Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026
A practical engineering guide to building indicator of compromise (IOC) pipelines—ingestion, normalization, deduplication, enrichment, scoring, distribution, and feedback—to turn raw threat feeds into operational defense.
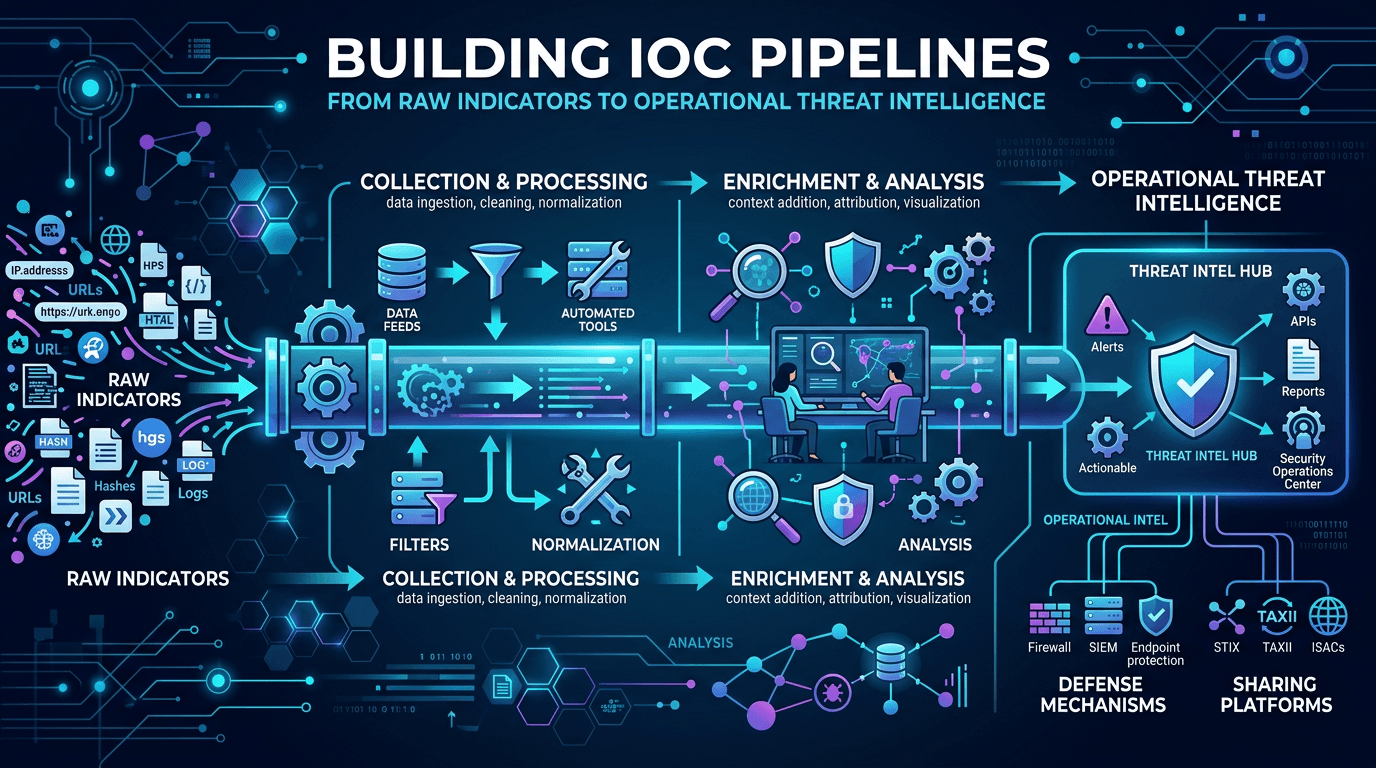
Indicators of compromise (IOCs) are the plumbing of tactical threat intelligence. Every SIEM rule, every firewall blocklist, every SOAR enrichment step ultimately depends on a pipeline that takes raw indicator data—domains, IPs, URLs, file hashes, email addresses—and converts it into filtered, contextualized, time-bound signals that security controls can consume. Done well, an IOC pipeline silently runs the tactical heart of a SOC; done poorly, it drowns analysts in noise or leaves them blind to known threats. This guide walks through IOC pipeline engineering end to end: ingestion, normalization, deduplication, enrichment, scoring, distribution, and feedback.
Why IOC Pipelines Matter
A single IOC—say, a domain observed hosting credential-harvesting pages—is only useful if it reaches the right control at the right time with the right context. In practice, that requires:
- Ingestion from the source that published it.
- Validation that the indicator is well formed.
- Normalization to a canonical representation.
- Deduplication against indicators already in the pipeline.
- Enrichment with context (reputation, WHOIS, passive DNS, associated infrastructure).
- Scoring for confidence and relevance.
- Distribution to consumers (SIEM, EDR, web proxy, firewall).
- Lifecycle management (TTLs, aging, revocation).
- Feedback from consumers back into the source ratings.
Skip any step and the pipeline degrades. A surprising amount of SOC pain—false positives, missed detections, analyst fatigue—traces back to weak IOC pipelines.
Ingestion: Many Sources, Many Formats
An effective pipeline ingests from a diverse portfolio:
- Commercial threat intelligence feeds via STIX/TAXII, CSV, JSON, or vendor APIs.
- Government and sector sharing (CISA, ISACs, national CERTs).
- Open source intelligence (OSINT) feeds on GitHub, community platforms, and research blogs.
- Vendor reputation services including infrastructure-focused providers like isMalicious for real-time domain, IP, and URL reputation.
- Internal telemetry: Your own EDR, SIEM, sandbox, and incident response produce IOCs that deserve first-class treatment.
- Partner exchanges: Bilateral sharing arrangements with trusted peers.
Each source has its own cadence, format, and quality level. Build ingestion adapters that handle the most common standards—STIX 2.x over TAXII 2.1, Mandiant MISP, CSV, JSON-lines—and write custom adapters sparingly.
Rate limits, authentication, and retries belong in the ingestion layer, not sprinkled through downstream code. A well-isolated adapter makes source churn (adding or dropping feeds) manageable.
Validation and Normalization
Raw indicators are dirty. Validation rejects obvious garbage:
- IP addresses: Reject RFC 1918 private ranges, link-local, loopback, and reserved ranges unless explicitly in scope.
- Domains: Enforce syntactic validity, Punycode normalization, removal of trailing dots, and rejection of schema-invalid values.
- URLs: Parse with an RFC-compliant parser, normalize scheme and host case, decide on path/query normalization policy.
- File hashes: Validate length (32 for MD5, 40 for SHA-1, 64 for SHA-256), lowercase hex.
- Email addresses: Lowercase domain, preserve local-part case per RFC 5321 guidance, strip display names.
Normalization prevents duplicates masquerading as distinct indicators. EXAMPLE.COM, example.com, and example.com. all represent the same domain—store one canonical form everywhere.
Deduplication and Merge Semantics
Once normalized, deduplicate against the existing indicator store. Merge semantics matter: when two sources report the same indicator, do not overwrite; combine. Track:
- Sources that have reported the indicator.
- Source-specific confidence and timestamps.
- Context fragments contributed by each source (tags, campaign, malware family).
Under merging, the indicator’s overall confidence typically rises with independent corroboration, particularly when sources are diverse (commercial + government + OSINT + internal).
Enrichment: Context Turns IOCs Into Intelligence
A raw IOC is just a string. Enrichment transforms it into operational intelligence. Core enrichment types:
- Infrastructure reputation: Query services like isMalicious for domain, IP, and URL reputation, scoring, and classification history.
- WHOIS: Registrar, registration date, privacy status, historical changes.
- DNS and passive DNS: Current resolutions, historical resolutions, SOA records, MX records.
- Certificate transparency: Certificates issued for the domain or related names.
- Geolocation and ASN: For IPs, country, AS number, AS organization, hosting type.
- File hash lookups: For hashes, multiscanner detection ratios, malware family, behavioral data.
- Sandbox context: Behavioral analyses from public or private detonation services.
- Campaign and actor mapping: When threat intelligence allows, link IOCs to known campaigns and threat actors.
Enrichment adds load. Design for parallelism, caching, and graceful degradation: an enrichment source that times out should not block the rest of the pipeline.
Confidence Scoring and Relevance
A well-designed pipeline assigns each indicator a confidence score (how sure are we this is malicious?) and a relevance score (how important is this to our environment?).
Confidence factors include:
- Number and diversity of sources reporting the indicator.
- Source-level confidence weights.
- Age of the indicator and freshness of reports.
- Corroboration with infrastructure reputation and enrichment data.
- Internal observations of the indicator in telemetry.
Relevance factors include:
- Sector and geography targeting of the associated campaign.
- Whether the indicator’s associated technology or product is present in your environment.
- Whether the indicator has appeared in your own telemetry already.
- Business impact if the associated threat were realized.
Encoding these scores as metadata lets downstream automation make decisions appropriately—for example, auto-blocking only indicators above a confidence threshold while routing lower-confidence indicators to analyst review.
Distribution: Meeting Controls Where They Live
Downstream consumers speak many protocols. Your distribution layer should support:
- SIEM rule updates via API or watchlist imports.
- EDR blocklists and custom indicators via platform APIs.
- Firewall and web proxy feeds via URL lists, IP blocklists, or direct integrations.
- DNS sinkholing via RPZ zones or DNS firewall integrations.
- Email gateway policies for domain and URL blocks.
- SOAR playbooks for alert enrichment and response actions.
Different consumers tolerate different throughput and latencies. Design the distribution layer as publishers with back-pressure support, not synchronous delivery chains.
Lifecycle Management: TTL, Aging, Revocation
Indicators have life spans. Infrastructure rotates, actors abandon domains, phishing kits change staging hosts. Your pipeline must manage lifecycle:
- TTL by indicator type: Domains and IPs expire faster than file hashes.
- TTL by source: A high-confidence indicator with strong enrichment may persist longer than a low-confidence OSINT mention.
- Re-verification: Before expiry, re-check whether the indicator is still flagged by enrichment sources.
- Revocation: Sources sometimes retract indicators. Honor revocations and propagate them to downstream controls.
Without lifecycle management, blocklists grow indefinitely, creating false positives (revoked IPs, reassigned domains) and reducing the pipeline’s trustworthiness.
STIX, TAXII, and Interoperability
STIX (Structured Threat Information Expression) and TAXII (Trusted Automated Exchange of Intelligence Information) are the primary standards for IOC and threat intelligence interchange. In 2026, STIX 2.1 and TAXII 2.1 are widely supported by commercial TIPs and many government sharing programs.
Adopting STIX/TAXII in your pipeline pays off in interoperability: your internal data model is compatible with public sharing, peer exchange, and most commercial vendors. Even if your internal storage uses a custom schema, expose STIX-compatible endpoints for sharing where appropriate.
Internal Telemetry as a First-Class IOC Source
Many SOCs treat internal telemetry as a consumer of IOCs rather than a producer. This undervalues internal data dramatically. A confirmed-malicious hash observed during incident response, a C2 domain extracted from EDR beacon analysis, a phishing URL reported by a user and confirmed—these are high-confidence IOCs that belong in your pipeline immediately.
Internal IOCs often have higher confidence than many external feeds because they come with ground truth. Feed them back into detection pipelines and share them (subject to approval) with peer communities to strengthen collective defense.
Feedback Loops: Measuring Pipeline Value
A healthy pipeline is instrumented with feedback:
- Detection outcomes: Track how often each source’s indicators produce true positives.
- False positive rates: Feed analyst verdicts back into source confidence.
- Coverage metrics: How many confirmed incidents had prior IOC coverage?
- Timeliness: How fast do indicators move from source to distribution?
- Source ROI: Which feeds justify their cost by volume of actionable indicators?
Feeds that consistently underperform should be trimmed; feeds that consistently produce value deserve deeper integration. Without feedback, feed portfolios accumulate indefinitely and cost outpaces benefit.
Common IOC Pipeline Pitfalls
Recurring failure patterns to avoid:
- All IOCs treated equally: Without confidence and relevance scoring, pipelines flood controls with low-signal data.
- Stale indicators left in place: Expired IOCs cause false positives that erode analyst trust.
- No normalization: Duplicates and near-duplicates pollute dashboards and metrics.
- Ignoring enrichment failures: Silent degradation when enrichment sources time out leads to under-contextualized indicators downstream.
- No feedback instrumentation: The pipeline cannot improve what it does not measure.
- Overlooking internal telemetry: External feeds alone miss the highest-confidence signals generated by your own SOC.
Scaling the Pipeline
As volume grows, pipelines face engineering challenges:
- Throughput: Parallelize enrichment and distribution; use message queues for decoupling.
- Storage: Time-series databases for indicator observations, relational stores for indicator metadata, key-value stores for caches.
- Search: Index indicators for fast retrieval during incident response pivots.
- Resilience: Graceful degradation when a source or enrichment provider is unavailable.
- Security of the pipeline itself: The IOC database is itself sensitive; protect it as a crown jewel.
Mid-size SOCs often reach these limits before they expected. Designing with scale in mind from the beginning pays off as the feed portfolio grows.
Integration With the Wider CTI Program
IOC pipelines are the tactical layer of a broader cyber threat intelligence program. Operational analysts feed the pipeline with campaign-derived indicators; strategic analysts use the pipeline’s telemetry to understand which campaigns are active against the environment. Good pipelines make it trivial to answer questions like:
- “Which indicators have fired in our environment in the last 30 days, and what campaigns are they associated with?”
- “Which detection rules depend on which feed sources, and what would we lose if a source were discontinued?”
- “How quickly did we block a newly disclosed IOC after it appeared in our feeds?”
These are operational metrics that executives, auditors, and incident responders all benefit from.
The Role of Infrastructure Reputation Providers
Dedicated infrastructure reputation services such as isMalicious are often the single most impactful enrichment source in an IOC pipeline. They aggregate data from many underlying sources and deliver normalized reputation in real time via API. For every ingested IP, domain, or URL, a reputation query adds critical context—confidence boost when it corroborates malicious status, confidence tempering when it indicates benign use.
This kind of dedicated infrastructure reputation complements multi-purpose threat intelligence platforms. It excels specifically at the domain/IP/URL layer that tactical IOC pipelines depend on most.
Conclusion
IOC pipelines are security engineering work, not spreadsheet work. Building one that reliably ingests, normalizes, enriches, scores, distributes, and retires indicators is an investment that pays off across detection, response, and threat hunting. Pair diverse ingestion with disciplined validation, multi-source enrichment, honest scoring, and rigorous lifecycle management, and your SOC gains a quiet but powerful backbone for tactical threat intelligence.
Leverage standards like STIX and TAXII for interoperability. Treat internal telemetry as a first-class source. Integrate dedicated reputation services like isMalicious to add real-time infrastructure context to every indicator. Measure outcomes and tune aggressively. The organizations with the quietest, most boring IOC pipelines often detect fastest, respond soonest, and tell the clearest stories to leadership after every incident.
Frequently asked questions
- What is an IOC pipeline?
- An IOC pipeline is a data engineering system that ingests indicators of compromise (domains, IPs, URLs, file hashes, email addresses) from many sources, normalizes and enriches them, scores their confidence and relevance, and distributes them to security controls like firewalls, EDR platforms, SIEMs, and detection rules.
- Do I need a threat intelligence platform (TIP) to run an IOC pipeline?
- Not necessarily. Small teams can run effective IOC pipelines using scripting, a database, and existing SIEM or SOAR integrations. A dedicated TIP becomes valuable when the volume, number of sources, and sharing requirements justify the investment—typically in mid-size and larger SOCs.
- How long should IOCs stay active in detection rules?
- It depends on indicator type and context. Domain and IP indicators often need aggressive expiration (days to weeks) because infrastructure rotates rapidly; file hashes can remain useful for years because they identify specific payloads. Your pipeline should assign TTLs based on source confidence, indicator type, and observed activity.
Related articles
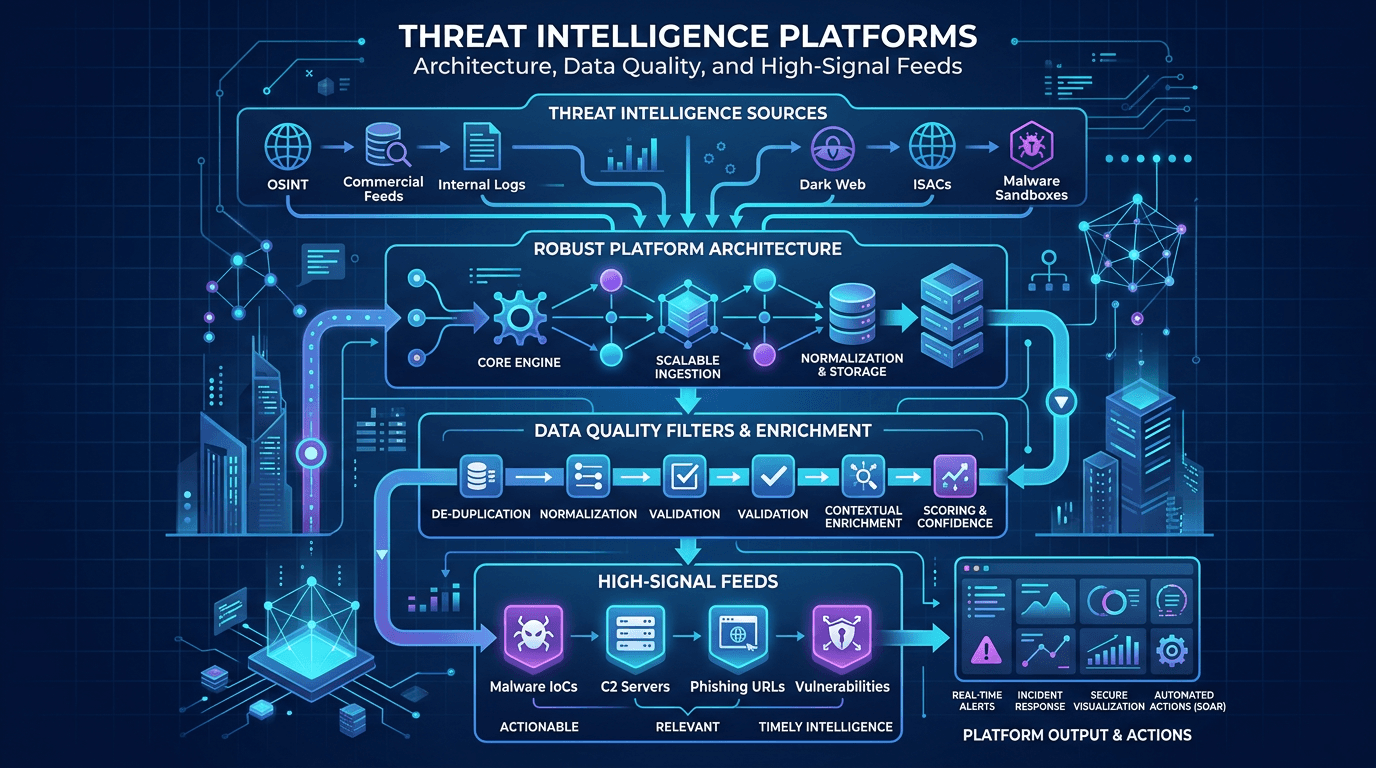 Apr 26, 2026Threat Intelligence Platforms: Architecture, Data Quality, and High-Signal Feeds
Apr 26, 2026Threat Intelligence Platforms: Architecture, Data Quality, and High-Signal FeedsDesign TIPs and intel pipelines that scale: normalization, confidence scoring, deduplication, API-first delivery, and how to pair platform investments with analyst workflows.
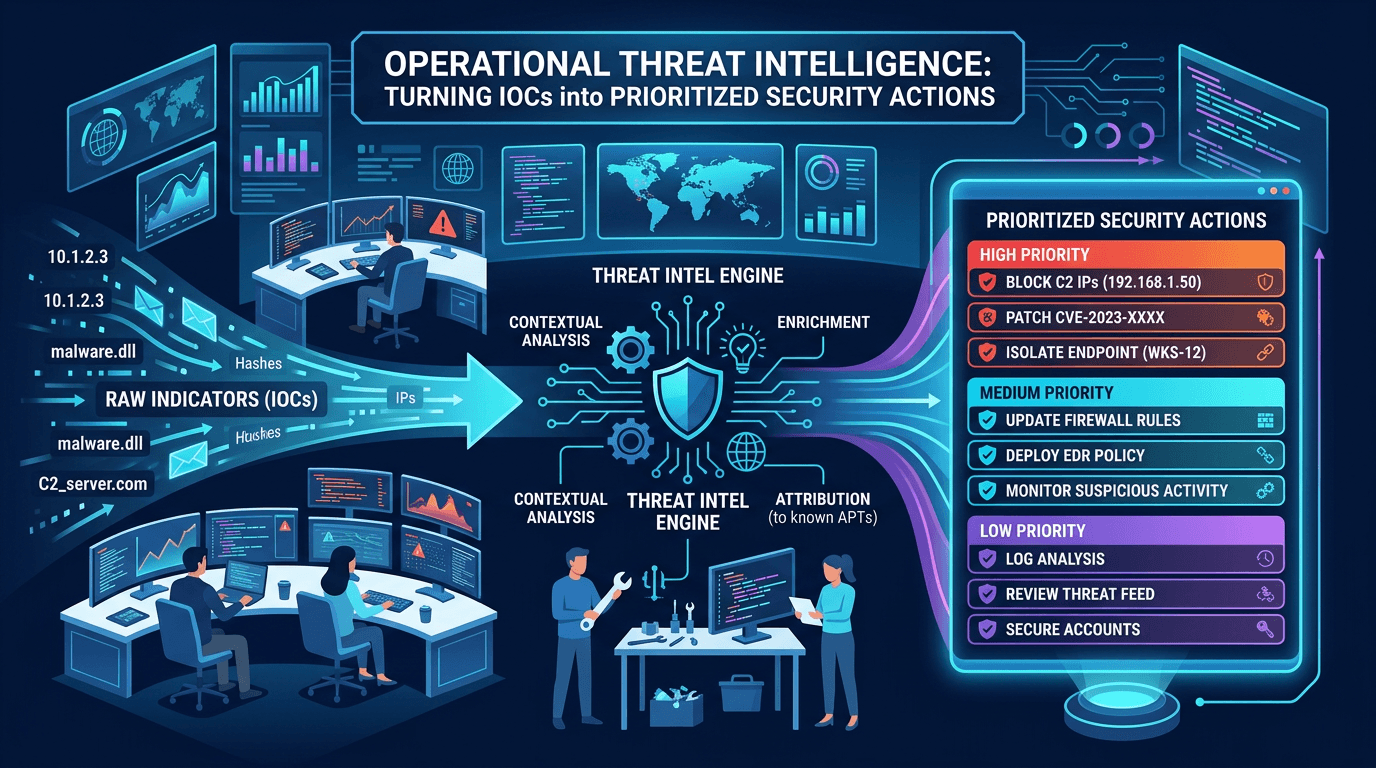 Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security ActionsDefine operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
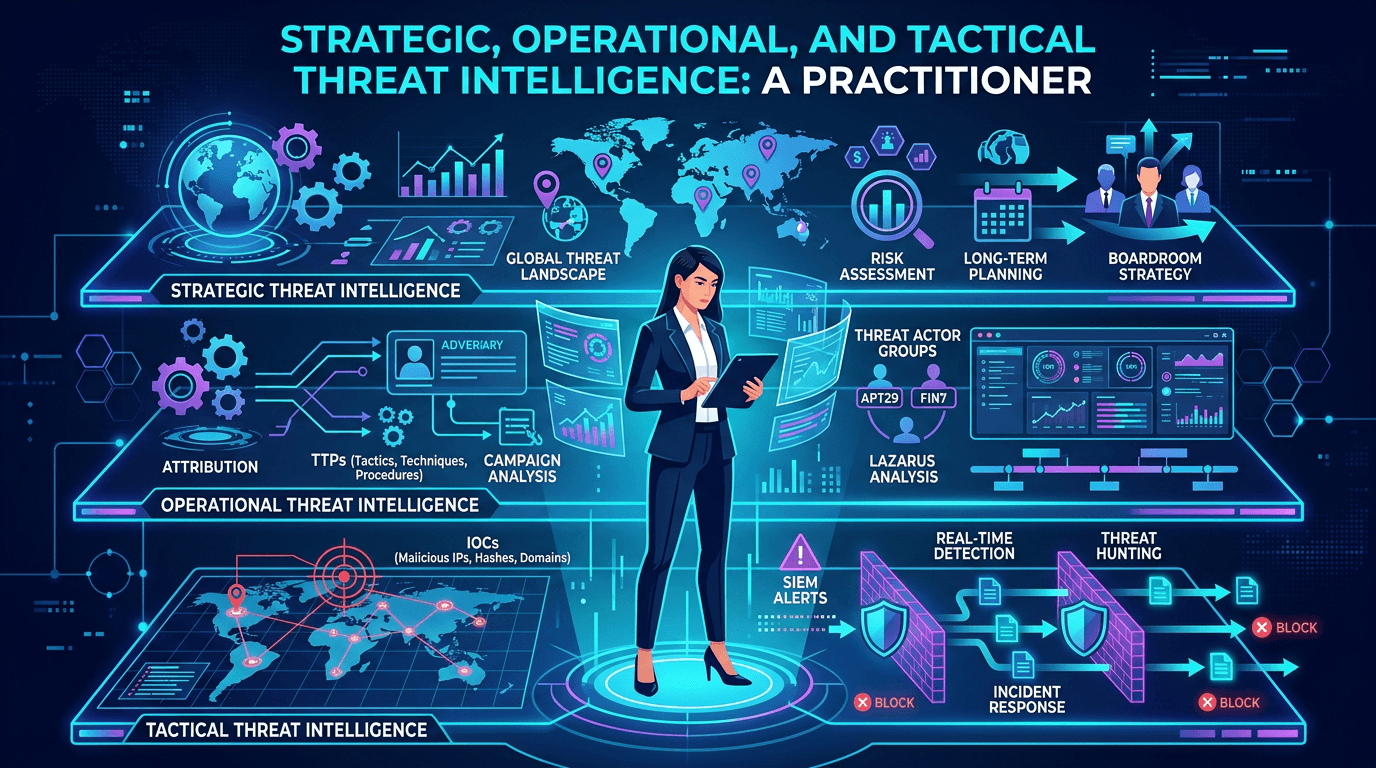 Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker