OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat Intelligence
A complete guide to open source intelligence (OSINT) for security operations—tools, techniques, workflows, and legal considerations for collecting, analyzing, and operationalizing open threat data in a modern SOC.
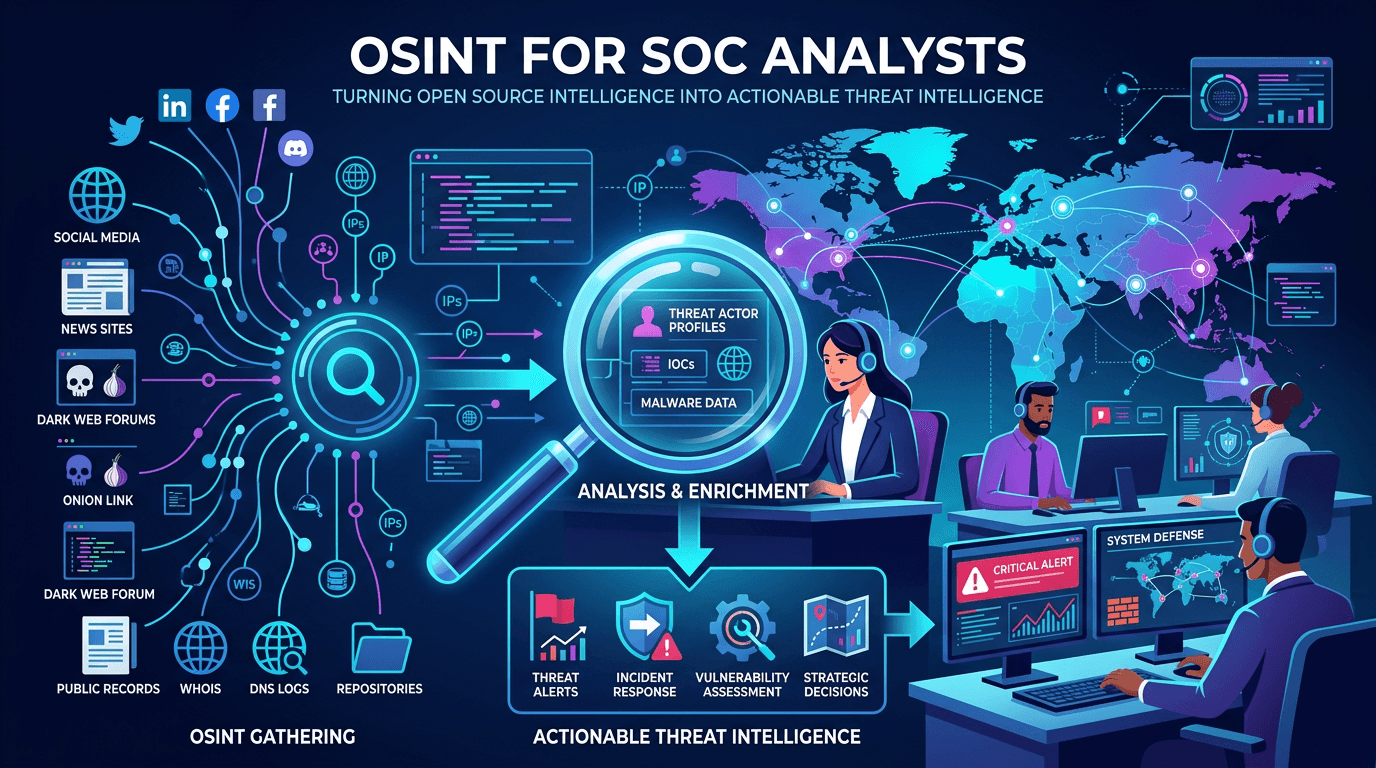
Open Source Intelligence (OSINT) is one of the most powerful and underused capabilities in a modern security operations center. Every day, security researchers, vendors, government agencies, and practitioners around the world publish vast quantities of data—malware analyses, indicator lists, vulnerability research, campaign reports, and infrastructure telemetry—that any SOC can legally and cheaply incorporate into its threat intelligence workflow. This guide explains OSINT end to end: what it is, which sources deliver the most value, how to build an OSINT workflow that survives analyst turnover, and how to integrate open signals with commercial cyber threat intelligence (CTI) and internal telemetry.
What OSINT Means for Security Operations
OSINT is the discipline of collecting and analyzing information that is publicly available—intentionally published or accessible without bypassing access controls. In cybersecurity, OSINT covers a huge range of data:
- Security researcher blog posts and whitepapers.
- Vendor advisories and threat reports.
- Government publications (CISA alerts, FBI flash notifications, ENISA reports).
- Indicator feeds hosted on GitHub, paste sites, and public repositories.
- Certificate transparency (CT) logs.
- Passive DNS, WHOIS, and reverse DNS records.
- Malware analysis sandbox databases.
- Dark web forum indexes and leak site monitoring.
- Social media posts from security researchers (Mastodon, X, LinkedIn).
- News reporting and press releases from affected organizations.
The value of OSINT is not any single source but the integration of many sources into a coherent picture. A blog post describing a new ransomware campaign, combined with CT logs revealing newly issued certificates matching the infrastructure pattern, combined with infostealer log analysis from a dark web researcher, can give a SOC a remarkably detailed picture of adversary operations days before the intelligence appears in commercial feeds.
OSINT vs Commercial Threat Intelligence
OSINT and commercial threat intelligence are complementary, not competitive. Commercial providers offer curated data, analyst-written reports, SLAs, and structured feeds. OSINT offers breadth, timeliness, and cost-effectiveness.
A balanced program consumes both:
- Commercial feeds for high-confidence indicators and analyst-driven reports that inform strategic and operational decisions.
- OSINT for fast-moving tactical signals, rapid validation of commercial findings, and niche coverage no vendor provides.
OSINT also enables sovereignty—an organization that depends entirely on commercial vendors for threat intelligence has a single point of failure. A healthy OSINT practice provides independence, which matters particularly in regulated industries or geopolitically sensitive contexts.
Core OSINT Sources for SOC Analysts
1. Security Researcher Communities
Platforms where security researchers publish early findings:
- Mastodon and X (Twitter): The first place many new IOCs appear.
- GitHub: Indicator feeds, YARA rules, proof-of-concept exploits, malware analyses.
- Blogs from major vendors and independent researchers: Deep technical writeups with campaign-level detail.
Build a curated follow list and push it into an RSS or ingestion pipeline. Stale follow lists are one of the most common failure modes of OSINT practice.
2. Government and Sector Sharing
Official advisories are high-confidence, often with sector-specific context:
- CISA alerts and the KEV catalog.
- FBI flash notifications and IC3 advisories.
- ENISA reports for European context.
- ISAC and ISAO alerts relevant to your sector.
Ingest advisories automatically and route them to both detection engineering (for new IOC coverage) and leadership (for sector-specific awareness).
3. Certificate Transparency and Passive DNS
Certificate Transparency (CT) logs publish every TLS certificate issued by participating CAs. Pivoting through CT can reveal:
- Newly registered domains matching a brand or a threat actor’s pattern.
- Shared certificate subjects across apparently unrelated infrastructure.
- Timing patterns that suggest coordinated deployments.
Passive DNS data—historical DNS resolutions collected from across the internet—lets analysts reconstruct the evolution of a domain, pivot to related hostnames, and identify staging infrastructure that was active before detection. Combine CT and passive DNS pivots with infrastructure reputation data from services like isMalicious to identify which discovered pivots are worth investigating first.
4. WHOIS and Registration Data
Despite privacy restrictions, WHOIS remains valuable. Patterns in registrant emails, registrar choices, and registration dates often cluster across campaigns. Bulk historical WHOIS services let analysts find sibling domains even when current records are private.
5. Malware Analysis Services
Public sandbox platforms expose a wealth of behavioral data for samples that other researchers submit:
- Process execution graphs.
- Network indicators (domains, IPs, URLs contacted).
- Dropped files and persistence mechanisms.
- Static analysis features.
Analysts pivoting through submitted samples can quickly identify new variants of known families or detect emerging clusters.
6. Paste Sites and Leak Monitoring
Actors regularly publish stolen data, credential dumps, and campaign telemetry to paste sites and leak forums. Monitoring services catch these early:
- Credentials for your domain appearing in a dump is a high-urgency signal.
- Code or secrets from internal repositories on paste sites indicates insider or contractor leakage.
- Victim listings on ransomware leak sites provide early warning for peers in your sector.
7. Dark Web and Cybercrime Forum Monitoring
Dark web forums host a large share of cybercrime activity, including initial access broker listings, malware-as-a-service advertisements, and victim announcements. Dedicated monitoring services or careful in-house collection surface this data safely and legally.
Operational consideration: direct dark web collection requires dedicated, isolated infrastructure, strict operational security, and clear legal guidance. Most organizations outsource at least part of this capability.
Building an OSINT Workflow
Define Intelligence Requirements
An OSINT program without requirements produces noise. Document the intelligence questions your SOC needs answered:
- Which threat actors target our sector?
- Which CVEs are being actively exploited against our technology stack?
- Is our brand appearing in phishing kit infrastructure?
- Are credentials for our domain circulating in infostealer logs?
- Are our executives or employees being targeted in known campaigns?
Each requirement maps to specific sources and collection cadences. Review and update requirements at least quarterly.
Automate Collection Where Possible
Manual OSINT is seductive but rarely sustainable. Automate:
- RSS ingestion from blogs and advisory services.
- GitHub repository watches for relevant projects.
- CT log and passive DNS queries for your brand and infrastructure patterns.
- Paste site monitoring for your domain.
- Social media keyword searches into a central intake.
The goal is that analyst time is spent on analysis, not collection.
Normalize Into a Common Schema
OSINT arrives in every format imaginable—Markdown, PDF, STIX, plain text, screenshots, JSON. Normalize into a consistent structure: source, collected timestamp, raw content, extracted IOCs, confidence, tags. Feed the normalized data into your TIP or SIEM.
Extract IOCs Automatically
Text mining tools can extract hashes, IPs, domains, URLs, and CVE IDs from unstructured OSINT. Couple the extractor with defanging/refanging logic (converting example[.]com to example.com safely) and a validator that rejects false positives like 1.1.1.1 inside version numbers.
Every extracted IOC should be enriched with infrastructure reputation—for example, querying isMalicious for domain or IP verdicts—before it reaches detection engineering. This pre-filters noise and highlights indicators that warrant immediate action.
Apply Confidence and Source Weighting
Not all OSINT is equal. A widely cited research blog post scores higher than an unattributed paste. A confirmed CISA advisory scores higher than a social media rumor. Bake confidence scoring into ingestion and propagate it downstream so automation can treat sources appropriately.
Route to Consumers
Different outputs land in different places:
- Tactical IOCs flow into detection engineering and blocking pipelines.
- Operational insights inform threat hunting and campaign tracking.
- Strategic findings feed executive briefings and risk reporting.
A single OSINT source may contribute to all three layers. Treat each OSINT artifact as a candidate for multiple audiences.
Legal and Ethical Considerations
OSINT collection is generally legal when it respects access controls and data protection rules, but defenders should document policy clearly:
- Do not bypass access controls—no registering fake personas on forums that require verification, no scraping behind login walls you do not legitimately access.
- Respect data protection regulations—particularly for personal data under GDPR, CCPA, and similar regimes.
- Attribute sources—especially when republishing or quoting inside analyst reports.
- Protect sources and methods—if you rely on a specific collection technique, do not broadcast it publicly.
- Document policy—have legal counsel approve an OSINT operating manual and train analysts on it.
When in doubt, ask. An hour of legal review costs far less than the consequences of a sloppy collection decision.
Common OSINT Mistakes in SOCs
Recurring failure patterns:
- Source sprawl without curation—too many feeds, too little quality control.
- Treating OSINT as a substitute for commercial CTI—the two have different jobs.
- Ignoring confidence scoring—acting on low-quality OSINT with high-quality consequences.
- Manual ingestion that breaks when the analyst goes on leave—automate or document thoroughly.
- No feedback loop—sources that consistently underperform should be dropped; sources that consistently produce value should get more investment.
OSINT and Threat Hunting
OSINT is fuel for threat hunting. A researcher’s blog post describing a new loader becomes a hunt hypothesis within hours. Passive DNS and CT pivots generate candidate infrastructure to check against SIEM logs. Paste site monitoring flags credentials to correlate with authentication telemetry. Well-run OSINT programs produce hunt hypotheses weekly that directly shape detection coverage.
This pipeline—from OSINT signal to hunt hypothesis to new detection—embodies the feedback loop that separates mature SOCs from reactive ones.
Integrating OSINT With Infrastructure Reputation
OSINT often surfaces raw IPs, domains, and URLs with limited context. Pairing each OSINT-discovered indicator with reputation data from a dedicated infrastructure provider adds decisive context:
- A new domain mentioned in a researcher’s thread → immediate reputation check → confirmed malicious → automatic blocking.
- An IP observed in passive DNS pivoting → reputation shows long history of C2 activity → escalate.
- A URL from paste site monitoring → reputation indicates phishing kit infrastructure → warn affected users.
isMalicious delivers this kind of reputation-at-scale via API, letting OSINT automation become operational defense in near real time.
Measuring OSINT Program Value
KPIs to track:
- Time from OSINT signal to detection coverage or block.
- Percentage of confirmed incidents with prior OSINT indicators.
- Ratio of OSINT-derived IOCs to total ingested IOCs (shows coverage).
- Analyst hours spent on OSINT vs outputs delivered (shows efficiency).
- Unique value contributions—what did OSINT find that commercial feeds missed?
Measure quarterly and refine. Programs that treat OSINT as measurable infrastructure, not anecdotal effort, consistently outperform those that do not.
Conclusion
OSINT is a cornerstone of modern security operations, not a hobbyist side project. By defining intelligence requirements, curating sources, automating collection, normalizing data, and enriching every indicator with infrastructure reputation from services like isMalicious, SOCs turn the public internet’s daily flood of security data into timely, actionable threat intelligence.
Commercial CTI and OSINT together give defenders the breadth, depth, and independence they need. Programs that invest in both, connect them to SIEM and detection engineering pipelines, and measure outcomes consistently deliver faster detection, earlier warning, and better strategic context—at a cost profile that fits any mature security budget.
Frequently asked questions
- What is OSINT in cybersecurity?
- OSINT (Open Source Intelligence) in cybersecurity refers to the collection and analysis of publicly available information to produce threat intelligence. Sources include security researcher blogs, certificate transparency logs, passive DNS, WHOIS, social media, GitHub repositories, paste sites, dark web forums, and government advisories.
- Is OSINT legal to use in corporate security operations?
- Collection of public information is generally legal, but specifics vary by jurisdiction, source, and context. Certain activities (accessing restricted forums, circumventing access controls, collecting personal data from EU residents) trigger additional legal considerations. Work with legal counsel to document an OSINT policy that your SOC can follow consistently.
- How does OSINT complement commercial threat intelligence?
- OSINT provides breadth and timeliness that commercial feeds may lack, while commercial intelligence provides curation, confidence scoring, and analyst labor. Together they form the most complete picture: OSINT surfaces emerging signals quickly, and commercial intelligence validates and structures the noise.
Related articles
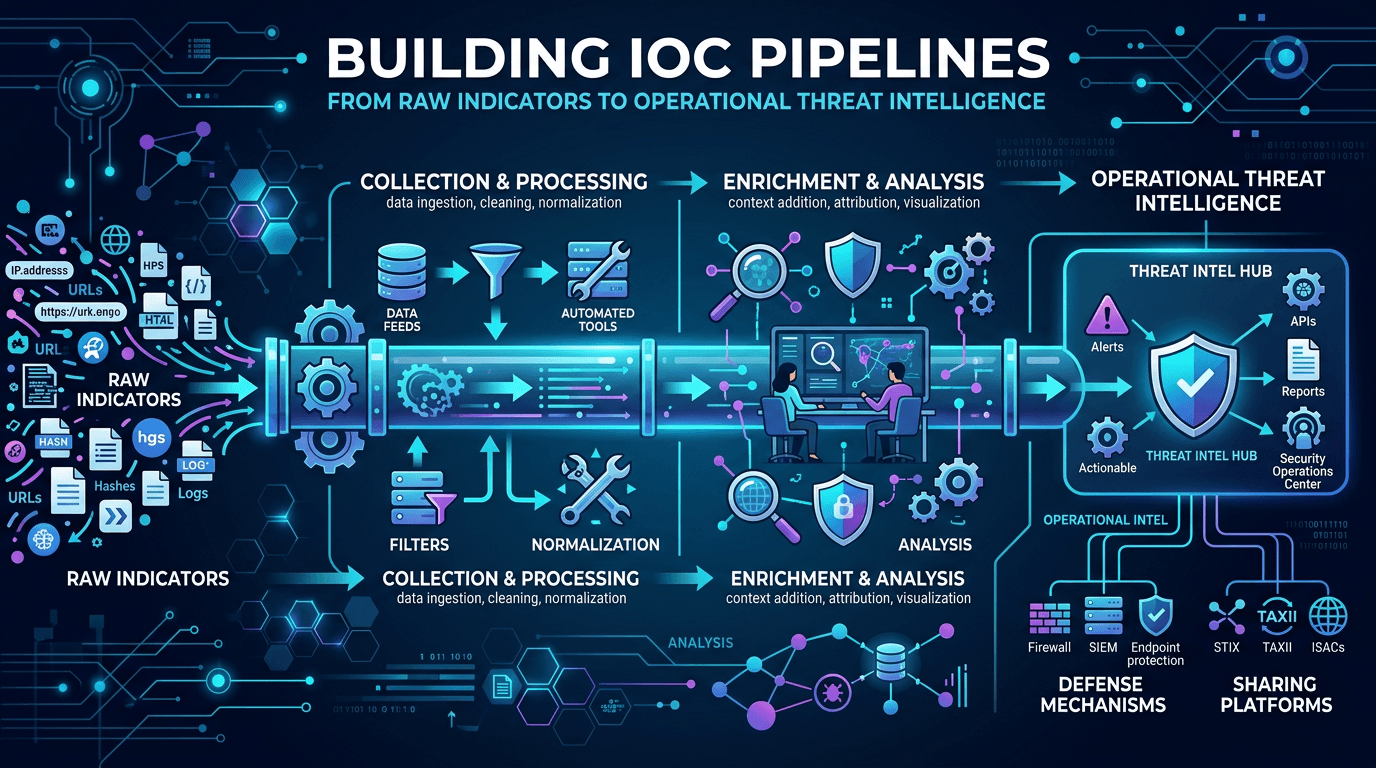 Apr 26, 2026Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026
Apr 26, 2026Building IOC Pipelines: From Raw Indicators to Operational Threat Intelligence in 2026A practical engineering guide to building indicator of compromise (IOC) pipelines—ingestion, normalization, deduplication, enrichment, scoring, distribution, and feedback—to turn raw threat feeds into operational defense.
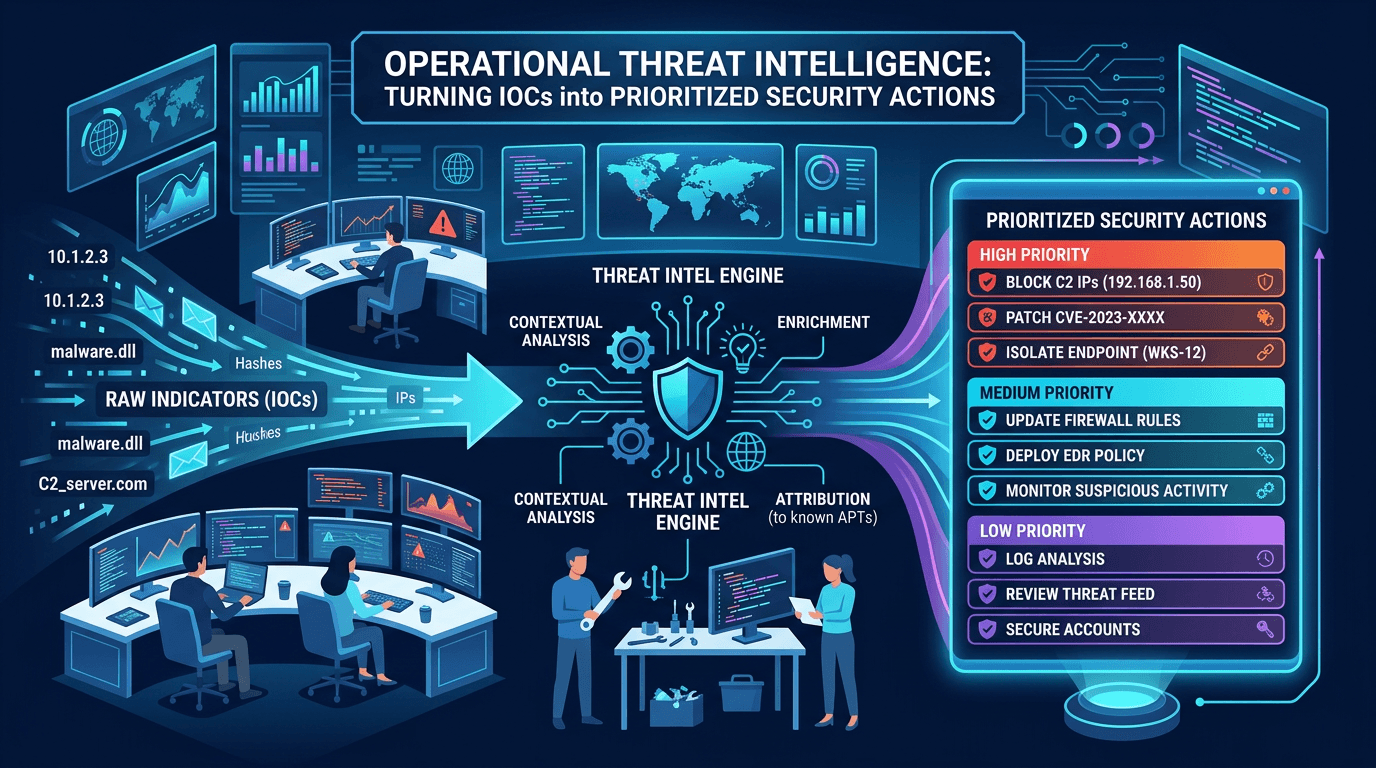 Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security Actions
Apr 19, 2026Operational Threat Intelligence: Turning IOCs into Prioritized Security ActionsDefine operational CTI that SOC teams can use daily: IOC lifecycle, confidence scoring, feed hygiene, and how to align indicators with detection engineering and incident response.
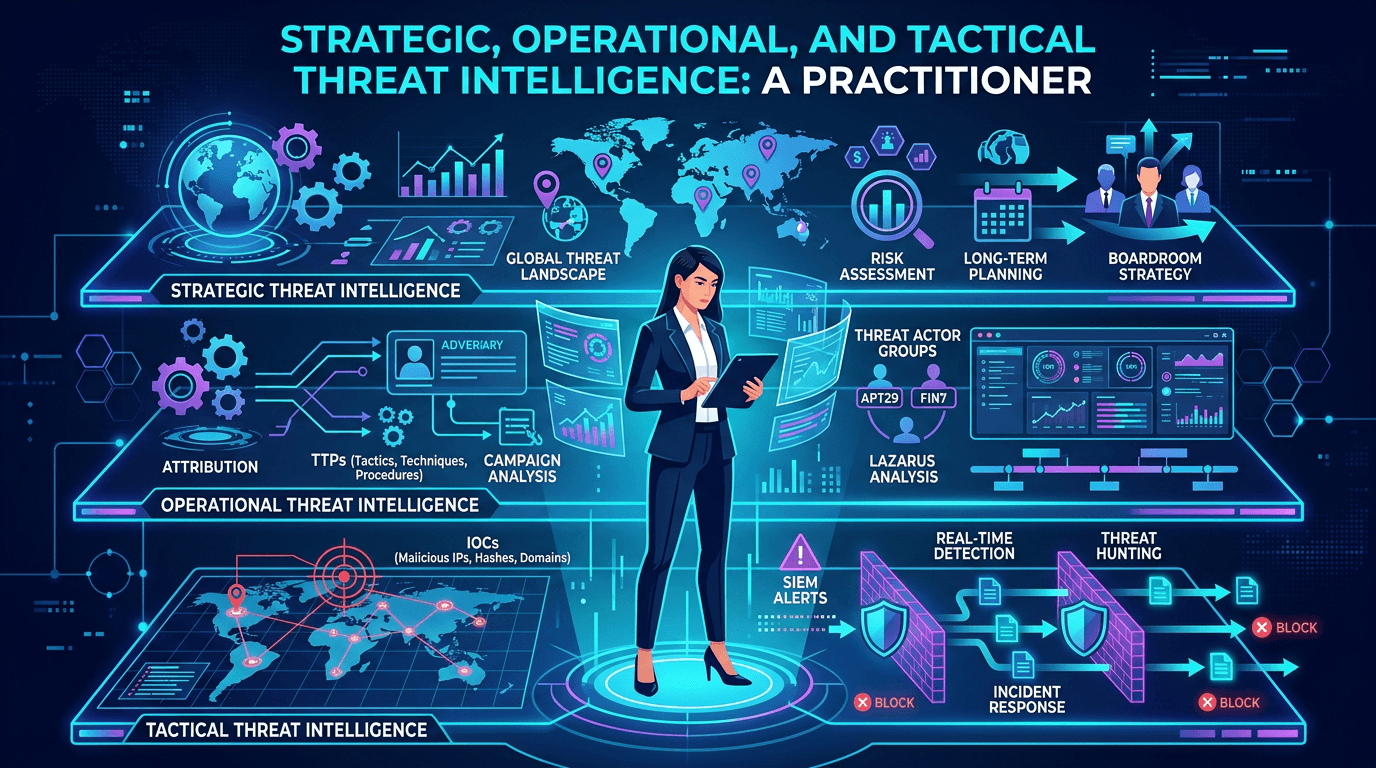 Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026
Apr 19, 2026Strategic, Operational, and Tactical Threat Intelligence: A Practitioner's Framework for 2026A complete guide to the three levels of threat intelligence—strategic, operational, and tactical—with practical examples of consumers, outputs, feeds, and how to connect them into a coherent CTI program.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker