Malvertising and Search Poisoning: Threats Hiding in Plain Sight
Malicious ads and manipulated search results push users toward malware and phishing without email. Learn how malvertising and SEO poisoning work and how teams can reduce risk.

Users do not need to open a phishing email to get compromised. Malvertising delivers malicious or misleading content through ad networks and publisher sites. Search engine poisoning (SEO spam) pushes fake download pages, support scams, or credential harvesters to the top of results for popular software names.
How Malvertising Works
Attackers submit or compromise ad creatives that:
- Redirect to exploit kits or fake updates (browser, Flash-style legacy patterns, or “required codec” scams).
- Mimic brand login pages after a click on a “sponsored” result.
- Use geofencing and device filtering so scanners see benign content while victims see malware.
The trust users place in known sites and ad platforms is the exploit.
Search Poisoning in Brief
Campaigns optimize malicious or cloned pages for high-intent queries: “download [popular app],” “[crypto] wallet,” “[game] crack.” Poisoned PDFs, forum spam, and compromised blogs also feed long-tail queries. The goal is the same: intercept intent before the user reaches the real vendor.
Organizational Defenses
- DNS and secure web gateway: Block known-bad domains and categories; inspect TLS where policy allows.
- Browser management: Enforce updates, block unnecessary extensions, consider ad-blocking or isolate high-risk browsing for sensitive roles.
- Software sourcing: Only install from vendor-verified channels; internal docs should link to official download pages, not raw search results.
- User messaging: Train on “sponsored results are ads” and verify the domain before downloads.
For Threat Intel and Brand Teams
- Monitor look-alike domains and abusive ads impersonating your product.
- Share IOC lists (domains, redirect chains) with marketing and legal for takedowns.
- Correlate surges in support tickets (“installer failed”) with new SEO spam clusters.
Conclusion
Malvertising and search poisoning abuse distribution channels users trust. Layered web controls, disciplined software procurement, and brand monitoring shrink the window where poisoned results and ads do damage.
Related articles
 Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026
Apr 24, 2026Spear Phishing and Social Engineering: The Top Attack Vectors Targeting Enterprises in 2026A complete guide to modern spear phishing and social engineering attack vectors—how threat actors plan, lure, and pivot, with detailed defensive controls for email, identity, training, and infrastructure reputation.
 Apr 10, 2026Domain Lookup for Phishing and C2 Infrastructure Detection
Apr 10, 2026Domain Lookup for Phishing and C2 Infrastructure DetectionPhishing campaigns and malware operations depend on domain infrastructure that leaves detectable traces. Learn how advanced domain lookup techniques help security teams uncover phishing sites and command-and-control servers before they compromise your organization.
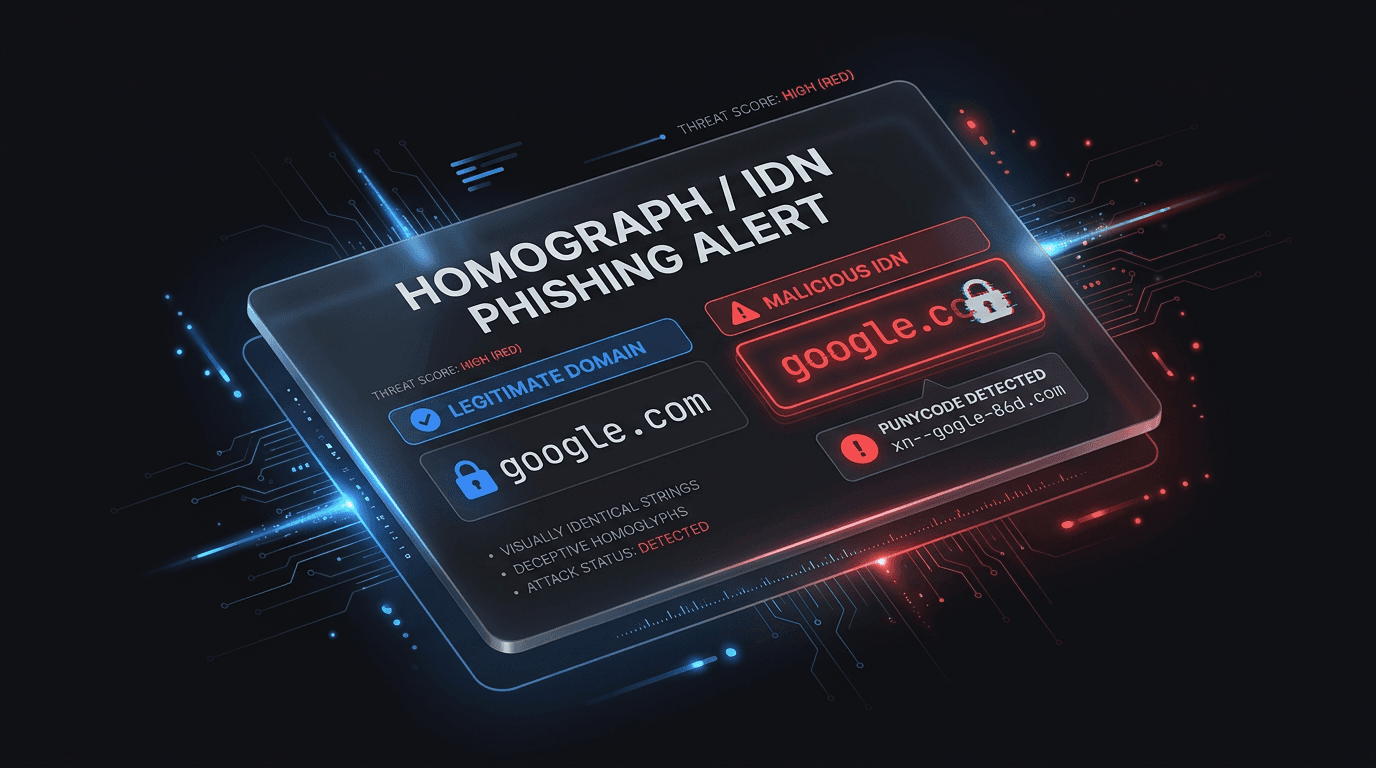 Apr 1, 2026IDN and Homograph Phishing: When the Domain Looks Right But Is Wrong
Apr 1, 2026IDN and Homograph Phishing: When the Domain Looks Right But Is WrongInternationalized domain names and look-alike characters let attackers spoof trusted brands in the address bar. Learn how homograph attacks work and how to defend users and SOC teams.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker