicious of a known site than a newly registered lookalike domain.
- What are signs that a legitimate domain is compromised?
- Suspicious paths, newly uploaded login pages, unexpected redirects, unfamiliar subdirectories, hidden scripts, unusual certificates, malware detections, and traffic from phishing campaigns are common signs.
- Should defenders block the whole compromised domain?
- It depends. Sometimes path-level or URL-level blocking is safer for business continuity, but active malware delivery or repeated abuse may justify domain-level blocking temporarily.
- How does threat intelligence help with compromised domains?
- Threat intelligence can correlate URL paths, hosting IPs, redirect chains, certificates, and campaign sightings so teams do not rely on domain reputation alone.
Related articles
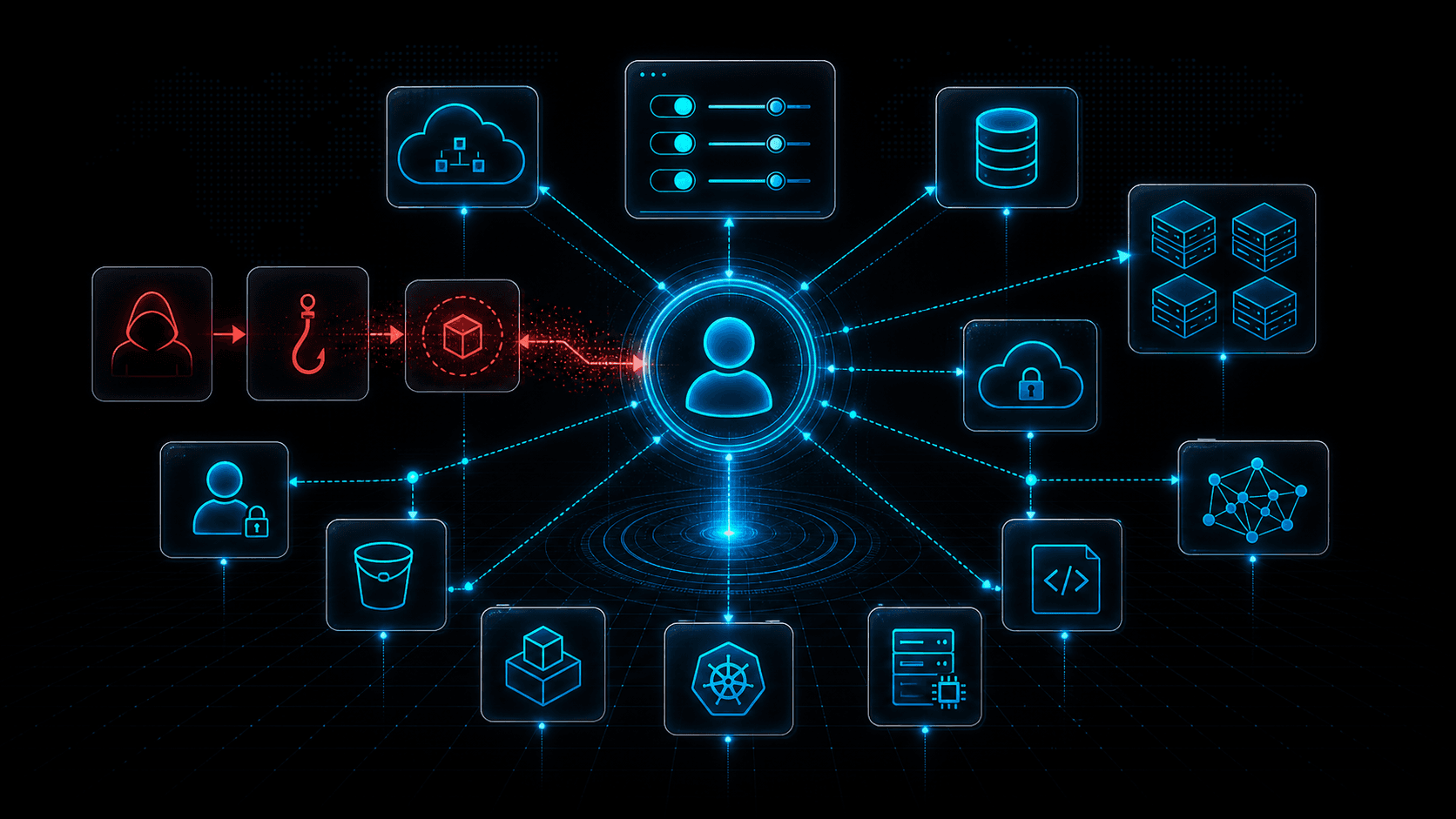 May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill Chain
May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill ChainCloud breaches increasingly target the control plane: identities, tokens, policies, APIs, and automation. Learn how attackers move from one credential to full cloud control.
 Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
 Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC EnrichmentA practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker