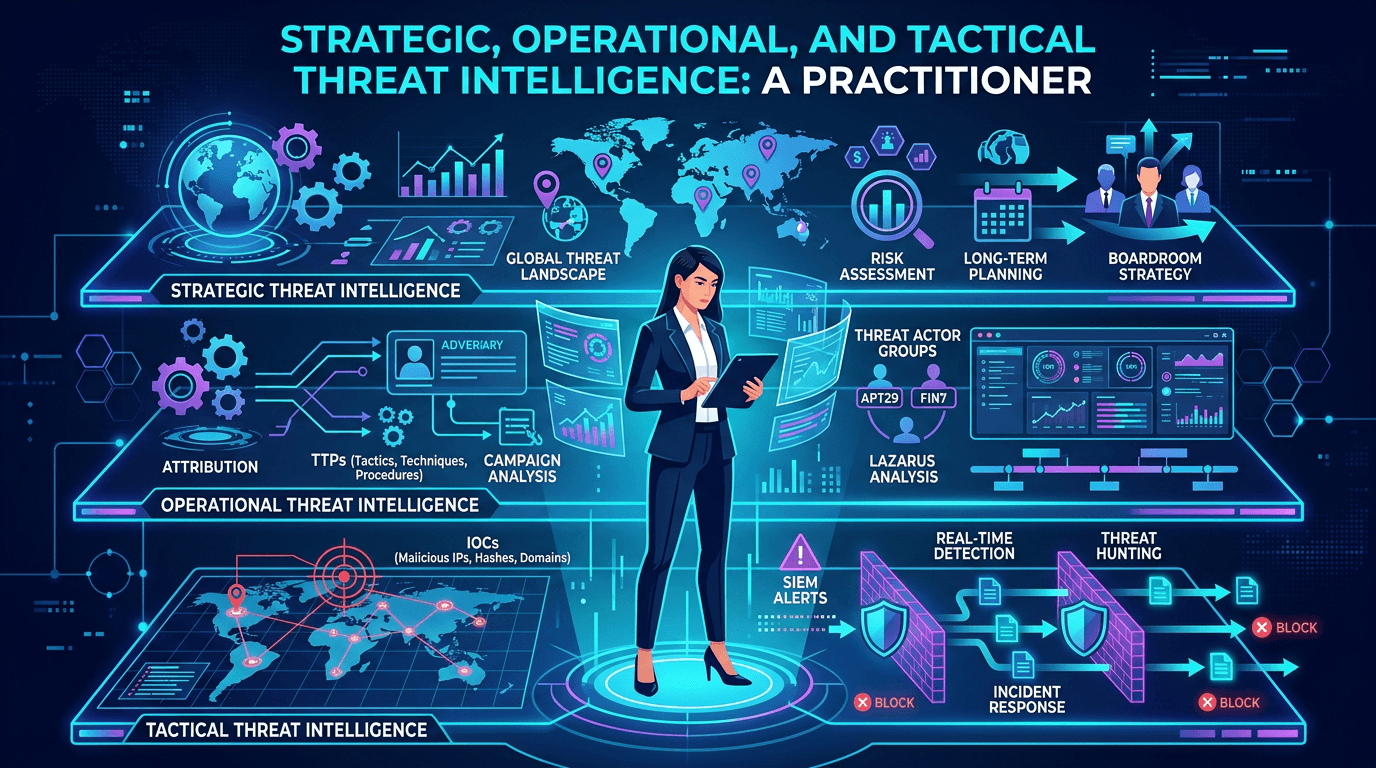
Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
Threat intelligence is one of the most overused phrases in cybersecurity—and one of the most misunderstood. Executives buy it to feel informed, engineers import feeds to check a compliance box, and analysts inherit mailing lists of vendor PDFs no one reads. None of that is threat intelligence. Real cyber threat intelligence (CTI) is a coherent program that produces decision-ready information at three complementary levels: strategic, operational, and tactical. Each serves different audiences, outputs different artifacts, and demands different sources. This guide explains how to build, consume, and measure each layer—and how to stitch them together into a CTI function that delivers value from the boardroom to the SOC console.
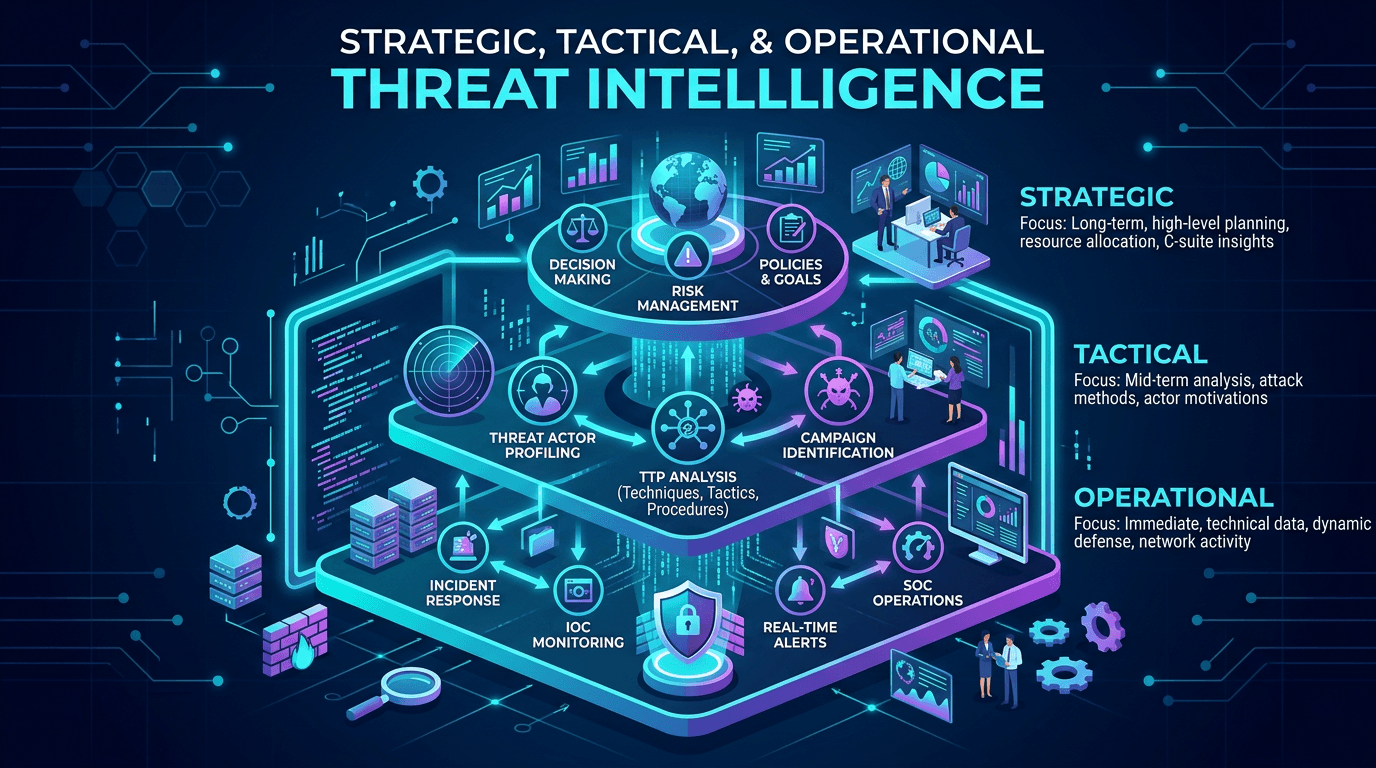
Why the Three-Level Model Matters
The strategic / operational / tactical split is not academic. It prevents two recurring failure modes in intelligence programs:
- Flooding executives with indicators they cannot act on.
- Burying analysts in narrative reports when they need machine-readable data.
By aligning output type to audience and decision horizon, the model lets a CTI team deliver the right artifact to the right consumer at the right moment. It also lets you scope tooling, feed subscriptions, and staffing rationally, rather than buying a platform and hoping value emerges.
Search demand for strategic threat intelligence, operational threat intelligence, and tactical threat intelligence remains strong because practitioners repeatedly encounter these terms in sales decks, job descriptions, and frameworks like MITRE ATT&CK without a unified explanation. Clarifying the model—internally and externally—is one of the simplest ways to elevate a CTI program’s visibility.
Strategic Threat Intelligence: Context for Decision-Makers
Strategic threat intelligence addresses the “why” and “who” of cyber risk. It informs executives, boards, risk committees, and senior security leadership making long-horizon decisions: where to invest, which business units carry elevated risk, how geopolitical developments might translate into cyber campaigns, and which regulatory shifts to anticipate.
Typical strategic outputs include:
- Quarterly or semi-annual threat landscape reports for the board.
- Industry-specific briefings on which threat actors target your sector.
- Geopolitical analyses tying state-sponsored activity to supply chain or partner risk.
- Post-incident strategic assessments—what an intrusion implies about attacker interest and sophistication.
Consumers expect narrative, written-English outputs, usually delivered as slide decks, memos, or structured reports. Strategic analysts often have backgrounds in intelligence studies, international relations, or enterprise risk. Their sources are not limited to technical feeds; they include open-source geopolitical analysis, vendor research reports, ISAC and ISAO publications, law enforcement advisories, academic research, and trusted peer exchanges.
The KPI for strategic CTI is not the number of indicators produced. It is the number of material decisions influenced: budget approvals for a new detection platform because the landscape report justified it, or a business pivot delayed because threat intelligence flagged an actor targeting that line of work.
Operational Threat Intelligence: Campaigns, Actors, and Current Activity
Operational threat intelligence sits between strategic narrative and tactical data. It describes how specific adversaries are currently operating—campaigns, TTPs (tactics, techniques, and procedures), infrastructure overlaps, and victim patterns. The audience is security operations leadership, incident response teams, threat hunters, and detection engineers.
Operational outputs include:
- Campaign analyses: Detailed writeups of active operations, linking actors, infrastructure, malware families, and targeted sectors.
- TTP updates: What a known actor changed in their toolkit last quarter, mapped to MITRE ATT&CK techniques.
- Sector-specific alerts: “Ransomware group X is currently targeting regional hospitals—watch for these behaviors.”
- Disruption reports: Law enforcement takedowns, vendor-driven infrastructure sinkholes, and their implications for ongoing monitoring.
Consumers need enough technical detail to build detections and hunt hypotheses but also enough narrative to brief leadership and prioritize effort. Effective operational CTI teams combine proprietary telemetry, paid threat intelligence subscriptions, open-source research, malware sandbox data, OSINT collection, and relationships with information-sharing communities.
Operational intelligence often drives the creation of detection content. When a campaign report describes a new PowerShell technique used by a threat actor, the detection engineering team translates it into EDR rules, SIEM queries, and threat-hunting playbooks—a concrete bridge from narrative to prevention.
Tactical Threat Intelligence: Indicators You Can Block Today
Tactical threat intelligence is the machine-readable layer: indicators of compromise (IOCs) consumed directly by security tools. IPs, domains, URLs, file hashes, SSL fingerprints, mutexes, registry keys, and email addresses flow through tactical feeds into firewalls, EDR platforms, email gateways, and SIEMs.
Tactical outputs include:
- Continuous IOC feeds via STIX/TAXII or vendor APIs.
- Curated blocklists for malicious IPs, domains, and URLs.
- YARA rules and Sigma rules for file and log detection.
- File hash reputation lookups accessed during investigations.
The audience is tooling: detection engines, automation workflows, SOAR playbooks. Humans rarely read tactical feeds line by line. The KPI is coverage and freshness: how quickly a newly observed malicious indicator flows from discovery to enforcement, and how effectively feeds are correlated across sources to avoid noise.
Services like isMalicious specialize in tactical intelligence—real-time reputation for domains, IPs, and URLs—feeding this layer with data curated from many underlying sources. Effective tactical programs aggregate multiple feeds, deduplicate indicators, score confidence, and expire stale entries aggressively to prevent alert fatigue.
How the Three Layers Work Together
Healthy CTI programs connect the layers so that each informs the others:
- Strategic → Operational: A landscape report identifies a state-sponsored actor newly targeting your sector; operational CTI prioritizes monitoring for that actor’s TTPs.
- Operational → Tactical: A campaign analysis yields concrete IOCs that flow into blocklists and detection rules.
- Tactical → Operational: A cluster of blocked IOCs suggests a new campaign, prompting operational analysis.
- Operational → Strategic: Multiple campaigns sharing traits reveal broader adversary intent, updating the strategic picture.
When these feedback loops work, the program ceases to be a collection of disconnected feeds and becomes a coherent system producing intelligence about your environment, not just about the internet.
Sources of Threat Intelligence Across the Layers
Source selection is where many programs go wrong—either overpaying for redundant feeds or failing to diversify across source types. A balanced source portfolio includes:
- Commercial threat intelligence vendors for curated, high-confidence indicators and analyst-driven reports.
- Open-source intelligence (OSINT): Security researcher blogs, GitHub repositories of malware analyses, Twitter/Mastodon communities, DNS and certificate transparency logs.
- Government and sector-specific sharing: CISA advisories, FBI flash notifications, ISAC and ISAO communities.
- Internal telemetry: EDR, SIEM, network logs, and sandbox detonations from your own environment.
- Partner and peer exchanges: Bilateral intelligence sharing with trusted industry peers and vendors.
- Darknet and cybercrime forums monitoring: Specialist collection of actor communications, leak sites, and initial access broker listings.
A well-designed CTI function tags each source with confidence metadata and feeds that tagging into downstream correlation. Not every OSINT tweet warrants the same trust as a confirmed ISAC alert.
Operationalizing CTI: From Collection to Action
A production-grade CTI program follows a loop, often described as the intelligence cycle:
- Direction: Stakeholders articulate intelligence requirements—what decisions need support?
- Collection: Sources are tasked and ingested.
- Processing: Raw data is normalized, deduplicated, and enriched.
- Analysis: Analysts turn data into intelligence, producing artifacts at each level.
- Dissemination: Reports, dashboards, and feeds reach the right audiences.
- Feedback: Consumers report whether the intelligence helped, refining direction.
Skipping feedback is the most common failure. A CTI team that produces reports without knowing who reads them cannot improve targeting. Even a lightweight quarterly survey of consumers—“Which reports changed a decision?”—tightens the cycle.
Integrating CTI With SOC and Incident Response
Tactical and operational CTI must meet the SOC where it already works. Practical integrations include:
- Alert enrichment: Every SIEM alert referencing an IP, domain, or hash is automatically enriched with reputation and campaign context before it reaches an analyst.
- Detection engineering backlog: Operational CTI reports generate prioritized detection engineering tasks mapped to MITRE ATT&CK.
- Threat hunt sprints: CTI provides fresh hypotheses each sprint—“Search for actor X’s new PowerShell loader”—with IOCs and behavioral patterns.
- Incident response playbooks: When a specific campaign is confirmed, a playbook pre-loaded with CTI context accelerates scoping and containment.
The goal is to remove friction: an analyst should never manually paste an indicator into a lookup service when automation can do it instantly and attach the context to the ticket.
Common Pitfalls in Threat Intelligence Programs
Recurring mistakes that undermine CTI value:
- Feed accumulation without pruning: Subscribing to many feeds produces noise, not insight. Measure feed value and cut low performers.
- No differentiation between levels: Delivering tactical indicators to executives or strategic narrative to SIEMs wastes effort.
- Missing requirements: Without documented intelligence requirements, collection is opportunistic and dissemination is random.
- Poor confidence scoring: Treating every indicator as equally true produces false positives at scale.
- One-way flow: Ignoring internal telemetry as a source misses the richest intelligence about your adversaries.
Measuring Threat Intelligence Value
Quantifying CTI impact is difficult but possible. Useful metrics include:
- Mean time to detect (MTTD) for CTI-flagged threats vs. un-flagged.
- Percentage of incidents with pre-existing CTI context.
- Feed precision and recall at each confidence tier.
- Reporting influence: Number of strategic decisions explicitly citing CTI.
- Detection coverage against top threat actor TTPs (measured via purple-team exercises).
Pairing these metrics with stakeholder feedback creates a CTI program that can defend its budget and expand its scope over time.
CTI and Infrastructure Reputation
Tactical threat intelligence leans heavily on infrastructure reputation: the ability to determine whether an IP, domain, or URL has a history of malicious behavior. Services that aggregate thousands of underlying sources and provide real-time reputation scoring are among the most efficient ways to enrich every alert at scale. isMalicious focuses on this layer, delivering programmatic reputation data that integrates with SIEMs, SOAR, and custom automation.
Combining infrastructure reputation with behavioral operational intelligence—actor TTPs, campaign dynamics, victimology—produces the richest picture of risk. Neither layer alone is sufficient; both together form the core of modern CTI operations.
Conclusion
Strategic, operational, and tactical threat intelligence are not marketing segments—they are distinct functions with different audiences, outputs, and success criteria. Mature programs invest in all three and connect them through feedback loops that turn raw data into executive insight, operational focus, and automated prevention.
If your CTI program still struggles to articulate what it produces and for whom, adopt the three-layer model as an internal north star. Document intelligence requirements for each audience, align source portfolios accordingly, and measure outcomes at every level. Pair strategic analysis with operational campaign tracking and real-time tactical feeds from providers like isMalicious, and your threat intelligence function will earn its place in the security budget year after year.
Frequently asked questions
- What is the difference between strategic and tactical threat intelligence?
- Strategic threat intelligence addresses long-term risk and attacker motivation for executive decision-makers, typically in the form of written reports and briefings. Tactical threat intelligence focuses on machine-readable indicators of compromise—IPs, domains, URLs, file hashes—that SOC analysts and detection engineers can consume directly.
- Do small teams need all three levels of threat intelligence?
- Yes, but the investment scales. Even a small team benefits from strategic context (what threats matter to our industry?), operational signals (what campaigns are active?), and tactical feeds (what do I block today?). The volume and formality grow with team size, but the logical layers exist in every mature program.
- How do I measure the ROI of a threat intelligence program?
- Measure outcomes at each level: strategic decisions influenced, operational campaigns detected before damage, and tactical indicators blocked. Useful KPIs include mean time to detect, mean time to contain, percentage of incidents with prior CTI context, and CTI-attributable prevention savings.
Related articles
 Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security Programs
Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security ProgramsAlign CTI outputs with audience needs: executive risk narratives, SOC-ready IOCs, and MITRE-mapped TTPs—plus governance models that keep intelligence timely and measurable.
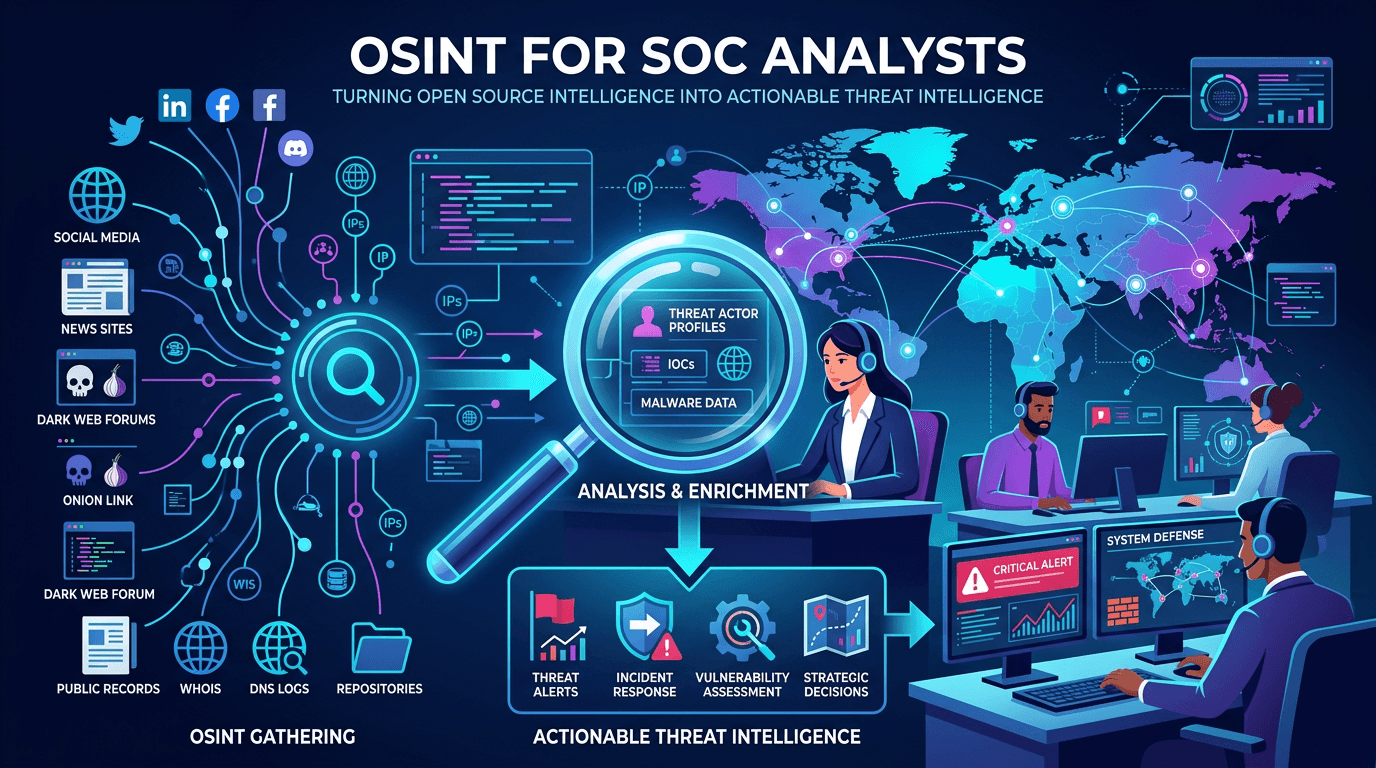 Apr 23, 2026OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat Intelligence
Apr 23, 2026OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat IntelligenceA complete guide to open source intelligence (OSINT) for security operations—tools, techniques, workflows, and legal considerations for collecting, analyzing, and operationalizing open threat data in a modern SOC.
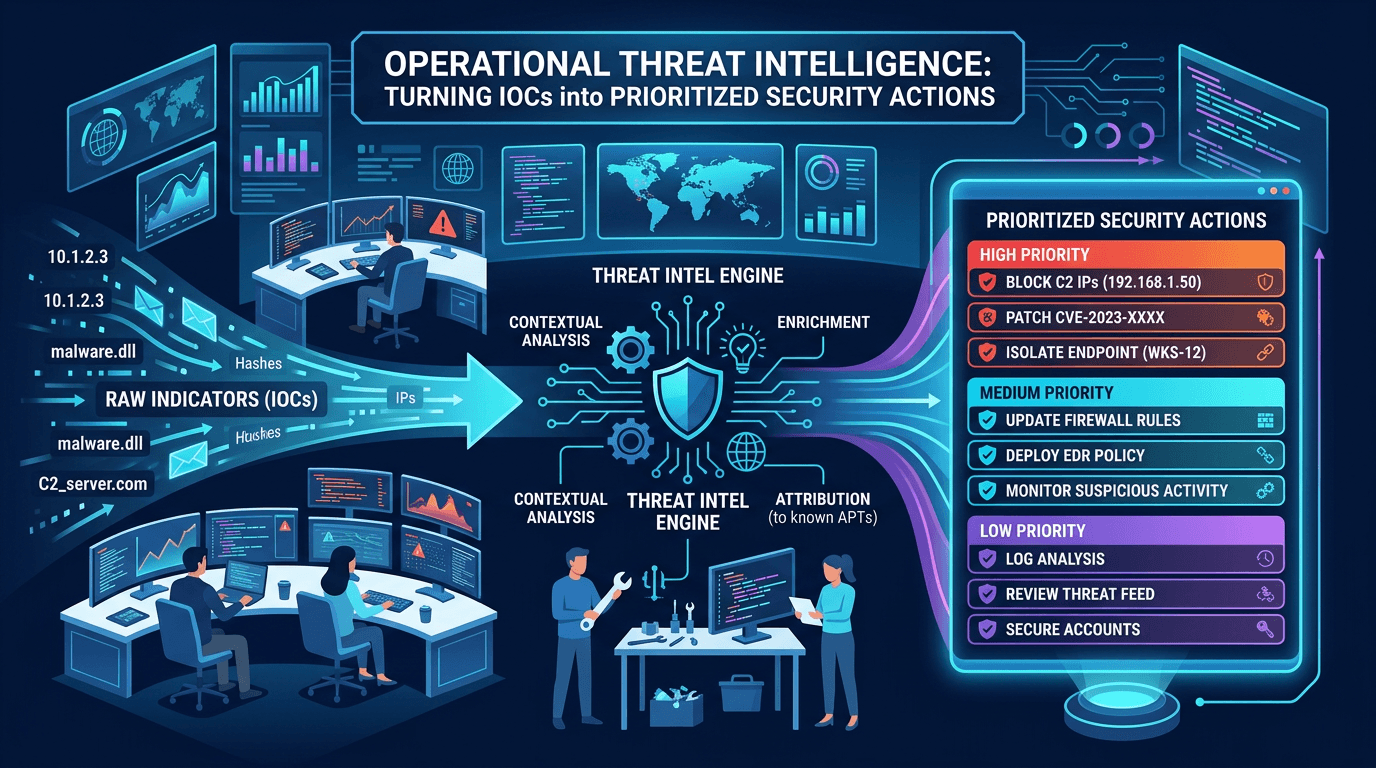 Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security ActionsDefine operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker