IP Lookup for Cyber Threat Detection: A Complete Security Guide
Learn how IP lookup works as a frontline defense against cyber threats. Discover how to use IP reputation data, threat intelligence feeds, and automated checks to block malicious actors before they reach your systems.
A single malicious IP address connecting to your infrastructure can be the first step in a breach that costs millions. Yet identifying that IP — before it exfiltrates data, installs ransomware, or harvests credentials — requires more than a firewall rule. It requires intelligence. IP lookup for cyber threat detection is the practice of querying real-time reputation databases to classify every connecting address as trustworthy, suspicious, or outright malicious, and acting on that classification automatically.
This guide explains how IP lookup works, what data sources power it, and how security teams and developers can embed it into their defenses to stop threats at the very first point of contact.
What Is IP Lookup in a Security Context?
When most people hear "IP lookup" they think of finding the geographic location of an address. In security, the term means something deeper: querying aggregated threat intelligence to determine an IP's behavioral history and current risk level.
A security-oriented IP lookup returns signals such as:
- Abuse categories: spam sender, botnet node, scanner, DDoS source, brute-force attacker
- Blocklist presence: appearance on industry blocklists like Spamhaus, SORBS, or Emerging Threats
- Autonomous System Number (ASN) risk: whether the IP belongs to a hosting provider, residential ISP, Tor exit node, or VPN service known for abuse
- Geolocation and country risk: origin country and whether it aligns with your expected user base
- First-seen and last-seen timestamps: how long the IP has been observed in threat feeds
- Confidence scores: an aggregated risk rating from 0 to 100 that distils all signals into a single actionable metric
These signals collectively answer one question: should I trust this connection?
Why IP Lookup Is Your First Line of Defense
Attackers do not materialize out of thin air. They operate from infrastructure — servers, compromised machines, rented proxies — that leaves a trail across the internet. That trail is captured in threat intelligence feeds updated continuously by security researchers, honeypot operators, and automated detection systems worldwide.
By the time an attacker connects to your application, there is a high probability their source IP is already flagged somewhere. IP lookup lets you act on that intelligence in real time, before the attacker has a chance to attempt a login, submit a form, or probe your API.
Consider the economics: a blocklist check at login adds roughly one to five milliseconds of latency but eliminates entire categories of attack — credential stuffing from botnet nodes, account enumeration from known scanner IPs, fraud attempts from high-risk VPN ranges. No machine learning model, no behavioral analysis engine, and no endpoint detection tool can match the cost-effectiveness of a simple "is this IP malicious?" check at the front door.
Key Data Sources Behind IP Threat Intelligence
The quality of an IP lookup is directly determined by the breadth and freshness of its underlying data. Leading platforms aggregate from multiple source categories:
Honeypots and Sinkholes
Security organizations operate servers with no legitimate users. Any connection to these systems is, by definition, malicious or unwanted. Honeypots capture scanner IPs, botnet beaconing addresses, and exploit-attempt sources in real time, feeding that data directly into threat databases.
Abuse Reporting Networks
Platforms like AbuseIPDB and similar community-driven services let system administrators report IPs that attacked them. A single IP generating thousands of reports across unrelated organizations is a strong indicator of malicious intent, regardless of what it claims to be.
Passive DNS and BGP Data
Passive DNS records which IP addresses resolve to which domains over time. When an IP hosts known phishing domains, malware distribution sites, or command-and-control servers, that association persists in passive DNS even after the domain is taken down. BGP routing data reveals when IP blocks change hands rapidly — a common technique used to launder reputation.
Commercial and Open Threat Feeds
Dozens of security vendors, national CERTs, and research organizations publish threat intelligence feeds. Leading platforms aggregate these into a single queryable dataset, normalizing formats and removing duplicates so that a single API call checks against hundreds of sources simultaneously.
Embedding IP Lookup into Your Security Stack
IP lookup is not a product you deploy once and forget. It is a capability you embed at every decision point where untrusted input enters your system.
Network Perimeter and Firewall
At the outermost layer, block or rate-limit connections from IPs on high-confidence blocklists. Many next-generation firewalls and CDNs support automatic threat intelligence feed integration. This stops volumetric attacks — DDoS, mass scanning — before they consume any application resources.
Authentication Endpoints
Login and registration are the highest-value targets for credential stuffing and account takeover campaigns. Check the connecting IP at every authentication event. A high-risk score should trigger step-up authentication (MFA prompt), CAPTCHA, or temporary lockout rather than an outright block — legitimate users occasionally connect through shared or flagged IPs.
API Rate Limiting and Fraud Prevention
For public APIs, IP reputation data informs adaptive rate limiting. A clean residential IP might receive a generous request quota while a known scraper IP gets a much tighter limit. Payment processing and transaction endpoints can use IP risk scores as one signal in a fraud scoring model.
Security Information and Event Management (SIEM)
Enriching SIEM log ingestion with IP reputation data transforms raw log lines into actionable intelligence. An authentication failure from a residential IP is noise; the same failure from a known botnet node is a critical alert. Automated enrichment at ingestion time means analysts start their investigation with context, not raw data.
Interpreting IP Lookup Results
Not every flagged IP represents an immediate threat, and not every clean IP is trustworthy. Effective use of IP lookup requires nuance.
High confidence, known bad: IPs scoring 80–100 on most platforms, appearing on multiple feeds, with recent abuse timestamps. These warrant automatic blocking or strong friction at sensitive endpoints.
Medium confidence, elevated risk: Scores in the 40–79 range, appearing on one or two feeds, or belonging to high-risk ASNs without specific abuse records. Apply additional verification — MFA, behavioral monitoring, shorter session lifetimes.
Low confidence, clean: Scores below 40, absent from known feed categories. Treat as trusted but continue behavioral monitoring, since IP reputation data reflects the past and attackers frequently rotate infrastructure.
Shared IP concerns: Corporate NAT gateways, university networks, and mobile carrier CG-NAT pools can cause legitimate users to share an IP with malicious actors. Risk scores from these ranges should inform friction, not automatic blocking.
How IsMalicious Makes IP Lookup Actionable
IsMalicious aggregates threat data from dozens of sources into a single, low-latency API. A query against any IPv4 or IPv6 address returns a risk score, abuse categories, ASN context, and blocklist presence in a single JSON response — typically in under 100 milliseconds.
The platform continuously refreshes its data, so an IP flagged for a botnet campaign this morning appears in query results within minutes. For security teams running manual investigations, the web interface provides the same data through a point-and-click lookup that requires no API key or coding.
Integration into existing workflows is straightforward. Developers can add an IP lookup call to authentication middleware in under ten lines of code, and the results feed directly into access control decisions, alert pipelines, or fraud scoring models.
Building a Threat Detection Workflow Around IP Lookup
The most effective implementations treat IP lookup as the first gate in a layered detection strategy:
- Check at the edge: Query IP reputation at the CDN or load balancer layer to drop high-confidence malicious traffic before it reaches application servers.
- Enrich at authentication: On every login or registration event, retrieve the full IP risk profile and factor it into access decisions.
- Log and correlate: Store IP risk scores alongside authentication events in your SIEM. Correlate risk spikes with unusual activity patterns — multiple failed logins from escalating-risk IPs often precede a successful account takeover.
- Automate response: Use risk score thresholds to trigger automated responses — rate limiting, MFA challenges, account holds — without requiring analyst intervention for every event.
- Review and tune: Regularly review false positives (legitimate users blocked) and false negatives (attacks that slipped through) to refine thresholds and response policies.
Cyber threats evolve constantly, but the fundamental principle does not change: the less time a malicious IP spends inside your perimeter, the less damage it can do. IP lookup is how you identify it at the gate.
Start protecting your systems today with a free IP reputation check — no account required, results in seconds.
Frequently asked questions
- What is an IP lookup and why does it matter for security?
- An IP lookup is the process of querying threat intelligence databases to determine whether an IP address is associated with malicious activity such as spam, botnets, DDoS attacks, or scanning campaigns. It matters because blocking or flagging malicious IPs before they interact with your systems is one of the cheapest and most effective security controls available.
- How accurate is IP reputation data?
- Accuracy depends on the breadth and freshness of the underlying threat feeds. Best-in-class providers like IsMalicious aggregate data from dozens of sources — honeypots, abuse reports, blocklists, and passive DNS — and refresh scores continuously. No single feed is perfect, so always combine IP reputation with contextual signals such as geolocation, ASN type, and behavioral anomalies.
- Can I automate IP lookup checks in my application?
- Yes. Every major threat intelligence platform exposes a REST API that you can call at registration, login, or any transaction boundary. IsMalicious provides a low-latency JSON API designed for real-time integration, with response times typically under 100 ms so checks do not noticeably slow user-facing flows.
Related articles
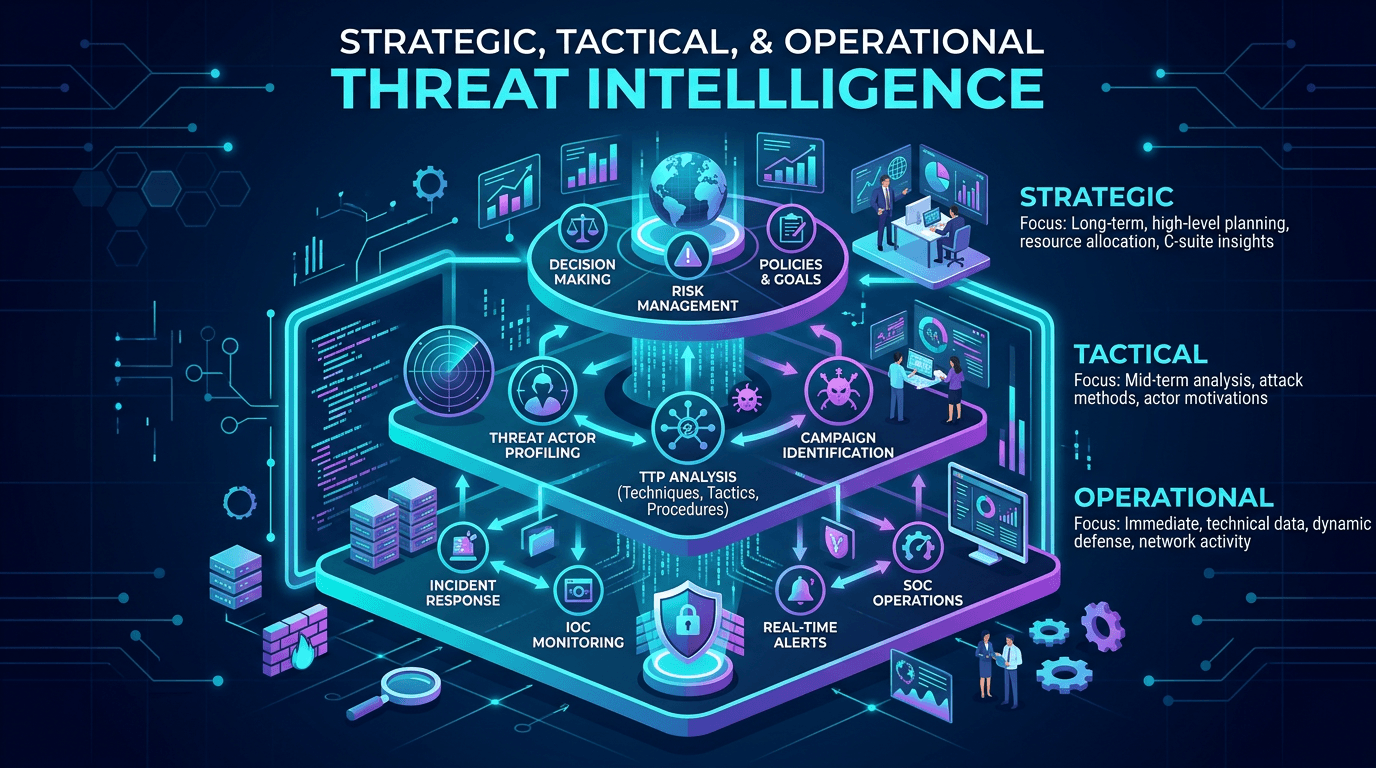 Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security Programs
Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security ProgramsAlign CTI outputs with audience needs: executive risk narratives, SOC-ready IOCs, and MITRE-mapped TTPs—plus governance models that keep intelligence timely and measurable.
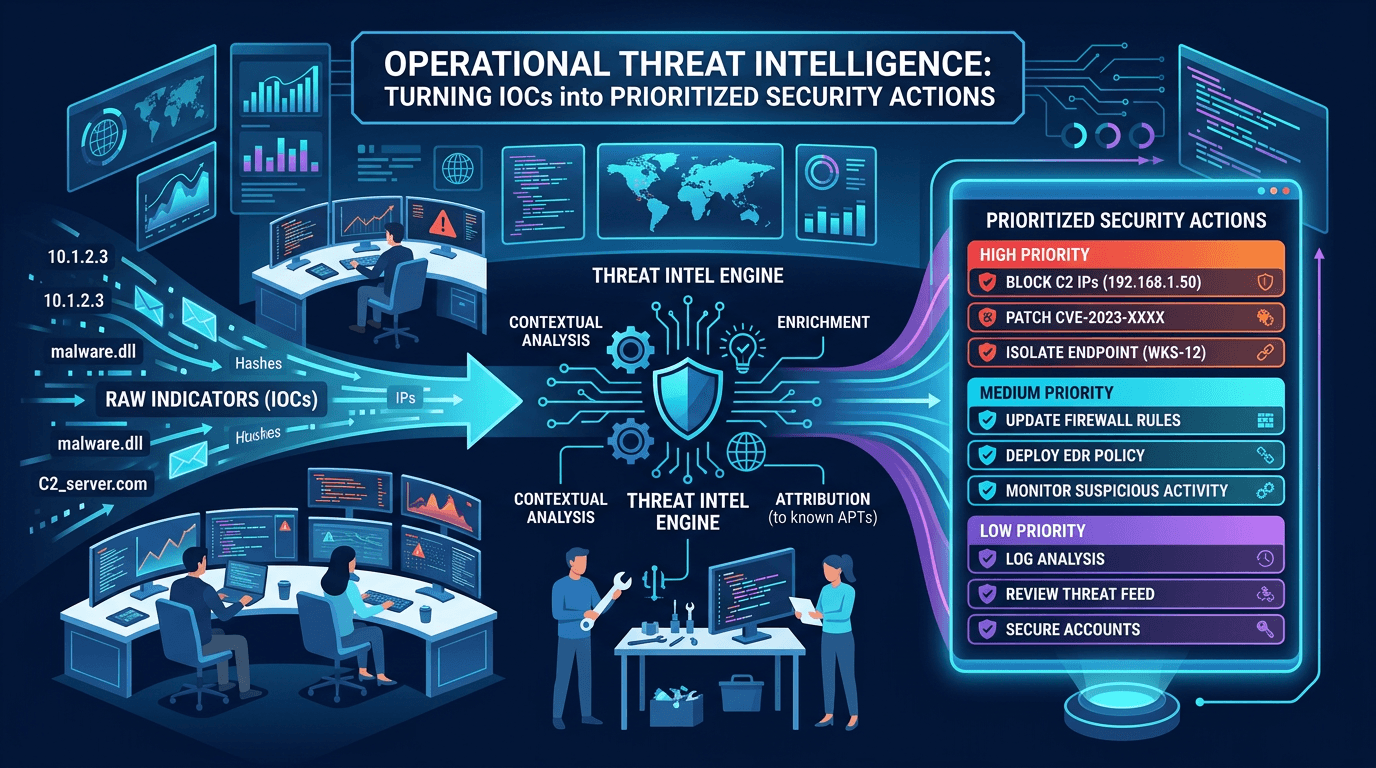 Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security ActionsDefine operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
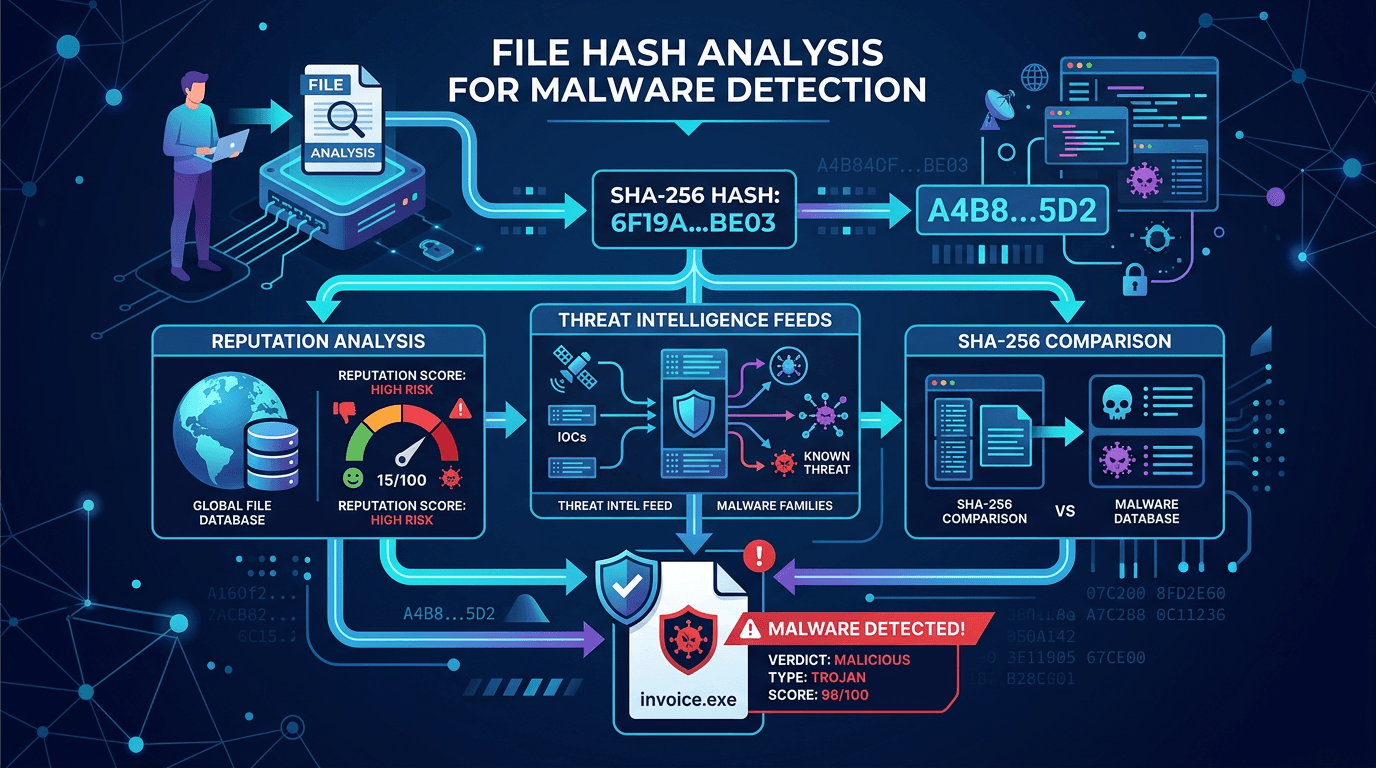 Apr 18, 2026File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel Workflows
Apr 18, 2026File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel WorkflowsLearn how cryptographic file hashes power malware identification, why SHA-256 dominates security tooling, and how to combine hash lookups with broader threat intelligence for fewer false positives.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker