Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
Short answer: In the cloud, a "malicious" IP is often just someone’s temporarily compromised tenant or a resold small VPS living inside a huge ASN. Mature teams combine per-IP reputation with cloud identity, configuration, and flow evidence so they are not trying to out-ban Amazon.
The Cloud Egress Story in One Paragraph
When an attacker spins up a command server in a customer region, the outbound IP is legitimate cloud infrastructure—no magic firewall rule can separate good tenants from bad ones without more context. That is why external reputation is necessary but never sufficient, and why ASN reputation alone misleads in hyperscalers.
How Abuse Shows Up: Three Patterns
1) Stolen creds, fast lateral movement
Compromised IAM keys, OAuth tokens, or admin sessions create new compute with attacker-controlled bootstrap scripts. The IP is "clean" in reputation databases until the campaign scales.
Pairing read: initial access broker trends for 2026 and C2 and callback infrastructure.
2) Exposed services and data stores
A mis-routed public endpoint becomes the bridge—often without any exotic malware. "Reputation" will not help if your storage bucket is public by policy.
Pairing read: cloud security threats and multi-cloud protection.
3) Phishing and lookalike infrastructure hosted in mainstream clouds
Attackers use the same well-known providers your employees trust. The domain, not the IP, may be the higher-signal field—see domain reputation scoring to prevent phishing.
What to Track for Each "Suspicious" Cloud IP
- Time window when it first appeared in your environment (newly seen vs long-lived partner)
- Port and protocol (HTTPS to odd endpoints vs SMTP vs SSH)
- Account identity that initiated the flow (workload role vs human SSO)
- Geography and ASN (weak priors) + domain reputation (often stronger) via IP/domain intelligence workflows
- Enrichment from a fast API, as in the IOC enrichment guide
AWS, Azure, and GCP: Platform-Native First
While vendor branding differs, the defensive spine is the same: strong identity, least privilege, and network segmentation.
- Identity guardrails — MFA, short-lived creds, break-glass discipline
- Network guardrails — private endpoints, service mesh, egress allowlists for sensitive subnets
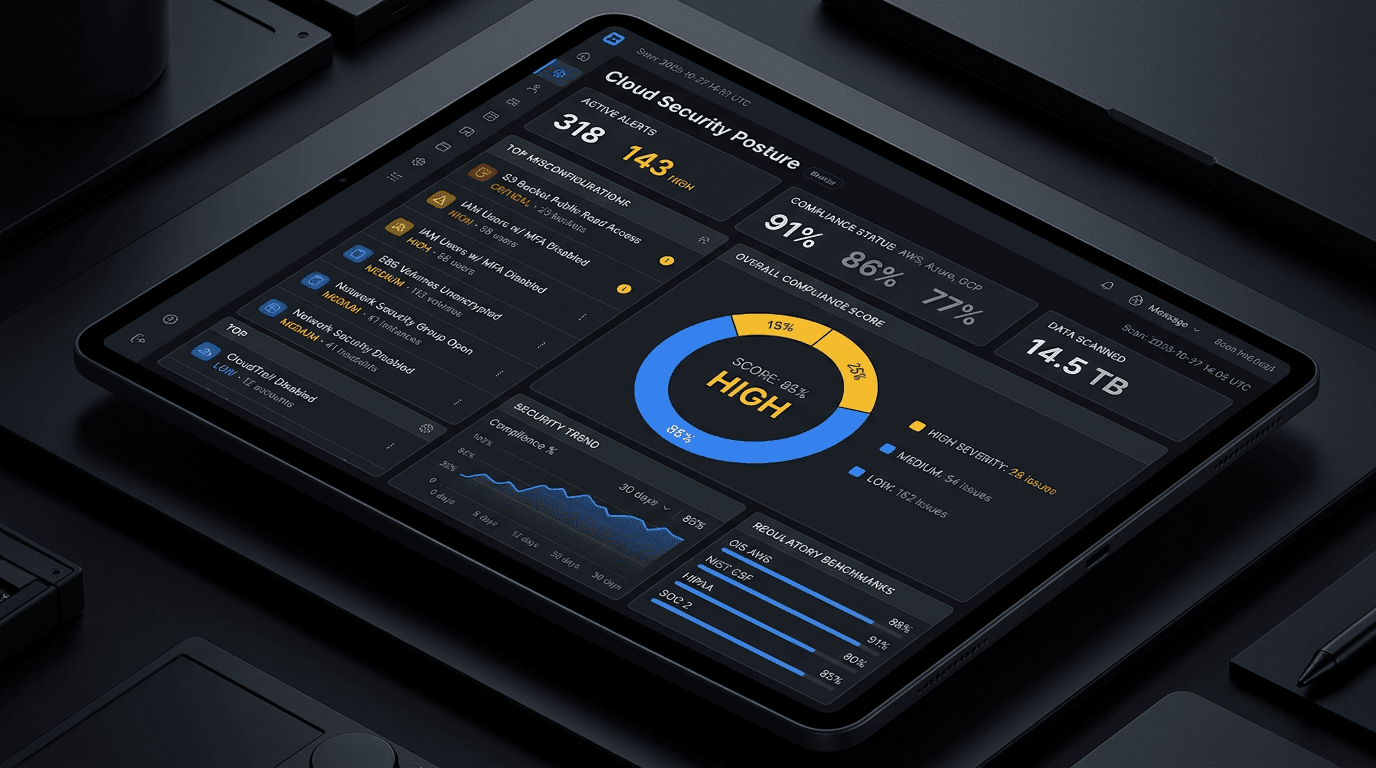
- Data guardrails — encryption, key rotation, and policy-as-code (CSPM topics covered in CSPM vs CWPP: cloud security acronyms)
False Positives: The Cloud SRE Problem
A blanket block on datacenter IPs can break B2B signups, break CI/CD, and enrage R&D. The right pattern is tiered friction: allow normal SaaS, challenge risky auth, block obvious abuse, and never silently drop partner traffic without a named exception.
The companion article proxy, VPN, Tor, and datacenter: classifying IP infrastructure in security tools offers a field-oriented matrix to separate anonymization, hosting, and mobile carrier contexts without moral panic.
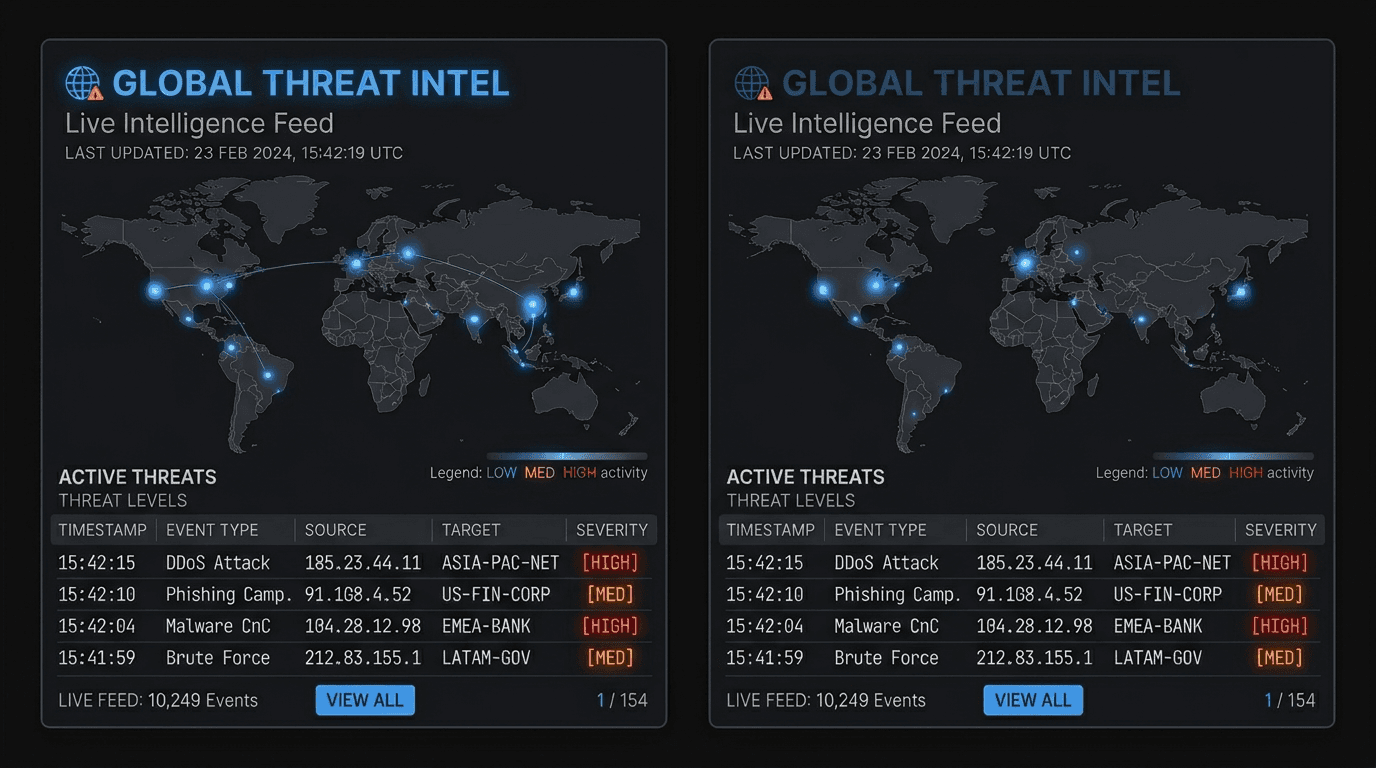
Threat Intel’s Role: Fast External Ground Truth
When a SIEM rule fires on a rare DNS name or a never-before-seen IP, a millisecond-level lookup can answer: is this a known sinkhole, a freshly registered domain, a widely reported C2, or a benign CDN? That is the sweet spot for an enrichment stack—also discussed in best threat intelligence APIs in 2026.
isMalicious is designed for fast entity checks across IP, domain, URL, and hash, ideal for the moment a cloud IR lead asks: "Is this object globally suspicious, or only suspicious in our unusual subnet?"
A Cloud Defender Checklist
- Inventory public exposure weekly (not annually)
- Tie every alert to an identity and asset, not just a 5-tuple
- Enrich network IOCs in tiered depth to avoid data swamp (see building IOC pipelines)
- Rehearse takedown for your own org’s stolen keys—speed beats cleverness
- Log reasoning in tickets: why you blocked or unblocked, with enrichment attached
Takeaway
Cloud IP reputation is a triage accelerant, not a moral judgment on an ASN. The winning architecture combines CSP controls + identity + targeted enrichment—so your team can move fast without turning the network into a roulette wheel of false positives.
Validate suspicious observables with the isMalicious IP / domain checker and attach the output to the incident file for auditability.
Field Notes: The Same Public IP, Three Different Truths
Engineers new to the cloud often get stuck on a question that sounds simple: “Is this IP good or bad?” The grown-up version is: good for what identity, in what time window, to which destination, with what data class? A public IP in AWS might be a NAT gateway for 200 microservices, a one-off red-team droplet, or a stolen key spinning cryptominers. Cloud logs—not reputation alone—tell you which world you are in.
Example thought experiment
- If the IP belongs to a workload role that suddenly talks to a never-before-seen domain on 443, enrich the domain first; often the real story is lookalike phishing and domain reputation rather than “bad Amazon.”
- If the same IP is seen across dozens of unrelated tenants in raw internet scans, you are probably just seeing a shared egress pattern; pivot by domain and certificate, not by ASN shame.
Working With Your Cloud Team: Questions That Get Answers Fast
- What region and account created this public IP, and is it stable or ephemeral (EC2, NAT, load balancer, Lambda egress)?
- Is there a service mesh or egress proxy you should be watching instead of raw VM traffic?
- Is this customer-facing or internal-only? (Same IP classes can be wildly different in acceptable risk)
These questions align security with the people who can actually stop the next breach: owners of IAM, networking, and data—not the ASN label in a CSV.
A Quick Win in Most Environments
Create a single “cloud egress” saved search that joins IP reputation + identity + DNS query name for any connection where the process is not a known update service. It will surface more true positives in a week than a wall of indiscriminate “datacenter = evil” WAF lines ever will, especially when you combine it with the practical scoring discipline in threat intel risk scores and false positives.
Frequently asked questions
- Why is cloud IP reputation different from "classic" IP reputation?
- Cloud IPs are frequently reassigned, shared across many tenants, and often represent ephemeral workloads. A reputation score for a public cloud egress IP may change meaning quickly, so defenders pair external reputation with account identity, network logs, and cloud-native asset context.
- Should I block an IP because it is in a "high-risk" ASN?
- Generally no for hyperscalers. Large ASNs are mixed-use. Use ASN as a weak prior and rely on per-IP reputation, domain context, and your own flow logs for decisions.
- What is the first-party control to prioritize?
- Identity and service exposure: IMDS hardening, public bucket policies, open security groups, and over-broad peering. Cloud compromise often presents as a stolen credential launching resources—not a "bad country IP".
- How do I reduce false positives on VPN and developer traffic?
- Track corporate egress ranges, require explicit allowlists for admin paths, and use step-up auth instead of indiscriminate IP blocking. See also VPN/proxy context articles linked from this post.
- How can isMalicious help?
- isMalicious can enrich suspicious IPs, domains, and URLs encountered in cloud logs, phishing reports, and IR timelines with aggregated reputation and threat context—complementing CSP-native telemetry rather than replacing it.
Related articles
 Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real Attacks
Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real AttacksAlert fatigue is not a staffing problem alone. SOC teams need better evidence, source quality, confidence bands, and enrichment workflows that turn noisy alerts into defensible decisions.
 Apr 29, 2026Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)
Apr 29, 2026Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)Not every "datacenter" IP is malicious, and not every Tor exit is a fraudster. This matrix-style guide helps you combine IP type signals with reputation and product context for safer, explainable security decisions.
 Apr 27, 2026ASN Reputation for Threat Intelligence: How Autonomous System Intelligence Improves Prioritization and Hunt Programs
Apr 27, 2026ASN Reputation for Threat Intelligence: How Autonomous System Intelligence Improves Prioritization and Hunt ProgramsAn IP address is a snapshot; an autonomous system (ASN) is a neighborhood. Learn how to use ASN context safely for triage, fraud, and security operations—without mistaking a giant cloud for a monolithic "bad host".
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker