File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
A practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
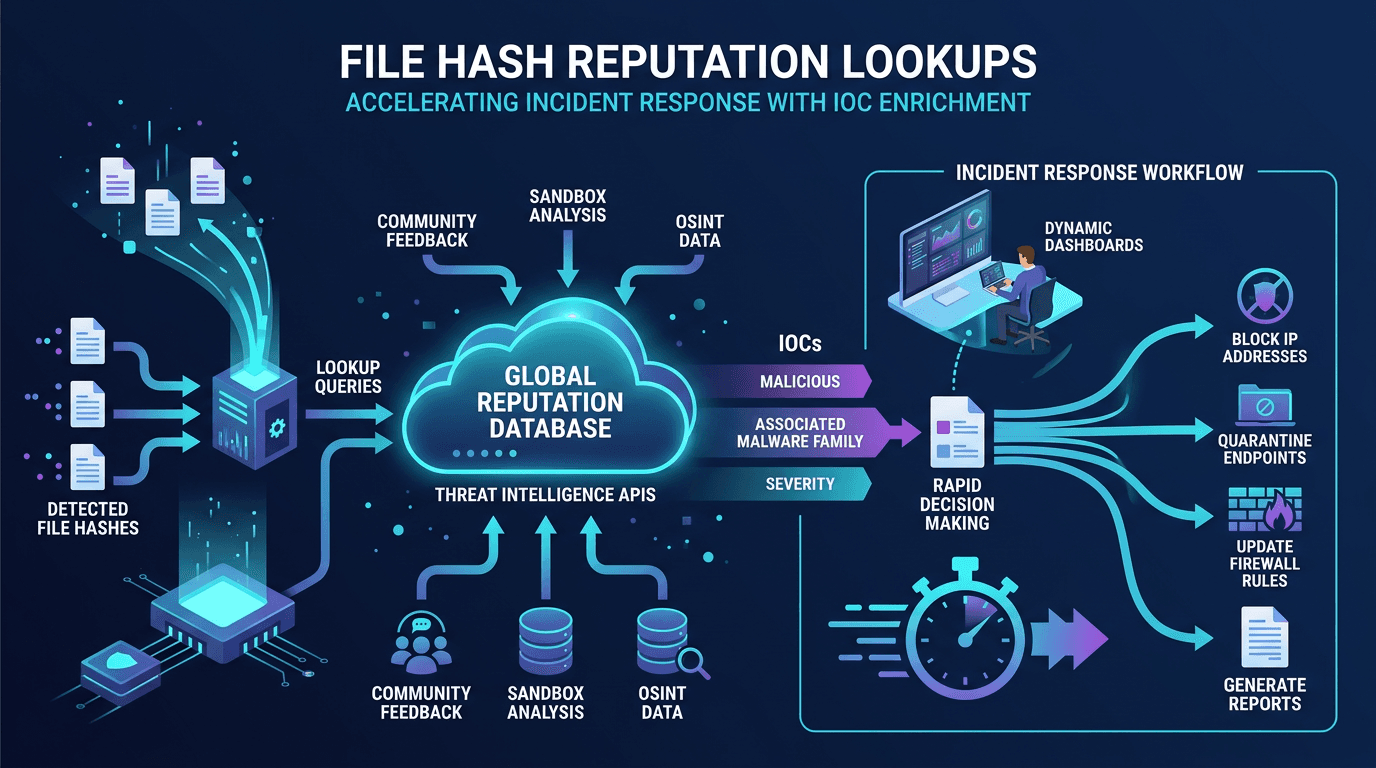
A file hash reputation lookup is one of the highest-leverage operations a security team can automate. A single API call against a well-known reputation source can convert a noisy endpoint alert into a fully contextualized incident—malware family, detection ratio across antivirus engines, first-seen date, associated infrastructure, and behavioral tags appear instantly. Multiply that by every alert every day and the throughput gains for a SOC are enormous. This guide explains how hash reputation lookups work, what data sources power them, how to build robust enrichment pipelines, and how to integrate hash intelligence across SOC, SOAR, incident response, and threat hunting workflows.
What a File Hash Reputation Lookup Delivers
A hash is a cryptographic fingerprint of a file. A reputation lookup takes that fingerprint and returns everything the queried service knows about it. Strong reputation records typically include:
- Detection statistics: How many antivirus engines flag the file, and as what families.
- First seen / last seen: When the file was first observed in the wild and its most recent sighting.
- File metadata: File type, size, compiled language, digital signature state.
- Behavioral data: Sandbox-derived process trees, network indicators, persistence mechanisms, dropped children.
- Associated infrastructure: Domains, IPs, and URLs the sample communicates with.
- Campaign and actor attribution: When available, links to known operations or threat groups.
- Community comments and votes: Analyst-contributed notes or voting scores on platforms that support them.
Receiving this payload before a human analyst opens the alert changes the shape of every investigation. Instead of staring at a naked hash for minutes, the analyst starts with a complete story and spends time on decisions, not data gathering.
Sources of Hash Reputation Data
A mature enrichment pipeline does not rely on a single source. Typical components include:
- Commercial multiscanner services: Aggregate detections from many antivirus engines.
- Open threat intelligence databases: Community-curated IOC repositories.
- Sandbox analysis platforms: Automated behavioral analysis services.
- EDR and XDR vendor clouds: Vendor-specific telemetry and reputation.
- Government and sector sharing: CISA advisories, sector-specific ISACs.
- Infrastructure reputation providers: Services like isMalicious specialize in domain, IP, and URL reputation; correlating a hash’s network connections against these sources adds context.
- Internal telemetry: Your own EDR, mail gateway, and sandbox history—often the highest-confidence source for your environment.
Each source has latency, coverage, and quality trade-offs. Weight them in your enrichment logic so high-confidence sources take precedence and low-confidence sources do not drown them out.
Building an Automated Hash Enrichment Pipeline
A reliable pipeline handles the full lifecycle of hash enrichment:
1. Hash Extraction
Alerts, tickets, emails, and reports arrive in many formats. Your pipeline must extract hashes cleanly. A regex for each algorithm (^[a-fA-F0-9]{32}$ for MD5, {40} for SHA-1, {64} for SHA-256) is a starting point, but also validate against expected content to avoid false positives—random 64-character hex strings are not always hashes.
Normalize aggressively: lowercase hex, strip whitespace, deduplicate. Inconsistent casing is a surprisingly frequent cause of missed matches in enterprise environments.
2. Query Routing
Different sources accept different hash types. Maintain a routing layer that sends the right hash to each source, cross-mapping when a source prefers one algorithm over another. Where a source returns additional hashes (for example, SHA-256 when you queried with MD5), store them for future use.
3. Caching With Short TTLs
Hash reputation changes over time. A sample that is unknown today may light up tomorrow. A cache reduces API load and cost but should respect the freshness tolerance of each data point. Typical TTLs:
- Known-malicious verdicts: Long TTL (days or weeks). Stable.
- Known-clean or unknown verdicts: Short TTL (hours). Likely to change.
- Behavioral data: Medium TTL. Re-query when new sandbox analysis is suspected.
4. Confidence Scoring and Merging
When multiple sources disagree, merge intelligently. Do not treat all sources equally. A simple scheme assigns weights:
- Confirmed-malicious with multiple vendors: High confidence.
- Reputation marker but no consensus: Medium confidence, flag for analyst review.
- Unknown in all sources: Low confidence, rely on behavioral signals.
Encode these as metadata on the enrichment record so downstream automation can make decisions based on confidence, not raw verdict alone.
5. Attachment to Alerts and Tickets
Enrichment that humans never see is wasted effort. Write the result back onto the source alert or ticket in a consistent format. Analysts should see, at a glance: hash, file family, detection ratio, first-seen date, associated infrastructure, and confidence level.
6. Re-Enrichment Over Time
Low-confidence or unknown hashes deserve follow-up. Automate re-queries at 24 hours, 7 days, and 30 days. A sample that was unknown on day zero often becomes a confirmed-malicious IOC by day seven as vendors catch up.
Using Hash Reputation in Incident Response
During active incident response, hash reputation lookups accelerate every major step:
Scoping
When the first sign of compromise is an unfamiliar executable on one endpoint, a hash lookup tells you whether it is known malicious, the likely family, and what other indicators typically accompany it. That context informs immediate hunt queries across the environment for siblings.
Containment
Confirmed-malicious hashes should feed directly into prevention controls: EDR blocklists, email gateway quarantine, web proxy denials, and SIEM rules. The faster this happens after confirmation, the narrower the incident window.
Attribution and Threat Modeling
When a hash maps to a known malware family or campaign, incident responders can anticipate what comes next: typical persistence mechanisms, lateral movement techniques, and exfiltration targets. This shortens containment because you are hunting for the specific next moves rather than generic activity.
Communication and Reporting
A compromise linked to a named ransomware family or threat actor tells the executive story faster than a generic “malicious file detected.” Pair that context with infrastructure reputation—known-bad IPs and domains the hash communicates with—and the narrative becomes board-ready.
Hash Reputation in Threat Hunting
Proactive threat hunting uses hash reputation as both starting point and pivot:
- Rare-hash hunting: Enumerate hashes present on only one or two endpoints; query reputation for each; escalate any with suspicion signals.
- Unsigned-binary hunting: Focus on executables without valid digital signatures; prioritize those with unknown or suspicious reputation.
- Campaign pivot: Take a single known-bad hash, retrieve campaign tags, enumerate all associated hashes, and hunt each across the estate.
- Infrastructure pivot: Start from a confirmed-malicious IP or domain flagged by a reputation provider, enumerate samples that communicate with it, and track those hashes down to endpoints.
Automation turns these into scheduled queries that fire daily or weekly, surfacing candidates for human review. The efficiency gain over manual hunting is large.
Integrating With SOAR Playbooks
SOAR platforms shine at orchestrating hash reputation workflows. A typical alert-enrichment playbook:
- Receive alert.
- Extract and validate hashes.
- Query each configured reputation source in parallel.
- Merge results with confidence weighting.
- Query infrastructure reputation (via isMalicious or similar) for any associated domains or IPs.
- Attach merged enrichment to the ticket.
- Auto-route based on outcome: known-malicious → high priority, unknown → analyst queue, benign → close with annotation.
Well-designed playbooks cut analyst time per alert dramatically and free them to focus on the genuinely ambiguous cases.
Common Pitfalls in Hash Enrichment Programs
Recurring mistakes that blunt the value of hash enrichment:
- Single-source dependence: One provider’s outage breaks enrichment for the entire SOC. Always have fallbacks.
- Ignoring rate limits: Bulk lookups without batching or caching exhaust quotas fast.
- Over-trusting stale verdicts: Cache TTLs that are too long mask evolving threats.
- Silent failures: Pipelines that drop enrichment when a source errors are worse than no enrichment at all—analysts assume the data is complete.
- Alert noise from benign hashes: Widely deployed legitimate software can still trigger detection; combine hash verdict with behavioral context before auto-blocking.
- Weak logging: Without logs of every enrichment request and response, auditing and debugging become impossible.
Privacy, Legal, and Operational Considerations
Submitting file hashes to third-party services is generally privacy-safe because hashes are one-way. However, be aware of nuances:
- Submitting files themselves (rather than just hashes) may expose sensitive internal content. Configure submission policies explicitly.
- Some services log queries and correlate queried hashes with querier identity; your search patterns may reveal information about your incidents. Use designated accounts and sometimes proxy queries.
- Rate limits and contracts: Commercial services enforce fair-use policies; automate within them.
Enterprise contracts with reputation providers typically include private-submission options and stricter data handling commitments for sensitive environments.
Combining Hash Reputation With Infrastructure Reputation
The strongest enrichment pipelines combine hash-level intelligence with infrastructure reputation:
- A hash connects to a specific domain → query the domain against isMalicious → discover the domain is part of a known C2 cluster → escalate the incident.
- A hash is unknown but communicates with an IP flagged as a known malicious proxy → the behavioral context elevates suspicion even without a hash verdict.
- A campaign tied to a hash maps to infrastructure patterns common across a threat actor’s operations → detection engineering can build rules covering the broader pattern, not just the single hash.
This multi-layer enrichment is the difference between a SOC that reacts to alerts and one that understands the broader threat picture behind each alert.
Measuring Enrichment Program Success
Metrics that indicate a healthy hash enrichment pipeline:
- Percentage of alerts with complete enrichment before analyst pickup.
- Median time from alert creation to analyst start (should drop with good enrichment).
- Cache hit rate across the enrichment layer.
- Re-enrichment false negative recovery: Number of initially-unknown hashes later confirmed malicious.
- False-positive suppression rate: Alerts closed automatically because hashes were confirmed benign.
Track these quarterly and tune the pipeline. A mature enrichment layer becomes a silent force multiplier for every other SOC function.
Future Directions: Fuzzy Hashing and AI Enrichment
Beyond exact hashes, fuzzy hashing (SSDEEP, TLSH) helps identify near-duplicate files—valuable against polymorphic malware that changes trivial bytes. Reputation services increasingly expose fuzzy-hash similarity as part of the response, enabling detection of variants that strict hashing misses.
AI-assisted enrichment is also emerging: models that summarize sandbox reports, cluster related samples, and propose likely attribution. These augment rather than replace the deterministic pipeline but can substantially reduce analyst reading time for complex samples.
Conclusion
File hash reputation lookups are among the fastest, highest-value enrichment operations in cybersecurity. By automating hash queries against a balanced portfolio of reputation sources—combined with infrastructure reputation from services like isMalicious—SOCs convert raw alerts into fully contextualized incidents before analysts open them. The time saved is not marginal; it is foundational to running a modern security operation.
Invest in a robust enrichment pipeline: extraction, normalization, multi-source querying, caching, confidence merging, re-enrichment, and attachment to tickets. Measure outcomes and tune aggressively. The organizations that treat hash reputation as infrastructure, not a manual query, consistently detect faster, contain smaller, and ship more defensible narratives to leadership after every incident.
Frequently asked questions
- What is a file hash reputation lookup?
- A file hash reputation lookup is a query against a threat intelligence service using a file's cryptographic hash (MD5, SHA-1, or SHA-256) to retrieve known data about that file—detection ratios, malware family, first-seen date, associated infrastructure, and behavioral tags. It is one of the fastest IOC enrichment operations available to a SOC.
- Which hash should I use for reputation lookups?
- SHA-256 is the modern default and preferred primary key. MD5 and SHA-1 remain widely supported for backward compatibility and appear in older indicator feeds. Good platforms accept all three and cross-map them to the same reputation record.
- How do I automate hash reputation lookups at scale?
- Build a SOAR playbook or SIEM enrichment step that extracts hashes from alerts, queries your reputation provider(s) via API, caches results with a short TTL, and writes the context back onto the alert or ticket. Respect API rate limits, handle unknown hashes gracefully, and re-query after 24 hours and 7 days to catch evolving verdicts.
Related articles
 Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROI
Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROIAn indicator without context is a ticket without an owner. Learn how IOC enrichment APIs work, which fields SOC teams need at each tier, and how to wire them into case management without building a data swamp.
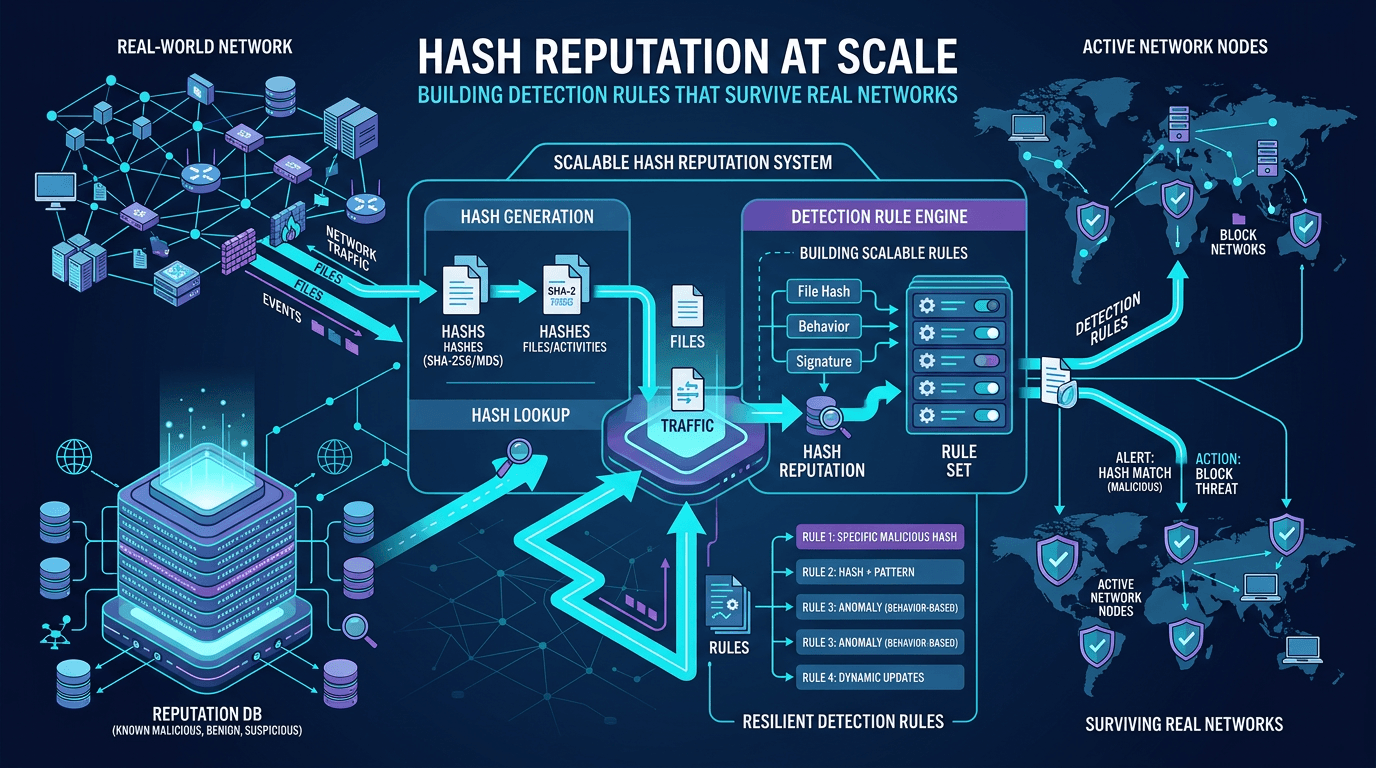 Apr 22, 2026Hash Reputation at Scale: Building Detection Rules That Survive Real Networks
Apr 22, 2026Hash Reputation at Scale: Building Detection Rules That Survive Real NetworksMove beyond one-off hash blocks: design reputation pipelines, reduce false positives, and integrate file intelligence with IP and domain context for enterprise-grade detection engineering.
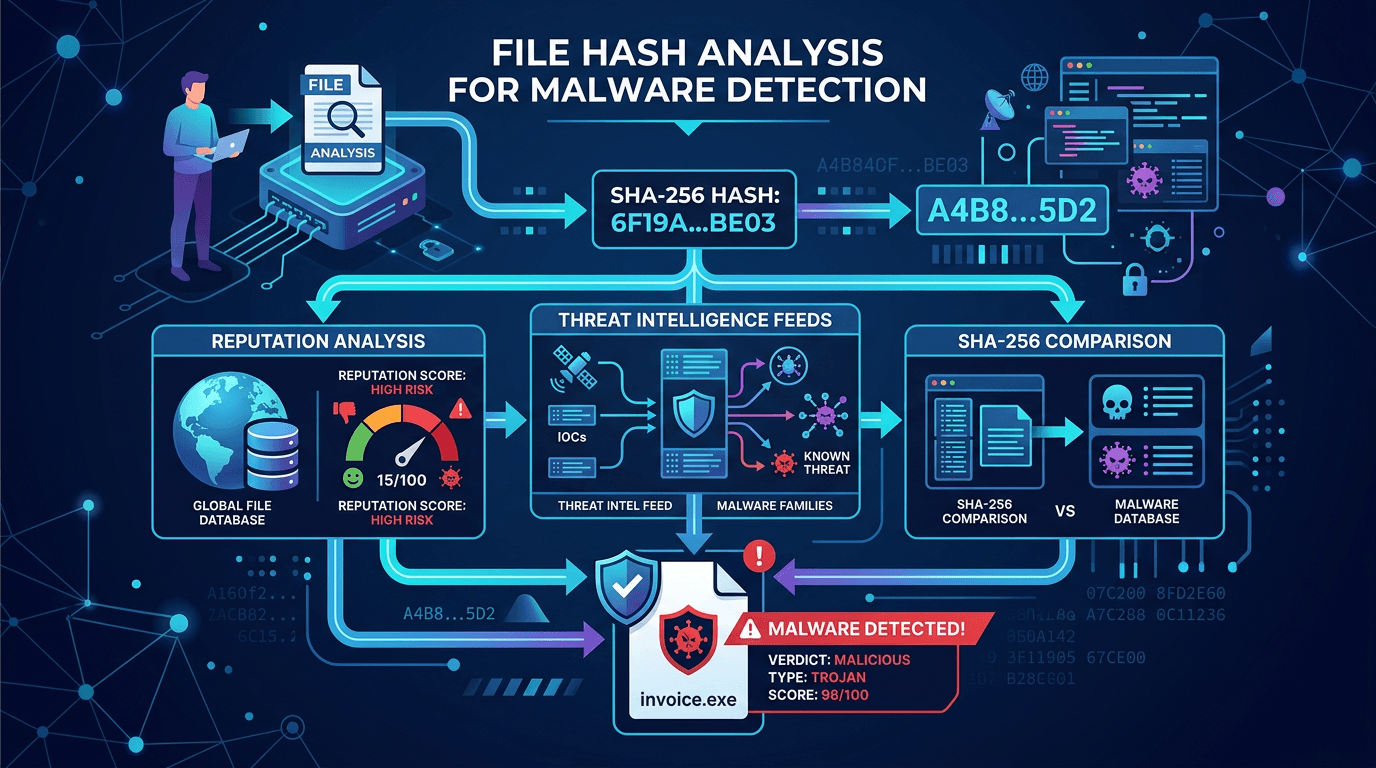 Apr 18, 2026File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel Workflows
Apr 18, 2026File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel WorkflowsLearn how cryptographic file hashes power malware identification, why SHA-256 dominates security tooling, and how to combine hash lookups with broader threat intelligence for fewer false positives.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker