Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026
A deep dive into initial access brokers (IABs)—the cybercrime specialists who sell footholds into corporate networks—covering their techniques, pricing, detection signals, and how to defend against the top attack vectors they exploit.
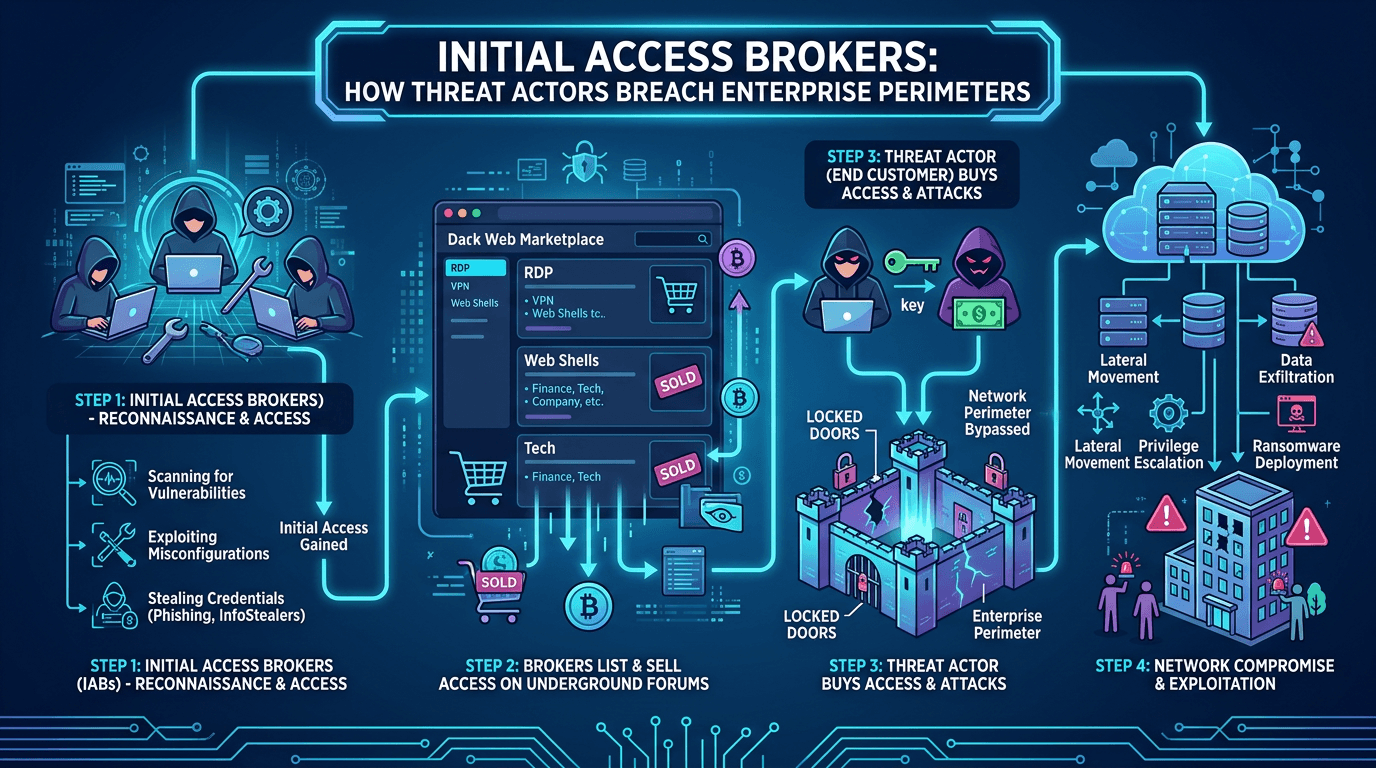
For most of cybercrime’s history, a single actor or group handled an intrusion end to end: reconnaissance, breach, movement, exfiltration, extortion. That model is largely gone. In 2026, the cybercrime economy is a specialized supply chain, and at the front of that chain sit initial access brokers (IABs)—criminals whose entire business is breaching corporate networks and selling the foothold to whoever will pay. This post explains who IABs are, what attack vectors they favor, how they package and sell access, and how defenders can detect the quiet early stages of an IAB intrusion before it escalates into a ransomware incident.
What Is an Initial Access Broker?
An initial access broker is a threat actor specializing in access acquisition. They compromise networks, characterize the access, and list it for sale on cybercrime forums, private Telegram channels, or dark-web marketplaces. The buyers are typically ransomware affiliates, data-theft extortionists, state-aligned operators, or other criminals who value a ready-made foothold over the effort of building one.
IABs are often more patient and disciplined than the actors who buy from them. Because their reputation depends on delivering working access, good IABs verify their footholds—testing credentials, documenting network topology, and listing access with details such as industry, revenue, geography, domain admin status, and security product telemetry. Some IABs even offer warranties or refunds if access expires before the buyer’s operation completes.
This specialization is the biggest force multiplier in modern ransomware operations. It shortens the time between “attacker chose target” and “attacker inside target” from weeks to hours, because the access already existed in inventory.
Why IABs Dominate the 2026 Threat Landscape
Three trends made IABs central to modern cybercrime:
- Ransomware-as-a-service (RaaS): RaaS programs divide labor across operators, affiliates, negotiators, and developers. Buying access from IABs completes the assembly line.
- Credential theft scale: Infostealer malware exfiltrates browser-stored credentials, session cookies, and VPN profiles from millions of endpoints. Raw logs flow through markets, and IABs mine them for corporate access.
- Edge-device vulnerabilities: VPN concentrators, firewalls, and file transfer appliances have been repeatedly hit by pre-authentication CVEs. Mass exploitation produces fresh access for resale within days.
Defenders who still think of threat actors as monolithic attackers will miss the entry phase, because IABs optimize for stealth in ways that financially motivated operators once did not. The initial foothold is their product; they cannot afford to spook it.
Top Attack Vectors Used by Initial Access Brokers
1. Compromised VPN and Remote Access Credentials
The single largest source of corporate network access in 2026 is compromised VPN credentials, typically harvested by infostealers and resold in bulk. An employee installs a cracked application at home, the infostealer captures their saved browser credentials, and six weeks later those credentials show up in an IAB listing.
The attack path is simple because the door was already unlocked: no exploitation, no malware on the perimeter, just a valid login from a new IP. Without multi-factor authentication (MFA) enforced everywhere, a single stolen password grants the same access the legitimate user had. MFA is a mitigation, but not a cure—IABs increasingly advertise access with session cookies that sidestep MFA entirely.
2. Unpatched Edge Devices
Edge devices—VPN concentrators, firewalls, MFT appliances, email gateways, remote management platforms—are the gift that keeps giving to IABs. When a pre-auth unauthenticated RCE CVE is disclosed in a popular product, IABs race to mass-scan the internet, exploit vulnerable instances, and list access. The delay between CVE disclosure and active exploitation is often measured in hours.
The defensive response depends on: (a) rapid patching of internet-facing equipment, (b) continuous external attack surface monitoring, and (c) threat intelligence on actively exploited CVEs. Pair these with infrastructure reputation from services like isMalicious to detect post-exploit beaconing to known malicious IPs.
3. Phishing and Infostealer Malware
Phishing remains a reliable initial vector, but its role has shifted. Rather than delivering ransomware directly, phishing lures now increasingly deliver infostealers that harvest credentials for later resale. The criminal economy behind infostealers is industrialized: log clouds, automated parsers, filtering for corporate credentials, and bulk sale to IABs.
This changes defender priorities. Detecting a single infostealer execution on one laptop is good; more importantly, you must assume that when an infostealer runs, all credentials stored in that user’s browser are compromised and might appear in an IAB listing. Rapid credential rotation and session invalidation become core incident response steps.
4. Exposed Remote Desktop Protocol (RDP)
Despite years of warnings, exposed RDP endpoints remain on the internet in large numbers. IABs brute-force, credential-stuff, and exploit RDP routinely. Some listings target specific industries, explicitly advertising “domain admin via RDP” access with confirmed screenshots.
Organizations that still rely on internet-facing RDP should move to zero-trust access models yesterday. Where RDP must remain available, wrap it in MFA-enforced brokers, not raw TCP/3389 exposure.
5. Supply Chain and Managed Service Provider (MSP) Compromise
High-value IAB listings sometimes describe access through a managed service provider—one breach yielding footholds into many downstream clients. MSP compromises are especially damaging because privileged remote access tools (RMM platforms) by design allow execution across customer environments. IABs listing MSP access often command premium prices because the buyer can monetize it against many victims.
Defensive mitigations include rigorous MSP security due diligence, least-privilege RMM deployments, separate privileged accounts per tenant, and telemetry sharing agreements that let clients observe access patterns.
6. Business Email Compromise Footholds
Some IABs focus on email-centric access: Microsoft 365 or Google Workspace tenant logins with persistent refresh tokens. This access enables not only credential and data theft but also internal phishing, invoice fraud, and lateral expansion via cloud-integrated apps. A single stolen session cookie can grant days or weeks of access before it expires.
Anatomy of an IAB-to-Ransomware Handoff
A typical handoff looks like this:
- The IAB gains access via one of the vectors above.
- They spend minimal time escalating privileges—often just enough to verify they have domain admin or cloud tenant admin.
- They test persistence (a secondary account, a new VPN configuration).
- They catalogue the victim: industry, approximate revenue, presence of EDR products, backup setup if visible.
- The access is posted or privately offered to trusted buyers.
- A ransomware affiliate purchases, moves laterally, deploys ransomware, and exfiltrates data.
Defenders have a window of days or even weeks between steps 1 and 6. Detecting the quiet phase—the IAB’s careful footprint—is the single highest-leverage investment a SOC can make.
Detection Strategies for IAB Activity
Since IABs optimize for stealth, signature-based detection falls short. Focus on behavioral signals:
- Identity anomalies: New logins from unusual geographies, impossible-travel patterns, MFA fatigue or push-bombing attempts, sudden changes in authentication patterns.
- Session and cookie abuse: Detect session tokens used from unexpected device fingerprints.
- Beaconing to unfamiliar infrastructure: Correlate outbound connections with infrastructure reputation. isMalicious and similar services flag IPs and domains with histories of malicious activity—an IAB beaconing to a staging server will often light these up.
- New privileged account creation or modification: Any change to admin accounts outside of approved change windows.
- VPN and remote access telemetry: Authentications from residential IP ranges, IP addresses previously associated with cybercrime infrastructure, or short-lived session patterns.
- Credential dumping tools: Even disciplined IABs occasionally use Mimikatz, LSASS dumping, or LSA Secrets extraction. EDR telemetry should flag these instantly.
No single signal is definitive; the combination, especially correlated against external reputation data, is how SOCs spot IAB activity.
Disrupting the IAB Supply Chain
Organizations cannot dismantle cybercrime markets alone, but they can reduce their exposure to the IAB supply chain:
- Aggressive MFA everywhere, including contractors, legacy apps, and on-premises VPN.
- Session-token lifetime reductions and automatic revocation on risk signals.
- Conditional access policies that factor in device posture and geolocation.
- External attack surface management to find exposed edge services before IABs do.
- Infostealer detection and response: When an endpoint shows infostealer signs, treat all credentials on it as compromised.
- Credential monitoring on dark web and paste sites: Early warning that your domain appears in a leak often translates to an IAB listing days later.
- Supplier risk management: For MSPs, demand specific controls (hardware MFA for privileged access, separation of duties, logging integration).
The Role of Threat Intelligence in IAB Defense
Effective defense against IABs blends tactical, operational, and strategic threat intelligence:
- Tactical: Live IOC feeds covering IAB staging infrastructure, malicious VPN exit nodes, and known-bad IP ranges. Platforms like isMalicious deliver this reputation data at speed.
- Operational: Campaign reports mapping IABs to their preferred CVEs, TTPs, and buyers. When a new edge-device CVE drops, operational CTI tells you which IABs jump on it fastest.
- Strategic: Market-level reporting on IAB pricing, sector targeting, and industry trends. This guides long-term investments—when reports show healthcare IAB listings rising, healthcare security leaders fund programs accordingly.
Integrated CTI also helps incident response. When a confirmed compromise maps to IAB-known infrastructure or patterns, responders can pivot to ransomware-affiliate playbooks before encryption starts.
Common Defensive Mistakes
Even security-mature organizations stumble on familiar mistakes when defending against IABs:
- MFA gaps in legacy systems: One unpatched legacy VPN gateway or RDP jump host undoes the rest of the program.
- Assuming EDR is enough: EDR catches many behaviors but not a valid VPN login from a new IP. Identity telemetry fills the gap.
- Underinvesting in external attack surface: Asset inventories on paper often differ from reality on the internet.
- Ignoring infostealer signals: A single infostealer hit should trigger credential hygiene across that user’s entire role.
- Weak supplier oversight: Your MSP’s posture is part of your attack surface.
The Economics Perspective
Understanding IABs as a business changes defender priorities. An IAB is rational: they invest where the return is highest. Organizations that make initial access cheaper than average become higher-probability targets; those who make it more expensive—through MFA, hardening, monitoring, and rapid patching—become less attractive. You do not need to be uncrackable; you need to be more expensive than the next target in the IAB’s scanner output.
This is why routine hygiene (patching, MFA, credential rotation, external exposure reduction) outperforms exotic defenses for most organizations. IAB defense is less about cleverness and more about denying the easy wins that sustain their business model.
Conclusion
Initial access brokers have transformed the cybercrime economy by specializing in the one step that ransomware operators used to do themselves. Their favored attack vectors—stolen VPN credentials, unpatched edge devices, infostealer logs, RDP, MSP compromise, email session theft—are well understood, but defending against them requires integrated identity, endpoint, network, and intelligence telemetry working together.
Invest in MFA everywhere, monitor session activity as seriously as login activity, reduce external attack surface aggressively, and enrich every alert with threat intelligence about the infrastructure IABs use. Reputation data from providers like isMalicious gives SOC analysts real-time signal on malicious IPs and domains—exactly the kind of context that turns a quiet login into a high-priority alert before ransomware ever arrives. The best defense against an IAB is to ensure your network is never worth their time.
Frequently asked questions
- What is an initial access broker?
- An initial access broker (IAB) is a cybercriminal who specializes in obtaining unauthorized access to corporate networks and selling that access to other threat actors, most commonly ransomware affiliates. IABs typically do not carry out the final attack themselves; they monetize the foothold.
- What are the most common initial access vectors used by IABs in 2026?
- The most common vectors are exposed VPN and remote access services with stolen credentials, unpatched edge devices (VPN concentrators, firewalls, file transfer appliances), phishing-delivered infostealers, exposed RDP, and supply chain compromises through managed service providers.
- How can organizations detect an IAB intrusion before ransomware deploys?
- Focus on the "dwell time" between initial access and full compromise. Monitor for unusual logins from new geographies, VPN authentication anomalies, sudden MFA prompts, beaconing to unknown infrastructure, and credential dumping activity. Good identity telemetry plus infrastructure reputation data on IPs and domains catches most IAB handoffs.
Related articles
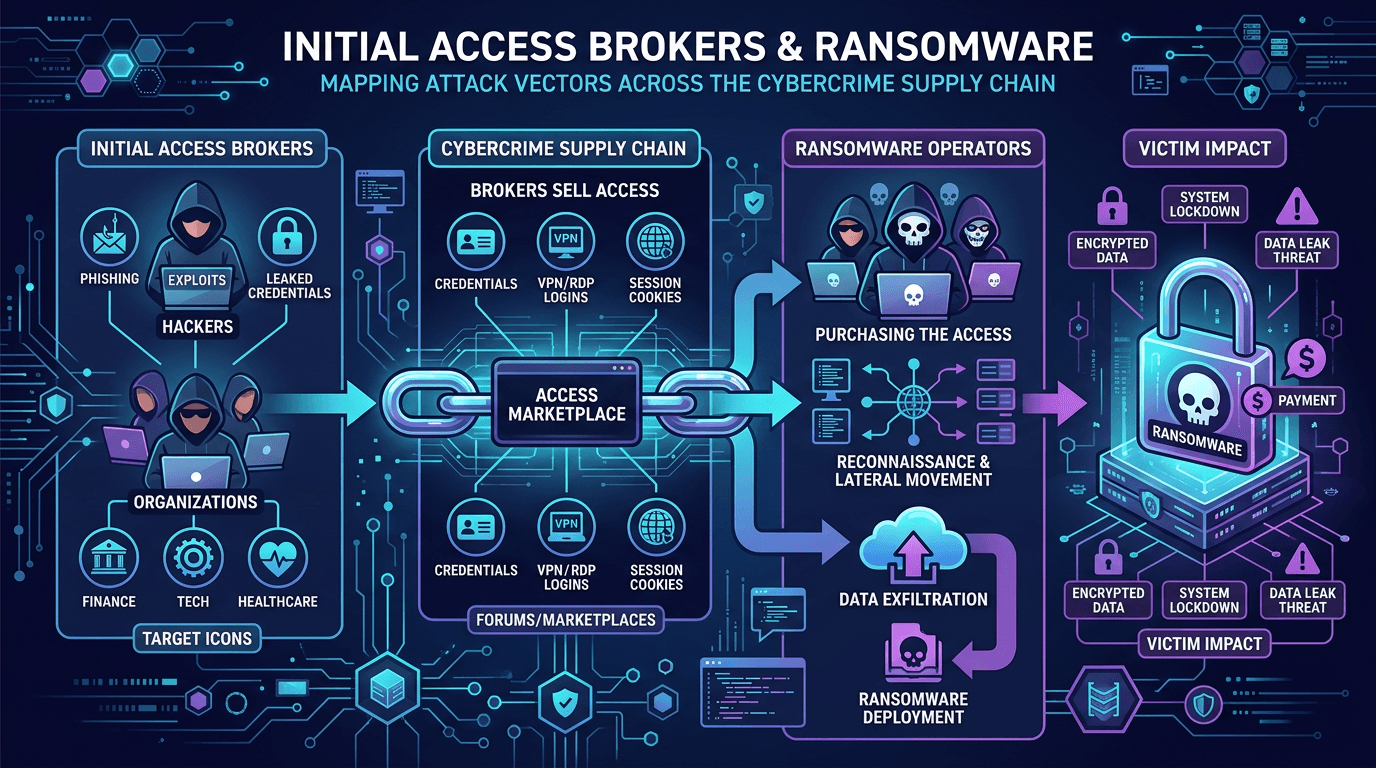 Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply ChainUnderstand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
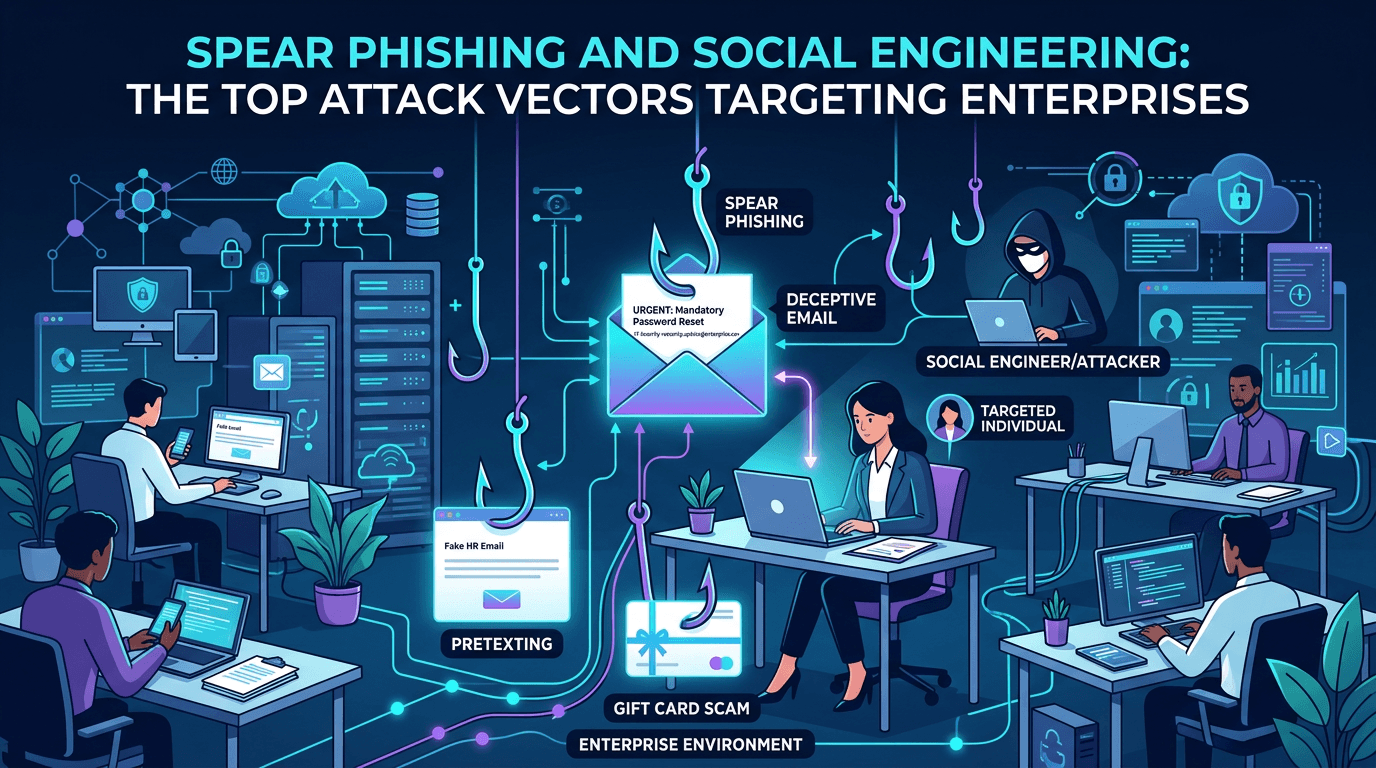 Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
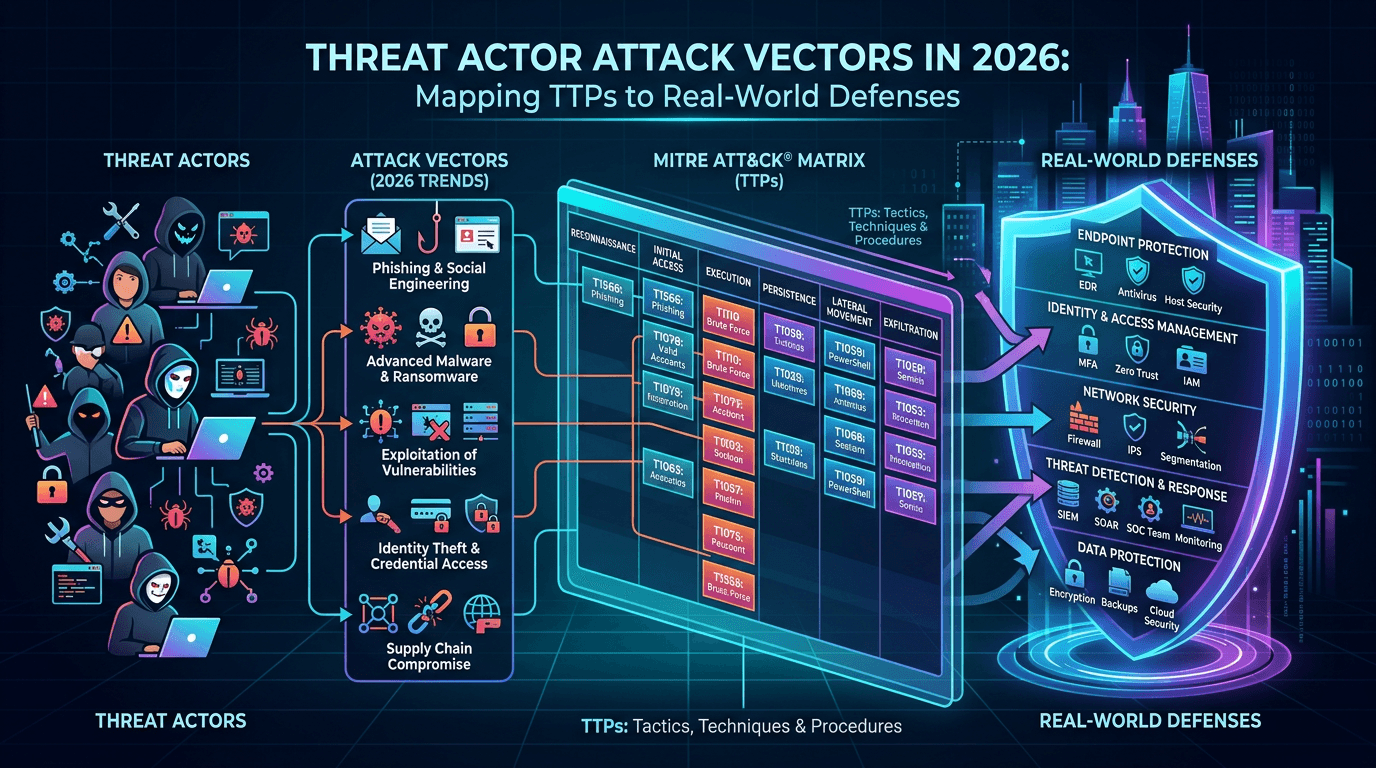 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker