Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security Programs
Align CTI outputs with audience needs: executive risk narratives, SOC-ready IOCs, and MITRE-mapped TTPs—plus governance models that keep intelligence timely and measurable.
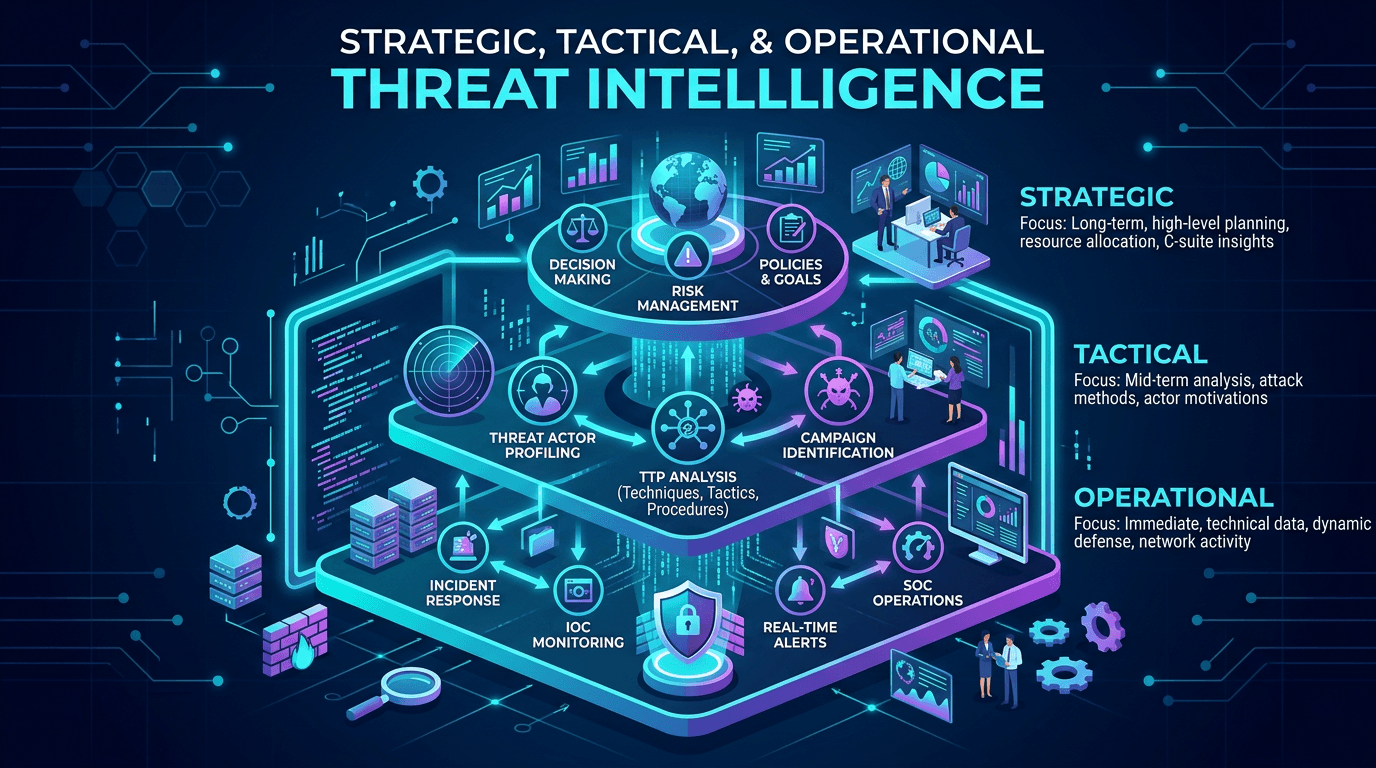
Threat intelligence programs fail when they optimize for a single audience. Executives want concise risk narratives; SOC analysts need IOCs and detection ideas; vulnerability managers want CVE exploitation insight. Industry frameworks separate strategic, tactical, and operational intelligence—this article clarifies those layers with actionable governance guidance, connects them to MITRE ATT&CK, and shows how network-centric telemetry (IP and domain reputation from services like isMalicious) complements narrative reporting.
Strategic Threat Intelligence: Horizon Scanning for Leadership
Strategic intelligence answers “what trends could disrupt our mission over the next year or more?” Topics include geopolitical cyber risk, regulatory evolution, ransomware economics, and sector-targeting shifts among threat actors. Deliverables might include quarterly briefings, board slides, and risk register updates.
Effective strategic reporting avoids jargon walls. Translate attack vectors into business impacts: operational downtime, intellectual property loss, regulatory fines. Pair qualitative analysis with quantitative benchmarks—peer incident frequencies, insurance premium drivers—so leaders grasp relative urgency.
SEO note: executive-facing articles rank for queries like “cyber risk trends 2026” when they provide structured takeaways and cite authoritative sources; depth beats keyword stuffing.
Tactical Threat Intelligence: TTPs, Campaigns, and Detection Ideas
Tactical intelligence bridges strategy and operations. Analysts map adversary behaviors to MITRE ATT&CK techniques, summarize phishing lures, describe malware staging, and recommend detection opportunities (Sigma/YARA ideas). This layer helps purple teams design realistic exercises and helps detection engineers prioritize backlog items.
Tactical reports should include:
- Threat actor aliases and confidence levels of attribution.
- Infrastructure patterns: registrar choices, naming conventions, hosting ASNs.
- Victimology and sector focus.
- IOCs with context—not raw CSV dumps alone.
When tactical intelligence ignores detection feasibility, it becomes academic. Always ask: “Which log sources in our environment could observe this technique?”
Operational Threat Intelligence: The SOC Lifeline
We covered operational CTI extensively in companion articles; here, emphasize interfaces. Operational intelligence must land in ticketing systems, EDR consoles, and firewalls with SLAs. IOC TTLs and confidence scores matter. Operational success is measured in blocked attacks and faster investigations—not slide count.
Integrating Layers: A Single Pipeline, Multiple Views
Rather than three disconnected teams, think one pipeline with multiple renderings:
- Collect raw data: feeds, OSINT, incident artifacts, partner sharing.
- Analyze and tag using consistent taxonomies (STIX objects, ATT&CK IDs).
- Publish via routes: API for tools, PDF for executives, wiki for hunters.
Shared taxonomies prevent contradictory messaging—if strategic briefings claim “low ransomware risk” while operational feeds scream high-confidence ransomware domains, credibility collapses.
Governance: Roles, SLAs, and Ethical Boundaries
Define:
- Source approval processes—who may subscribe to paid feeds on behalf of the org?
- Handling instructions for sensitive sharing (government, ISAC).
- Retention policies aligned with privacy regulations.
- Bias checks—avoid mirror-imaging (assuming adversaries will always behave as you would).
Ethical intelligence work respects civil liberties; indiscriminate monitoring of personal data undermines trust and may violate law.
Mapping Intelligence to the MITRE ATT&CK Matrix
ATT&CK gives tactical and operational teams a Rosetta Stone. Strategic teams can summarize which tactic categories (initial access, persistence, impact) face elevated industry risk in a given year. Ensure your coverage assessments distinguish available data from implemented detections—a common reporting gap.
Vulnerability Intelligence as a Bridge
CVE prioritization sits between strategy and operations. EPSS and KEV data inform patch schedules (operational), while discussions about zero-day markets belong in strategic forums. Intelligence analysts should narrate active exploitation trends connecting vulnerability disclosures to threat actor campaigns.
Measuring CTI Program Maturity
Meaningful KPIs:
- Time from publication to detection coverage for new campaign IOCs.
- Executive briefing satisfaction scores (qualitative but informative).
- Contribution to incident mean time to respond when intel shortens investigations.
Avoid raw “reports published per quarter” without consumption metrics.
Tooling: TIPs, SIEM, and Data Lakes
Threat Intelligence Platforms (TIPs) aggregate feeds, deduplicate, and distribute—but require curation or they become expensive dashboards. Integrate TIPs with SIEM and SOAR so IOCs flow automatically where appropriate. For IP/domain reputation, direct API enrichment during alert triage reduces context switching.
Collaboration with Legal and Communications
Public attribution statements and breach disclosures intersect with intelligence conclusions. Coordinate language carefully; overstating attribution confidence invites criticism. Internal intelligence summaries should carry confidence labels consumed by legal before external posts.
Training and Career Paths
Analysts may specialize: geopolitical risk, malware reverse engineering, dark web monitoring. Cross-training reduces single points of failure and improves quality of peer review. Certification programs (vendor-neutral and commercial) help baseline skills—though hands-on labs beat acronym collections.
Threat Intelligence in DevSecOps
Developers benefit from tactical summaries of supply chain threats—typosquatted packages, compromised maintainer accounts—translated into secure coding guidance. Strategic alignment with product roadmaps ensures security features land where threat modeling indicates highest risk.
Common Anti-Patterns
- Feed hoarding without analysis capacity.
- Attribution obsession that delays defensive action.
- One-size reporting that satisfies nobody.
- Ignoring internal incidents as an intelligence source—your breaches contain the most relevant lessons.
International Considerations
Multinationals must reconcile intelligence sharing across jurisdictions. Data localization may constrain where IOCs reside; document architecture decisions clearly for auditors.
Conclusion
Strategic, tactical, and operational threat intelligence are complementary lenses on the same adversary landscape. Structure your program so each audience receives timely, actionable, and appropriately scoped insight—grounded in shared taxonomies and measured by risk reduction, not vanity metrics.
Search-optimized technical blogs should interlink related concepts (attack vectors, CVE, IOCs) to build topical authority clusters that search engines reward over time.
Deep Dive: Briefing Cadence and Agendas
Establish weekly tactical standups for analysts and SOC liaisons, monthly strategic synthesis for leadership, and quarterly red-team readouts connecting intelligence to control effectiveness. Predictable cadence builds trust; ad-hoc chaos signals immaturity.
Integrating File Intelligence
Where file hash analysis informs tactical reporting, cross-link to sandbox outputs and YARA coverage. Practitioners often search “strategic vs tactical threat intelligence examples”—include concrete mini case studies (sanitized) to satisfy informational intent and improve dwell time on page.
Future Outlook: Standards and Automation
Expect more automated STIX graph reasoning and LLM-assisted summarization—with human oversight. Standards evolution (STIX 2.x objects, CSAF for advisories) will keep architects busy; subscribe to change logs so your integrations do not silently rot.
Community Participation
Encourage analysts to contribute sanitized research to conferences and blogs—community reputation attracts talent and sharpens analytical rigor through feedback loops.
Intelligence Requirements (IRs): Starting From Business Questions
Mature programs begin with prioritized intelligence requirements—explicit questions stakeholders need answered (“Which threat actors target our region’s energy sector?” “What phishing kits spoof our brand?”). IRs drive collection plans and prevent aimless feed purchases. Revisit IRs semi-annually; business pivots (new product lines, M&A) shift adversary interest.
Document IRs in a living spreadsheet with owners, due dates, and satisfaction criteria. When SEO teams ask for blog topics, mine unanswered IRs for content gaps that also serve customers—alignment rarely happens by accident.
Collection Management: Open Sources, Closed Sources, and Primary Research
Balance OSINT (social media, code repositories, certificate transparency logs) with paid databases and closed sharing communities. Primary research—sandbox detonations, honeypots—produces unique insights competitors lack. Budget time for validation; misinformation spreads quickly during major incidents.
Fusion Analysis: Combining Internal and External Data
Fusion means correlating partner IOCs with your SIEM—not just stacking feeds. Example: external report mentions domain X; internal DNS logs show rare queries days earlier—your proactive hunting window. Fusion analysts need query skills across data lakes; invest in training.
Dissemination Formats That Actually Get Read
Executives prefer one-page summaries with a risk dial and three actions. Engineers want JSON and APIs. Middle management may want slide decks with narrative arcs. Reuse source analysis; rewrite presentation—never dump the same PDF everywhere.
Feedback Loops From Incidents to Intelligence
Post-incident reviews should answer: which IRs were satisfied, which intelligence was stale, which detection gaps remain? Feed those answers into next quarter’s collection priorities. Without closure, incidents become traumatic one-offs instead of organizational learning.
Threat Intelligence for Product Security
Product teams benefit from tactical insights on abuse patterns—credential stuffing against your APIs, fake mobile apps, fraudulent domains impersonating your brand. Strategic teams forecast investment needs for fraud prevention platforms. Embed intelligence liaisons in product councils.
Budget Conversations: Articulating ROI
Translate outcomes: “This feed reduced phishing investigation time by 22% last quarter” beats “we have 50 million IOCs.” Pair with risk scenarios—expected loss reductions—to speak finance’s language cautiously but credibly.
Tabletop: Intelligence Failure Simulation
Exercise a scenario where trusted intelligence was wrong—defenders learn to maintain skepticism and redundant controls. Discuss communication plans when customers ask why a published IOC list contained false positives.
Aligning With Enterprise Risk Management
Map intelligence findings to enterprise risk categories and heat maps. When risk committees see cyber risks alongside financial and operational risks, CTI stops being an isolated tower.
Knowledge Management and Search Optimization
Internal portals should tag documents by threat actor, region, technique, and data source. Externally, pillar pages linking to deep dives (like this series) strengthen site architecture for SEO—clear internal linking signals topical authority to crawlers.
Diversity of Analyst Backgrounds
Teams blending malware analysts, geopolitical specialists, and former incident responders produce richer fusion. Hiring solely for certifications misses creative synthesis skills developed in multidisciplinary environments.
Practical Checklist for Program Leaders
- Publish IRs and review quarterly.
- Maintain a source catalog with cost, coverage, and overlap analysis.
- Automate low-risk IOC distribution; reserve human time for fusion and narrative.
- Measure consumption—not just production.
- Train spokespeople for media inquiries during crises—intelligence conclusions become public fast.
Closing Thoughts on Sustainable CTI
Threat intelligence is not a platform purchase; it is a cycle of questions, answers, and refinements. Strategic clarity, tactical precision, and operational speed reinforce each other when pipelines—not org charts—integrate them.
Treat your public articles as part of that cycle: educate the market, attract talent, and document methodologies your future self will thank you for.
Frequently asked questions
- What is strategic threat intelligence?
- Strategic threat intelligence provides high-level insight into trends, motivations, and long-term risks—often consumed by executives and boards to guide investments and policy.
- What is tactical threat intelligence?
- Tactical intelligence focuses on the techniques, procedures, and infrastructure patterns adversaries use in campaigns, helping defenders understand how attacks are conducted and how to detect them.
- How should organizations structure CTI teams across these levels?
- Use shared taxonomies and intake processes, but assign clear owners for collection, analysis, and dissemination per audience. Avoid forcing one report format to serve executives and SOC analysts simultaneously without tailoring.
Related articles
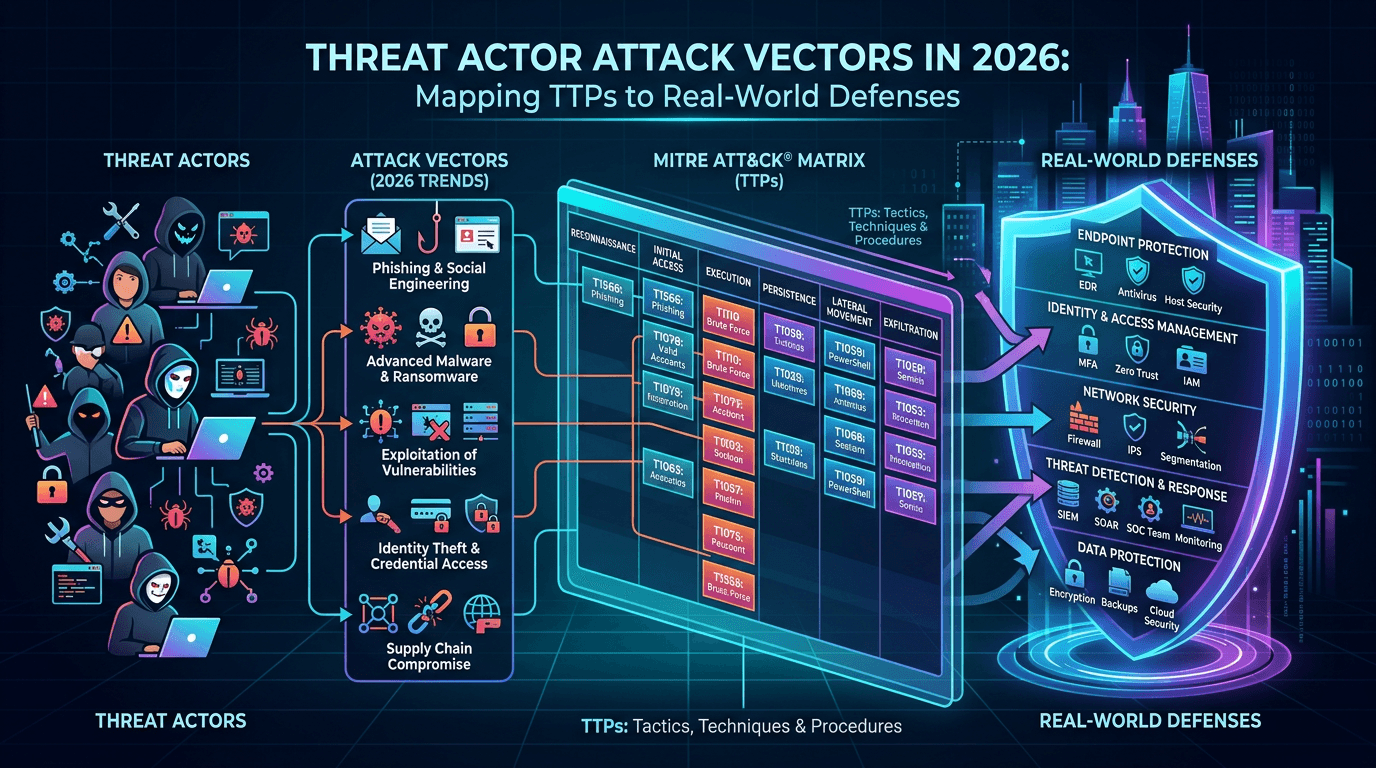 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
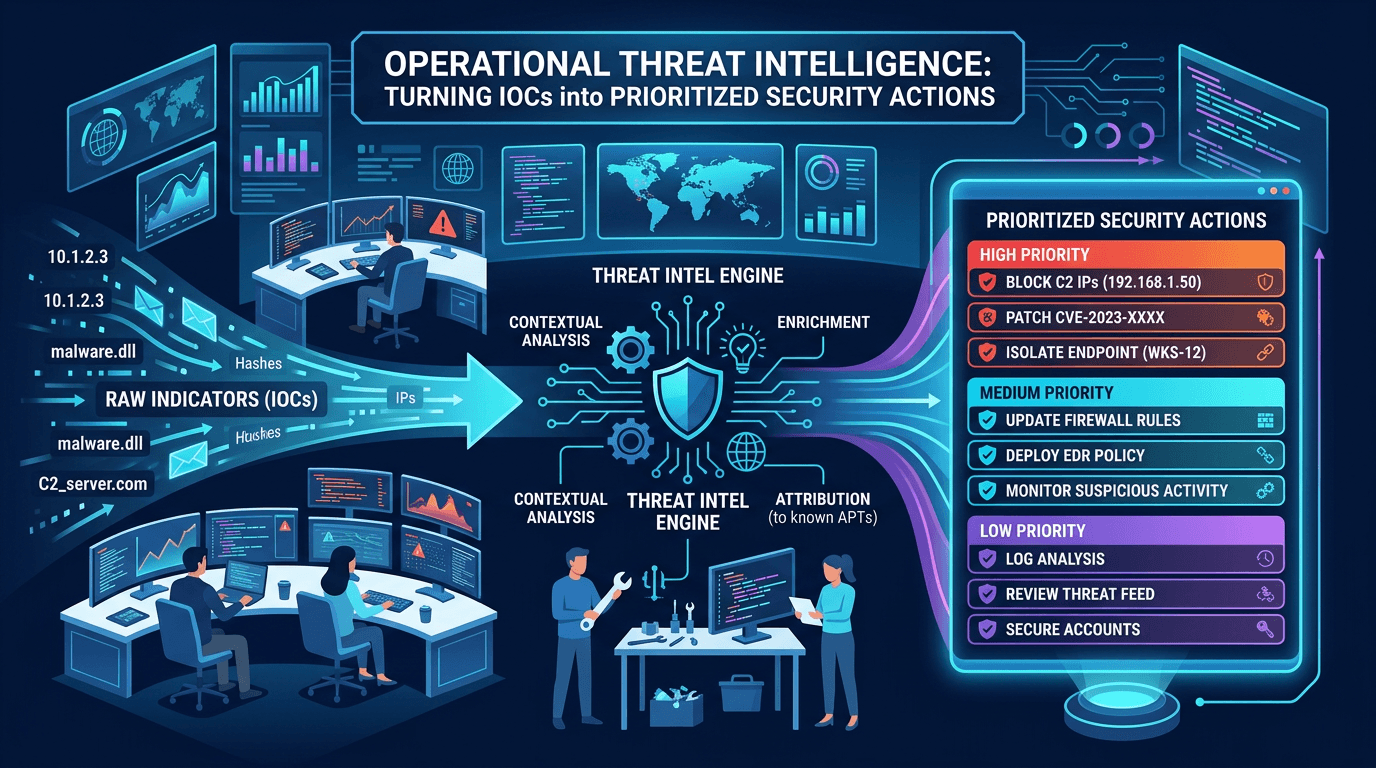 Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security ActionsDefine operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
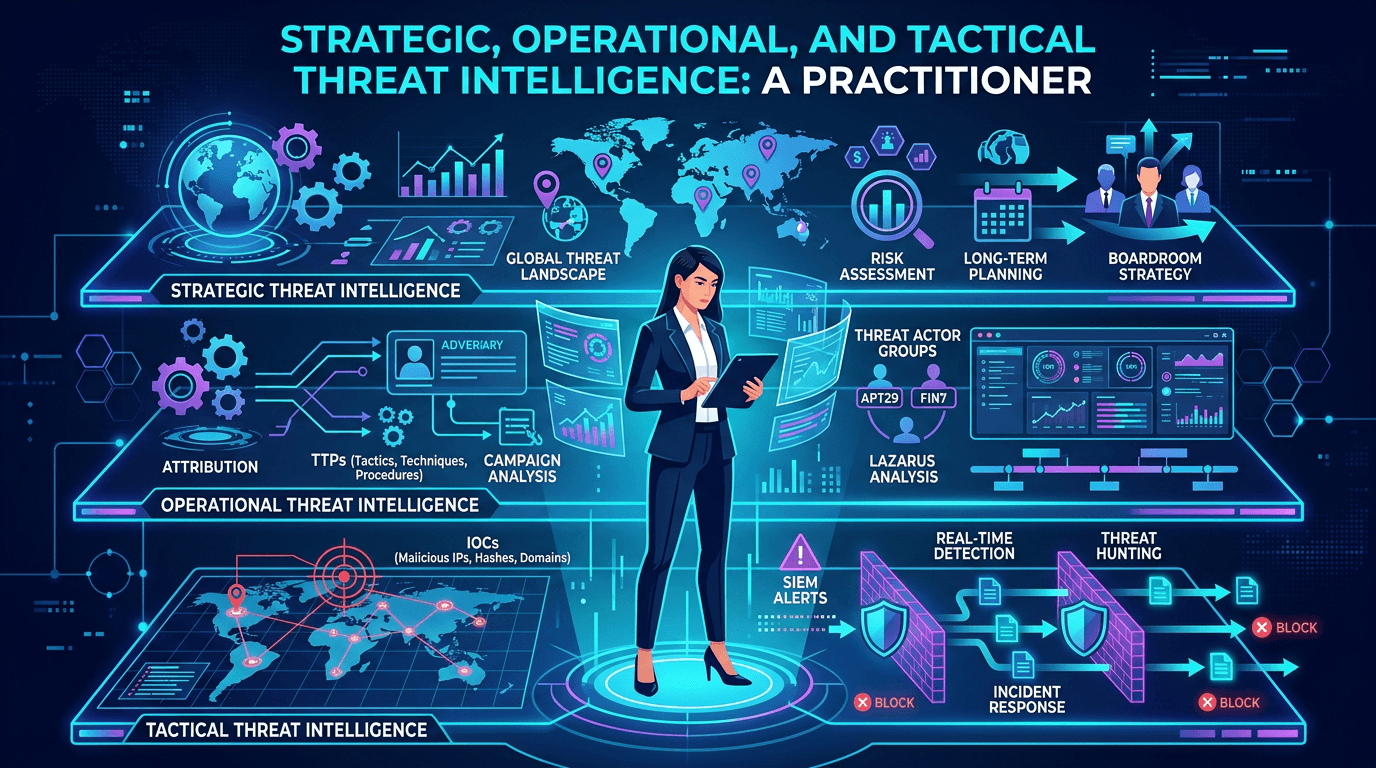 Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker