Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Explore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
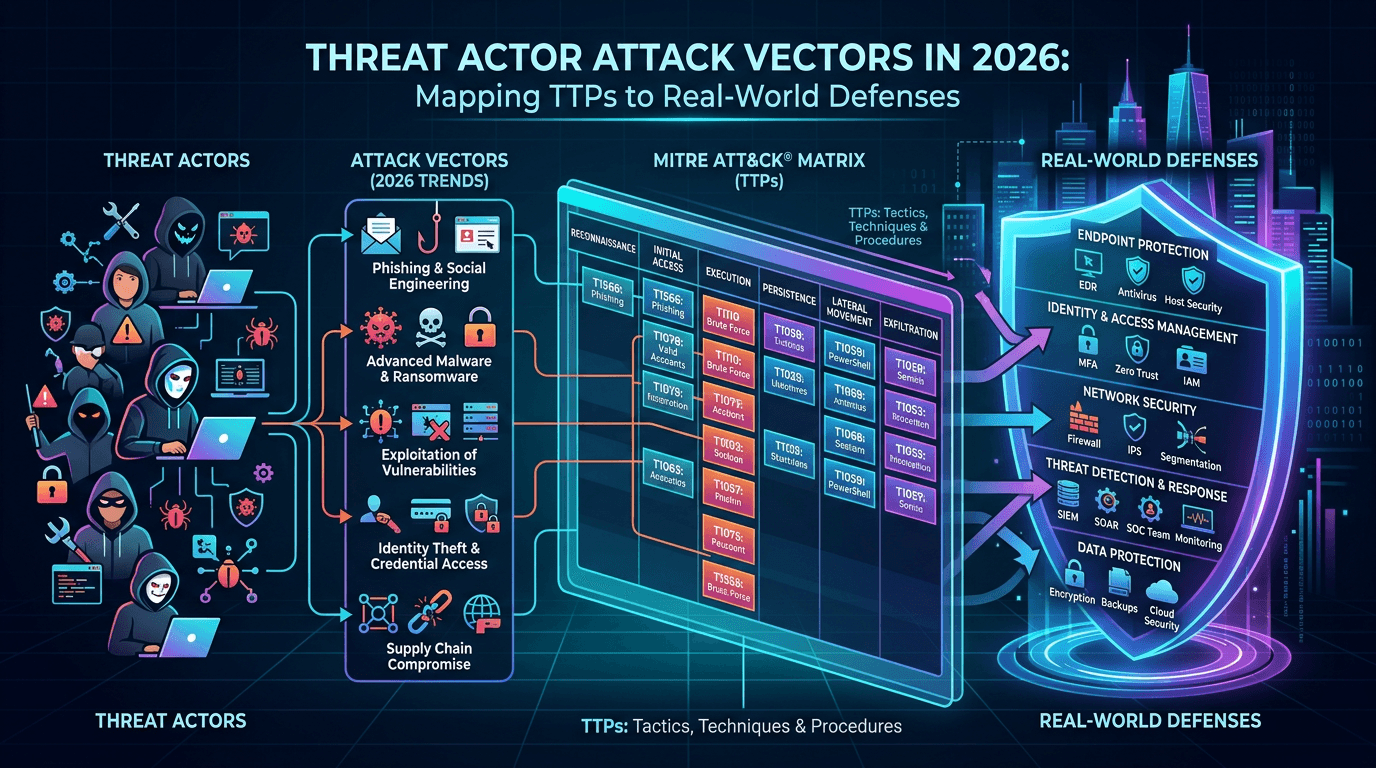
When executives ask which threat actors worry them most, seasoned CISOs often redirect the conversation toward attack vectors—the repeatable methods adversaries use to enter and expand within environments. Attribution is fascinating for intelligence analysts, but defenders win by understanding how campaigns unfold regardless of brand name. This article surveys dominant attack vectors in 2026, maps them to MITRE ATT&CK thinking, and explains how threat intelligence, vulnerability management, and detection engineering combine into threat-informed defense.
Initial Access: The Front Door Problem
Initial access remains the most scrutinized phase because preventing entry eliminates downstream damage. Common vectors include:
- Phishing and social engineering targeting employees and contractors.
- Exploitation of public-facing applications (VPNs, mail gateways, collaboration tools).
- Valid accounts obtained via credential stuffing, infostealer logs, or insider assistance.
- Supply chain compromise where trusted software updates become delivery channels.
Search traffic around “initial access broker” and “ransomware entry points” reflects practitioner focus on cutting compromise chains early. Security awareness programs still matter, but technical controls—phishing-resistant MFA, device compliance checks, and strict external surface monitoring—reduce reliance on human perfection.
Credential Theft and Session Hijacking
Passwords alone are insufficient; attackers increasingly steal session tokens and MFA cookies from endpoint malware or adversary-in-the-middle phishing kits. Attack vectors here include malicious browser extensions, compromised SSO configurations, and help-desk social engineering to reset MFA devices.
Defensive stacks must evolve from “password policies” to “session and device trust.” Continuous authentication signals—device health, impossible travel, and anomalous OAuth grants—complement static credentials.
Living Off the Land and Dual-Use Tools
Not every malicious action involves a malware binary with a known file hash. Adversaries abuse built-in utilities—PowerShell, certutil, WMI—reducing their footprint on disk. These attack vectors challenge traditional antivirus-centric models and elevate EDR behavioral analytics.
Purple teams simulate LOTL chains to validate that detections trigger on command-line patterns, parent-child anomalies, and unusual network destinations—not only on unsigned executables.
Lateral Movement and Identity Paths
Once inside, attackers pivot using Remote Desktop, SMB, WinRM, or cloud APIs. Lateral movement often follows identity: stolen domain administrator credentials, Kerberos ticket abuse, or misconfigured IAM roles in public cloud tenants.
Segmentation and least privilege remain foundational. Micro-segmentation projects fail when organizations cannot maintain accurate inventory of workloads and dependencies—another reason threat intelligence about typical ransomware lateral tooling informs architectural priorities.
Command and Control: Domains, IPs, and Protocols
C2 infrastructure uses resilient domains, bulletproof hosting, and encrypted channels. Defenders rely on DNS monitoring, TLS inspection (where ethically and legally permissible), and IP/domain reputation services to spot beaconing. isMalicious and similar platforms aggregate reputation signals so analysts do not manually pivot across dozens of passive DNS sources during every alert.
From an SEO perspective, content clusters that combine “C2 detection,” “malicious domain,” and “network threat intelligence” capture researchers comparing approaches and tools.
Data Exfiltration: Stealth Versus Speed
Ransomware groups may exfiltrate data before encryption; espionage actors prioritize stealth over years. Vectors include cloud storage APIs, DNS tunneling, email forwarding rules, and removable media on air-gapped jumps (rare but catastrophic).
Detection strategies layer DLP, egress filtering, and behavioral baselines for unusual upload volumes. Threat intelligence about exfil tooling names helps signature developers—but behavior wins when attackers rename binaries constantly.
Ransomware Affiliate Models and Attack Surface
Modern ransomware operations resemble franchises: core developers provide payloads; affiliates perform intrusion. Affiliates choose attack vectors aligned with skills—some specialize in VPN exploits, others in phishing. Understanding this ecosystem explains why the same ransomware strain appears alongside diverse entry TTPs in breach reports.
Nation-State Campaigns Versus Financially Motivated Actors
Nation-state actors may accept longer dwell times and invest in zero-day vulnerability research. Financial actors optimize for ROI, often racing to exploit newly disclosed CVEs before patches propagate. Your threat intelligence subscription should clarify which actor classes target your sector so you calibrate monitoring depth appropriately.
Mapping Attack Vectors to MITRE ATT&CK
MITRE ATT&CK provides a common language. Threat-informed defense programs build coverage maps: for each prioritized technique, document preventive controls, detective controls, and data sources. Gaps become funded projects rather than ad hoc surprises after incidents.
Technique IDs also improve communication with auditors and insurers who increasingly recognize ATT&CK-aligned assessments.
Purple Team Scenarios by Attack Vector
Structured exercises validate defenses:
- Phishing simulation with credential capture → test MFA bypass detections.
- Assume breach from a workstation → test lateral movement alerts.
- Cloud IAM misconfiguration scenario → test CSPM detections and response.
Document results in intelligence-friendly formats so CTI teams update briefings with realistic defensive posture—not generic maturity scores.
Threat Intelligence Feeds and Actor Reporting
Quality actor reporting includes TTP evolution, preferred infrastructure, and regional targeting. When reading such reports, extract IOCs and technique narratives; the latter drives durable detections while IOCs expire.
Share sanitized findings with industry peers through ISACs—collective visibility raises everyone’s baseline against shared attack vectors.
Vulnerability Exploitation as a Vector
Public CVE exploitation often appears in scanning surges hours after PoC release. EPSS and KEV catalogs help prioritize patching. Combine patch urgency with temporary network blocks for known scanning IPs sourced from threat intelligence—a bridging control when systems cannot restart immediately.
Measuring Coverage of Attack Vectors
Metrics might include:
- Percentage of prioritized ATT&CK techniques with automated detective coverage.
- Time to detect simulated lateral movement.
- Volume of phishing messages blocked pre-inbox versus reported by users.
Avoid purely quantitative ATT&CK “coverage percentages” without qualitative validation—checkbox mapping games rarely survive red teams.
Communication with Leadership
Translate attack vectors into business terms: “criminal groups routinely breach peers via unpatched VPNs” resonates more than technique IDs alone. Pair narratives with trend data from threat intelligence vendors and government advisories.
Common Mistakes in Attack-Vector Planning
- Over-indexing on malware samples while ignoring identity-based paths.
- Treating cloud and on-prem as separate risk universes—attackers chain them.
- Neglecting third-party access paths used by vendors and MSPs.
- Failing to retire legacy protocols that modern attackers still love (looking at you, NTLM-heavy environments).
Extended Outlook: AI-Augmented Social Engineering
Generative tools lower the cost of convincing phishing and deepfake-assisted voice fraud. Attack vectors through communications channels will diversify. Technical mitigations—sender policy frameworks, verified calling workflows for sensitive requests, and rapid domain takedown coordination—gain importance alongside user training.
Document your organization’s stance on emerging vectors so SOC playbooks evolve in step—not after painful incidents.
Building an Internal Attack Vector Register
Maintain a living register listing prioritized vectors for your industry, linked controls, owners, and last test date. During audits, this register demonstrates proactive governance and gives CTI teams a structured place to attach new reporting. Public blog articles can mirror anonymized excerpts (without sensitive details) to demonstrate thought leadership and capture search traffic for terms like “attack vector register template” or “threat informed defense checklist.”
Watering Holes, SEO Poisoning, and Drive-By Risks
Not every intrusion begins with an email. Watering hole compromises target websites frequented by employees in your sector, while search engine optimization poisoning pushes malicious pages near the top for niche queries. Users who trust organic search results may download trojanized installers that evade email gateways entirely.
Defensive layers include secure browsing policies, reputation checks on domains before download, and EDR rules that scrutinize child processes launched by browsers. Threat intelligence that tracks malicious domains and URL patterns complements traditional email-centric controls.
API Abuse and Modern Application Attack Surfaces
Microservice architectures expose APIs that become attack vectors when authentication is weak or rate limits are absent. Attackers abuse OAuth flows, scrape data via overly permissive keys, and probe GraphQL endpoints for hidden fields. Application security reviews should treat APIs as perimeter surfaces with logging parity to north-south traffic.
Pair WAF/API gateway telemetry with IP reputation to throttle automated probing campaigns early—often precursors to targeted exploitation attempts.
Mobile and Endpoint Diversity
BYOD policies and mobile phishing expand the footprint. Mobile devices may lack the same EDR depth as managed laptops, creating inconsistent visibility. Unified endpoint management and mobile threat defense products close some gaps, but policy clarity matters: define which workloads may access corporate data from which device classes.
Collaboration Tool Abuse
Chat platforms, ticketing systems, and code hosts become distribution channels for malicious attachments and links because users inherently trust internal workspaces. Attack vectors here include compromised partner accounts posting “fixes” that are actually malware. Monitoring identity risk scores and anomalous posting behavior supplements static malware scanning.
Tabletop: Cross-Functional Attack Vector Review
Quarterly sessions with IT, development, and business stakeholders surface shadow workflows—finance teams using unsanctioned file shares, marketing teams testing unreviewed plugins—that become real attack vectors. Document findings and feed them into risk registers; CTI briefings should reference these business realities rather than abstract hacker stereotypes.
Why Keyword-Rich Documentation Helps Defenders Find You
Practitioners search for precise combinations—“MITRE initial access phishing,” “ransomware lateral movement detection,” “malicious IP blocking best practices.” Articles that use those phrases naturally (not stuffed) while delivering substantive guidance perform better in search and reduce support burden for vendor documentation teams.
Conclusion
Threat actors come and go; attack vectors evolve more slowly and predictably once you study them at scale. Prioritize vectors by likelihood and impact for your organization—not generic industry heatmaps alone. Map them to MITRE ATT&CK, fund measurable detection coverage, enrich network alerts with IP and domain reputation (for example via isMalicious telemetry), and rehearse incidents until runbooks feel routine.
Long-form guides that connect attack vectors, MITRE ATT&CK, and measurable defense outcomes rank well in search because they match how practitioners research during program builds and board presentations—especially when refreshed annually to reflect shifting TTPs. Operational takeaway: boring response drills mean muscle memory when crises arrive.
Frequently asked questions
- What is an attack vector in cybersecurity?
- An attack vector is a path or method an adversary uses to compromise or abuse a system—such as phishing, exposed services, stolen credentials, or software vulnerabilities. Mapping vectors helps defenders prioritize controls and detection coverage.
- How does MITRE ATT&CK relate to attack vectors?
- MITRE ATT&CK organizes adversary tactics and techniques into a matrix. Techniques describe how adversaries achieve tactical goals (for example, phishing for initial access). Mapping your defenses to ATT&CK shows coverage gaps across attack vectors.
- Do all threat actors use the same attack vectors?
- No. Nation-state groups, cybercriminal ransomware affiliates, and hacktivists differ in resources, stealth requirements, and monetization models. However, many reuse common building blocks like valid accounts, living-off-the-land binaries, and public exploits.
Related articles
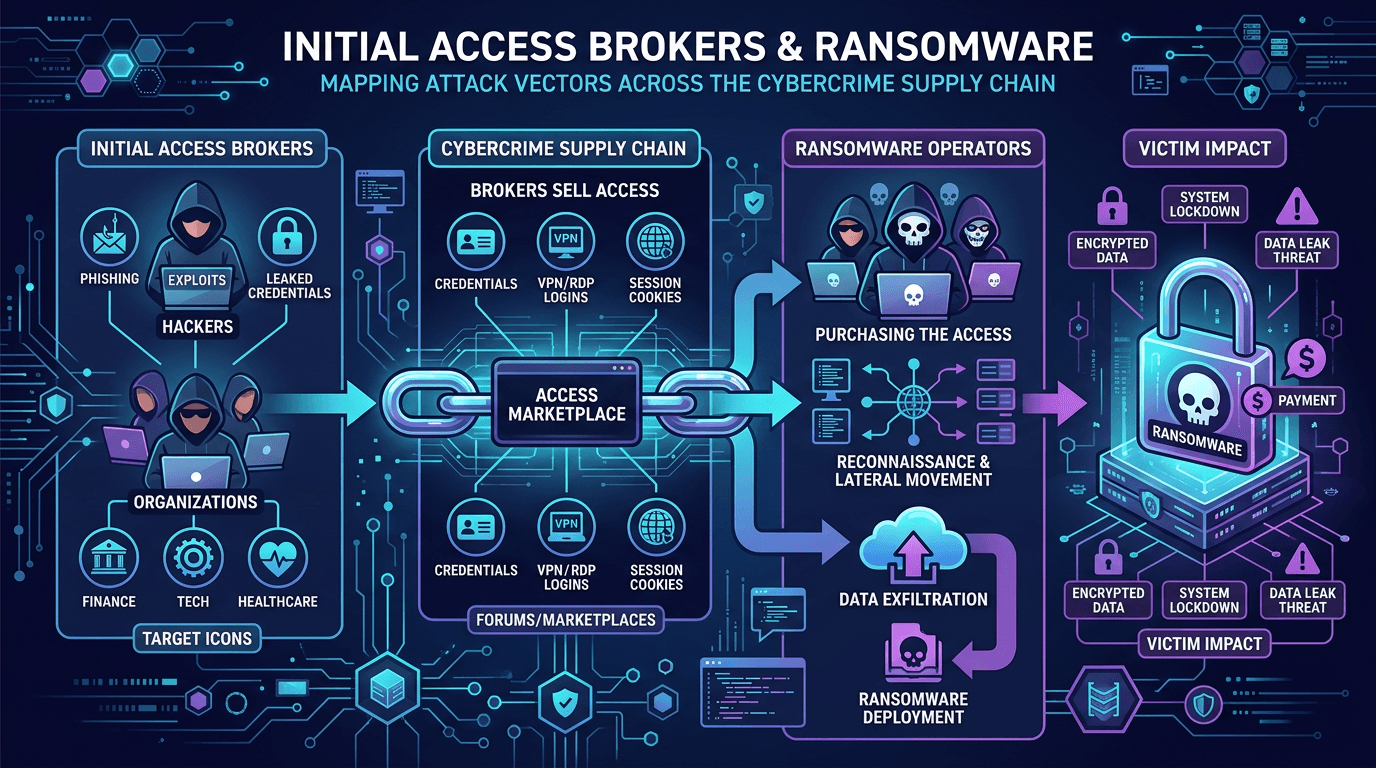 Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply ChainUnderstand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
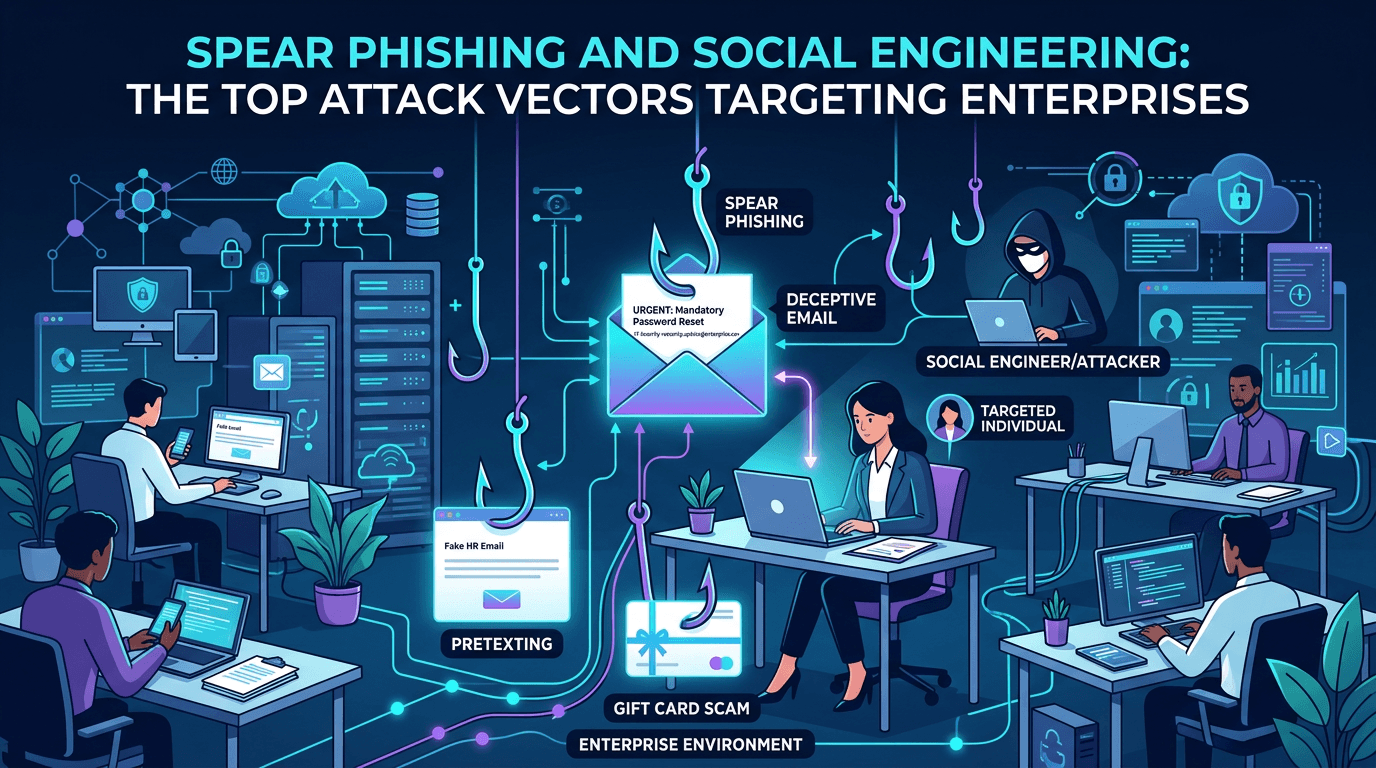 Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
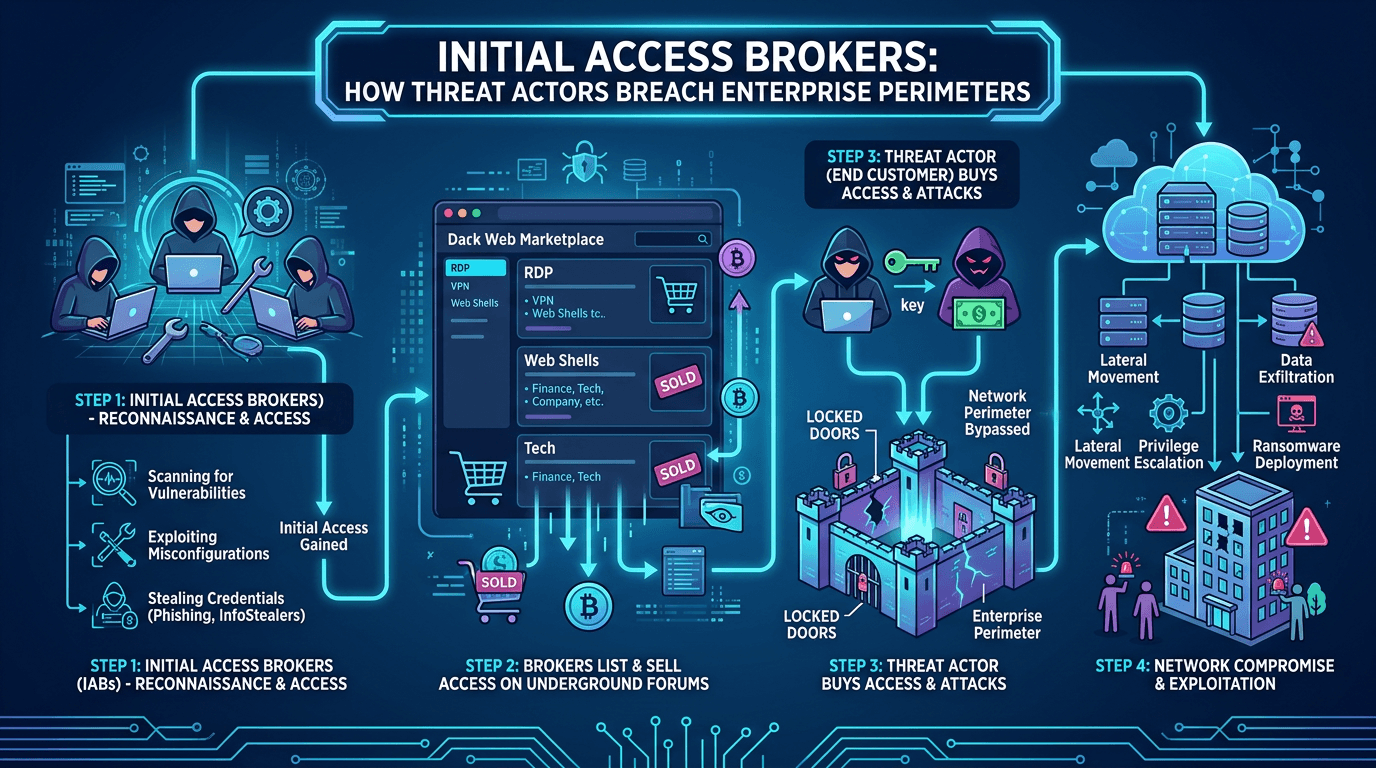 Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026
Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026A deep dive into initial access brokers (IABs)—the cybercrime specialists who sell footholds into corporate networks—covering their techniques, pricing, detection signals, and how to defend against the top attack vectors they exploit.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker