File Hash Analysis for Malware Detection: SHA-256, Reputation, and Threat Intel Workflows
Learn how cryptographic file hashes power malware identification, why SHA-256 dominates security tooling, and how to combine hash lookups with broader threat intelligence for fewer false positives.
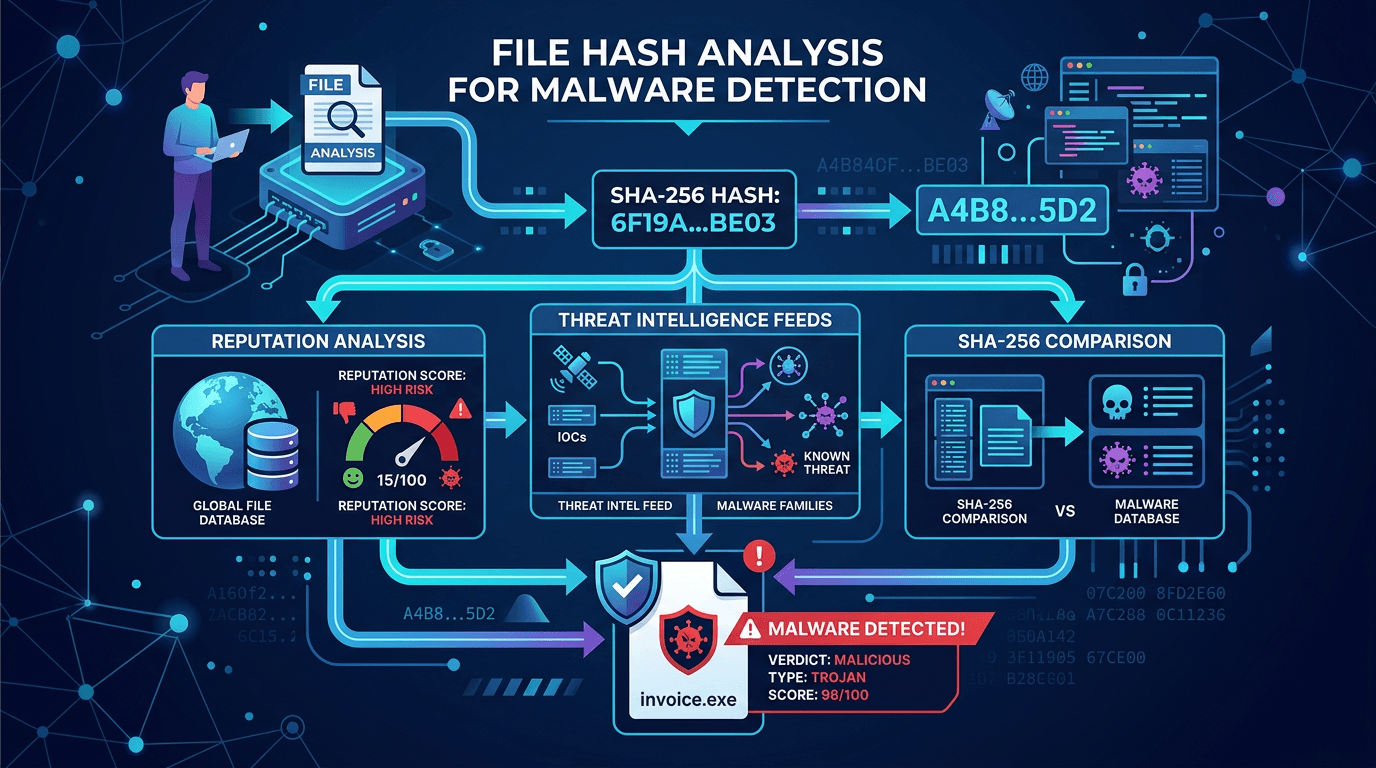
When security teams talk about a file hash, they usually mean a fixed-length fingerprint produced by a cryptographic hash function. That fingerprint lets you refer to a binary artifact—an executable, a script, a document macro, or a memory dump fragment—without storing the entire object in every log line. In defensive operations, file hash values become indicators of compromise (IOCs) you can share across SIEMs, EDR platforms, email gateways, and threat intelligence exchanges. This article explains how hash-based detection works in practice, why SHA-256 has become the de facto standard, and how to build workflows that scale without drowning analysts in noisy alerts.
What a File Hash Actually Represents
A cryptographic hash function takes an input of arbitrary size and outputs a string of fixed length. For SHA-256, that output is 256 bits, typically written as 64 hexadecimal characters. Changing even one bit of the input should produce a completely different hash output—a property that makes hashes useful for integrity checking and malware identification.
Importantly, the file hash is a derived label for a specific byte sequence. If an attacker recompiles malware with a trivial change, the hash changes. That polymorphism is why mature programs never rely on static hashes alone; they combine hash reputation with behavioral signals, certificate reputation, parent-child process relationships, and network indicators.
For SEO and documentation clarity, distinguish between:
- Cryptographic hashes (SHA-256, SHA-1, MD5) used for identification and integrity.
- Fuzzy hashing (ssdeep and similar) that can match similar-but-not-identical files—useful when malware variants share large code regions.
- TLS certificate fingerprints and domain reputation, which answer different questions than file identity.
MD5 and SHA-1: Legacy Context
Historically, MD5 and SHA-1 appeared everywhere in antivirus and incident response because they were fast and widely implemented. Research and practical attacks have shown that MD5 and SHA-1 are unsuitable for security-sensitive applications that assume collision resistance against intentional adversaries.
You will still encounter MD5 in older logs and third-party feeds. Ingest pipelines should normalize to SHA-256 where possible and treat MD5 matches as legacy signals requiring corroboration. When writing internal runbooks or public knowledge base articles, stating this migration path explicitly helps practitioners searching for “MD5 vs SHA-256 malware” find authoritative guidance—exactly the kind of long-tail query that rewards detailed technical content.
SHA-256 as the Operational Default
SHA-256 belongs to the SHA-2 family and strikes a balance between performance on modern hardware and resistance to known attacks. Endpoint agents, sandboxes, and email security appliances routinely compute SHA-256 at ingestion time and emit it alongside process creation events.
Operational benefits include:
- Stable correlation across tools that all speak the same identifier language.
- Feed interoperability when sharing IOCs with partners via STIX or simple CSV exports.
- Database efficiency when indexing threat intelligence repositories keyed by hash.
Teams designing new pipelines should default to SHA-256 end-to-end, from raw telemetry through ticketing systems, to avoid duplicate work translating between hash types.
File Hash Lookups and Threat Intelligence Platforms
A file hash lookup asks a simple question: “Have we seen this exact content before, and if so, with what verdict?” Commercial and community threat intelligence platforms aggregate millions or billions of labeled samples contributed by researchers, automated sandboxes, and customer telemetry (subject to privacy policies).
High-quality platforms attach context beyond “malicious” or “clean”: family names, MITRE technique mappings, prevalence statistics, first-seen timestamps, and related network IOCs. That context transforms a bare hash hit into an investigative thread.
However, hash reputation has failure modes:
- Benign tools abused by attackers (PsExec, living-off-the-land binaries) may accumulate ambiguous reputations.
- Legitimate software updates can briefly appear rare and suspicious until prevalence grows.
- Attackers test unseen samples against public scanners before deployment, creating a race between defender visibility and attacker iteration.
Therefore, pair hash checks with prevalence and organizational allowlists for known internal build artifacts.
Building Detection Rules That Use File Hashes Wisely
A naive rule that blocks any process whose SHA-256 matches a threat feed will generate disruption whenever the feed lags reality or mislabels software. Better patterns include:
- Scope by path and signer. Require matches on unsigned binaries in user-writable directories, not on every global hit.
- Combine with parent process anomalies. A known-bad hash launched by an unexpected chain (for example,
winword.exespawning a rare executable) carries more signal than the hash alone. - Time-bound escalation. Treat first-seen-in-environment events as higher priority than ubiquitous hashes already blocked everywhere.
Security orchestration platforms can enrich alerts automatically: when a file hash triggers, query IP and domain reputation for concurrent network connections—areas where services like isMalicious provide complementary telemetry beyond file-centric data.
Hashing in Incident Response and Forensics
During investigations, analysts compute hashes of suspicious artifacts collected from disk images, memory, or extracted email attachments. Those hashes feed case timelines and evidence packages. Chain-of-custody documentation often includes SHA-256 values to prove artifacts were not altered between collection and analysis.
For malware analysts, comparing hash sets across endpoints can reveal lateral movement of identical payloads. For ransomware incidents, identical encryptor hashes across multiple hosts may indicate a single deployment wave versus multiple intrusion attempts.
Privacy, Compliance, and Telemetry Sharing
Uploading files or hashes to cloud services may intersect with data residency requirements and customer agreements. Some organizations operate on-premise hash databases or subscribe to offline updates. When evaluating vendors, clarify whether file hash submissions become part of community intelligence and whether metadata retention aligns with GDPR or sector-specific rules.
Transparent policy pages rank well in search because buyers compare legal posture alongside technical features—another reason comprehensive blog posts should address compliance adjacent topics, not only algorithms.
Limitations: When Hashes Are Insufficient
Attackers know defenders track file hash IOCs. Techniques to evade static identification include packing, encryption of payloads at rest, polymorphic engines, and downloading stage-one droppers that fetch malicious content only in memory. Modern EDR emphasizes behavioral analytics and memory scanning precisely because hash-only defenses are brittle.
Your content strategy should acknowledge this arms race honestly. Articles that promise “hash-based detection solves malware” lose credibility; articles that position hashes as one layer in a defense-in-depth stack earn trust and backlinks from practitioners.
Operational Metrics for Hash-Centric Programs
Measure effectiveness with metrics tied to outcomes, not raw match counts:
- Precision of hash-based alerts: percentage resulting in confirmed malicious activity.
- Time to ingest new IOCs from partners into blocking tiers.
- False unblock rate after allowlisting adjustments.
- Coverage of endpoints that successfully report SHA-256 on process creation events.
Improving telemetry quality—ensuring agents compute hashes consistently—often yields more value than indiscriminately adding more threat feeds.
Integrating File Hashes with CVE and Patch Context
Hashes sometimes intersect with vulnerability response: weaponized proof-of-concept binaries circulate with consistent SHA-256 values until authors modify them. Threat intelligence that links a CVE to known exploit file samples helps defenders hunt beyond patching alone—useful when patching lags or when legacy systems cannot be updated quickly.
Practical Checklist for Security Architects
- Standardize on SHA-256 in new systems; plan migration away from MD5-only keys in legacy indexes.
- Document how file hash lookups interact with allowlists for developer tools and penetration testing artifacts.
- Automate enrichment so analysts see family names, MITRE mappings, and related domain and IP IOCs in one pane.
- Review feed quality quarterly; stale or noisy feeds poison detection logic.
- Train SOC staff on fuzzy hashing and behavioral escalation paths when hash alone is inconclusive.
STIX, TAXII, and Sharing Hash IOCs at Scale
Many enterprises exchange file hash indicators using STIX objects packaged and distributed through TAXII servers or vendor-specific APIs. When you publish or consume STIX bundles, validate that file:hashes['SHA-256'] fields are normalized (lowercase hex, no stray whitespace) so automated consumers deduplicate correctly. Poor normalization duplicates tickets and breaks correlation searches—an implementation detail that rarely appears in marketing copy but matters enormously in production.
If you participate in industry sharing groups, align retention and classification labels with participant agreements. Threat intelligence sharing is as much about governance as it is about technology; searchable documentation that explains your hashing pipeline helps new members onboard faster.
Sandboxing and Dynamic Analysis Complement Static Hashes
Automated sandboxes execute unknown binaries in controlled environments and emit SHA-256 identifiers alongside behavioral reports: API call sequences, registry modifications, and attempted C2 domain resolutions. That dynamic layer catches malware that static hash lists miss on first encounter. Feed the sandbox’s file hash outputs back into your threat library so the next appearance anywhere in the fleet benefits from collective learning.
Balance cost: not every file warrants full sandbox execution. Tier uploads by risk—email attachments from untrusted sources rank higher than internal build artifacts with known signers.
Finally, schedule periodic red-team tests that introduce benign renamed binaries with previously unseen hashes to confirm analysts escalate on behavior when reputation data is empty—proving detections are robust beyond stale lists.
Conclusion
File hash analysis remains a cornerstone of malware detection and threat intelligence operations because it is cheap to compute, easy to share, and works across heterogeneous tooling. The evolution from MD5 to SHA-256 reflects a maturing field that understands both cryptographic limits and operational needs. The winning strategy combines strong hash reputation data with prevalence analytics, process context, network intelligence, and continuous tuning—never static lists in isolation.
Organizations publishing technical SEO content around file hash, SHA-256, and malware workflows should prioritize depth, transparent discussion of limitations, and integration guidance. That is how you attract practitioners who are ready to evaluate products and adopt best practices, not just skim definitions.
Frequently asked questions
- Why do security teams prefer SHA-256 over MD5 for file hashing?
- SHA-256 offers a much larger output space and stronger collision resistance than MD5. MD5 collisions can be crafted for some threat scenarios, so modern platforms treat SHA-256 as the default for file identification and integrity verification.
- Can two different files have the same hash?
- In theory, any hash function can collide, but for SHA-256, accidental collisions are astronomically unlikely for practical purposes. Attackers may try to craft collisions for broken algorithms; that is why legacy MD5-only workflows are discouraged.
- Is a file hash enough to prove a file is malicious?
- A hash match in a reputable threat intelligence database is strong evidence, but analysts should still consider false positives, renamed legitimate tools, and context such as path, signer, and parent process. Hash alone is a signal, not a full verdict.
Related articles
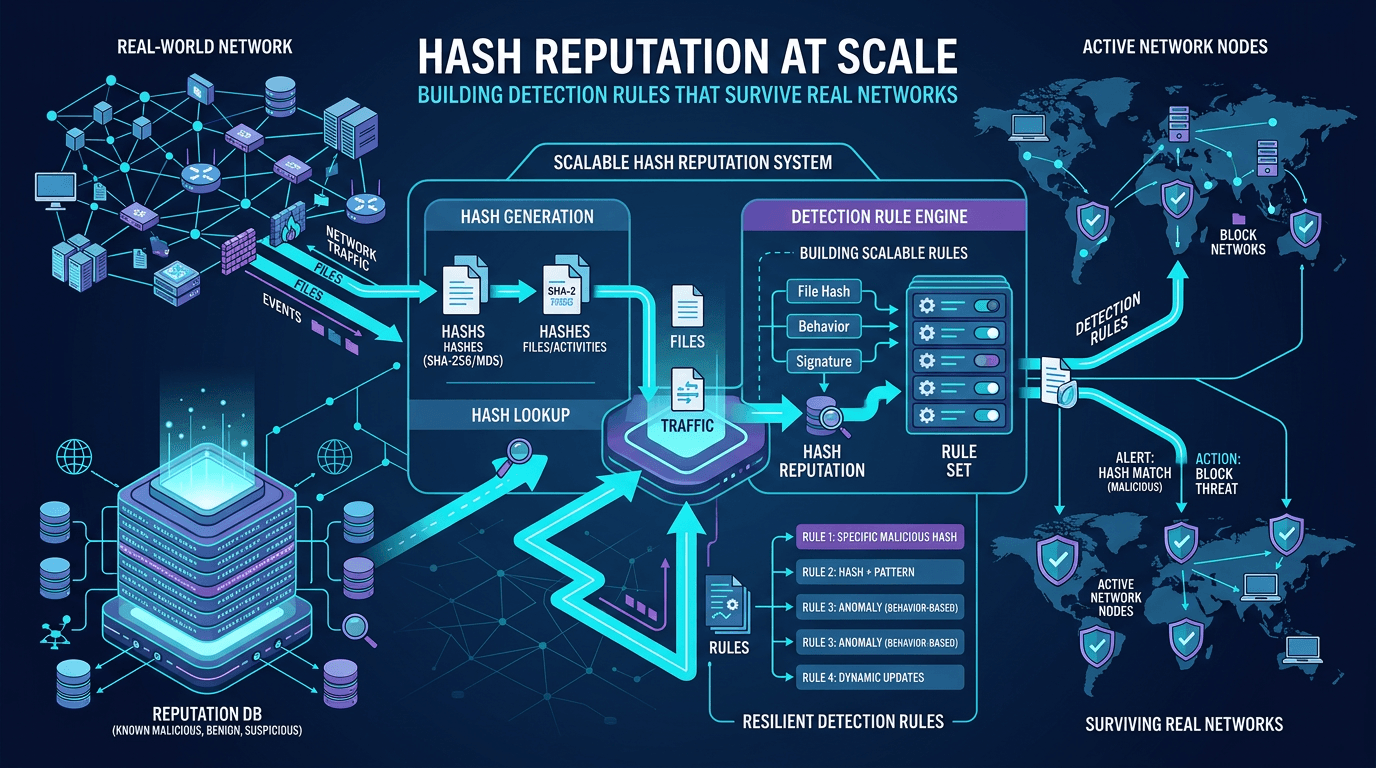 Apr 22, 2026Hash Reputation at Scale: Building Detection Rules That Survive Real Networks
Apr 22, 2026Hash Reputation at Scale: Building Detection Rules That Survive Real NetworksMove beyond one-off hash blocks: design reputation pipelines, reduce false positives, and integrate file intelligence with IP and domain context for enterprise-grade detection engineering.
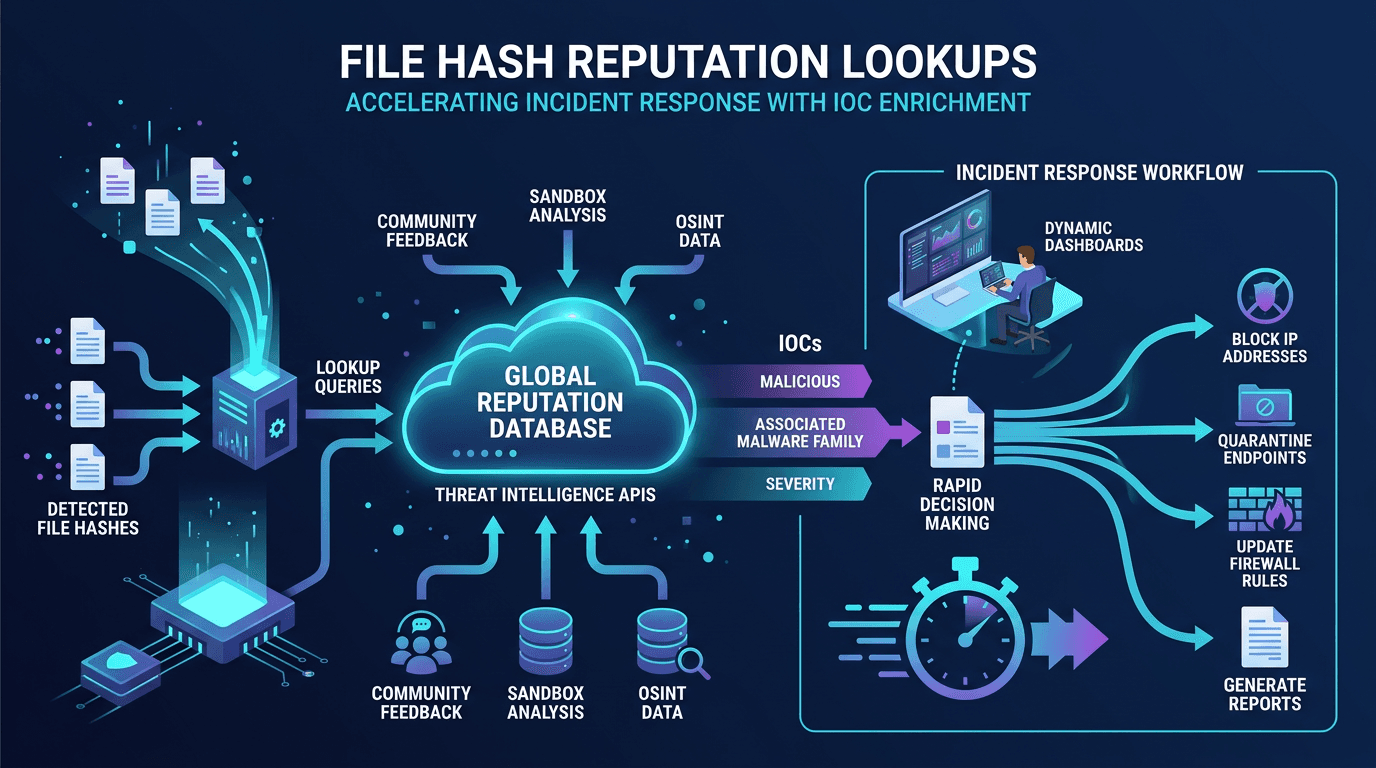 Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC EnrichmentA practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
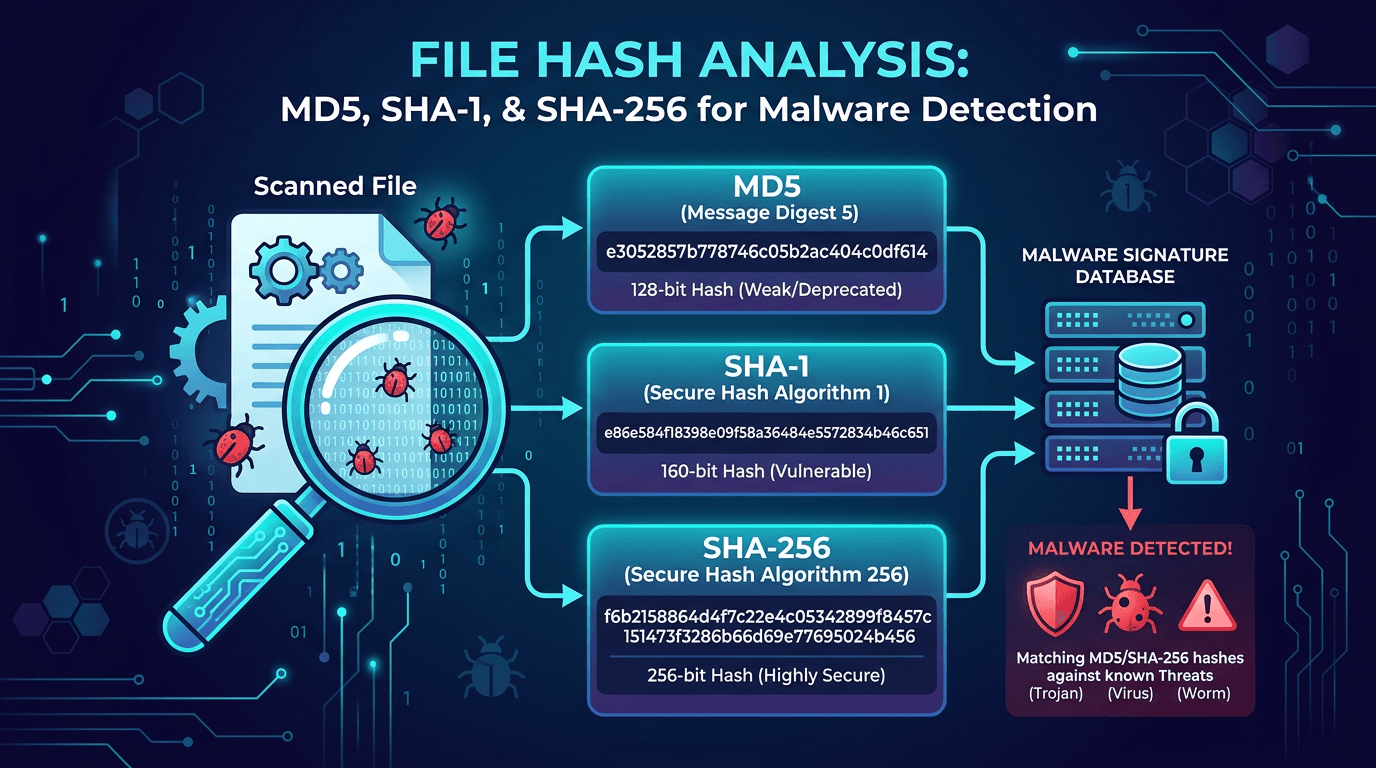 Apr 18, 2026File Hash Analysis: MD5, SHA-1, and SHA-256 for Malware Detection and Threat Hunting
Apr 18, 2026File Hash Analysis: MD5, SHA-1, and SHA-256 for Malware Detection and Threat HuntingA practical guide to file hashes in cybersecurity—how MD5, SHA-1, and SHA-256 work, why they matter for malware detection, incident response, and threat hunting, and how to use hash lookups to enrich indicators of compromise.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker