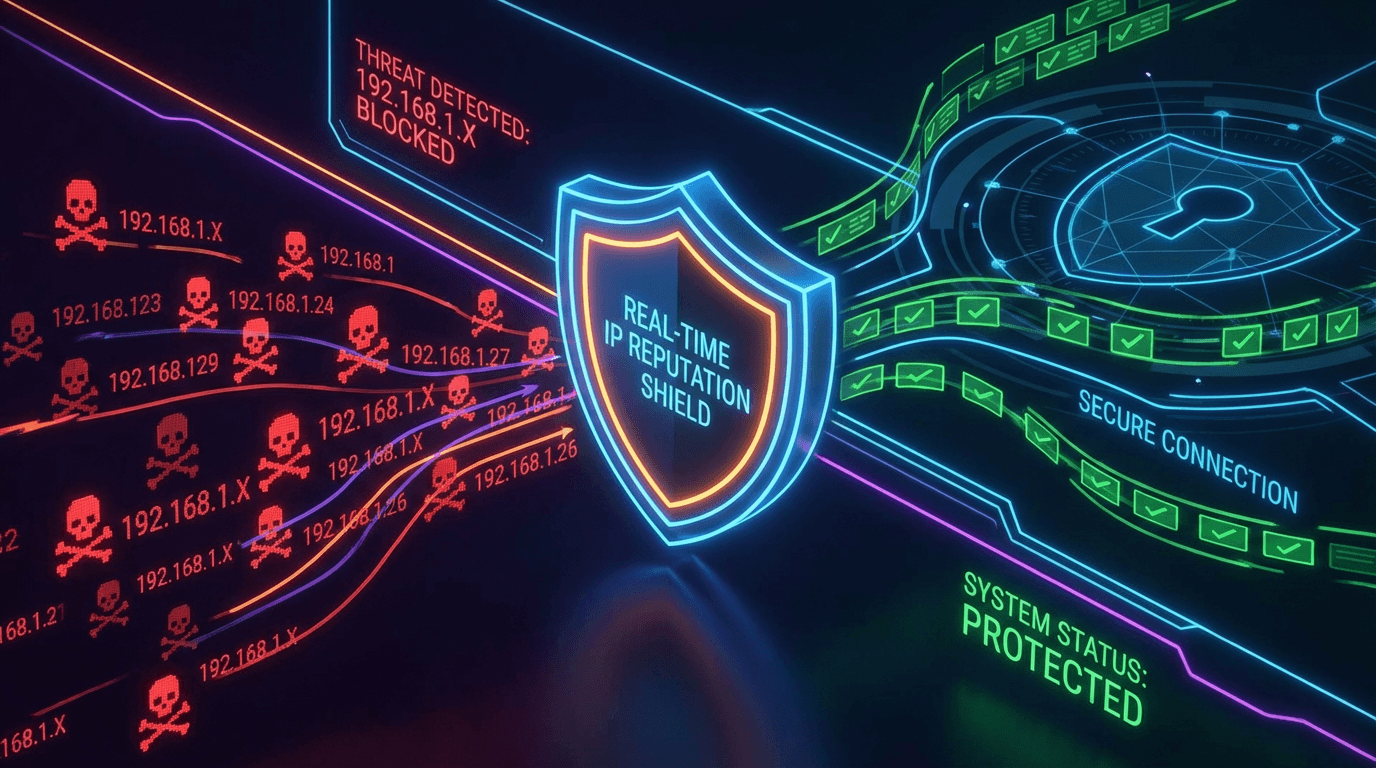
Real-Time IP Reputation Check: Stop Cyber Threats at the Network Edge
Real-time IP reputation checks give you the power to identify and block malicious actors the moment they connect to your systems. Discover how to implement automated threat detection that works at machine speed, not analyst speed.
Attackers move fast. From the moment a compromised server is repurposed as a credential-stuffing launcher, to the instant a botnet node begins hammering your login endpoint, the window between "threat active" and "breach complete" is measured in minutes. Security controls that update nightly, weekly, or even hourly cannot keep pace. Real-time IP reputation checks can.
Unlike traditional blocklists that are distributed as static files and refreshed on a schedule, real-time IP reputation APIs query continuously updated threat intelligence databases at the moment each connection arrives. The result is a security layer that operates at machine speed — capable of recognizing and blocking a newly emerging threat within minutes of its first detection anywhere in the global threat intelligence network.
Why "Real-Time" Matters in IP Threat Detection
The distinction between scheduled and real-time threat intelligence seems subtle until you face an active attack campaign.
Consider a credential stuffing operation targeting financial services applications. The attacker rotates through a pool of 50,000 IP addresses, making a handful of requests from each before moving to the next. A blocklist updated nightly might flag addresses already burned and discarded by the attacker. Real-time intelligence that reflects the global attack surface as it evolves can identify IPs in the active rotation — addresses that appeared in attack logs at other organizations minutes ago — and block them before they make their first attempt against your systems.
The same principle applies to phishing infrastructure takedowns, botnet disruptions, and vulnerability exploitation campaigns. Threat intelligence is most valuable when it is freshest.
The Architecture of Real-Time IP Reputation
A real-time IP reputation system has three essential components:
Continuous Data Ingestion
Threat data must flow in from multiple sources without interruption. Effective platforms ingest from honeypots that capture scanner activity in real time, from automated phishing report systems, from abuse reporting APIs maintained by hosting providers, from passive DNS monitors that detect when IPs begin resolving to new and suspicious domains, and from partner data-sharing arrangements with ISPs, government CERTs, and security vendors.
The ingestion pipeline normalizes, deduplicates, and scores incoming indicators so that query results reflect the full aggregated picture, not just one data source.
Low-Latency Query Infrastructure
Real-time checks are only valuable if they return results fast enough to be used at connection time. A reputation check that takes two seconds does not belong in a login handler that should respond within 200 milliseconds. Purpose-built threat intelligence platforms use in-memory caching, globally distributed query nodes, and highly optimized data structures to return reputation data in under 100 milliseconds from anywhere in the world.
Actionable Scoring and Classification
Raw threat data is not actionable at machine speed. The query response must include a clear risk score, specific abuse categories, and enough context for automated decision-making — without requiring an analyst to interpret the result before action is taken. A score of 95 with categories botnet, credential-stuffing, and brute-force gives an authentication middleware exactly what it needs to make an access control decision automatically.
Where to Apply Real-Time IP Checks
At the Load Balancer or API Gateway
The earliest point where a real-time reputation check can operate is at the network edge — the load balancer, CDN edge node, or API gateway that receives every inbound connection. Dropping a malicious IP here costs nothing in application resources. It never reaches your servers, never touches your database, and never generates an authentication event.
Most modern API gateways support plugin architectures that make it straightforward to add reputation checks as middleware. The check runs before routing, before authentication, before any business logic executes.
At Authentication Entry Points
Login, registration, password reset, and MFA enrollment are the highest-value targets for automated attacks. Every one of these flows should check the connecting IP in real time. The response can be graduated based on the risk score:
- Score 0–30: Allow normally
- Score 31–60: Log for monitoring, optionally trigger soft CAPTCHA
- Score 61–80: Require MFA regardless of account settings, flag for analyst review
- Score 81–100: Block with generic error, alert security team, log full request details
This graduated response prevents legitimate users from being locked out due to shared IP infrastructure while creating meaningful friction for automated attack tools.
At Payment and High-Value Transaction Endpoints
Fraud operations often originate from IP ranges with elevated reputation risk. Adding a real-time IP check to checkout flows, wire transfer initiations, or high-value account changes provides an additional fraud signal that complements traditional fraud detection systems based on transaction patterns and device fingerprinting.
In Content Submission and API Abuse Prevention
Public comment forms, API endpoints that accept user content, and webhook receivers are targets for spam, scraping, and abuse. Real-time IP reputation provides a fast, low-friction way to apply graduated rate limiting or content review based on the submitter's risk profile.
Implementing Real-Time IP Checks: A Practical Guide
Step 1: Choose a Threat Intelligence Provider
Select a provider that offers:
- Sub-100 ms response times globally
- Continuous data refresh (not scheduled batch updates)
- Multiple threat categories and confidence scores
- IPv4 and IPv6 support
- High availability with documented uptime SLAs
Step 2: Integrate at the Right Layer
Determine which layer in your stack is the optimal integration point. For most web applications, integrating at the authentication middleware layer offers the best balance of protection and implementation simplicity. For high-traffic applications, consider a network-level integration at the reverse proxy or API gateway.
Here is a conceptual example of how a real-time IP check integrates into a Node.js authentication handler:
async function authMiddleware(req, res, next) {
const clientIp = req.headers['x-forwarded-for']?.split(',')[0] || req.socket.remoteAddress;
const reputation = await checkIpReputation(clientIp);
if (reputation.score >= 81) {
return res.status(403).json({ error: 'Access denied' });
}
if (reputation.score >= 61) {
req.requiresMfa = true;
}
req.ipRiskScore = reputation.score;
req.ipCategories = reputation.categories;
next();
}
Step 3: Define Response Policies
Document your response thresholds and the actions triggered at each tier. Review these policies quarterly and after any significant security incident to ensure they remain calibrated to your threat environment.
Step 4: Log Everything
Store IP reputation scores alongside every authentication event, transaction, and significant application action. This data is invaluable for post-incident analysis, trend monitoring, and threshold calibration. A pattern of medium-risk scores that don't individually trigger alerts often reveals a sophisticated, slow-moving attack when analyzed in aggregate.
Step 5: Build Feedback Loops
If your application generates its own abuse signals — failed logins, anomalous API usage, confirmed fraud — consider contributing that data back to threat intelligence platforms through their reporting APIs. This improves the quality of data for the entire community while enhancing your own intelligence coverage.
Handling Edge Cases and False Positives
Real-time reputation systems occasionally flag legitimate users. Common sources of false positives include:
Corporate NAT and proxies: Hundreds of legitimate users sharing a single egress IP that was previously abused by one of them. Mitigate by using graduated responses rather than hard blocks, and by providing a support escalation path.
VPN and privacy services: Many legitimate users, especially security-conscious professionals and journalists, use VPN services that appear in threat feeds. Distinguish between clearly malicious VPN infrastructure and privacy-focused consumer services when setting block thresholds.
Cloud provider IP ranges: Developers, CI/CD systems, and legitimate automation often originate from AWS, Google Cloud, or Azure IP ranges. These may appear elevated in certain threat categories. Context matters — a developer registering a new account from a cloud IP is different from a bulk account registration script.
The solution is always the same: use reputation data as a signal, not an absolute verdict. Combine it with behavioral context, account history, and user-provided verification to make access decisions that protect against real threats without unnecessarily impeding legitimate users.
The Compounding Value of Real-Time Protection
Every blocked malicious IP is more than a stopped attack. It is data. Patterns in the IPs attempting to compromise your systems reveal intelligence about the threat actors targeting your industry, the attack tools they use, and the infrastructure they rely on. This intelligence feeds back into improved defenses, better-tuned thresholds, and more accurate risk models.
Organizations that implement real-time IP reputation checks consistently report significant reductions in credential stuffing volume, bot-driven form submissions, and fraudulent account creations — not because they block every attack, but because the friction added to each attempt makes mass automated attacks economically unviable.
Start with a real-time IP reputation check powered by IsMalicious and see exactly what is knocking on your doors.
Frequently asked questions
- What is a real-time IP reputation check?
- A real-time IP reputation check is an automated query against threat intelligence databases at the moment a connection is established or a request is received. Unlike batch-mode blacklist updates that run daily or hourly, real-time checks query continuously updated data so that an IP flagged for abuse minutes ago is blocked on the very next connection attempt.
- How fast are real-time IP reputation API responses?
- Well-optimized threat intelligence APIs return results in 20–150 milliseconds depending on network conditions and the platform architecture. This latency is imperceptible to users in interactive applications and trivial compared to backend processing time in most web services. IsMalicious is designed specifically for sub-100 ms response times to support real-time integration.
- What happens when a legitimate user is flagged by an IP reputation check?
- IP reputation checks should apply a graduated response rather than a hard block. For medium-risk scores, trigger additional authentication factors (MFA, email verification) rather than denying access outright. Reserve outright blocking for high-confidence malicious IPs. Provide a way for legitimate users to appeal or verify their identity if they are incorrectly flagged.
Related articles
 Apr 7, 2026IP Lookup for Cyber Threat Detection: A Complete Security Guide
Apr 7, 2026IP Lookup for Cyber Threat Detection: A Complete Security GuideLearn how IP lookup works as a frontline defense against cyber threats. Discover how to use IP reputation data, threat intelligence feeds, and automated checks to block malicious actors before they reach your systems.
 Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?
Mar 15, 2026The Dark Web vs. Deep Web: Where Do Cyber Threats Hide?Confused by the Dark Web and Deep Web? We explain the difference and where cyber threats like stolen credentials and malware actually live.
 Mar 6, 2026Space Systems Cyber Threats: Securing the Final Frontier
Mar 6, 2026Space Systems Cyber Threats: Securing the Final FrontierAs space becomes accessible, it becomes a target. From satellite hijacking to ground station jamming, we analyze the unique threats to orbital assets and how threat intelligence secures the new space race.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker