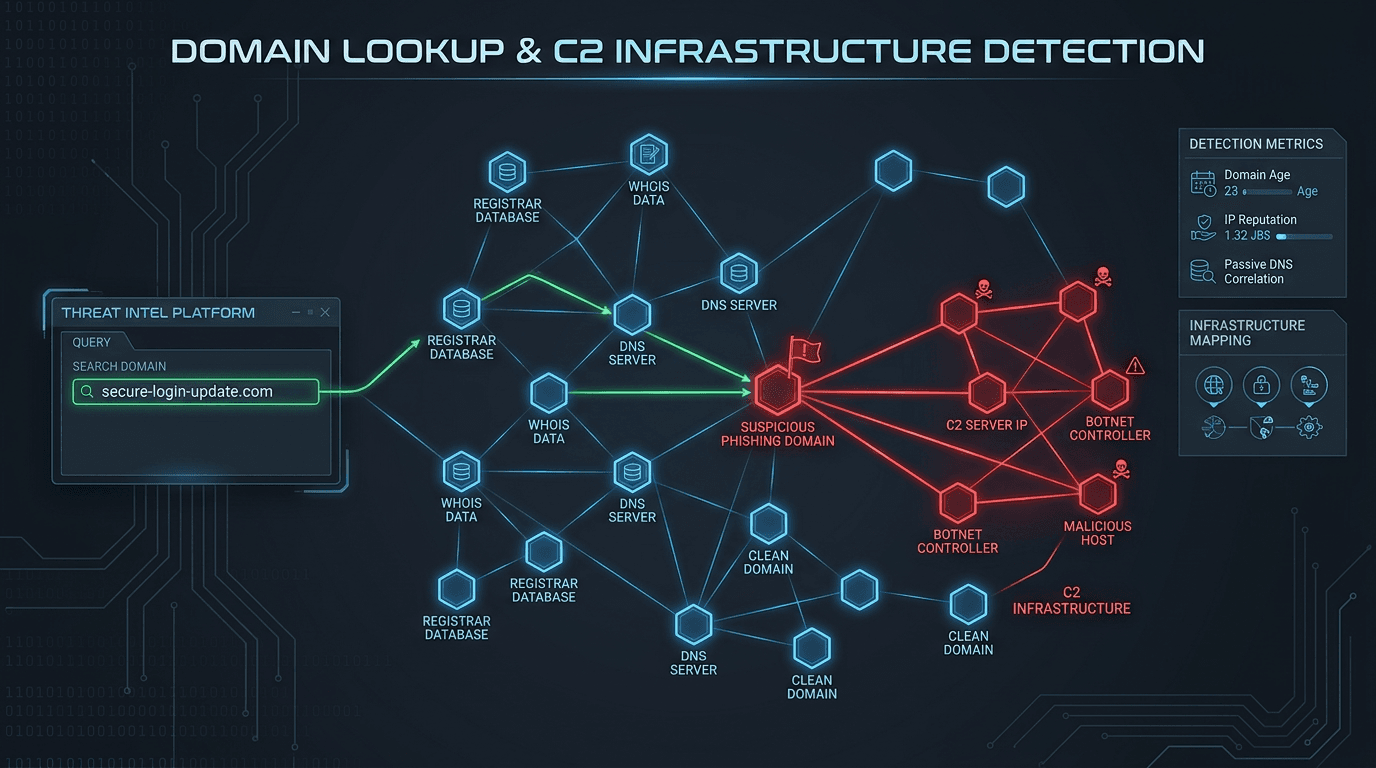
Domain Lookup for Phishing and C2 Infrastructure Detection
Phishing campaigns and malware operations depend on domain infrastructure that leaves detectable traces. Learn how advanced domain lookup techniques help security teams uncover phishing sites and command-and-control servers before they compromise your organization.
Every successful phishing attack and every piece of malware that communicates with its operators shares a common dependency: domain names. Phishing sites need domains that look convincing to victims. Malware needs domains — or in some cases IP addresses — to receive commands and exfiltrate data. This dependency is both the attacker's necessity and the defender's opportunity.
Domain lookup for phishing and command-and-control (C2) infrastructure detection is a threat hunting and prevention discipline focused on identifying malicious domains before they can be used against your organization. By understanding how attackers build and operate domain infrastructure, security teams can detect threats at the infrastructure layer rather than waiting for behavioral indicators that only appear after compromise.
How Attackers Build Phishing Domain Infrastructure
Understanding the attacker's playbook is prerequisite to detecting their infrastructure. Modern phishing operations are sophisticated supply chains with specialized components.
Domain Registration at Scale
Sophisticated phishing groups operate at industrial scale. They register dozens or hundreds of domains per campaign, using automated scripts and a rotating roster of registrar accounts to evade registration-level controls. Each domain serves a short window — often hours to days — before being abandoned and replaced. This burn-and-rotate strategy is designed specifically to outlast manual blocklisting processes.
Defenders who rely solely on reactive blocklists are perpetually behind. The attacker has already moved to the next domain by the time the previous one is blocked.
The Life Cycle of a Phishing Domain
A typical phishing domain passes through predictable stages:
- Registration: The domain is registered, often with privacy protection, at a registrar with lax abuse policies.
- Infrastructure setup: DNS records are configured, hosting is provisioned on a bulletproof or compromised server, and SSL certificates are obtained from automated issuers.
- Content deployment: Phishing kit content — cloned login pages, fake invoice portals, spoofed brand pages — is deployed.
- Campaign launch: The domain is embedded in phishing emails, SMS messages, or social media posts and sent to targets.
- Burn and replace: After the domain is reported and blocked, the operation shifts to the next prepared domain.
Each of these stages leaves observable signals that domain lookup intelligence can detect.
Command-and-Control Domain Infrastructure
Malware C2 infrastructure operates differently from phishing sites but shares common detection opportunities.
Domain Generation Algorithms (DGAs)
Sophisticated malware families use Domain Generation Algorithms to generate hundreds or thousands of potential C2 domains algorithmically. Only the attacker knows which of these domains will actually be registered and operational on any given day. This makes it impossible to preemptively blocklist all possible C2 destinations while ensuring the malware can always find a working contact point.
Security researchers have reverse-engineered DGAs for many malware families and can predict the domains a given malware variant will attempt to contact. This intelligence allows proactive DNS blocking of DGA domains before malware actually reaches an organization.
Fast Flux DNS
Fast flux is a technique where a domain's DNS records rotate through dozens or hundreds of IP addresses with very short TTLs (time-to-live values). This makes it difficult to block C2 infrastructure by IP address, since the resolving IP changes every few minutes. Domain lookup tools that track DNS resolution history and flag domains exhibiting fast flux behavior provide detection capability that pure IP blocking cannot achieve.
Passive DNS Analysis
Passive DNS captures the historical record of which IP addresses resolved to which domains over time. This data reveals:
- When a C2 domain first appeared in DNS resolution
- Which IPs it has resolved to historically (revealing infrastructure clusters)
- How many domains share the same IP addresses (indicating shared hosting infrastructure)
- Resolution patterns that match known malware communication behaviors
Detecting Phishing Infrastructure with Domain Lookup
Registration Pattern Analysis
Phishing domains exhibit characteristic registration patterns that distinguish them from legitimate domains even before they appear on any blocklist:
Age: The majority of phishing domains are registered within 30 days of being used. A domain registered yesterday hosting a banking login page is an almost certain indicator of phishing.
Registrar concentration: Certain registrars appear disproportionately in phishing domain datasets due to permissive abuse policies, low prices, and easy anonymous registration. A domain registered at such a registrar immediately warrants elevated scrutiny.
Privacy registration combined with brand similarity: Legitimate financial institutions, healthcare providers, and e-commerce platforms do not hide their contact details behind WHOIS privacy services. A domain visually similar to a trusted brand that uses privacy registration is a phishing red flag.
Certificate Transparency Monitoring
Certificate Transparency (CT) logs are public records of every SSL certificate issued by participating Certificate Authorities. Attackers must obtain certificates to run convincing phishing sites over HTTPS. By monitoring CT logs for certificates issued to domains matching patterns associated with targeted brands — using regular expressions or fuzzy matching — security teams can identify phishing infrastructure within minutes of it becoming operational, often before any phishing email is sent.
Passive DNS Clustering
Individual phishing or C2 domains often share infrastructure with dozens of other malicious domains. If you identify one malicious domain and query its historical IP associations through passive DNS, you can surface the entire cluster. A single confirmed phishing site might lead to twenty other phishing domains hosted on the same IP, all of which can be added to blocklists preemptively.
Building a Domain-Based Threat Hunting Practice
Effective domain lookup for phishing and C2 detection requires moving beyond reactive lookups to proactive hunting.
Monitor Your Brand Surface
Define the set of terms that constitute your brand: your primary domain, product names, executive names, and common variations. Configure monitoring against Certificate Transparency feeds and new domain registration data to alert when any domain containing these terms is registered or receives an SSL certificate. Many phishing campaigns target specific organizations — catching the phishing domain before the campaign launches gives defenders a decisive advantage.
Investigate Every Suspicious Domain in Logs
DNS query logs are a goldmine for C2 detection. Every domain queried by systems in your environment should be inspectable. Anomalous DNS traffic — queries to newly registered domains, domains with DGA-like random character strings, domains with fast flux resolution patterns, or domains absent from legitimate business registries — warrants investigation.
Enrich Alerts with Domain Intelligence
When a security alert fires — antivirus detection, SIEM correlation rule, EDR behavioral flag — domain lookup should be an automatic enrichment step. Extract every domain from the alert context and query reputation data immediately. A process making outbound connections to a domain registered three days ago, resolving to a known bulletproof hosting IP, and present on C2 blocklists is almost certainly compromised. Reputation data turns a behavioral anomaly into a confident incident.
Use Threat Intelligence Platforms for Correlation
Platforms like IsMalicious correlate domain reputation data across multiple source categories simultaneously, providing a single risk score that reflects the full picture. Rather than manually querying half a dozen separate blocklists, a single API call returns presence across all of them plus registration data, IP reputation, and historical abuse context. This consolidation is what makes real-time domain lookup practical in high-volume environments.
Integrating Domain Lookup into Security Tooling
DNS Firewall (RPZ) Integration
DNS Response Policy Zones allow organizations to intercept DNS queries for malicious domains and return a blocked response before the connection is established. IsMalicious data can feed directly into RPZ policies, blocking C2 domains and phishing sites at the DNS layer — before any TCP connection is established, before any content is loaded, and before any user can be deceived.
SIEM Enrichment Pipeline
Configure your SIEM ingestion pipeline to automatically enrich log entries containing domain names with reputation data from IsMalicious. Security analysts reviewing alert queues then see domain risk context alongside every event, without needing to perform manual lookups.
Email Security Gateway
Configure your email gateway to extract all domains from inbound message bodies and headers and submit them for reputation checks. Phishing links frequently hide behind URL shorteners or redirect chains — configure checks at the final resolved destination, not just the initial URL.
The Intelligence Edge
Phishing and C2 infrastructure detection through domain lookup is not a replacement for endpoint security, behavioral monitoring, or user training. It is an intelligence layer that makes every other security control more effective.
When your endpoint detection tool fires an alert, domain reputation data tells you immediately whether the domain involved is a known threat actor infrastructure. When your email gateway flags a suspicious message, domain lookup confirms whether the embedded links are active phishing sites. When your threat hunting team investigates anomalous DNS traffic, domain intelligence separates noise from confirmed threats in seconds.
Use IsMalicious to check any domain against our comprehensive threat intelligence database and see whether it is linked to phishing campaigns, C2 operations, or other malicious activity.
Frequently asked questions
- What is a command-and-control (C2) domain and why is it dangerous?
- A command-and-control domain is a domain used by malware authors to send instructions to infected machines and receive stolen data. When malware infects a system, it periodically contacts the C2 domain to receive commands — such as installing additional payloads, exfiltrating files, or joining a DDoS attack. Blocking C2 domains at the DNS or firewall level effectively neutralizes installed malware by cutting off its communication channel.
- How do domain lookup tools detect phishing sites?
- Domain lookup tools compare queried domains against threat intelligence feeds from anti-phishing organizations (PhishTank, OpenPhish, APWG), analyze registration patterns for characteristics common to phishing infrastructure (new registration, privacy registration, brand impersonation), check hosting reputation, and examine certificate issuance history. A domain scoring high on multiple phishing-specific indicators can be blocked proactively even before it appears on any specific blocklist.
- Can I use domain lookup to investigate suspicious emails?
- Yes. Extract every domain from links in a suspicious email and run each through a domain reputation tool. Check the sender's domain as well — attackers frequently use look-alike domains in the From header. Review the risk score, registration date, blocklist presence, and associated IP reputation. A sender domain registered two days ago with privacy protection, resolving to a bulletproof hosting IP, and absent from any legitimate business registry is almost certainly phishing infrastructure.
Related articles
 Apr 8, 2026Domain Lookup: How to Identify Malicious Websites Before They Strike
Apr 8, 2026Domain Lookup: How to Identify Malicious Websites Before They StrikeMalicious websites are the launchpad for phishing, malware distribution, and credential theft. Learn how domain lookup tools use reputation data, WHOIS analysis, and threat feeds to identify dangerous domains before your users click.
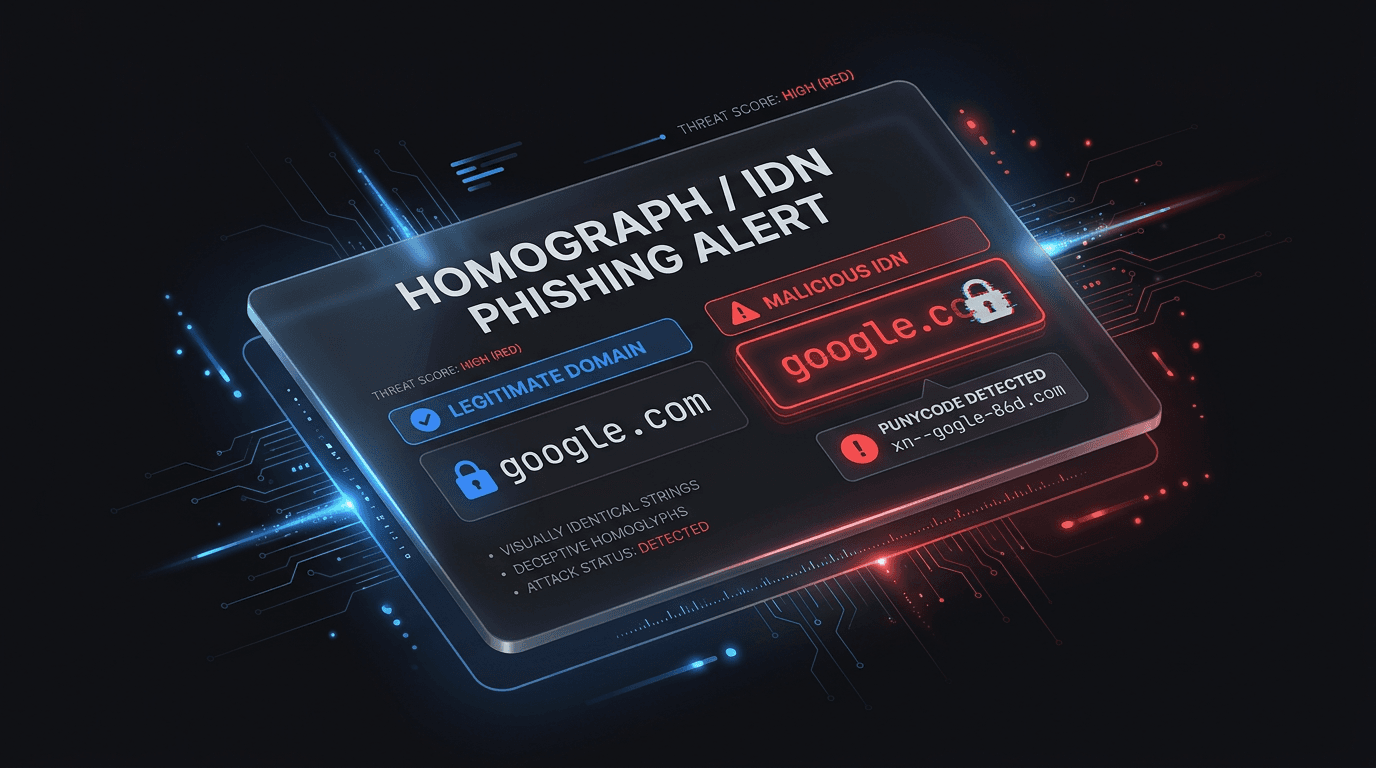 Apr 1, 2026IDN and Homograph Phishing: When the Domain Looks Right But Is Wrong
Apr 1, 2026IDN and Homograph Phishing: When the Domain Looks Right But Is WrongInternationalized domain names and look-alike characters let attackers spoof trusted brands in the address bar. Learn how homograph attacks work and how to defend users and SOC teams.
 Dec 4, 2025Why Checking Malicious Domain and IP Reputation is Critical for Threat Prevention
Dec 4, 2025Why Checking Malicious Domain and IP Reputation is Critical for Threat PreventionLearn why monitoring domain and IP reputation is essential for cybersecurity. Discover how to detect malicious threats, prevent phishing attacks, and leverage threat intelligence to protect your infrastructure.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker