Cloud Control Plane Attacks: Why Identity Is the New Kill Chain
Cloud breaches increasingly target the control plane: identities, tokens, policies, APIs, and automation. Learn how attackers move from one credential to full cloud control.
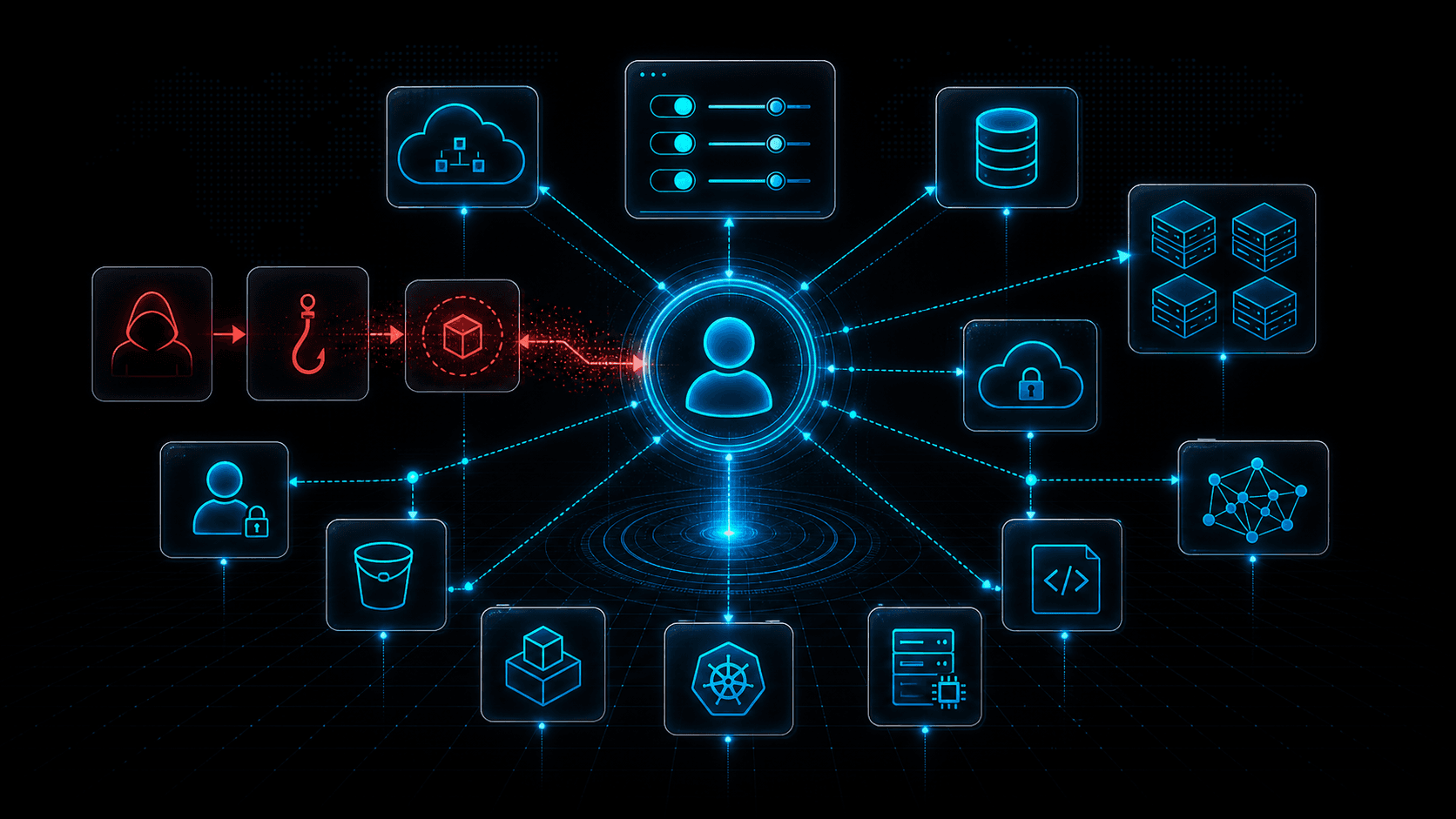
Short answer: The cloud kill chain often starts with identity, not a vulnerable server. Once attackers reach the control plane, they can create resources, change permissions, steal data, and persist through APIs. Defenders need to monitor cloud identities as closely as workloads.
Traditional infrastructure security imagined attackers moving from exposed hosts to internal networks. Cloud environments changed that pattern. A single credential can reach the management plane where resources are created, policies are assigned, logs are configured, and automation runs.
That management layer is the cloud control plane. It is powerful by design. Your engineers use it to deploy applications, scale infrastructure, configure storage, rotate secrets, and connect services. Attackers want it for the same reason. Control plane access can make exploitation of individual workloads unnecessary.
Google Cloud M-Trends and other incident reports repeatedly show how cloud intrusions hinge on identity, credentials, and configuration. Attackers do not always need zero-days. They need one exposed token with the right permissions.
The Control Plane as an Attack Surface
The cloud control plane includes:
- IAM users, roles, service accounts, and policies.
- API keys, access tokens, and refresh tokens.
- Cloud consoles and command-line tools.
- Infrastructure-as-code pipelines.
- Kubernetes management APIs.
- Logging, monitoring, and audit controls.
- Storage, compute, networking, and secret management APIs.
Every one of these surfaces can become part of an attack path. An attacker with read-only cloud access can inventory assets and identify targets. An attacker with permission to create keys can persist. An attacker who can modify policies can escalate. An attacker who can disable logging can hide.
The control plane collapses distance. A compromised developer laptop can become a cloud breach if it contains the wrong token.
Common Initial Access Paths
The most common paths are not exotic:
- Access keys committed to repositories.
- Service account tokens exposed in CI/CD.
- Infostealer malware harvesting cloud CLI credentials.
- Phished SSO sessions.
- OAuth consent phishing against cloud admin users.
- Metadata service abuse from vulnerable workloads.
- Overprivileged third-party integrations.
- Misconfigured federated identities.
These paths overlap with non-human identity security, session token theft, and LLMjacking. In each case, the credential is the bridge from a local compromise into a cloud-wide problem.
What Attackers Do After Control Plane Access
Once inside, attackers often enumerate first. They list users, roles, storage buckets, secrets, container registries, compute instances, regions, and network rules. Enumeration tells them what is valuable and what permissions they have.
Next, they look for persistence. They may create new access keys, add a federated identity provider, modify trust policies, create a new service account, or plant credentials in automation.
Then comes impact. Depending on motive, attackers may:
- Read sensitive storage.
- Launch compute for cryptomining or AI abuse.
- Exfiltrate databases or backups.
- Disable logging or change retention.
- Add firewall rules.
- Create snapshots.
- Modify serverless functions.
- Deploy backdoored containers.
- Access secrets and use them elsewhere.
Cloud attacks are often API-heavy. The good news is that APIs create logs. The challenge is making those logs actionable.
Detection Signals
Control plane detection starts with baselines. Which identities normally call which APIs, from which networks, in which regions, and at what times?
Useful alerts include:
- New access key creation for old or privileged identities.
- Policy changes that add broad permissions.
- Use of root or break-glass accounts.
- API calls from unfamiliar ASNs or countries.
- First-time use of sensitive services.
- Logging disabled, retention reduced, or trails modified.
- Secrets read by unusual principals.
- Compute launched in unused regions.
- Failed permission probes followed by success.
- Activity from proxy, VPN, Tor, or known abusive cloud hosts.
Do not review these events as isolated alerts. Attackers chain actions. A suspicious login followed by IAM enumeration, key creation, and storage listing is one story.
Response Playbook
When control plane compromise is suspected:
- Preserve logs immediately.
- Disable or rotate affected credentials.
- Identify all actions performed by the compromised identity.
- Review newly created keys, users, roles, policies, service accounts, and trust relationships.
- Check whether logging, monitoring, or alerting was changed.
- Inspect storage access, secret reads, compute launches, and network changes.
- Enrich source IPs and callback domains.
- Search for the same infrastructure across other accounts and tenants.
Containment must be careful. If you delete evidence or revoke the wrong production automation without planning, you can create outages. Have cloud-specific incident runbooks ready before the incident.
Prevention Priorities
Use identity federation and short-lived credentials instead of long-lived keys. Scope roles narrowly. Separate duties across environments. Require approval for sensitive policy changes. Monitor all administrative APIs. Protect CI/CD systems as privileged cloud actors.
Apply service control policies or equivalent guardrails to prevent dangerous actions even if an identity is compromised. Examples include blocking unused regions, preventing logging deletion, disallowing public storage, and restricting key creation.
For human access, require phishing-resistant MFA for administrators. For machine access, prefer workload identity and rotate static secrets aggressively.
Building Cloud Attack Path Maps
Control plane risk is easier to explain when teams can see attack paths. A useful map starts with identities, then connects them to permissions, resources, trust relationships, and network exposure. The map should answer: If this token is stolen, what can it read, change, create, or delete?
Do not map only administrators. Many real incidents start with moderate permissions that chain into impact. A role that can read secrets may expose a database password. A CI token that can update a deployment may plant a backdoor. A service account that can assume another role may become privileged through trust relationships. Attack paths are often combinations, not single dangerous permissions.
Add external context to the map. Internet-exposed workloads, public repositories, third-party CI systems, remote contractors, and SaaS integrations are common places where credentials leak or are abused. If one of those entry points connects to a broad cloud role, prioritize it.
Review the map after every major infrastructure change. Cloud permissions drift quickly. A temporary debugging permission can become permanent. A new automation role can accidentally inherit broad access. A merger or new SaaS integration can introduce trust relationships nobody reviews.
Logging Requirements
Cloud control plane defense depends on audit logs. Logs should be enabled before an incident, protected from modification, centralized, and retained long enough for investigation. Attackers often try to disable or shorten logging after access. That action itself should be high severity.
Collect identity, API, network, storage, secret manager, Kubernetes, and CI/CD logs. Normalize fields such as principal, source IP, user agent, API name, resource, region, result, and request ID. Without normalization, cross-account investigations become slow.
Store logs in a separate security account or project with restricted write-once controls where possible. The identity that manages production should not be able to erase its own audit trail.
Executive Briefing
For executives, cloud control plane attacks can be framed as "management-plane compromise." The attacker is not breaking into one server; they are using the same APIs your team uses to run the business. That is why a single credential can create broad impact.
Useful business metrics include number of long-lived cloud keys, percentage of privileged roles with recent review, number of unused regions blocked, time to disable a compromised identity, and percentage of sensitive API calls covered by alerts.
The board-level message is simple: cloud resilience depends on identity resilience. Patch management still matters, but compromised credentials can bypass patched workloads entirely.
Tabletop Exercise
Practice a scenario where a CI token is stolen by a malicious dependency. The attacker uses it to assume a deployment role, read secrets, create a new access key, launch compute in an unused region, and disable a log sink.
The exercise should test who can revoke the token, how quickly logs are preserved, whether guardrails block unused regions, whether secret reads are visible, and whether source IP reputation is available inside the investigation workflow. The goal is to discover gaps before the same chain happens under pressure.
90-Day Control Plane Roadmap
In the first 30 days, identify standing privileged access, long-lived keys, inactive identities, unused regions, and logging gaps. Remove what is clearly unnecessary. Turn on alerts for new key creation, logging changes, and administrative API calls from unfamiliar networks.
By day 60, introduce stronger guardrails. Block unused regions, protect log sinks, require approvals for broad IAM changes, and separate production from development identities. Review CI/CD roles as privileged cloud identities, not as ordinary automation.
By day 90, build continuous attack path review. Map which identities can reach secrets, production data, deployment systems, and administrative roles. Prioritize paths that begin from exposed workloads, developer machines, third-party integrations, or build systems because those are common entry points.
Human Factors
Cloud teams often resist controls that slow deployment. Security teams should focus on paved roads: templates, approved roles, reusable policies, and automated checks that make the safe path the fastest path. The goal is not to make engineers file tickets for every change. The goal is to prevent one stolen token from becoming full environment control.
Detection Content to Build
Build detections around dangerous sequences, not only single events. A login from an unfamiliar ASN followed by IAM enumeration, policy changes, key creation, secret reads, and compute launches is a control plane intrusion story. Each event alone might look explainable; together they are urgent.
Prioritize events that weaken visibility. Disabling logging, changing retention, deleting trails, or modifying alert destinations should page responders immediately. Attackers who change logging know they are in the management layer.
Also monitor denied API calls. Permission probing helps attackers understand what a stolen identity can do. A burst of denied calls followed by successful sensitive actions is often more revealing than the success alone.
Include cost and quota events in the same detection library. Unexpected compute launches, storage growth, and high-cost service use can be signs of abuse even when IAM activity appears valid. Control plane attackers often use legitimate APIs for illegitimate work, so operational anomalies are security telemetry.
Finally, review access broker logs if engineers use SSO portals, bastions, or privileged access systems. Those tools often show the first point where a human or automation identity crossed into sensitive cloud control.
Those broker events make timelines clearer when multiple cloud accounts are touched quickly.
They also expose unusual access brokers.
Threat Intelligence Takeaway
Cloud control plane attacks are identity attacks with infrastructure consequences. The suspicious signal may be an API call from an unfamiliar IP, a new key, or a policy change that looks administrative until viewed in context.
isMalicious helps enrich source IPs, domains, and infrastructure seen in cloud audit logs. When an identity begins controlling your cloud from suspicious infrastructure, reputation context can shorten the path from alert to containment.
Frequently asked questions
- What is the cloud control plane?
- The cloud control plane is the management layer used to create, configure, monitor, and delete cloud resources through APIs, consoles, identities, policies, and automation.
- Why do attackers target the control plane?
- Control plane access lets attackers enumerate assets, create credentials, change policies, launch compute, read storage, disable logging, and persist without exploiting individual servers.
- What are common control plane attack paths?
- Common paths include stolen API keys, compromised SSO sessions, overprivileged service accounts, CI/CD token abuse, metadata service theft, and malicious OAuth grants.
- How do you detect cloud control plane compromise?
- Monitor identity behavior, unusual API calls, new keys, policy changes, logging changes, activity from unfamiliar infrastructure, region anomalies, and use of rarely used services.
Related articles
 May 8, 2026LLMjacking Explained: How Attackers Abuse Cloud Credentials to Steal AI Compute
May 8, 2026LLMjacking Explained: How Attackers Abuse Cloud Credentials to Steal AI ComputeLLMjacking combines cloud credential theft with expensive AI workloads. Learn how attackers find exposed keys, abuse model APIs, hide compute costs, and how defenders can detect the pattern.
 May 2, 2026Compromised Domains in Phishing: When Trusted Sites Become Attack Infrastructure
May 2, 2026Compromised Domains in Phishing: When Trusted Sites Become Attack InfrastructureAttackers increasingly host phishing pages, redirects, and malware on compromised legitimate domains. Learn why reputation bypass works and how to detect hidden malicious paths.
 Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker