Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
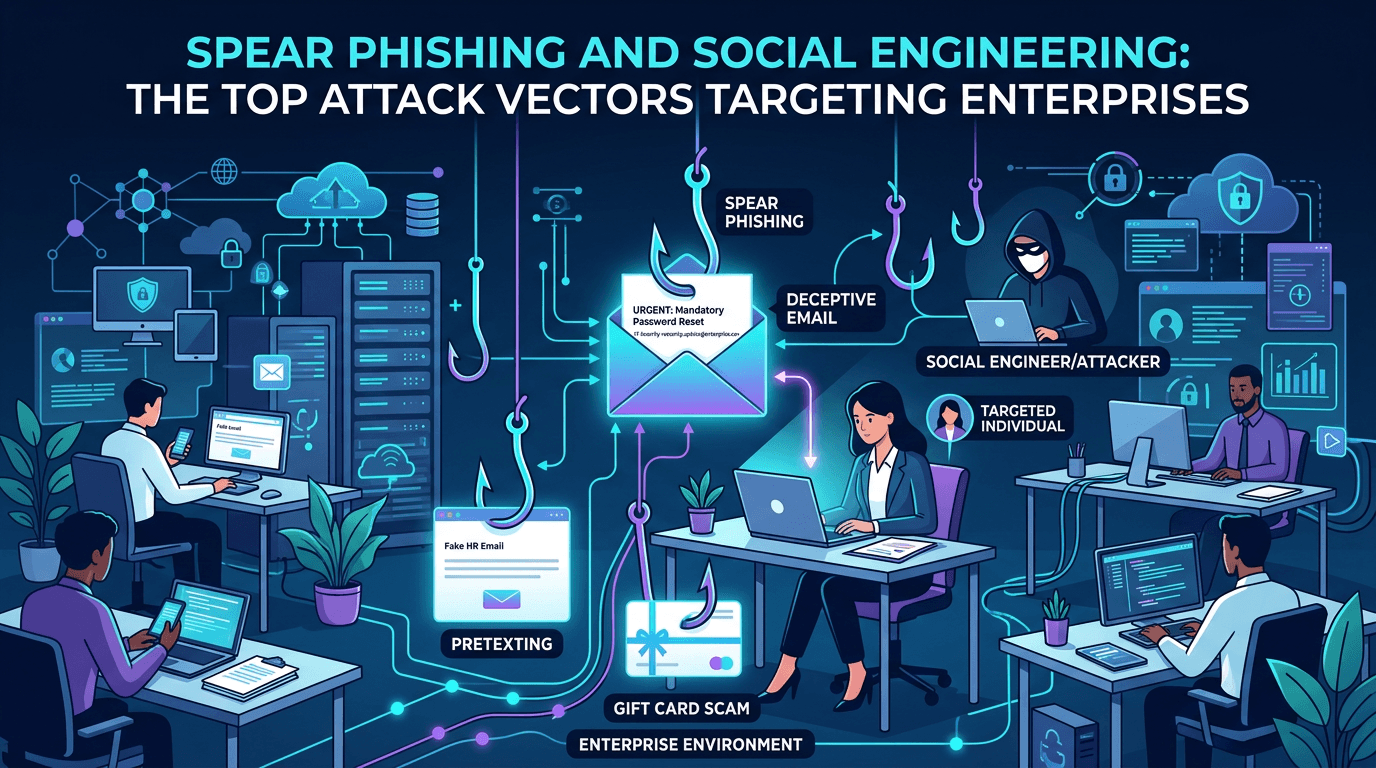
Email security has been “solved” roughly once every five years since the 1990s. Each solution holds for a while, and then threat actors evolve. In 2026, the most damaging enterprise compromises rarely start with a zero-day exploit—they start with a spear phishing message, a convincing phone call, or a cloned login page that harvests credentials. The human layer remains the path of least resistance, and modern social engineering is more sophisticated, better-researched, and better-tooled than ever. This guide explores the full spectrum of phishing-adjacent attack vectors targeting enterprises, the techniques actors use to craft them, and the defensive stack that actually reduces risk.
What Makes Spear Phishing Different
Broad phishing casts a wide net: millions of generic lures emailed to anyone. Spear phishing targets specific individuals or small groups, using research to craft a pretext that feels authentic. Attackers know the target’s name, role, recent projects, internal jargon, and often their reporting chain. A well-crafted spear phishing email from an apparent CFO to a senior accounts payable analyst at the right moment in the quarter is orders of magnitude more effective than generic phishing.
The research inputs that power spear phishing are, in most cases, OSINT: LinkedIn profiles, corporate websites, press releases, leaked data, and social media. Attackers invest hours per target because the payoff—credential compromise, invoice fraud, malware deployment—justifies the effort. Some campaigns use AI-generated copy to scale this research further, automatically tailoring lures to each recipient.
For defenders, the implication is stark: awareness training alone cannot close the gap. Some well-written spear phishing messages are indistinguishable from legitimate internal correspondence. The defensive stack must handle attacks that will occasionally succeed at fooling humans.
The Modern Attack Vector Spectrum
1. Email Spear Phishing
Email remains the dominant spear phishing channel. Techniques include:
- CEO fraud / executive impersonation: Forged or look-alike sender domains instruct urgent action.
- Vendor impersonation: Faked invoices, changes to banking details, urgent payments.
- Credential harvesting: Links to cloned login pages mimicking Microsoft 365, Google, Okta, VPN portals.
- Attachment-based malware: PDFs with malicious URLs, macro-laden documents, container-based payloads (ISO, IMG, LNK).
- Reply-chain hijacking: Attackers compromise one mailbox and inject malicious messages into existing legitimate threads, defeating pattern detection.
Defensive responses include robust email authentication (SPF, DKIM, DMARC), advanced threat protection with link rewriting, sandboxing for attachments, and domain reputation lookups on every URL clicked. Infrastructure reputation services like isMalicious add critical signal when link-time analysis needs to decide quickly.
2. Business Email Compromise (BEC)
Business Email Compromise is spear phishing with financial fraud as the payoff. Typical patterns:
- Compromise of a vendor or partner mailbox.
- Monitoring of legitimate invoicing communication.
- Injection of fraudulent banking details at the right moment.
- Redirection of payments to attacker-controlled accounts.
BEC requires sustained access and careful reconnaissance. Defense depends on verification procedures (out-of-band confirmation of any banking changes), mailbox anomaly detection, and supplier-communication controls. Pure technical email security is insufficient; process controls matter.
3. Smishing (SMS Phishing)
Mobile phishing has accelerated as enterprises move to cloud-based authentication workflows. Attackers send SMS messages impersonating corporate IT, package carriers, or banks, directing victims to credential-harvesting pages. Because mobile browsers often truncate URLs and device keyboards make inspection inconvenient, users fall for smishing at disproportionate rates.
Defensive countermeasures include mobile device management (MDM) with safe-browsing enforcement, employee awareness specific to SMS lures, and reputation checks on any URL opened from SMS.
4. Vishing (Voice Phishing)
Voice-based social engineering is resurgent, amplified by realistic voice-cloning AI. Attackers impersonate executives, IT support staff, or vendors in live calls, pressuring victims to reset passwords, approve MFA prompts, or install remote access tools. “IT support” vishing is especially effective against employees newly onboarded or unfamiliar with corporate support processes.
Defensive responses include formal helpdesk verification procedures (callbacks to known numbers, unique identifiers required before sensitive actions), employee training on common vishing scripts, and MFA designs that resist prompt-bombing.
5. Quishing (QR Code Phishing)
Quishing delivers phishing URLs via QR codes, often in emails that appear to come from HR, IT, or security (“scan this code to complete MFA registration”). QR codes bypass many link-rewriting defenses because the URL lives inside the image. Once a user scans with a personal phone, the click happens outside corporate security telemetry.
Defense requires: flagging QR codes in emails at delivery time, policies that no legitimate workflow will ever begin with an unsolicited QR code, and training to that effect.
6. MFA Fatigue / Prompt Bombing
Attackers with stolen credentials for accounts protected by push-based MFA repeatedly trigger authentication prompts, hoping the victim eventually approves one to make the noise stop. This vector has bypassed MFA at multiple high-profile organizations.
Mitigations include number-matching MFA, phishing-resistant authenticators (FIDO2, passkeys), conditional access policies that factor in risk signals, and user training on never approving unexpected prompts.
7. OAuth Consent Phishing
Rather than stealing a password, attackers trick users into consenting to malicious OAuth applications that then access mail, files, or identity data legitimately. The attacker never needs a credential; the user granted consent.
Defense requires tight application governance: block unverified OAuth apps by default, audit consent grants regularly, and train users to treat consent prompts with the same seriousness as login prompts.
8. Collaboration Platform Phishing
As enterprise work shifts to platforms like Microsoft Teams, Slack, and Zoom, attackers follow. Techniques include:
- External Teams messages from impersonated vendors.
- Malicious Slack app invitations.
- Shared document links in collaboration tools leading to credential harvesters.
Defensive coverage for these channels often lags email. Explicit policies (no external messaging unless allowlisted, governance for third-party apps) and monitoring of unusual collaboration activity are essential.
9. Calendar and Meeting Invite Phishing
Calendar invites can contain malicious links or attachments. Because calendar entries are often auto-accepted by default and do not trigger the same scrutiny as email, attackers use them to insert lures into victims’ agendas.
Review auto-accept settings, require explicit acceptance for external invites, and apply the same link and attachment scanning policies to calendar content that apply to email.
10. Watering Hole and Supply Chain Adjuncts
Beyond direct outreach, attackers sometimes compromise websites or tools the target organization uses routinely and inject malicious content. This blends into the broader category of supply chain attack, but often starts with spear phishing against a third-party vendor’s staff.
Anatomy of a Modern Spear Phishing Campaign
A typical campaign runs through discrete phases:
- Target selection: Actors choose organizations or individuals based on revenue, sector, access they hold, or vulnerability.
- Reconnaissance: OSINT-heavy phase collecting names, roles, relationships, ongoing projects, technology stack.
- Infrastructure preparation: Domain registration, certificate issuance, hosting setup. Infrastructure often leverages newly registered domains or domains with plausible look-alike names.
- Pretext crafting: Message, pretext, and lure tailored to the target, increasingly with AI assistance.
- Delivery: Via email, SMS, voice, collaboration tool, or calendar invite.
- Credential or access harvest: Landing pages capture credentials, MFA codes, or session cookies; alternatively, malicious payloads establish footholds.
- Exploitation: Lateral movement, privilege escalation, objective completion (data theft, fraud, ransomware deployment).
Defensive opportunity exists at every stage. Early infrastructure detection often provides the longest warning window: newly registered lookalike domains and phishing-kit-hosted URLs can be flagged days before messages arrive. Services like isMalicious publish reputation and risk signals that let defenders monitor exactly this kind of pre-campaign activity.
The Defensive Stack for Phishing-Class Attacks
No single control stops modern spear phishing. A layered stack is required:
Email Authentication and Content Filtering
- SPF, DKIM, DMARC with enforcement policies that reject or quarantine failed messages.
- BIMI for brand visibility.
- Advanced threat protection with link rewriting, sandboxing, and attachment detonation.
- Impersonation detection for executive names and close-match domains.
Identity and Authentication Hardening
- Phishing-resistant MFA (FIDO2 tokens, passkeys) wherever possible.
- Conditional access factoring in device posture, geolocation, and risk scores.
- Session management: Short token lifetimes, aggressive revocation on risk signals.
- Privileged access separation: Separate accounts with separate devices for admin roles.
Infrastructure Reputation and Intelligence
- Real-time reputation on URLs at click time, on domains at delivery time, on IPs at SMTP handshake.
- Passive monitoring of newly registered lookalike domains targeting your brand.
- Threat intelligence feeds covering phishing kits and actor infrastructure.
User Training and Process Controls
- Targeted, role-specific phishing simulation, not once-a-year generic quizzes.
- Clear reporting mechanisms (one-click “report phishing” buttons with fast response).
- Verification procedures for high-risk actions (banking changes, credential resets, remote access installs).
- Explicit policies for QR codes, OAuth consent, and external collaboration messages.
Detection and Response
- SIEM correlation of email, identity, endpoint, and network telemetry.
- SOAR playbooks for reported phishing that pull mailboxes, reset sessions, and enumerate recipients.
- Threat hunting for subtle post-compromise indicators: unusual inbox rules, token replay from new IPs, anomalous OAuth grants.
The Role of Threat Intelligence
Operational threat intelligence shapes phishing defense in several ways:
- Campaign awareness: Knowing which actors currently target your sector lets you tune detection and training.
- Infrastructure signatures: Phishing kits and actor tooling leave fingerprints that detection engineering can encode.
- Pre-campaign warning: Lookalike domain registration monitoring catches preparation.
- Incident attribution: Linking a compromise to a known actor speeds containment and forecasts next moves.
Pairing intelligence with infrastructure reputation providers such as isMalicious gives SOCs real-time reputation checks and historical context for every domain, IP, or URL that appears in a suspicious message.
Common Enterprise Phishing Defense Mistakes
Repeated failure modes:
- Over-investing in training, under-investing in controls: Training helps, but controls catch what training misses.
- Uniform MFA across all accounts: Privileged roles need phishing-resistant MFA even if it is inconvenient.
- Ignoring newer channels: SMS, QR codes, and collaboration tools are often underprotected.
- Slow phishing triage: A reported message that sits in a queue for hours lets the same lure spread.
- Missing OAuth governance: Consent phishing bypasses every password-focused defense.
- Weak supplier verification: BEC through vendor compromise bypasses your internal controls.
Measuring Phishing Defense Outcomes
Useful metrics:
- Time from phishing report to mass-takedown of the campaign in your environment.
- Click-through rate on simulations by role and cohort.
- Detection coverage against common phishing kits and TTPs.
- Percentage of privileged accounts using phishing-resistant MFA.
- Phishing-originated incidents per quarter; track the trend against control investments.
Conclusion
Spear phishing and social engineering remain the most productive initial attack vectors for modern threat actors because they exploit the one system that does not get patched: human judgment. Defending against them requires a layered stack spanning email authentication, identity hardening, infrastructure reputation, user awareness, detection engineering, and fast response. Each layer compensates for weaknesses in the others.
Integrate continuous reputation data from providers like isMalicious into every link-evaluation decision, pair it with phishing-resistant MFA and behavioral detection, and measure outcomes relentlessly. The organizations that treat phishing defense as a multi-layer engineering problem—not a training problem—consistently avoid the compromises that destroy the ones who do not.
Frequently asked questions
- What is spear phishing and how is it different from regular phishing?
- Spear phishing is targeted phishing aimed at specific individuals or organizations, using tailored pretexts, insider knowledge, and carefully crafted lures. Regular phishing is broad and opportunistic; spear phishing is researched, personalized, and far more likely to succeed against a specific victim.
- What attack vectors do spear phishing campaigns use beyond email?
- Modern spear phishing spans email, SMS (smishing), voice calls (vishing), collaboration platforms like Teams and Slack, social media direct messages, QR codes (quishing), calendar invites, and OAuth consent phishing. Attackers choose the channel with the weakest defensive controls for the target.
- How do infrastructure reputation services help defend against spear phishing?
- Reputation services score IPs, domains, and URLs based on malicious history. Spear phishing campaigns often reuse infrastructure, register newly observed domains, or route through known malicious proxies. Real-time reputation lookups at email delivery, link click, and network egress catch many attacks even when the message itself looks legitimate.
Related articles
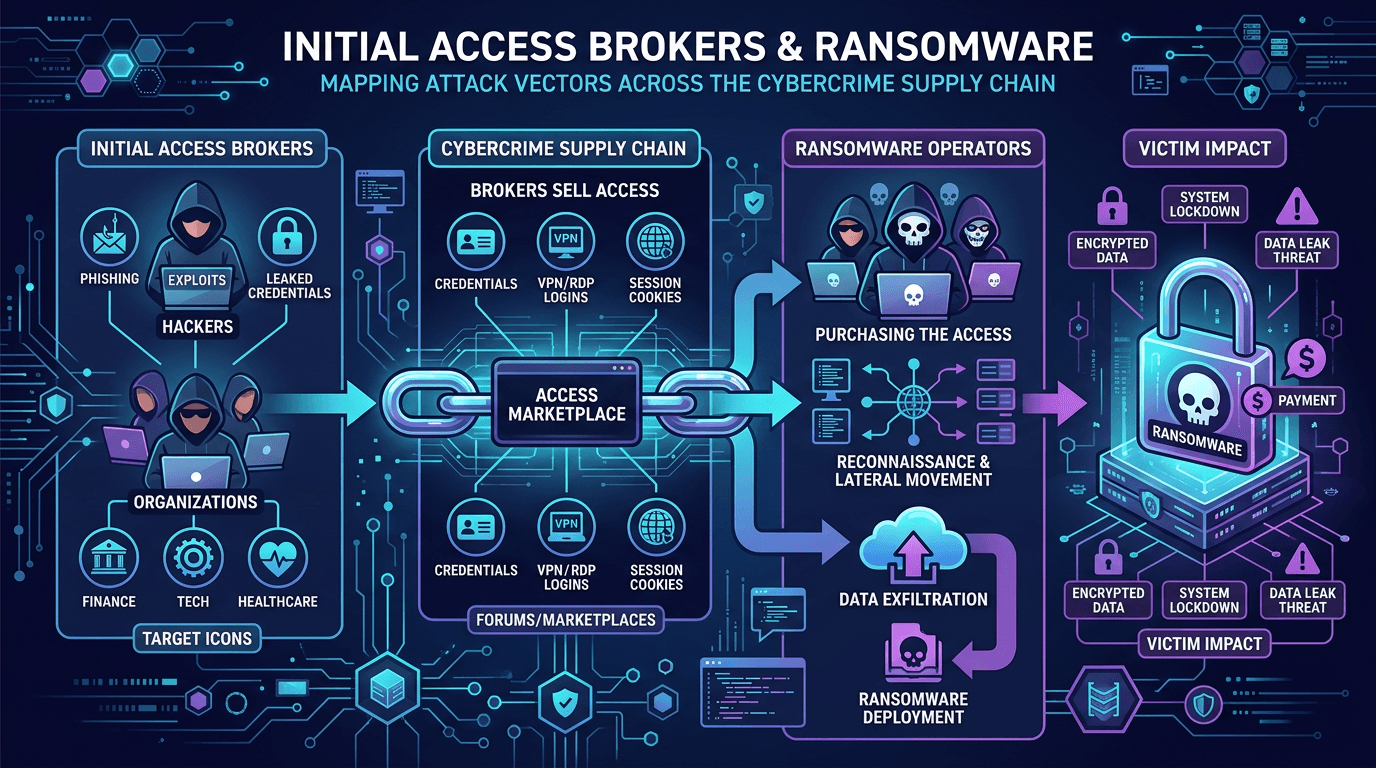 Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply ChainUnderstand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
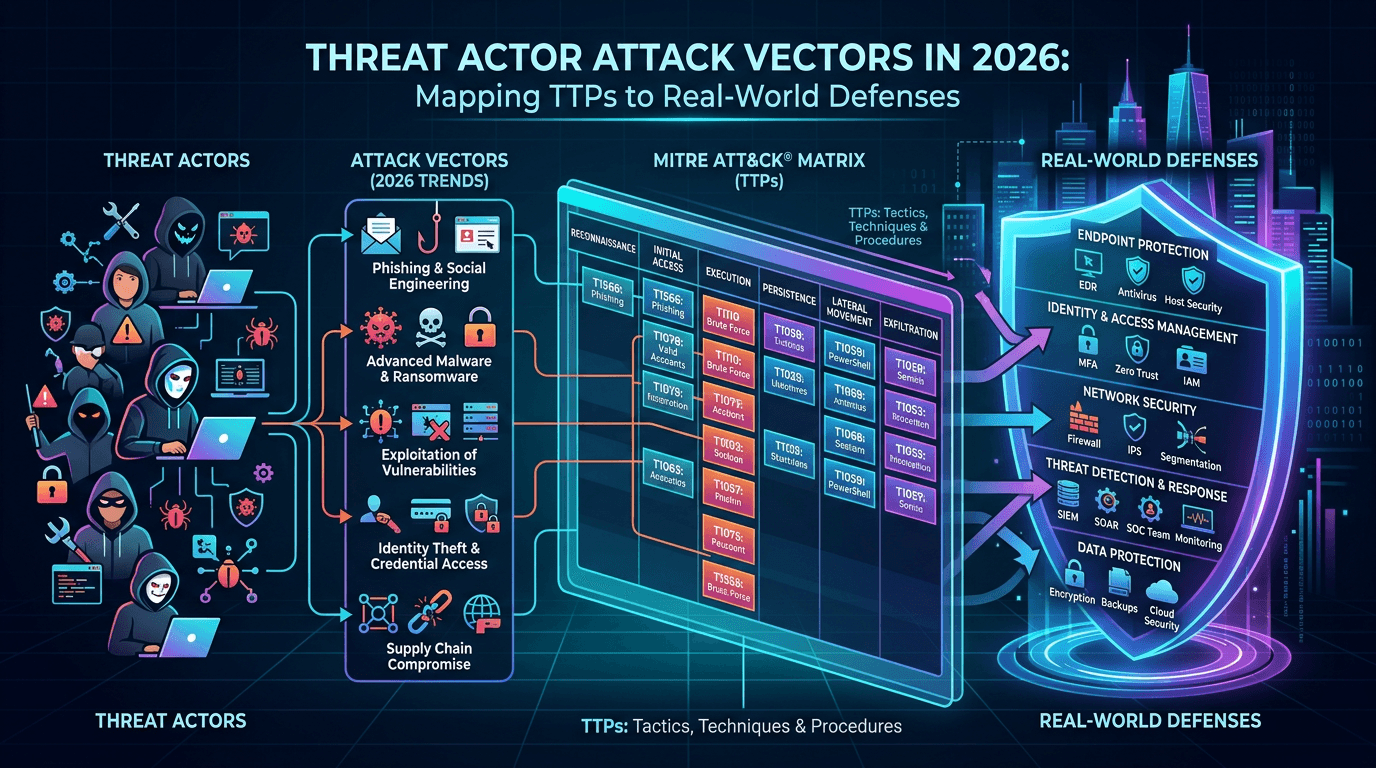 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
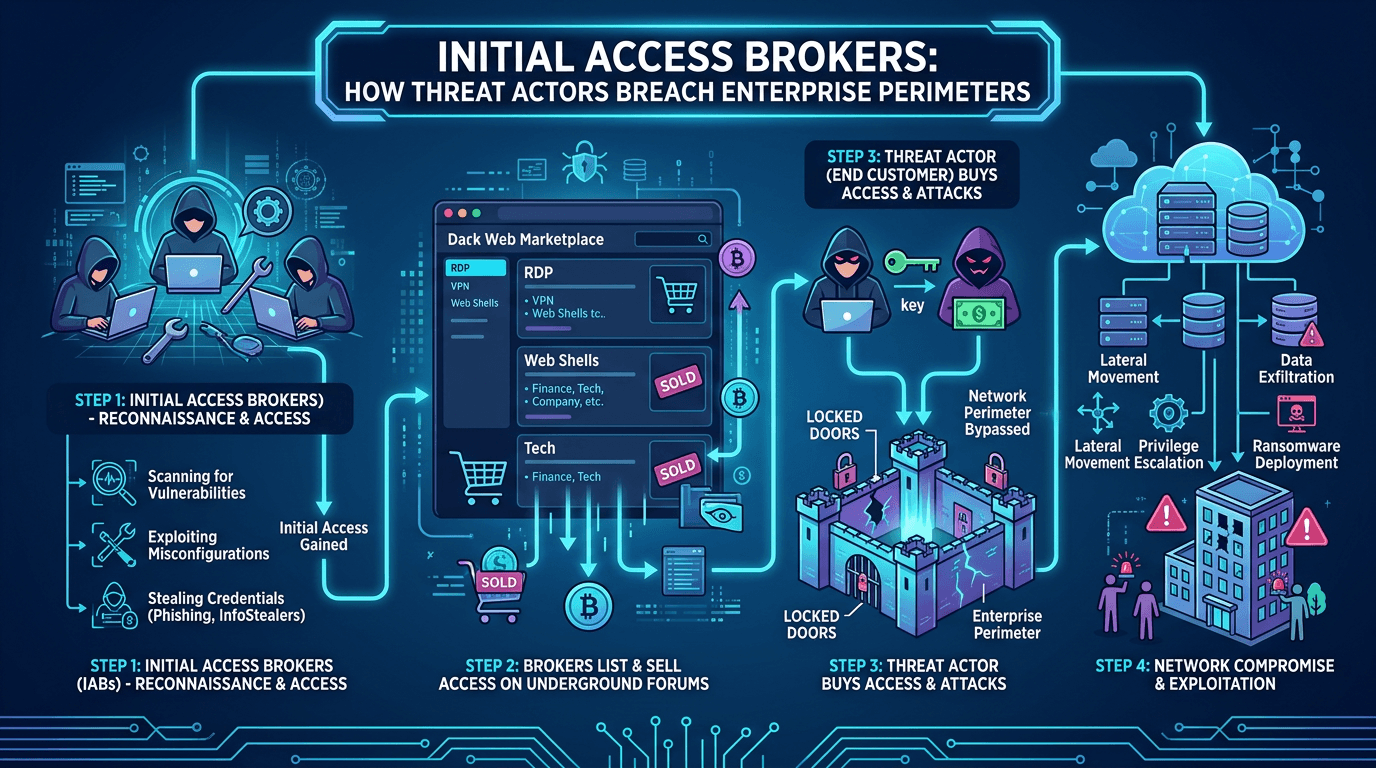 Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026
Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026A deep dive into initial access brokers (IABs)—the cybercrime specialists who sell footholds into corporate networks—covering their techniques, pricing, detection signals, and how to defend against the top attack vectors they exploit.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker