Incident Response Playbooks: Less PDF, More Rehearsal
A playbook nobody has run is fiction. Learn how to build IR phases, roles, and communications that work under pressure—and how to test them.
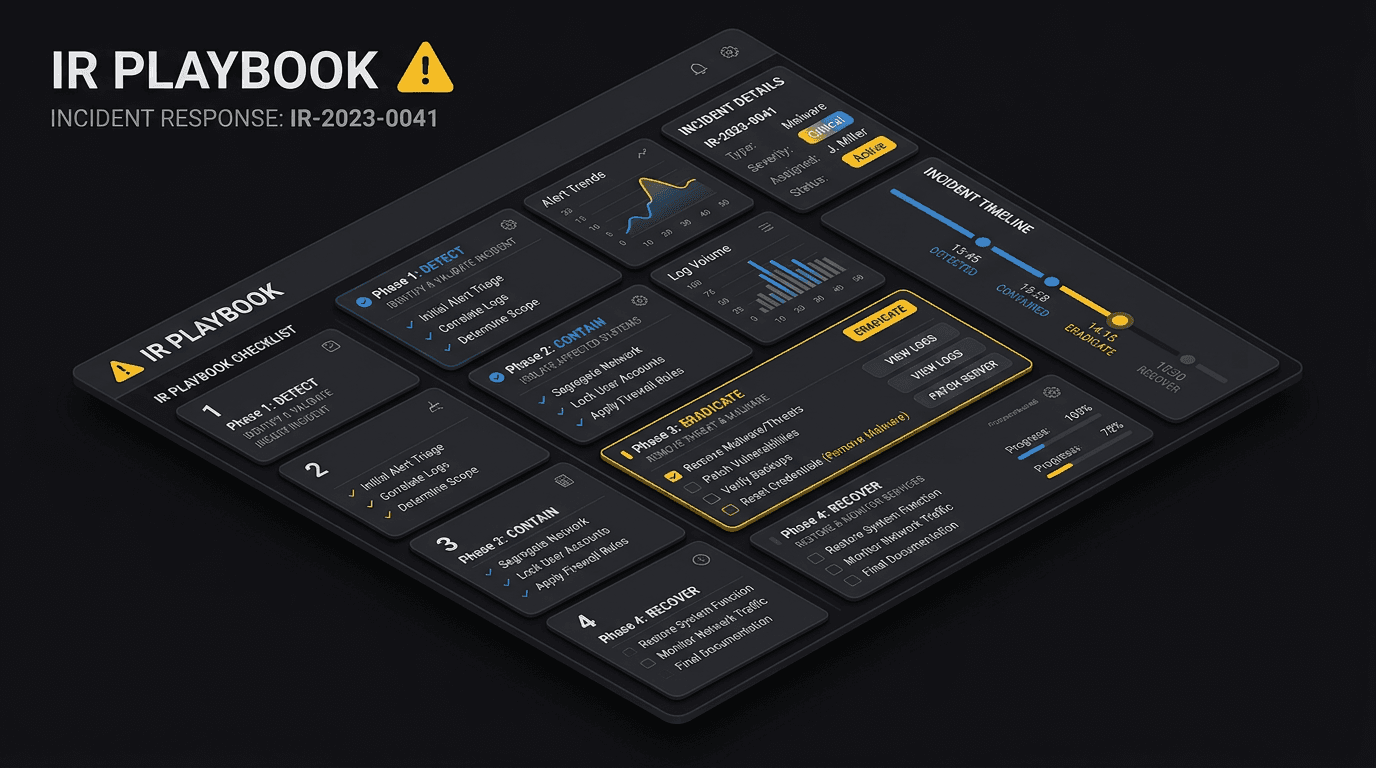
Incident response is a process, not a document. Playbooks should be short, scenario-specific, and tied to named roles so that when logs light up at 2 a.m., people know who decides what—without opening a fifty-page PDF.
Core Phases (Keep Them Consistent)
Most teams align to NIST-style phases: Prepare, Detect, Analyze, Contain, Eradicate, Recover, and Post-incident activity. The labels matter less than clear handoffs between security, IT, legal, and communications.
What Belongs in a Playbook
For each scenario (ransomware, business email compromise, data leak), define:
- Severity triggers and escalation paths
- Evidence preservation steps (logs, disk images) without destroying continuity
- Containment options (isolate host, disable account, block domain) with approval rules
- Comms templates for internal stakeholders and, when needed, customers
Tabletops and Drills
Run tabletop exercises quarterly with realistic injects: legal wants to hold disclosure, an executive demands immediate restore, the attacker is still in the network. Follow with technical drills for backup restore and log availability.
Metrics That Matter
Track time to detect, time to contain, and time to recover per incident class. Improve playbooks based on post-incident reviews, not assumptions.
Conclusion
The best playbook is the one your team has executed before the crisis. Invest in rehearsal and crisp decision rights; the PDF is just the souvenir.
Related articles
 May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud TeamsTyposquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
 Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC Enrichment
Apr 22, 2026File Hash Reputation Lookups: Accelerating Incident Response With IOC EnrichmentA practitioner's guide to file hash reputation lookups—how they work, which data sources power them, how to build automated IOC enrichment pipelines, and how to integrate hash intelligence into SOC, SOAR, and incident response workflows.
 Feb 13, 2026Building an Effective Incident Response Plan: A Step-by-Step Guide
Feb 13, 2026Building an Effective Incident Response Plan: A Step-by-Step GuideWhen a cyberattack strikes, panic is your enemy. Learn how to create and test an incident response plan to ensure your team knows exactly what to do.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker