IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROI
An indicator without context is a ticket without an owner. Learn how IOC enrichment APIs work, which fields SOC teams need at each tier, and how to wire them into case management without building a data swamp.
Short answer: An IOC enrichment API turns bare indicators into decisions: who owns it, whether it is widely reported as abuse, and what related infrastructure suggests follow-on hunting. The security win comes from tiered enrichment—only enough data for the decision at hand, delivered fast enough to stay ahead of the queue.
Why Raw IOCs Create Expensive Work
A firewall block or a SIEM match tells you something happened. It does not tell you whether the IP was a one-off drive-by, a shared host with occasional abuse, a bulletproof hoster, or a stolen cloud VM spinning up and down. Without enrichment, L1 has two bad choices: over-block (and burn credibility with the business) or under-react (and miss real intrusions).
Enrichment is not "more data" for its own sake. It is the minimum structured story that lets an analyst pick the next action: open a case, request host isolation, notify fraud, or close as benign.
The Enrichment Data Model: What to Ask For
Enrichment services vary widely. A robust API usually combines:
- Entity classification (IP vs domain vs URL vs hash) and normalization (punycode domains, defanged URLs)
- Reputation and prevalence (how many sources flag it, with diversity—not just a single list)
- Network context (ASN, hosting vs residential, proxy/VPN/Tor hints, geo at city/country level)
- Domain lifecycle (creation date, registrar, name servers) when the observable is a hostname
- Linkage to related infrastructure (sibling domains, shared cert fingerprints, parents in passive DNS) as discussed in malicious domain and IP reputation fundamentals
- Optional deep sections (malware tags, OTX context, or CVE hints when the platform exposes them) without forcing every consumer to pay the latency and storage cost of "full" enrichment every time
For a broader discussion of quality vs quantity in your stack, see threat intelligence platform architecture, data quality, and feed selection.
Tiered Enrichment: A Pattern That Scales
Tier 0 — inline automation
Use when latency matters: WAF, login, payments, and API gateways. You typically need: risk score, category label, a boolean allow/deny, and a short reason code. Favor vendors that are honest about limitations; see our article on risk scoring and false positives in reputation systems.
Tier 1 — SOC L1
SIEM/EDR notables and phishing inboxes. Add ASN, whois/age for domains, and "first seen/last seen" if available. Keep output narrow enough to show in a ticket summary.
Tier 2 — threat hunting and IR
Here you can justify passive DNS, related hashes, and infrastructure clustering, especially when you suspect C2 or lookalike phishing. Pair operational guidance from operational threat intelligence: IOC prioritization with technical drill-downs in C2 and malware C2 tradecraft when investigating callback infrastructure.
Wiring APIs Without Splintering the Truth
Single source of normalized fields inside your case system matters. If every tool names the same field differently, your SOAR will concatenate chaos.
Practical approach:
- Map vendor fields to a STIX-like internal schema (even if you are not using STIX transport end-to-end)
- Store a provenance object: which provider, when fetched, and confidence level
- Version your playbooks: enrich-on-create vs enrich-on-escalation
If you are building a pipeline, our walkthrough of operational IOC pipelines is a useful companion.
Enrichment in IR: Pair Hashes and Network
File-heavy teams often start with file hash reputation for incident response while network-heavy teams start with domain and IP check workflows. The most mature programs link both, because malware moves across stages: payload hash → C2 domain → exfil IP.
ROI You Can Defend in a Budget Review
- MTTR for phishing and malware tickets (hours → minutes for obvious abuse)
- False-positive cost in locked accounts, helpdesk time, and firewall churn
- Automation coverage: percentage of L1 triage with evidence attached before a human opens the ticket
A Week-One Integration Pattern for Engineering Teams
If you are a platform engineer, treat enrichment like any other high-volume dependency: SLOs, fallbacks, and idempotency.
- SLOs — define p50/p95 latency and error budget for the enrichment hop. A SOAR that blocks on a slow vendor is just a DDoS you built yourself.
- Idempotency — the same
sha256:…in five alerts should return one cached result per TTL window, not five vendor round trips. - Circuit breakers — when a provider fails, degrade to “escalate to human with partial context” instead of “drop the ticket in /dev/null”.
- Schema versioning — if you add a new field, keep backward compatibility in your
ti.enrichmentobject in SIEM. Analyst macros break silently when key names wobble.
Sample “compact record” (illustrative)
| Field | Example | Why store it? |
| ------------- | ---------------- | --------------------- |
| observable | 203.0.113.9 | Join key |
| verdict | suspicious | Triage |
| categories | c2, scanning | Story |
| sources | 8 distinct feeds | diversity > volume |
| enriched_at | ISO timestamp | Staleness / audit |
| asn | AS-EXAMPLE-1 | Context without drama |
Common Anti-Patterns in API Wiring
- Giant raw JSON in tickets that analysts never scroll through
- “Enrich on every log line” instead of first occurrence per case
- No TTL on cached context (you will fight yesterday’s war)
- Merging conflicting vendor categories without a priority table
How isMalicious Approaches the Problem
isMalicious is designed for fast entity reputation and enrichment for IPs, domains, URLs, and hashes, with a modern API and streaming options described at a high level in the threat API comparison for 2026. It is a strong building block for enrichment tiers where milliseconds and clarity matter, alongside—not instead of—your EDR, email gateway, and internal telemetry.
Try it: use the in-app IP / domain checker to validate a suspicious observable before you file the incident, then attach the output to the ticket for traceability.
Takeaway
IOC enrichment is not a luxury feature. It is the control loop that makes indicators actionable. Get the data model, tiering, and case-system mapping right, and you will not just "add threat intel"—you will shorten the distance between signal and decision.
Frequently asked questions
- What is IOC enrichment?
- IOC enrichment is the process of taking a raw indicator—such as an IP address, domain, URL, or file hash—and retrieving structured context: reputation scores, whois, passive DNS, linked malware families, and related infrastructure so analysts can decide faster whether it is malicious, suspicious, or benign in their environment.
- When should I call an enrichment API vs looking up a feed manually?
- Use APIs when you have volume: EDR/SIEM alerts, phishing triage, automated ticket creation, or user sign-up risk checks. Manual lookups do not scale past a handful of events per day and rarely produce auditable, repeatable evidence.
- What is the most common design mistake?
- Dumping every available field into your SIEM. That bloats licensing and drowns analysts. Enrich in tiers: minimal fields for L1, deeper correlation for L2, and full narrative only when opening an incident or IR case.
- How do I reduce false positives in enrichment-led workflows?
- Combine reputation with corroboration: time-windowed sightings, source diversity, and environment-specific scoping. Treat a single noisily labeled IP as a clue, not a conviction—especially for cloud and CDN-heavy networks.
- How does isMalicious support enrichment workflows?
- isMalicious exposes IP, domain, URL, and hash context through a fast API, suitable for SOAR, inline application checks, and research workflows, with a focus on aggregated list intelligence and high-speed lookups rather than a full malware detonation lab.
Related articles
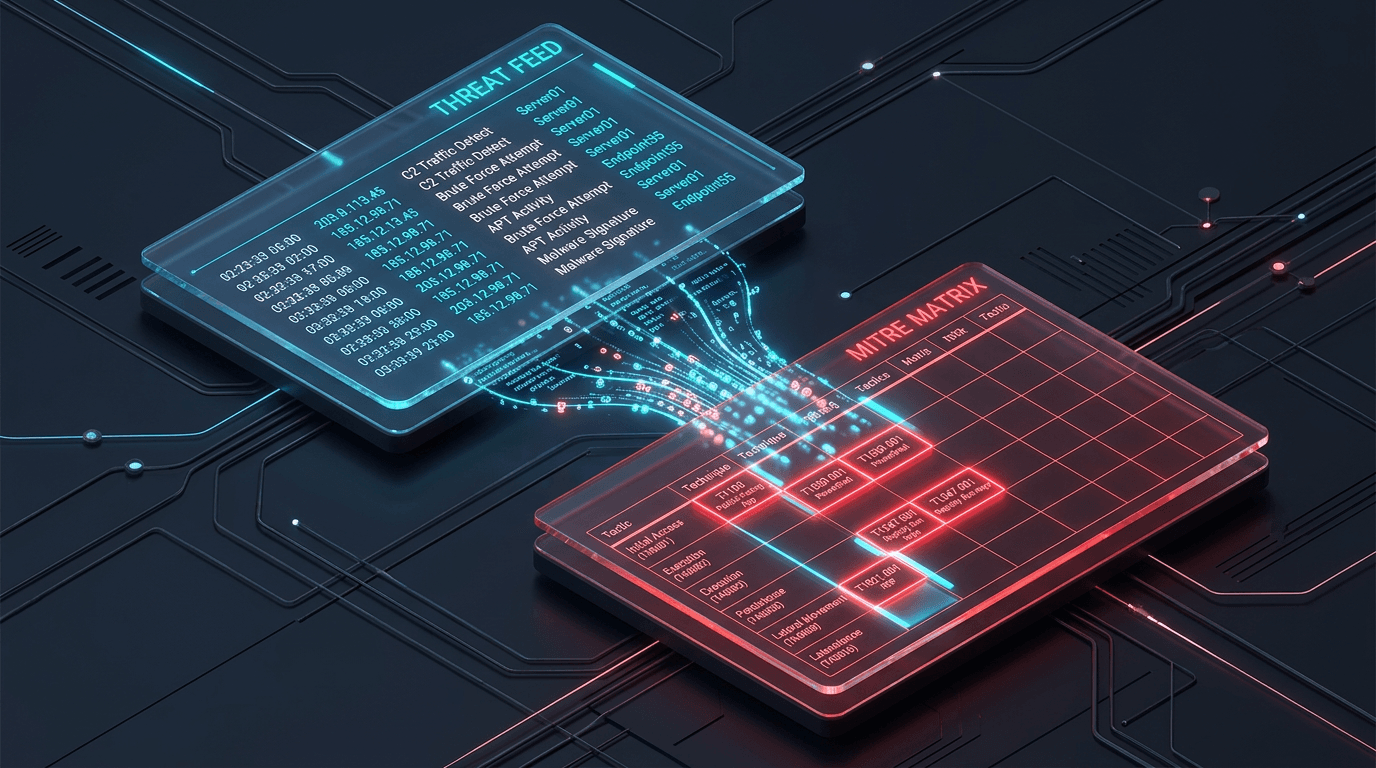
 Jun 4, 2026AI-Enabled Cyberattacks and MITRE ATT&CK: Turning New Threat Maps Into SOC Action
Jun 4, 2026AI-Enabled Cyberattacks and MITRE ATT&CK: Turning New Threat Maps Into SOC ActionAI-enabled threats are being mapped into ATT&CK language, but mapping is only useful when it drives enrichment, detection, triage, and response workflows.
 Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real Attacks
Jun 4, 2026SOC Alert Fatigue: How Threat Intelligence Reduces False Positives Without Hiding Real AttacksAlert fatigue is not a staffing problem alone. SOC teams need better evidence, source quality, confidence bands, and enrichment workflows that turn noisy alerts into defensible decisions.
 Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC EnrichmentA practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker