Proxy, VPN, Tor, and Datacenter IPs: A Decision Matrix for WAF, Fraud, and SIEM Rules (Without Breaking Real Users)
Not every "datacenter" IP is malicious, and not every Tor exit is a fraudster. This matrix-style guide helps you combine IP type signals with reputation and product context for safer, explainable security decisions.

Short answer: Treat IP type (Tor vs VPN vs datacenter vs residential) as a prior that shapes friction—not a final verdict. Pair it with reputation and app-specific abuse heuristics so you can explain every block to a human in support.
Note: We already publish a deep narrative on VPN, proxy, and Tor anonymized traffic and fraud risk. This page is a complement: a decision matrix and policy patterns for people wiring rules, not a second essay on the same story.
The One-Minute Mental Model
| Signal | What it usually means | How to use it | Pitfalls | | ------------------ | ---------------------------------- | ----------------------------------------- | ------------------------------------------- | | Tor exit | High anonymity, abuse-friendly | High friction for high-value actions | Journalists, researchers, and privacy users | | Commercial VPN | Geoshift not necessarily malicious | Add MFA on sensitive flows | Over-blocking harms global users | | Datacenter | Server-side traffic, bots common | Tighten auth for consumer apps | Breaks B2B signups, ops tools | | Residential | Looks "normal" | Rely on behavior + device, not just IP | Residential proxy networks are sneaky | | Mobile carrier | Consumer mobility | Less bot-like unless you see automation | Carriers re-use NAT—velocity matters |
Where IP Type Fits in the Control Stack
- Edge/WAF — challenge or CAPTCHA, not indiscriminate 403, unless a tiny admin surface
- Fraud/ATO — combine IP signals with credential stuffing patterns and session telemetry
- SOC triage — use IP type to route tickets; pair with IOC enrichment APIs
- IR — avoid burning infrastructure pivots: combine IP with domain/hostname context and C2 heuristics from C2 over DNS and web
Policy Anti-Patterns (We See These Weekly)
- "Block all non-residential" for a general B2B SaaS → revenue and support pain
- Using country alone as a security control → false positives, compliance debates, and blind spots. If you have regulatory drivers, document them; do not conflate geo with malice in a threat model
- Treating a single list hit as a conviction without timestamps—stale data causes stale bans
A cleaner approach lives in risk scoring and false positives in reputation systems.
Engineering the Rule: A Template
For each public route (signup, password reset, payment, file upload, API with user token):
- Base controls — rate limit, account lockout policy, and device binding where appropriate
- IP type tier — if Tor or known open proxy, require step-up; if datacenter, add bot checks; if mobile, add velocity
- Reputation check — call an enrichment service for both IP and related domain, like isMalicious’ unified checks described in the threat API comparison for 2026
- Exception registry — partner org VPN ranges, your own office egress, third-party integrators
- Logging — store both inputs and the decision for post-incident review
Cloud, CDN, and Shared Hosting: Read ASNs with Care
Massive ASNs (especially clouds) are mixed neighborhoods. A datacenter label should raise attention for consumer fraud, but not justify blocking API integrations for enterprise customers. For cloud-native nuance, read cloud IP reputation for AWS, Azure, and GCP alongside ASN reputation basics.
A Simple Runbook: "We Saw This IP"
- Is it a static corporate VPN? → confirm with the customer
- Is it a compromised cloud instance? → pivot to cloud account identity and IR essentials
- Is it Tor? → decide product policy, document it publicly if consumer-facing
- Is the domain typosquatted? → typosquatting patterns and IDN homograph attacks
Why isMalicious Is a Pragmatic Enrichment Block
isMalicious focuses on high-speed multi-entity checks—IP, domain, URL, hash—so you can put one integration behind WAF, SOAR, and analyst tooling instead of taping three niche feeds together. If you are comparing vendors, the VirusTotal alternative perspective is a candid look at scope.
The Bottom Line
The internet is supposed to be messy: privacy tools, dev clouds, and mobile NAT all produce scary-looking logs. Mature security teams do not "win" by blocking the most; they win by explaining the most decisions correctly—and keeping false positives from training users to click through warnings.
Try a live lookup in the isMalicious IP / domain checker when you are unsure whether a session deserves a block, a step-up, or a yawn.
Sample Policy Statements You Can Put in a Runbook
Clarity cuts escalations. Consider adopting language like this:
- “We do not block countries for security. We use reputation, behavior, and product risk; geo rules are documented separately if legally required.”
- “A datacenter IP requires extra verification for high-value consumer actions, but is normal for B2B and partnership integrations.”
- “Tor exits are blocked for consumer banking sessions unless the user is on a named research allowlist, managed by the security team.”
- “Any automated block that impacts customers requires a named exception path in under 15 minutes of wall-clock time on business days.”
This is the same explainability bar we apply to reputation products in risk scoring and false positives: if a policy is not defensible, it is not a policy.
For Analysts: What to Write in the Ticket
A good note includes: the observable (IP), the inferred class (hosting, Tor, etc.), the reputation summary, the product surface (login, password reset, API), and a recommendation (allow + monitor, step-up, block). It should not include moralizing about a country, and it should not include unverifiable hunches. When you are unsure, enrich the domain and URL too—safe browsing and URL risk basics are still table stakes, especially for ATO and phishing lures.
Frequently asked questions
- Is blocking Tor exits a good default?
- It can be, depending on the application. For consumer banking, you may need strict controls. For public research portals, wholesale blocking can harm legitimate users. Prefer risk-based step-up: MFA, velocity checks, and device signals alongside IP intelligence.
- Why is datacenter IP a weak stand-alone signal?
- Legitimate B2B traffic, CI/CD, and cloud admin consoles often come from data centers. Treat datacenter as a "raise scrutiny" flag, not an automatic block—unless you have a very narrow public surface.
- How is this post different from generic VPN education?
- We focus on operational policy: how to combine IP type, reputation, and product-specific abuse patterns, with explicit anti-patterns (like geo-blocking) that create security debt.
- What tool data should a rule include for audit?
- The indicator, enrichment timestamp, source lists or scores, ASN, the decision, and a link to a runbook. If you use isMalicious, store the output snapshot in your ticket for repeatability.
- How does isMalicious help classify risky IPs?
- isMalicious offers fast, aggregated IP and domain reputation context suitable for pre-auth checks, fraud stacks, and SOAR, covering multiple observable types in one place.
Related articles
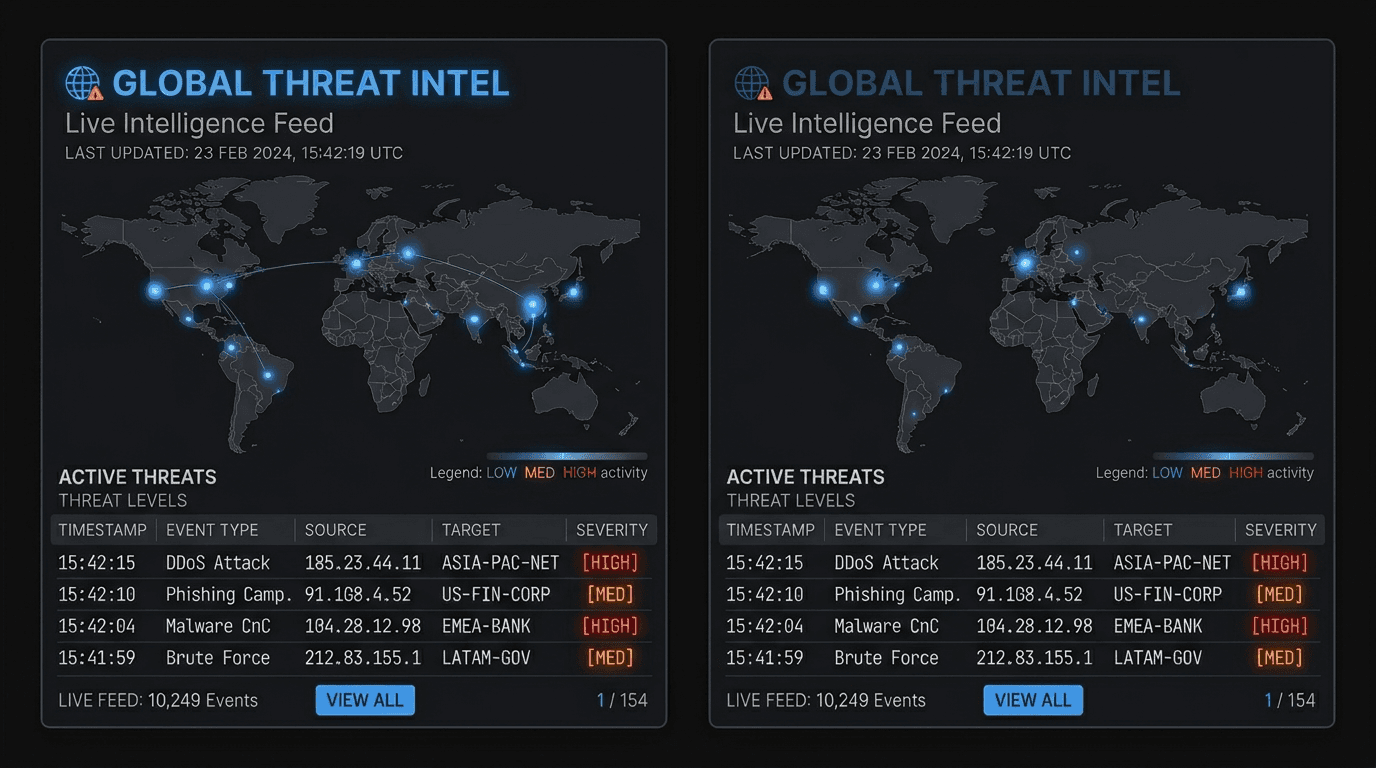
 Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real Attacks
Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real AttacksAlert fatigue is not a staffing problem alone. SOC teams need better evidence, source quality, confidence bands, and enrichment workflows that turn noisy alerts into defensible decisions.
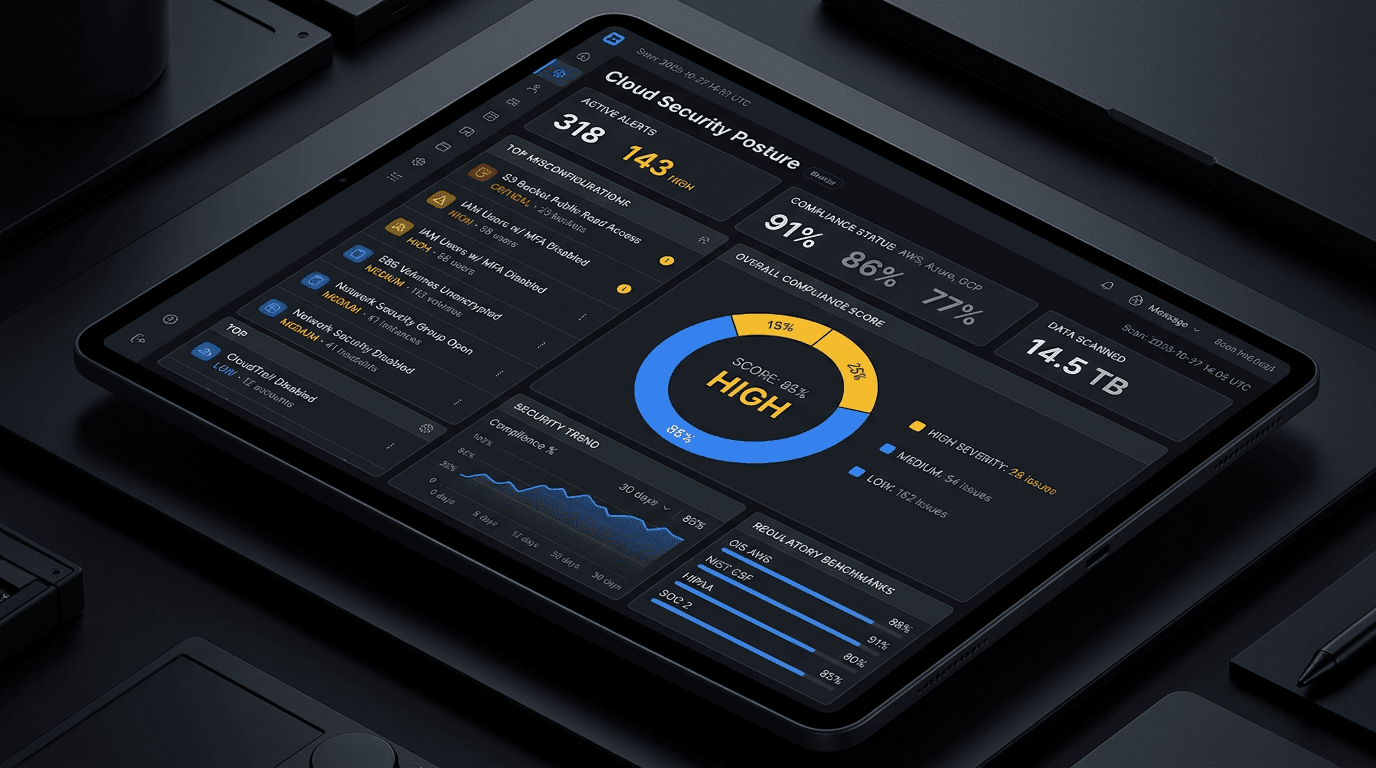 Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
 Apr 27, 2026ASN Reputation for Threat Intelligence: How Autonomous System Intelligence Improves Prioritization and Hunt Programs
Apr 27, 2026ASN Reputation for Threat Intelligence: How Autonomous System Intelligence Improves Prioritization and Hunt ProgramsAn IP address is a snapshot; an autonomous system (ASN) is a neighborhood. Learn how to use ASN context safely for triage, fraud, and security operations—without mistaking a giant cloud for a monolithic "bad host".
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker