Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Understand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
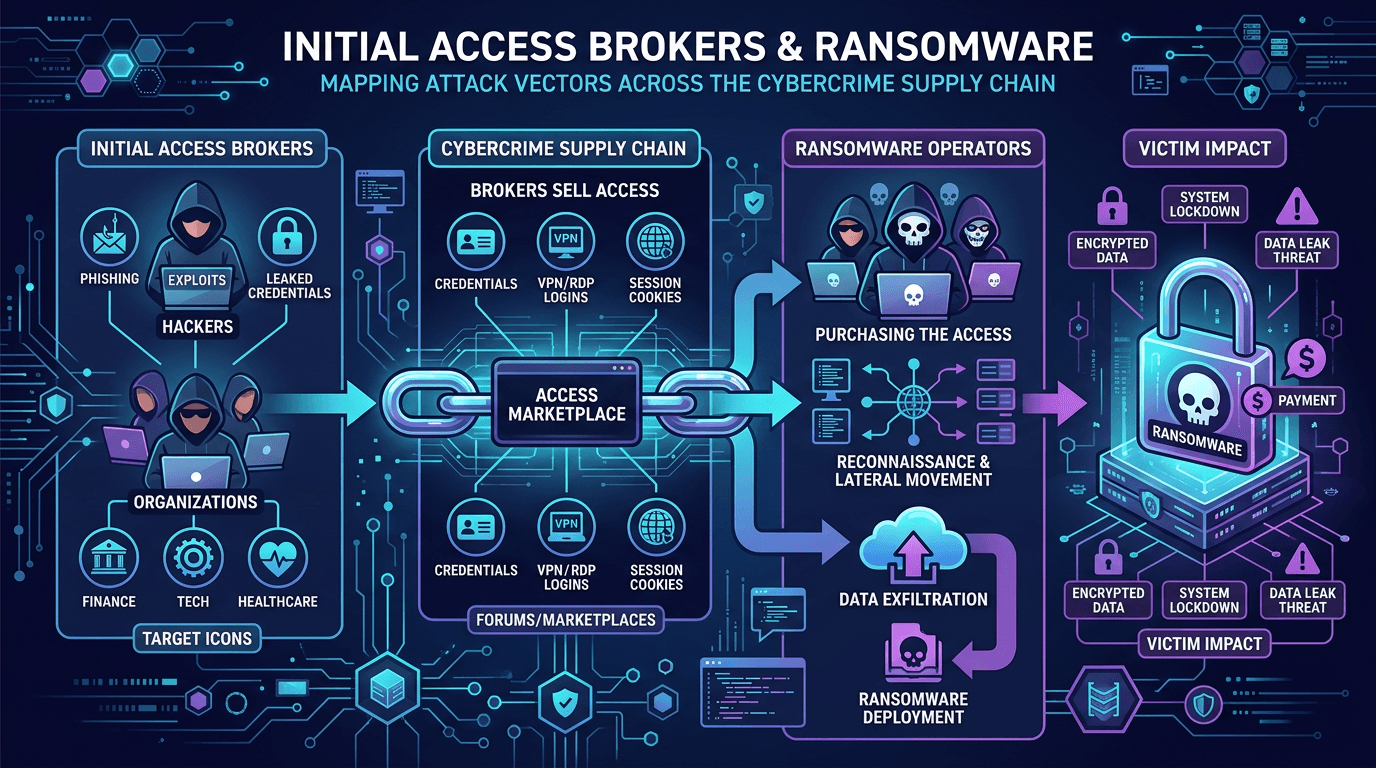
Ransomware operations in 2026 resemble illicit marketplaces more than monolithic hacking groups. Initial access brokers (IABs) occupy a specialized niche: they break in—or buy credentials that let others break in—then sell that foothold to the highest bidder, often a ransomware affiliate seeking a faster path to monetization. This article maps how attack vectors flow through the cybercrime supply chain, how threat intelligence tracks broker activity, and how defenders disrupt economics by raising attacker costs across phishing, CVE exploitation, and identity abuse.
The Supply Chain: From Access to Extortion
A simplified criminal pipeline:
- Access acquisition via phishing, credential stuffing, exploitation of vulnerabilities, or purchasing logs from infostealer malware.
- Broker listing on forums or private channels—advertising company revenue estimates, sector, and persistence mechanisms.
- Affiliate purchase and privilege escalation inside the victim network.
- Data theft, encryption, and extortion communications.
Disrupting any stage reduces expected profits. Law enforcement focuses on takedowns and arrests; defenders focus on prevention and rapid detection.
Common Initial Access Techniques
Brokers diversify to keep inventory fresh:
- Credential theft from phishing pages and infostealer panels—often including session cookies that bypass traditional MFA.
- Exploitation of edge devices—VPNs, firewalls, remote management tools—especially when CVE patches lag.
- Purchased access from other criminals, effectively arbitraging prices across markets.
SEO clusters around “initial access broker” and “ransomware attack chain” attract readers researching crimeware economics—use precise language and avoid sensationalism that misstates technical facts.
Why Ransomware Affiliates Buy Access
Building reliable intrusion capability requires skills in reconnaissance, exploitation, and evasion—not every affiliate possesses them. Purchasing access converts variable upfront work into predictable costs: pay thousands (currency varies) for a foothold that might yield millions in extortion—though outcomes remain uncertain and law enforcement risk is non-zero.
Understanding incentives clarifies defensive priorities: if broker markets prize Active Directory domain access, hardening identity systems yields outsized returns.
Threat Intelligence Signals of Broker Activity
Analysts monitor:
- Forum posts advertising “access” with sector tags.
- Sudden spikes in malicious IP scanning aligned with known broker tooling.
- Patterns of domain registrations used for staging remote access trojans.
Commercial threat intelligence may provide actor-specific reporting; open sources require careful verification. Cross-reference broker claims with your external attack surface—unexpected RDP exposure might validate a worrying listing.
Network reputation services such as isMalicious help analysts prioritize IPs and domains observed during broker-related investigations without manually aggregating dozens of passive DNS sources.
Mapping Broker TTPs to MITRE ATT&CK
Broker tradecraft maps across initial access, credential access, and persistence tactics. Purple teams should simulate broker-style opportunistic scanning plus targeted phishing—many enterprises over-invest in malware while under-investing in stolen session tokens.
Defensive Controls: Raising Broker Costs
Effective controls include:
- Phishing-resistant MFA (FIDO2/WebAuthn) to reduce cookie replay viability where supported.
- Rigorous patch SLAs for internet-facing systems, informed by KEV and EPSS data for CVE prioritization.
- Zero Trust network access replacing broad VPN trust assumptions.
- Privileged access workstations and just-in-time admin to slow lateral movement post-access purchase.
- Outbound monitoring to catch beaconing to novel domains and bulletproof hosts.
Incident Response Considerations
If intelligence suggests your organization appeared in broker markets, initiate high-priority hunts: validate credential resets, review VPN logs for unusual geographies, search for new local accounts. Engage law enforcement channels appropriate to your jurisdiction.
Communicate carefully with executives—unverified forum claims may be scams or recycled old data. Pair intelligence with internal evidence.
Legal and Ethical Monitoring
Monitoring criminal forums walks a fine line; ensure your program complies with local computer misuse and surveillance laws. Many organizations rely on vendor-collected intelligence rather than direct forum participation.
Economics and Insurance
Cyber insurance questionnaires increasingly ask about identity posture and remote access hygiene—controls that also deter brokers. Underwriters may differentiate organizations with verified MFA rollouts and segmented networks.
Reducing Identity Sprawl
Brokers exploit stale service accounts and over-permissioned third parties. Regular access reviews and lifecycle management for contractors shrink the inventory of sellable credentials.
Collaboration with Brand Protection and Fraud Teams
Credential phishing hurts customers and employees alike. Joint operations between security and marketing/fraud teams accelerate domain takedowns of lookalike properties used to harvest passwords—cutting broker supply.
Tabletop Exercise: Simulated Broker Sale
Run a tabletop where threat intel reports a broker advertisement referencing your company name (sanitized exercise). Test procedures: who validates? who decides containment? how do you communicate with legal? Lessons improve real readiness.
Measuring Progress
Metrics might include: reduction in successful phishing sessions, mean time to patch critical CVEs on edge devices, percentage of admin actions requiring phishing-resistant MFA, and volume of blocked remote access attempts from high-risk IPs.
Common Misunderstandings
- All ransomware groups operate uniformly — affiliate models vary; some develop in-house access teams.
- Brokers always tell the truth — scams and exaggerated claims exist; verification matters.
- Blocking one IOC stops brokers — they rotate infrastructure; defense must be systemic.
Conclusion
Initial access brokers intensify ransomware risk by industrializing intrusion. Fight back with identity-first security, disciplined vulnerability management, and threat intelligence that converts forum noise into prioritized hunts and hardening projects. The goal is not moral persuasion of criminals—it is raising their costs until your organization becomes a less attractive target than the next.
Long-form content that explains criminal economics responsibly—without glorifying attackers—earns backlinks from researchers and educates defenders searching “IAB ransomware defense.”
Extended Analysis: Regional and Sector Variations
Broker inventory pricing fluctuates with geopolitical events and law enforcement pressure. Energy, healthcare, and professional services frequently appear in listings—not solely due to willingness to pay ransoms, but because heterogeneous IT stacks create exploitable gaps. Tailor threat intelligence monitoring to sector-specific attack vectors and regulatory reporting obligations.
Technical Deep Dive: Infostealer Logs and Session Cookies
Modern brokers traffic in logs from malware that exfiltrates browser data. Defenses must include endpoint hygiene, application hardening, and rapid session revocation processes when credentials leak. Treat leaked sessions as incidents—not mere password resets.
Partnerships and Information Sharing
ISACs sometimes distribute sanitized indicators tied to broker campaigns. Participate actively; collective defense raises costs across the ecosystem.
Looking Ahead: Law Enforcement and Platform Takedowns
Periodic forum takedowns disrupt markets temporarily; brokers migrate. Assume continuous adaptation—your security program should not depend solely on external disruption.
Bridging to File-Based Indicators
Broker-delivered implants may arrive as signed or unsigned binaries—file hash intelligence still matters for detection engineering, especially when paired with behavioral analytics as hashes rotate.
Cloud and SaaS Attack Paths Brokers Exploit
As workloads migrate, brokers adapt: compromised OAuth applications, overprivileged service principals, and exposed cloud metadata services become new merchandise. Cloud detection requires identity-centric logging (sign-in risk, anomalous consent grants) alongside traditional network telemetry. Threat intelligence feeds that include malicious IP ranges scanning cloud APIs complement domain reputation checks for phishing landing pages targeting Microsoft 365 and Google Workspace users.
Supply Chain and Third Parties
Brokers also sell access obtained via vendor compromises—your supply chain risk is their inventory. Vendor risk assessments should include incident history and remote access practices; contractual clauses mandating phishing-resistant MFA for support accounts reduce downstream exposure.
Communications and PR Preparedness
If broker chatter becomes public news, coordinate technical validation with communications teams. Premature statements damage credibility; delayed statements frustrate stakeholders. Pre-draft holding statements and factual checklists—without specific victim names in templates—to accelerate responsible responses.
Detection Engineering Priorities for Broker-Like Activity
Prioritize alerts combining geographically improbable VPN logins, new device registrations, and subsequent lateral movement tool execution. Tune baselines seasonally—travel and mergers shift normal patterns.
Intelligence Sharing with Law Enforcement
When legally permissible, sharing indicators from broker investigations helps global disruption efforts. Understand evidentiary requirements before exporting logs; chain of custody matters if cases proceed to prosecution.
Security Awareness: Beyond Phishing Simulations
Train users specifically on session theft risks—approve sign-in prompts only when initiating login, avoid password reuse, and report unusual MFA prompts. Awareness content ranks well in internal portals when refreshed with current threat actor narratives.
Budgeting for Identity Infrastructure
Investments in SSO hardening, PAM, and lifecycle automation often outperform incremental EDR spend when broker risk dominates. Frame proposals with broker marketplace economics—executives grasp supply-and-demand metaphors.
Research Ethics and Responsible Disclosure
Researchers studying broker markets must avoid facilitating harm—publishing step-by-step exploit recipes crosses ethical lines. Corporate blogs should model responsible tone: educate defenders without enabling offenders.
Cross-Linking Internal Playbooks
Link broker response procedures to general ransomware IR playbooks and CVE emergency patch processes—analysts navigate faster when documents interconnect.
KPI Dashboards for Executive Review
Show trendlines: phishing click rates, MFA adoption, mean time to contain suspected broker access, and external attack surface changes (new exposed services). Visual narratives sustain executive attention better than one-off incident stories.
Why This Topic Matters for Organic Search
Queries combining “initial access,” “ransomware,” and “defense” indicate high-intent readers—CISOs building board briefings, journalists seeking accurate context, and students entering cybersecurity. Comprehensive articles earn featured snippets when structured with clear definitions and bullet summaries.
Final Operational Reminder
Brokers profit from frictionless resale. Increase friction through segmentation, monitoring, and rapid credential rotation—make access hard to monetize at scale, and many adversaries move on to softer targets.
Purple Team Scenario: Credential Stuffing to RDP
Simulate password spray against exposed management interfaces (in a controlled lab), then lateral movement using purchased “access” assumptions. Debrief with identity and network teams; translate lessons into conditional access policies and firewall rules that block unexpected geographies for admin paths.
Continuous Improvement Loop
After each hunt or incident touching broker tradecraft, update detection content, threat intelligence briefings, and awareness modules. Adversaries iterate weekly; annual training alone cannot keep pace.
Document wins: when a control blocks broker-style access, share metrics internally—success stories fund the next round of identity investments faster than fear alone. Momentum matters.
Frequently asked questions
- What is an initial access broker?
- An initial access broker (IAB) is a cybercriminal who sells network access—often remote desktop or VPN access, stolen credentials, or webshells—to other criminals such as ransomware affiliates.
- Why do ransomware groups use brokers instead of hacking directly?
- Specialization improves efficiency. Some affiliates focus on encryption and extortion while brokers continuously scan for exposed services and stolen credentials, reducing time-to-compromise for the downstream operator.
- What defenses most effectively disrupt IAB business models?
- Phishing-resistant MFA, robust patching for internet-facing systems, network segmentation, egress monitoring, and strong identity governance reduce the inventory of sellable access brokers rely on.
Related articles
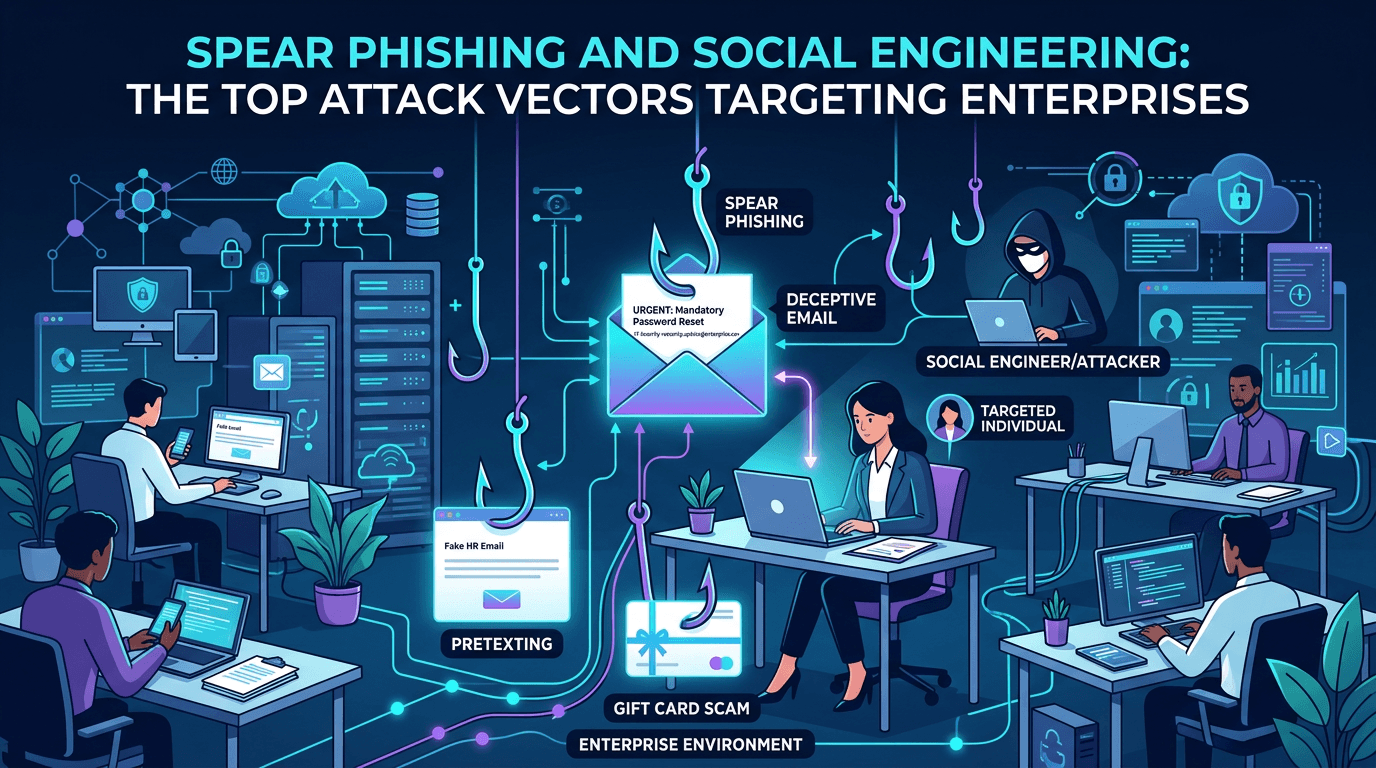 Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
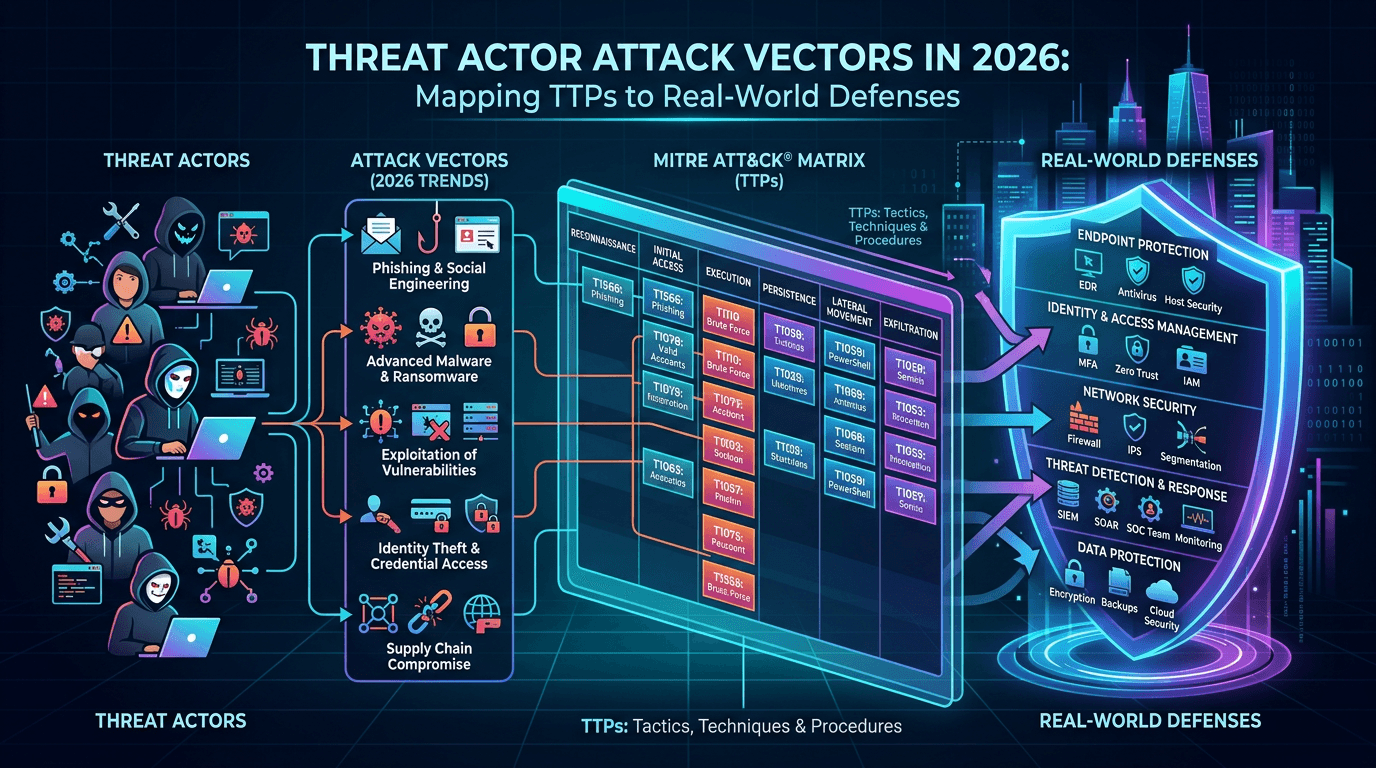 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
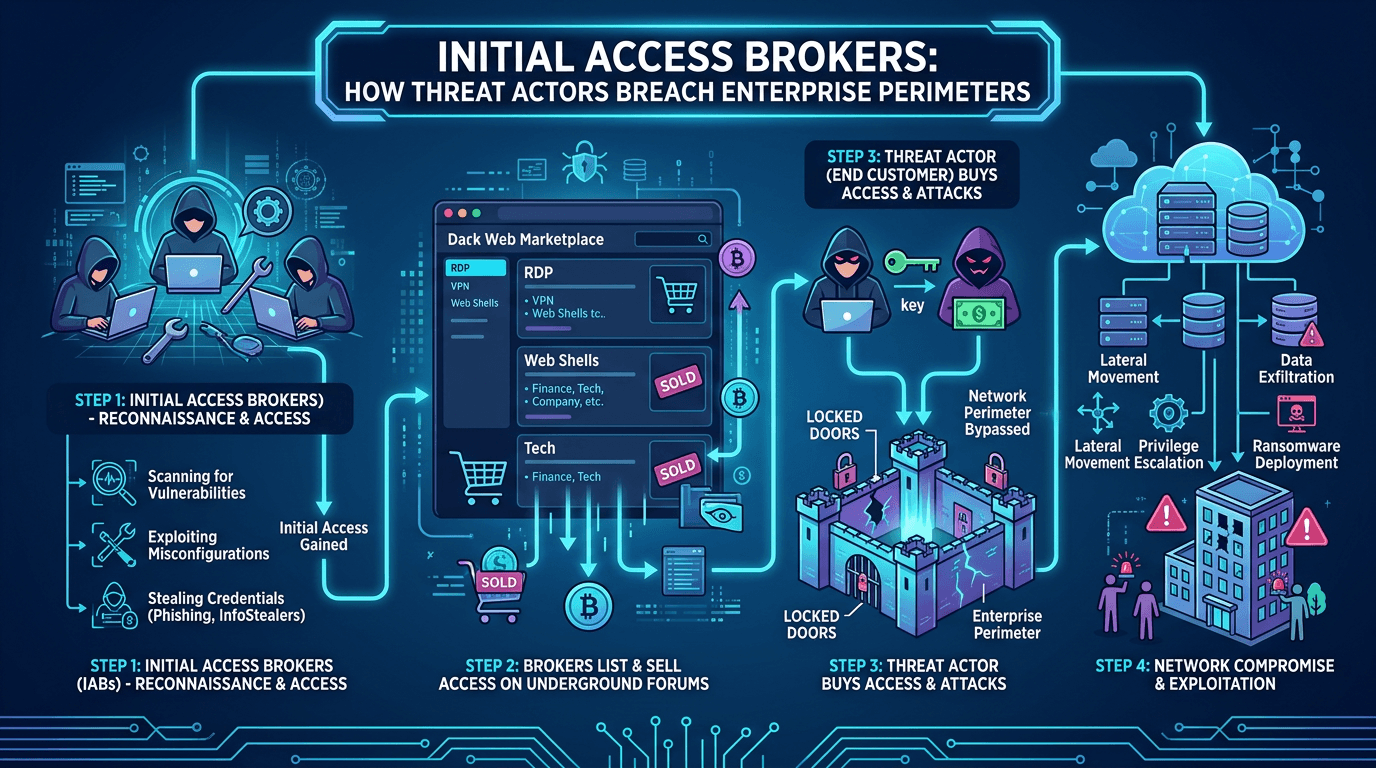 Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026
Apr 20, 2026Initial Access Brokers: How Threat Actors Breach Enterprise Perimeters in 2026A deep dive into initial access brokers (IABs)—the cybercrime specialists who sell footholds into corporate networks—covering their techniques, pricing, detection signals, and how to defend against the top attack vectors they exploit.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker