Hands-on detection
engineering
Production-ready detection rules, integration guides, and incident response playbooks — wired to the public REST API at api.ismalicious.com.
Endpoints used in these playbooks
Guides reference the same contract as the OpenAPI spec.
- GET
api.ismalicious.com/checkFull threat analysis (query + optional enrichment level)
- GET
api.ismalicious.com/check/reputationAggregated reputation counts (lighter than full /check)
- GET
api.ismalicious.com/bulk/checkPlan limits and usage for batch lookups
- POST
api.ismalicious.com/bulk/checkBatch domains, IPs, and URLs in one JSON request
- GET
api.ismalicious.com/blocklist/statsEntry counts and last-updated times (no auth)
- GET
api.ismalicious.com/blocklist/download/blocklist-ips-critical.txtPlain-text blocklists (plan-gated full vs sample)
All playbooks
Filter by difficulty or role. Each card shows the minimum plan needed to run the API examples.
Lightweight Reputation Checks vs Full Threat Analysis
Choose GET /check/reputation when you only need vendor-style verdict counts, and reserve GET /check for investigations. Includes curl examples and when to add /check/whois or /check/location.
A clear decision tree for API calls: faster reputation polling for high-volume paths, full /check for triage, and narrow endpoints for geo or WHOIS-only questions.
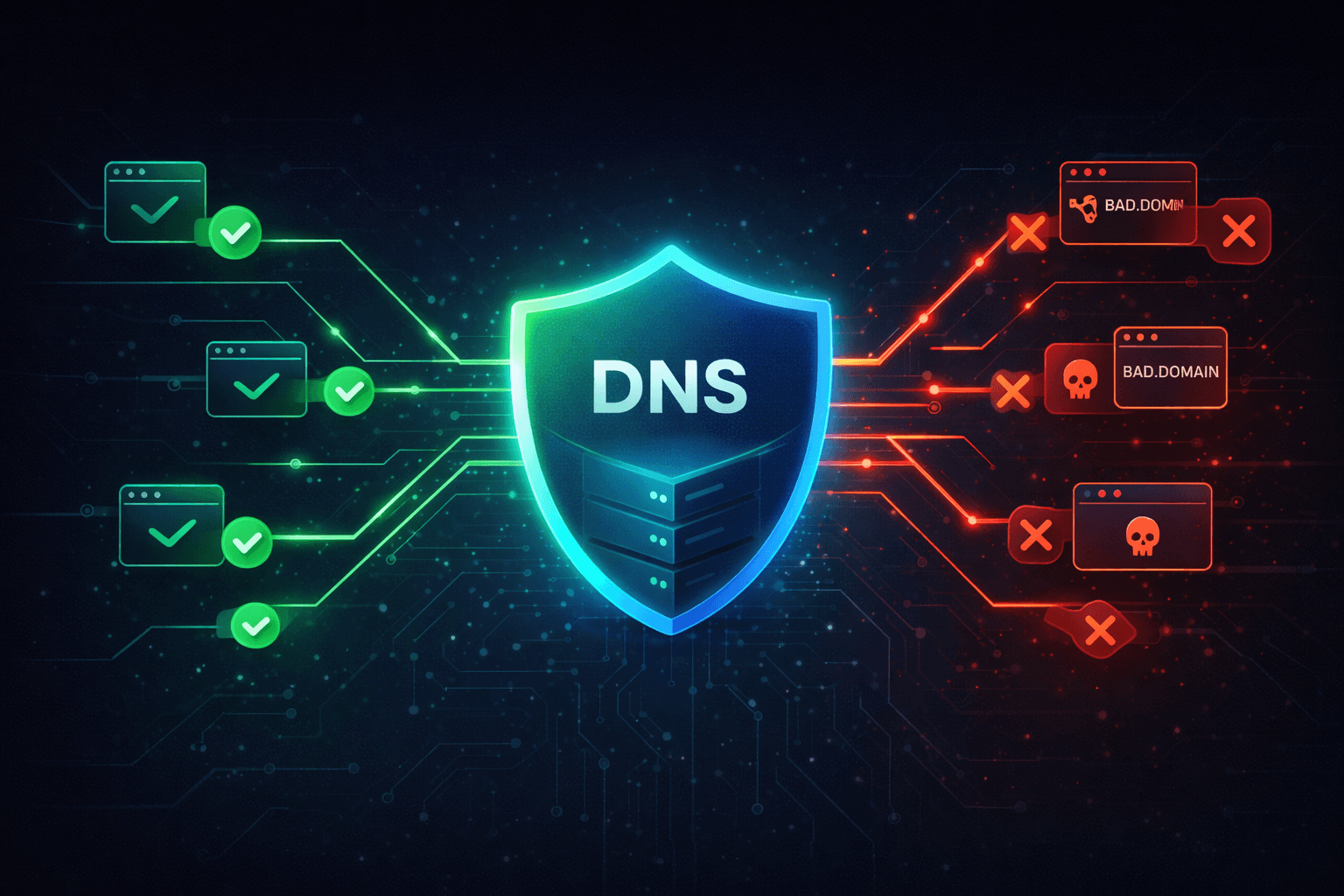
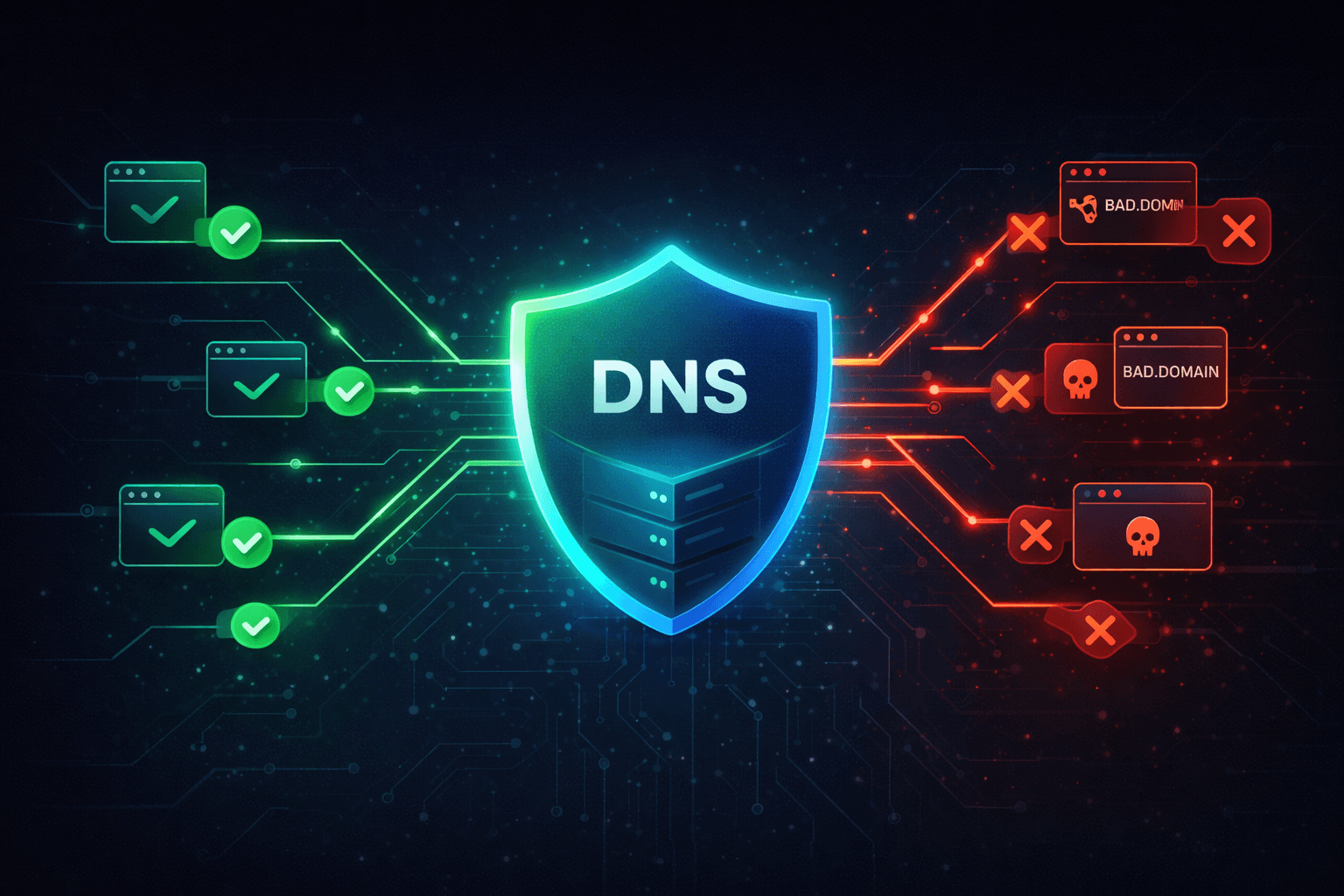
Automating Malicious IP and Domain Blocklist Downloads
Use GET /blocklist/stats for freshness, then GET /blocklist/download/{filename} to pull plain-text lists into your WAF, DNS firewall, or SOAR— with curl, diff, and cron-friendly patterns.
A scheduled job that downloads the correct blocklist file for your plan, detects changes, and feeds only deltas into downstream controls—aligned with the public HTTP API.
Bulk IOC Triage with the isMalicious Batch API
Turn a CSV or SIEM export into scored verdicts in minutes. Use GET /bulk/check for limits, then POST /bulk/check with mixed domains, IPs, and URLs—curl and Python included.
A repeatable batch pipeline that classifies hundreds of IOCs per run with per-entity malicious flags, confidence, source counts, and categories—without hammering single-entity endpoints.
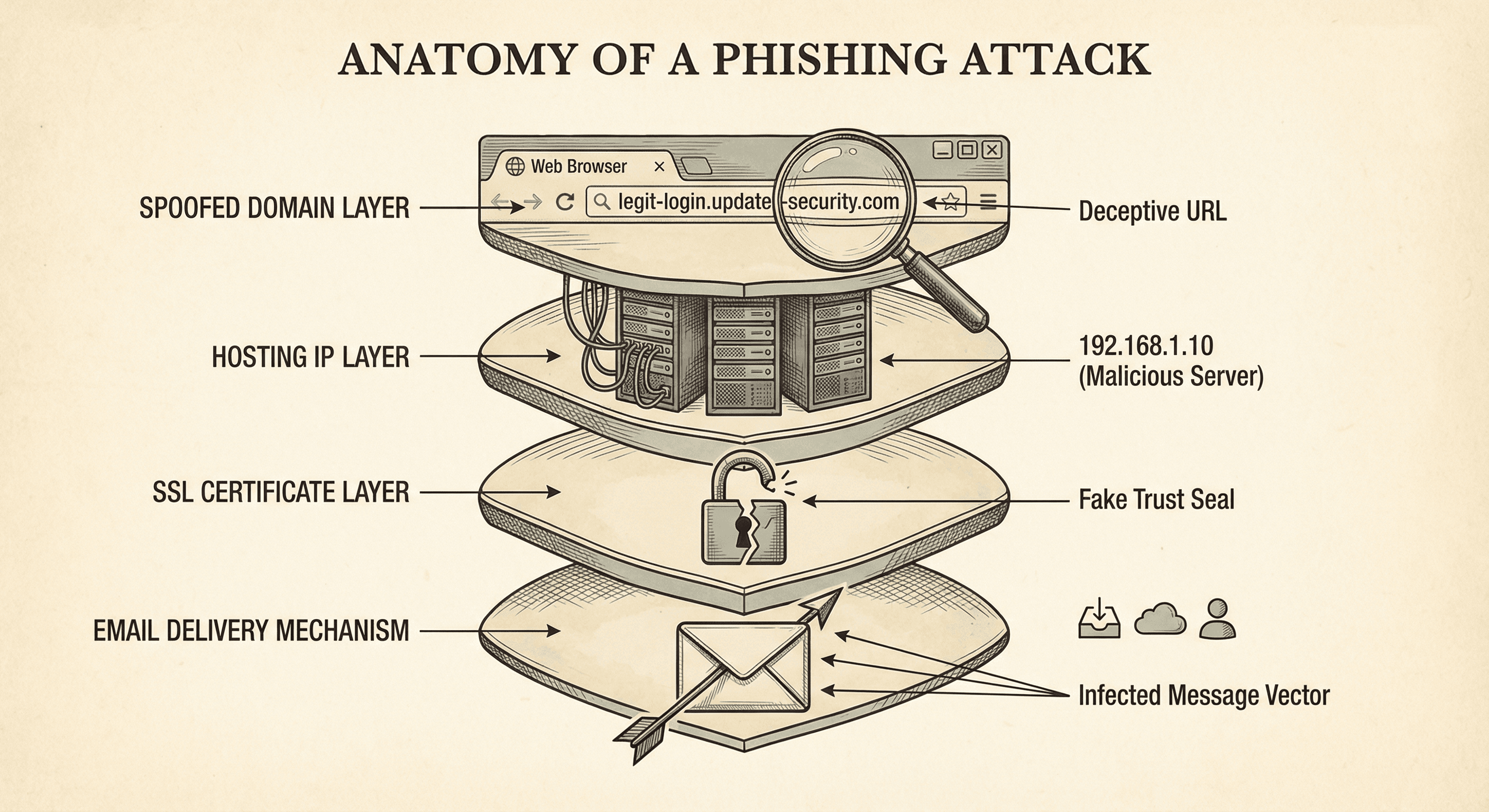
Phishing Domain Detection with Typosquatting Analysis
Build an automated pipeline to detect phishing domains targeting your brand. Uses typosquatting generation, DNS resolution, and isMalicious reputation checks to catch threats before victims do.
An automated daily scan that detects typosquatting domains targeting your brand, with live reputation checking and alerting when a suspicious domain becomes active.
Blocking Malicious IPs with Firewall Automation
Automatically update firewall blocklists using isMalicious threat data. Covers pfSense, iptables, Palo Alto, and cloud security groups (AWS/GCP/Azure). Zero manual effort after setup.
A cron-driven pipeline that automatically blocks malicious IPs at the network edge, updated every 6 hours from live threat intelligence.
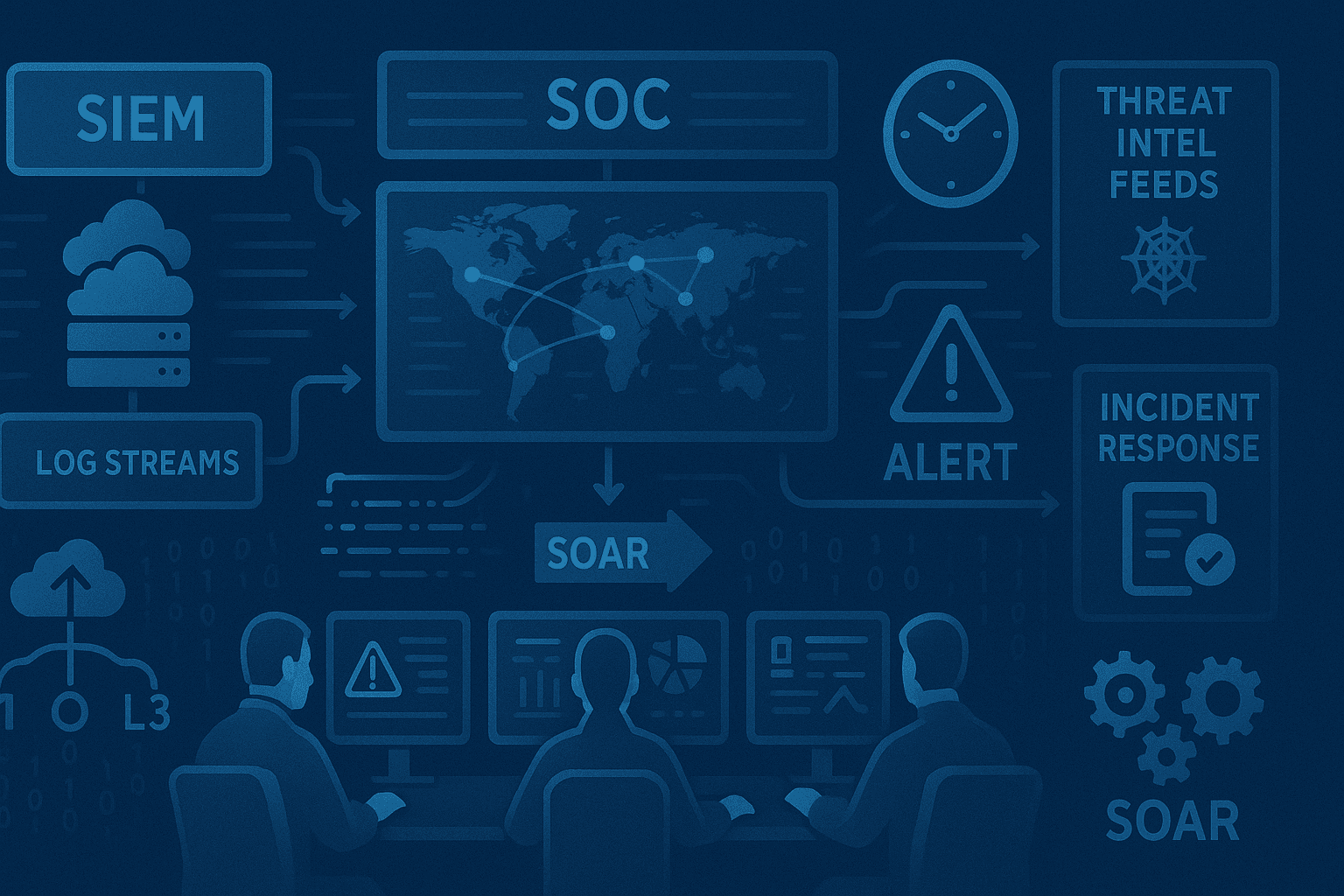
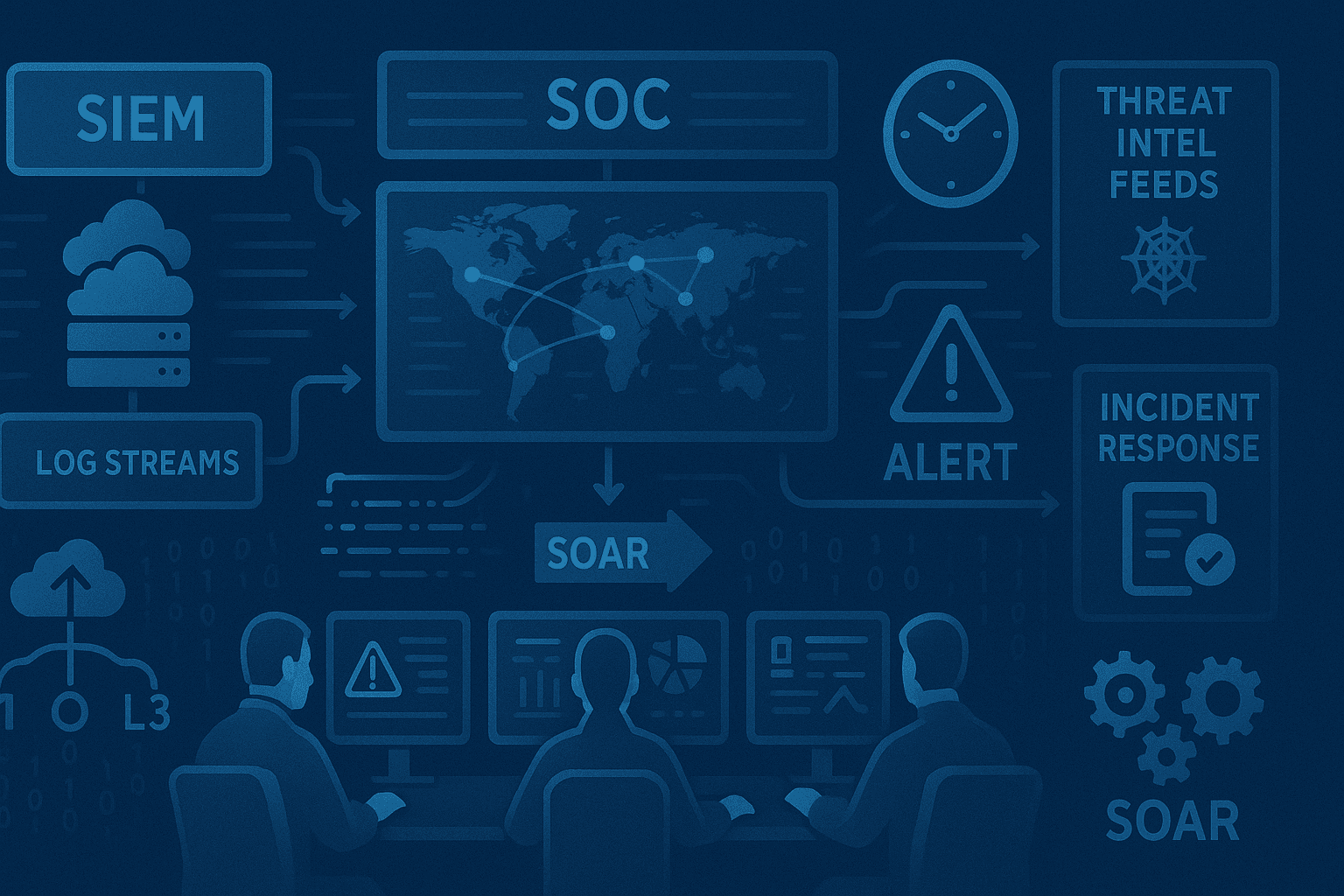
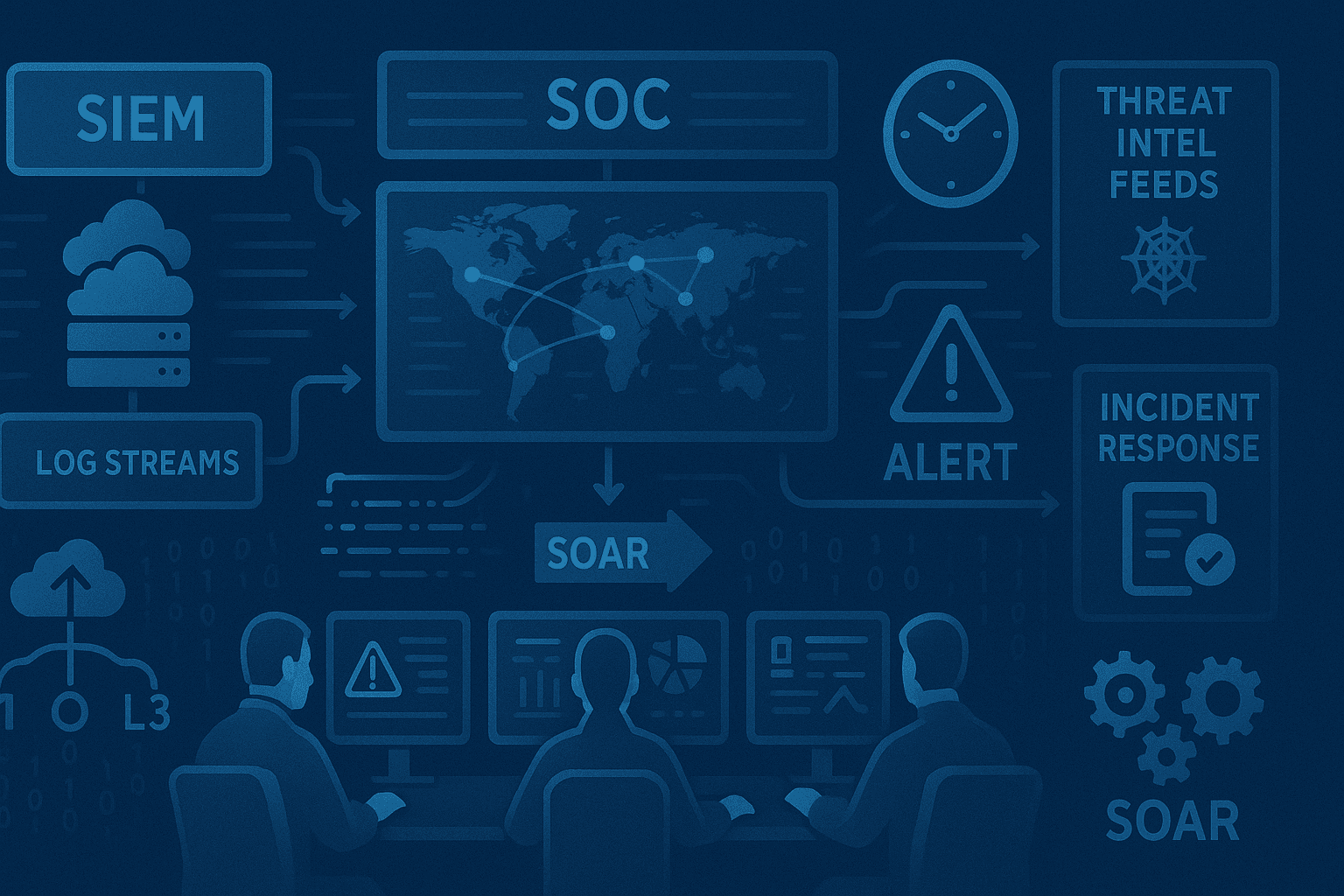
Enriching SIEM Alerts with isMalicious Threat Intel
Integrate isMalicious API into Splunk and Elastic to auto-enrich every alert with IP/domain reputation, categories, and risk scores. Includes lookup tables and correlation searches.
Every SIEM alert automatically enriched with threat reputation, category, and confidence score — cutting triage time by up to 60%.
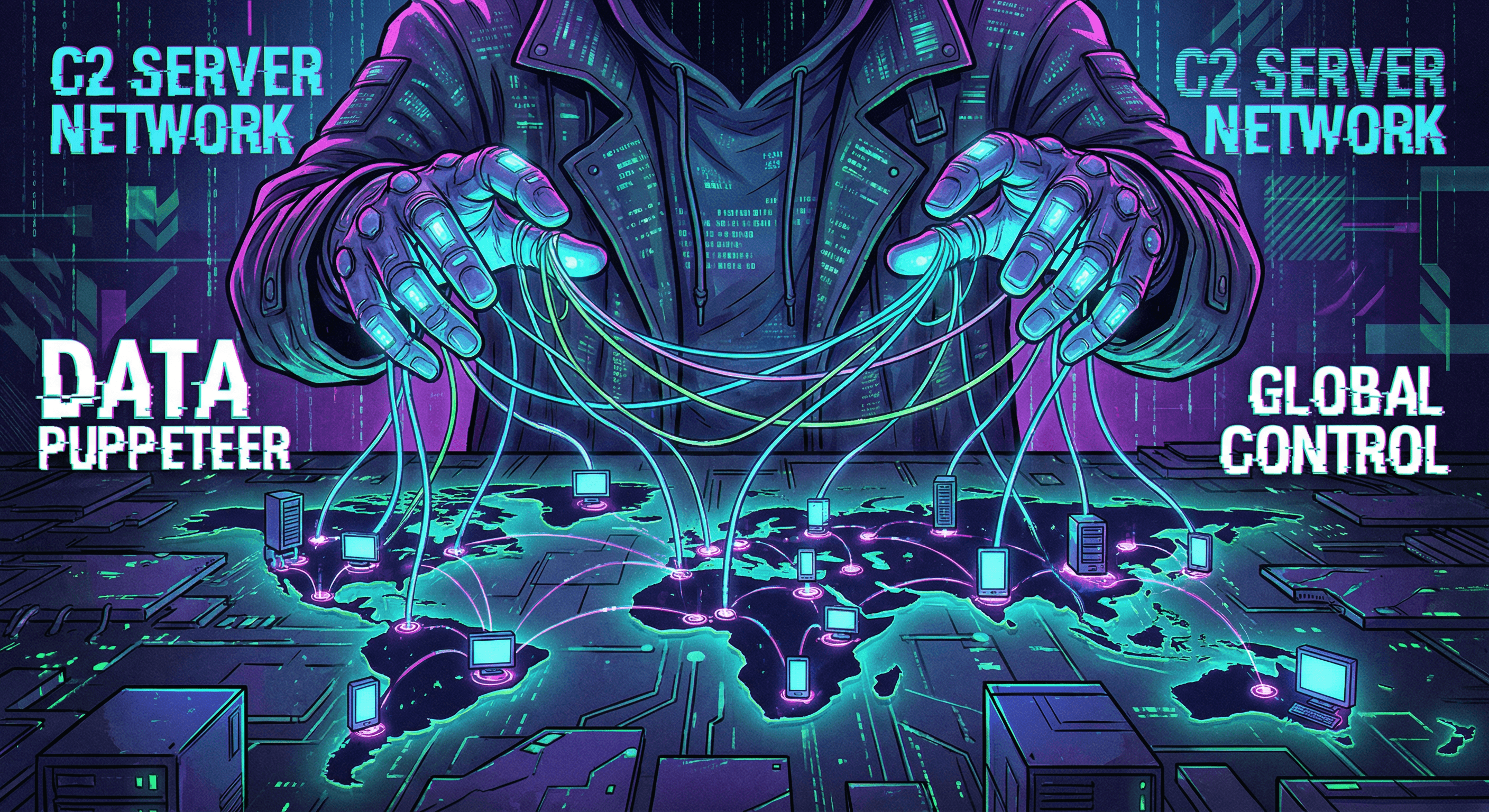
Detecting C2 Beacons with YARA Rules
Build and deploy YARA rules to detect Command & Control beacon traffic in your network. Includes copy-paste rules for Cobalt Strike, Sliver, and Metasploit.
A set of production-ready YARA rules that detect Cobalt Strike, Sliver, and Metasploit C2 beacons, integrated into your SIEM pipeline.
Frequently asked questions
What are isMalicious playbooks?
Step-by-step guides for security teams: detection rules (YARA, SIEM), incident response workflows, and integrations that call the public threat intelligence API at https://api.ismalicious.com. Each playbook includes copy-paste examples you can adapt.
How do I authenticate API calls in these guides?
Use the X-API-KEY header with a Base64-encoded string of your apiKey:apiSecret from the dashboard (Account → API). The same pattern is used across /check, /bulk/check, and blocklist downloads.
Where is the official API reference?
Interactive documentation and OpenAPI are at ismalicious.com/api-docs. You can also try requests in the API Playground at ismalicious.com/api/playground.
Do playbooks replace the web report or dashboard?
No. The dashboard and one-off reports are for analysts; playbooks show how to automate the same intelligence in your SIEM, firewalls, or scripts using the REST API.
Which API endpoints do the playbooks use?
Guides reference documented endpoints such as GET /check, GET /check/reputation, POST /bulk/check, GET /blocklist/stats, and GET /blocklist/download/{filename}. Exact URLs and parameters match the OpenAPI spec.
Are rate limits and plan tiers documented?
Yes. The Free tier includes rate-limited API access (100 requests/month); Basic ($49/mo) lifts that to 2,000/month with bulk and blocklist support; Pro ($99/mo) adds streaming and webhooks. See /pricing for the full matrix.
Run any of these today
Free API key, 100 checks/month, no credit card. Most playbooks run on the Free or Basic ($49/mo) tier.
Get new playbooks by email
One short email when we publish. No spam, unsubscribe anytime.