Non-Human Identity Security: API Keys, Service Accounts, and Workload Credentials in 2026
Non-human identities now outnumber users in most environments. Learn how API keys, service accounts, CI tokens, and workload credentials become attack paths and how to govern them.
Short answer: Non-human identity security is the discipline of knowing which machines, apps, pipelines, and agents can act in your environment. In 2026, many breaches do not need a human password because an API key, service account, or workload token already has the access attackers want.
Human identity programs have matured. Organizations deploy SSO, MFA, conditional access, device posture, and risky sign-in detection. Meanwhile, software identities have multiplied quietly. Every CI job, Terraform runner, Kubernetes workload, data pipeline, monitoring bot, webhook, SaaS connector, and AI agent needs a way to authenticate.
Those identities are powerful. They also tend to be messy. Some are created during urgent launches and never reviewed. Some are shared by multiple services. Some have administrator privileges because nobody knew the minimum scope. Some live in .env files, container images, build logs, or old laptops. Some continue to work years after the project that created them was shut down.
Attackers understand this. If stealing a user's password triggers MFA and risk controls, stealing a service token may be easier.
The Non-Human Identity Sprawl Problem
Non-human identities include:
- API keys.
- Cloud service accounts.
- Workload identities.
- Kubernetes service account tokens.
- CI/CD deployment tokens.
- OAuth applications and app registrations.
- SSH keys used by automation.
- Database credentials.
- Webhook secrets.
- Certificates and private keys.
- AI agent tool credentials.
The common feature is that software uses them to act. That action may be read-only, or it may deploy code, create infrastructure, access customer data, send email, query logs, or call paid AI services.
The sprawl problem appears when security teams cannot answer basic questions: Who owns this key? What system uses it? What can it access? When was it last used? Where is it stored? What happens if we revoke it?
Why Attackers Love NHI
Non-human identities are attractive because they can be long-lived and under-monitored. A user account may have interactive login alerts. A service account may quietly authenticate through an API thousands of times a day. Malicious use can hide inside automation noise.
Many NHI credentials also bypass normal user controls. MFA does not apply to an API key. Device compliance does not apply to a CI token. A password reset does not rotate a hardcoded secret.
Attackers can find these credentials through public repositories, private repository compromise, malicious packages, build log exposure, phishing of developers, infostealer malware, cloud metadata service abuse, and SaaS integrations with broad permissions.
The result is direct access. A stolen CI token may push a backdoored release. A cloud service account may read storage buckets. An AI API key may enable LLMjacking. A webhook secret may let an attacker spoof trusted events.
Build an Inventory First
You cannot govern identities you cannot see. Start by collecting NHI data from each control plane:
- Cloud IAM and access keys.
- Source control deploy keys and app installations.
- CI/CD variables and runner credentials.
- Secret managers.
- Kubernetes clusters.
- SaaS OAuth app grants.
- API gateways.
- Databases.
- Monitoring and logging tools.
For each identity, record owner, business purpose, environment, permissions, creation date, last use, rotation status, and storage location. Ownerless identities should be treated as risk. Unused identities should be disabled before they become mystery backdoors.
Do not make inventory a spreadsheet exercise only. The data changes constantly. Build recurring discovery and alerts for new identities.
Permission Design
Least privilege sounds obvious, but it is rarely implemented for automation. Teams often grant broad permissions because the pipeline must ship today. Months later, that permission becomes invisible risk.
Design identities around specific jobs. A build job that publishes artifacts does not need production database access. A monitoring integration that reads metrics does not need write access to IAM. A crawler that checks domain reputation does not need access to customer billing.
Separate environments. Development credentials should not access production. Production credentials should not be available to local notebooks. Break-glass automation should have strict approval and logging.
Use short-lived credentials where possible. Workload identity federation, managed identities, and token exchange reduce the blast radius of leaked static keys. Static credentials should be rotated and scoped tightly.
Storage and Secret Handling
Secrets should live in a secret manager, not in source code, container images, chat, tickets, or wiki pages. That principle is simple; enforcement is harder.
Use secret scanning across repositories, CI logs, container images, and collaboration tools. Block commits that contain secrets. Rotate exposed credentials automatically. Treat any public exposure as compromise, even if logs show no use.
Be careful with build systems. CI environments often echo variables during debugging or pass secrets to third-party actions. Review what actions can read. Pin dependencies. Limit secrets available to pull requests from forks.
For more detail, see CI/CD Security: Secrets in Pipelines and Malicious npm Packages.
Monitoring NHI Usage
Monitor non-human identities by behavior, not just existence. Useful alerts include:
- First use of a new service account.
- Use from a new ASN, region, or IP range.
- Use outside expected deployment windows.
- Permission denied events followed by successful access.
- API calls to resources the identity has never touched.
- Sudden increase in volume or cost.
- Access from known proxy, VPN, Tor, or malicious infrastructure.
- Long-unused identity suddenly active.
Tie logs back to owners. An alert that says "service-account-prod-17 used from a new IP" is much less useful than "billing export job identity owned by Data Platform used from an unfamiliar cloud host."
Threat intelligence improves triage. If the source IP is known abusive infrastructure, the incident priority changes immediately.
Response Playbook
When an NHI credential is suspected compromised:
- Disable or rotate it.
- Identify all systems that depend on it.
- Review audit logs for actions performed by that identity.
- Check whether permissions allowed lateral movement.
- Search for the credential in repositories, logs, images, and developer machines.
- Replace static secrets with short-lived identity where practical.
- Add detection for similar identities.
Do not rotate only the obvious key. If one key leaked through a pipeline, other keys stored the same way may be exposed too.
Maturity Model
A basic non-human identity program starts with discovery. The organization can list API keys, service accounts, app registrations, CI tokens, and workload identities. It can identify unused credentials and remove them. It can rotate exposed secrets quickly.
The next level is ownership. Every identity has a named team, business purpose, environment, and risk tier. New identities require an owner at creation time. Ownerless credentials are blocked or expired automatically. Access reviews include machine identities, not just employees.
The third level is policy enforcement. Static secrets are replaced with workload identity where possible. High-risk permissions require approval. Secrets are not exposed to untrusted build steps. Sensitive systems require managed devices, expected networks, and short-lived tokens.
The advanced level is behavioral detection. The organization understands normal usage for each identity and alerts when it changes. Service accounts are monitored for new source IPs, new APIs, unusual volume, and suspicious infrastructure. Response teams can revoke, rotate, and redeploy without guessing which system will break.
Questions for Every Service Account
Ask these questions during review:
- Who owns this identity?
- Which system uses it?
- What business process fails if it is disabled?
- What exact permissions does it have?
- When was it last used?
- Where is the credential stored?
- Can it be replaced by workload identity?
- What network locations should use it?
- What logs prove its activity?
- What is the rotation process?
If the team cannot answer, the identity is a risk. That does not mean it must be deleted immediately, but it should be prioritized for investigation.
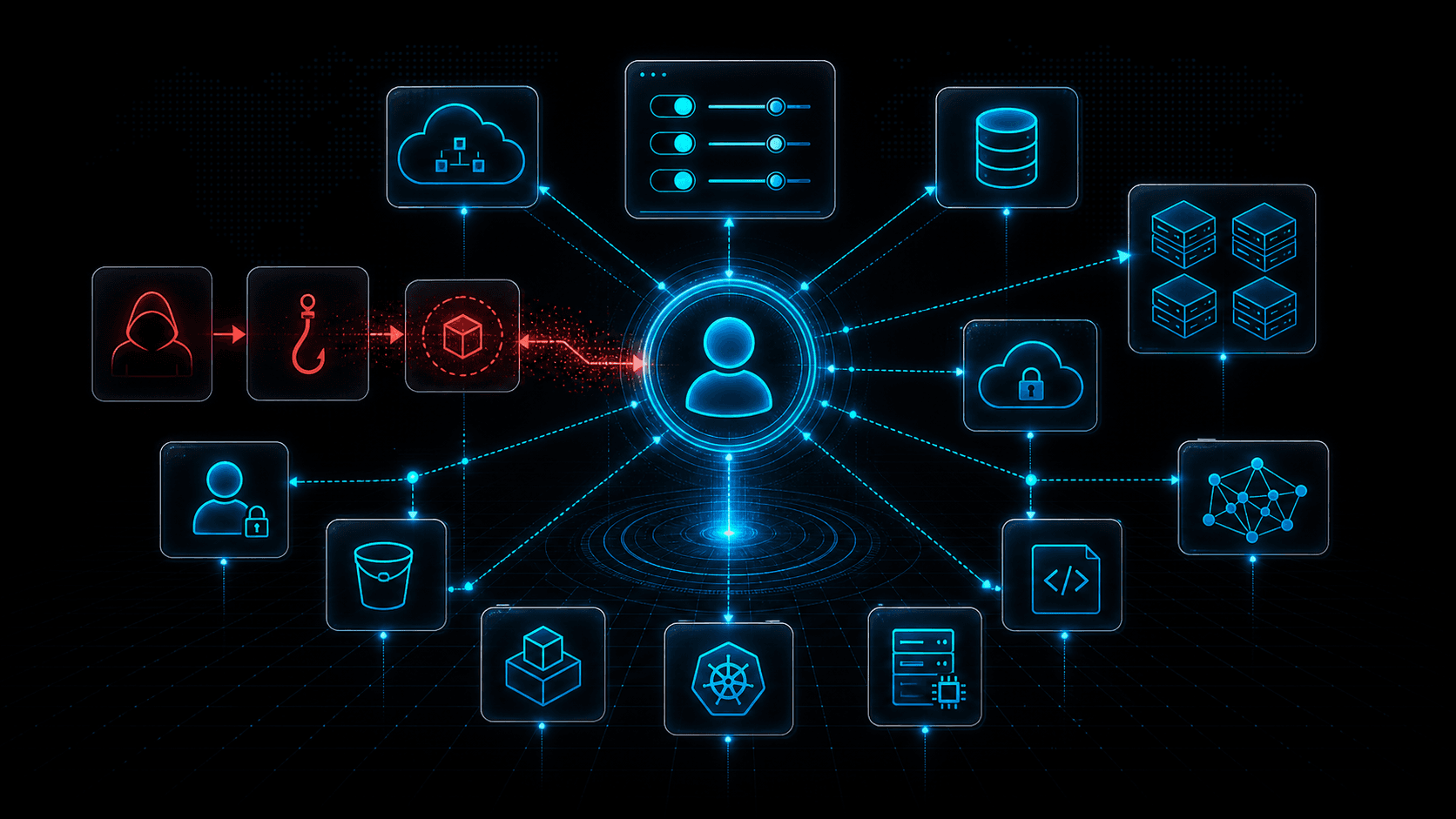
CI/CD and NHI
CI/CD systems are non-human identity concentrators. They often hold cloud credentials, package registry tokens, signing keys, deployment credentials, and chat webhooks. A malicious dependency or compromised runner can turn those secrets into an attack path.
Separate install, build, test, publish, and deploy stages. The dependency installation step should not have production deployment credentials. Pull requests from untrusted forks should not receive secrets. Runners should be isolated, ephemeral, and logged. Outbound network access should be controlled, especially during dependency installation.
Use different identities for different repositories and environments. A token for one project should not deploy another. A staging pipeline should not read production secrets. A documentation build should not have cloud admin privileges.
Measuring Progress
Track practical metrics: number of active static keys, number of ownerless identities, percentage of identities unused for 30 or 90 days, median credential age, number of identities with administrator privileges, number of secrets found in repositories, and time to rotate after exposure.
These metrics help leadership see the program as risk reduction rather than cleanup. The goal is not a perfect inventory on day one. The goal is steady reduction of unknown, overprivileged, long-lived credentials.
90-Day Implementation Plan
In the first month, focus on discovery and removal. Pull identity lists from cloud platforms, source control, CI/CD, Kubernetes, secret managers, and SaaS applications. Disable credentials that are clearly unused, expired, duplicated, or ownerless after validation. Add labels for owner, environment, and purpose to the remaining identities.
In the second month, reduce privilege. Prioritize identities with administrator access, production access, secret read permissions, package publishing rights, and deployment rights. Split shared identities by application. Move secrets from code and CI logs into managed secret stores. Configure alerts for new key creation and first-time use from unfamiliar infrastructure.
In the third month, modernize the highest-risk credentials. Replace static keys with workload identity federation or managed identity where possible. Add just-in-time elevation for rare administrative jobs. Create a quarterly access review that includes non-human identities. Test a compromised service account scenario and measure how long it takes to revoke, rotate, and redeploy safely.
Ownership Culture
Non-human identities often become risky because nobody feels responsible for them. Treat ownership as an engineering requirement. A new service account should not be approved unless it has a team owner, documented purpose, review date, and decommission plan. When teams ship automation, they should also ship the access lifecycle.
Ownership should survive reorganizations. When a team changes name, merges, or shuts down a project, its machine identities should be reviewed like its repositories and cloud resources. Many dangerous credentials are not created maliciously; they become dangerous because their owners disappear.
Lifecycle ownership is the control that keeps that from becoming normal.
Threat Intelligence Takeaway
Non-human identities are becoming the connective tissue of modern infrastructure. They are also becoming an attacker shortcut around human-focused security controls.
isMalicious helps by enriching the IPs and domains that appear in API logs, CI callbacks, webhook traffic, and cloud audit events. When a service account acts from suspicious infrastructure, reputation context helps responders separate expected automation from credential abuse.
Frequently asked questions
- What is a non-human identity?
- A non-human identity is an identity used by software rather than a person: API keys, service accounts, workload identities, CI tokens, bots, OAuth apps, certificates, and machine credentials.
- Why are non-human identities risky?
- They are often long-lived, overprivileged, poorly inventoried, and embedded in automation. If stolen, they can provide direct access without triggering user-focused security controls.
- How should teams inventory non-human identities?
- Collect identities from cloud IAM, SaaS apps, CI/CD systems, secret managers, Kubernetes, source control, OAuth applications, and API gateways, then map each identity to owner, purpose, scope, and last use.
- What is the best first control for NHI security?
- Start by eliminating unused and ownerless credentials, then rotate long-lived secrets, scope permissions, and replace static keys with workload identity federation where possible.
Related articles
 May 8, 2026LLMjacking Explained: How Attackers Abuse Cloud Credentials to Steal AI Compute
May 8, 2026LLMjacking Explained: How Attackers Abuse Cloud Credentials to Steal AI ComputeLLMjacking combines cloud credential theft with expensive AI workloads. Learn how attackers find exposed keys, abuse model APIs, hide compute costs, and how defenders can detect the pattern.
 May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill Chain
May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill ChainCloud breaches increasingly target the control plane: identities, tokens, policies, APIs, and automation. Learn how attackers move from one credential to full cloud control.
 Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026
Apr 28, 2026Cloud IP Reputation: What AWS, Azure, and GCP Defenders Should Track in 2026Cloud IP addresses are shared, recycled, and abused at scale. Learn how to interpret reputation signals, reduce false positives, and align network security with platform-native controls across the three major hyperscalers.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker