IDN and Homograph Phishing: When the Domain Looks Right But Is Wrong
Internationalized domain names and look-alike characters let attackers spoof trusted brands in the address bar. Learn how homograph attacks work and how to defend users and SOC teams.
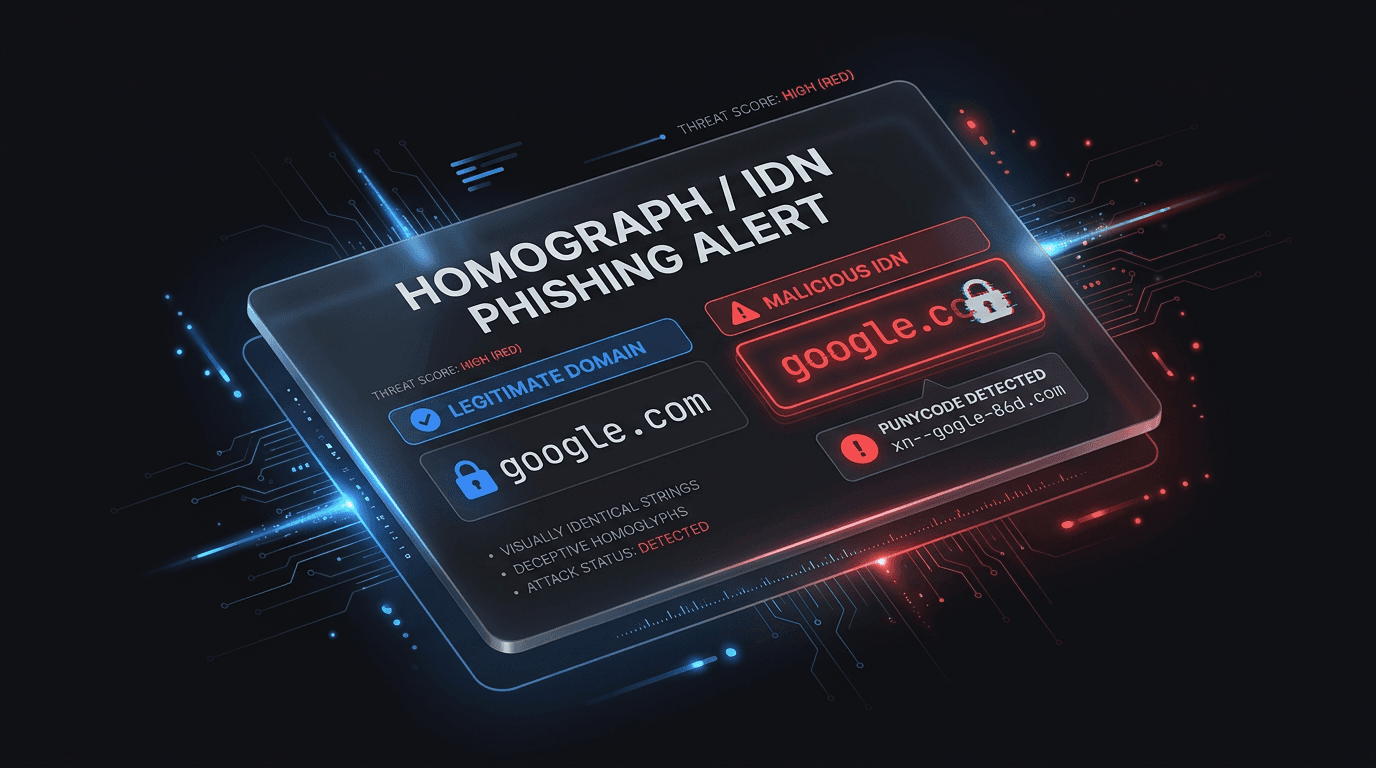
Phishing is not only misspelled domain names. Homograph attacks abuse visually similar characters from different Unicode scripts—Cyrillic “а” instead of Latin “a”—so the browser’s address bar looks identical to a legitimate site while resolving to an attacker-controlled hostname.
How IDN and Punycode Fit In
Browsers support internationalized domain names (IDNs) so people can use native scripts. Those names are represented in DNS using Punycode (xn--…). Many users never see the Punycode form; they see a friendly label. Attackers register domains that display like paypal.com or microsoft.com but encode to a different underlying ASCII name.
Why It Bypasses Casual Checks
Security awareness training often says “check the URL.” Homograph phishing targets exactly that habit: the string looks right. Combined with HTTPS, a polished login page, and urgency in the email or message, click-through rates stay high.
Defensive Measures
- Browser and OS policies: Prefer browsers that show Punycode or warn on mixed-script domains; keep clients updated.
- Email and web gateways: Detect newly registered IDNs, homograph clusters, and look-alikes of your brand with reputation and visual-similarity feeds.
- User education: Teach “don’t trust the address bar alone”—use bookmarks for sensitive apps and verify out-of-band when wiring money or resetting credentials.
- Brand protection: Monitor registrations that spoof your domains and file takedowns with registrars where policy allows.
For Security Operations
Alert on:
- First-seen domains with high visual similarity to internal or SaaS allowlists.
- Logins or OAuth flows where the redirect host is an IDN or recent registration.
- TLS certificates issued for confusable brand strings.
Conclusion
Homograph and IDN phishing exploit human perception and Unicode normalization. Technical controls (reputation, gateway rules, browser behavior) plus assume-breach thinking on authentication flows close the gap when the URL “looks” correct.
Related articles
 May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain Compromise
May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain CompromiseMalicious npm packages use typosquatting, dependency confusion, install scripts, and maintainer compromise to steal secrets and backdoor builds. Learn practical detection and response.
 May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud TeamsTyposquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
 Feb 25, 2026Domain Reputation Scoring: The First Line of Defense Against Phishing
Feb 25, 2026Domain Reputation Scoring: The First Line of Defense Against PhishingNot all domains are created equal. Discover how real-time domain reputation scoring helps organizations proactively identify and block phishing infrastructure, fake websites, and parked domains used by cybercriminals.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker