CSPM vs. CWPP: Decoding Cloud Security Acronyms
 IsMalicious Team
IsMalicious Team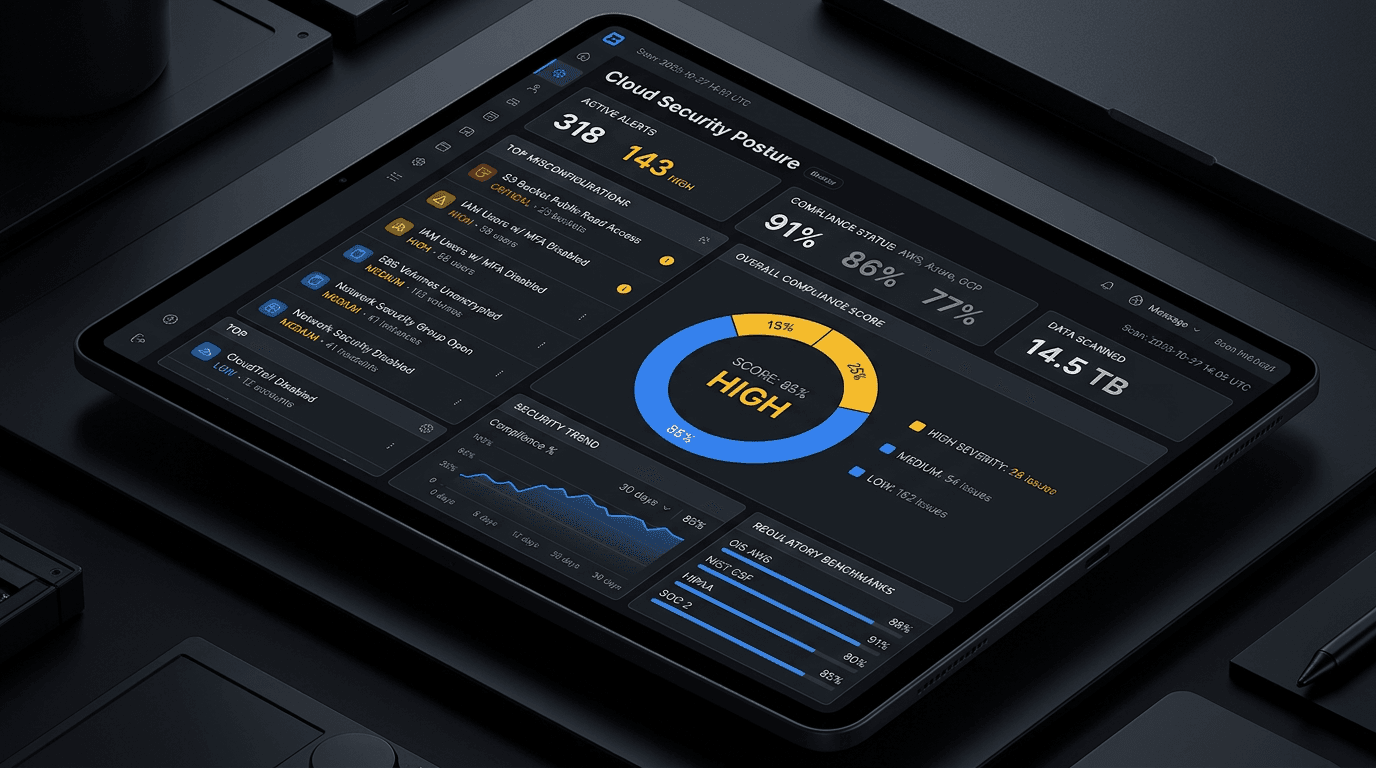
Navigating the cloud security market can feel like swimming in a sea of acronyms. Two of the most critical are CSPM (Cloud Security Posture Management) and CWPP (Cloud Workload Protection Platform). While they sound similar, they solve different problems.
CSPM: The Control Plane
Cloud Security Posture Management focuses on the configuration of your cloud infrastructure. It answers the question: "Is my cloud environment set up securely?"
- Key Functions:
- Detecting misconfigurations (e.g., open S3 buckets).
- Monitoring compliance (e.g., CIS Benchmarks, HIPAA).
- Visualizing cloud asset inventory.
- Analogy: CSPM is like checking that all the doors and windows of your house are locked and the alarm is set.
CWPP: The Data Plane
Cloud Workload Protection Platform focuses on the workloads running inside your cloud environment—virtual machines, containers, and serverless functions. It answers the question: "Are my applications secure from runtime threats?"
- Key Functions:
- Runtime threat detection.
- Vulnerability scanning of running containers.
- System integrity monitoring.
- Micro-segmentation.
- Analogy: CWPP is like having a security guard inside the house to stop an intruder who managed to break in.
CNAPP: The Convergence
Recently, the industry has moved towards CNAPP (Cloud Native Application Protection Platform), which combines CSPM and CWPP into a single solution. This provides a holistic view of cloud risk, correlating misconfigurations with runtime threats.
Conclusion
You likely need both. A perfectly configured cloud (CSPM) can still host a vulnerable application (CWPP). Conversely, a secure application running on an open bucket is a data breach waiting to happen. Understanding these tools is the first step to a robust cloud defense.
Related articles
 Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
 Jan 23, 2026Container and Kubernetes Security: Protecting Cloud-Native Applications
Jan 23, 2026Container and Kubernetes Security: Protecting Cloud-Native ApplicationsContainer environments introduce unique security challenges. Learn how to secure Docker containers, Kubernetes clusters, and cloud-native applications from emerging threats and misconfigurations.
 Jan 7, 2026Cloud Security Threats: Protecting Multi-Cloud Infrastructure
Jan 7, 2026Cloud Security Threats: Protecting Multi-Cloud InfrastructureCloud environments face unique security challenges from misconfigurations to cryptomining attacks. Learn how to monitor cloud assets, detect threats, and protect your multi-cloud infrastructure with threat intelligence.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker