Living Off the Land (LOTL): Why “No Malware File” Still Means Breach
Attackers increasingly abuse built-in OS binaries and scripts to avoid dropping traditional malware. Understand LOTL tradecraft and what to log, detect, and hunt for.
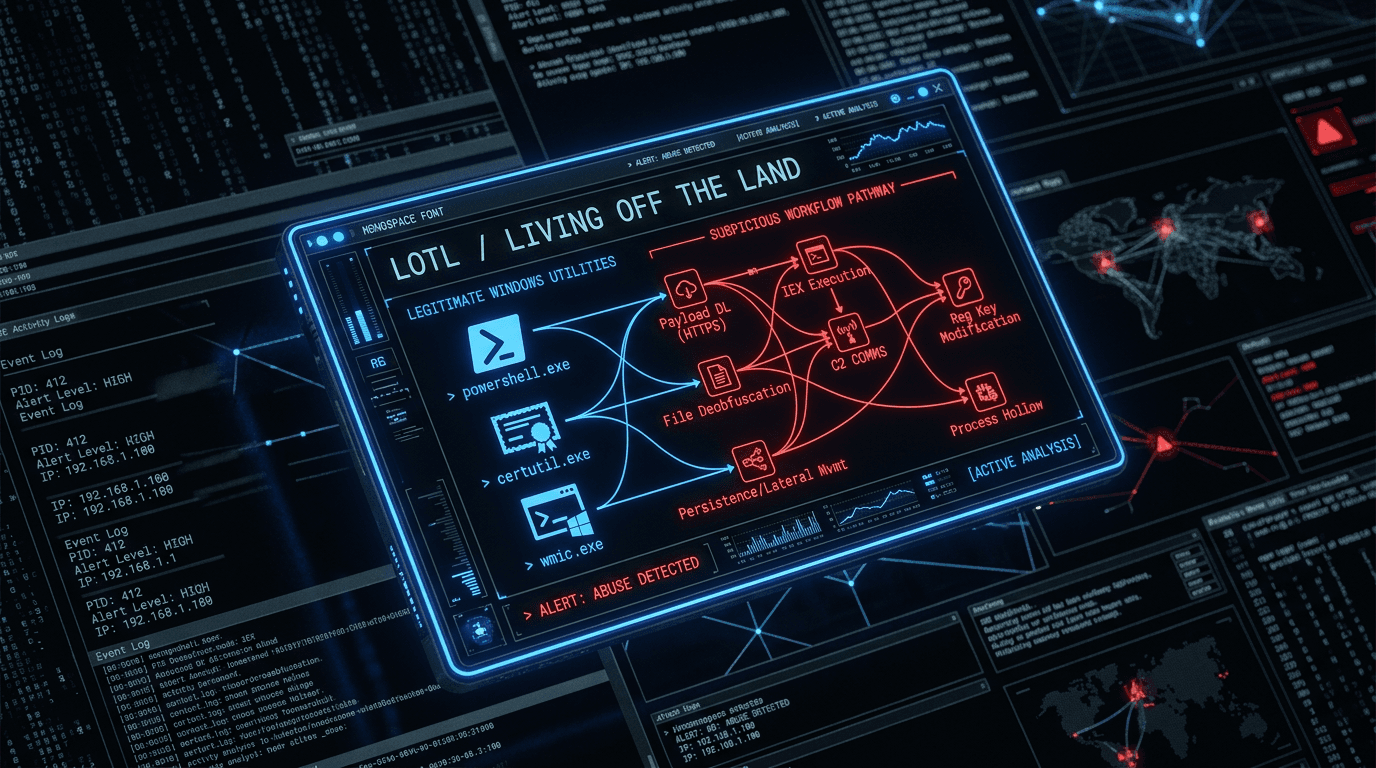
Living off the land (LOTL) means using legitimate tools already on the system—PowerShell, certutil, WMI, mshta, remote admin utilities—to execute objectives without introducing a well-known malicious binary. Defenders lose the easy win of “block this hash,” and detection shifts to behavior and context.
Why Attackers Prefer LOTL
- Signed, trusted binaries rarely trigger legacy antivirus heuristics.
- Dual use: The same command an admin runs daily can exfiltrate data or load a payload.
- Blends with IT noise in large environments.
Common Patterns (Examples)
- Scripting engines pulling code from remote hosts (
IEX,Invoke-WebRequestchains). - Living binaries used to decode, stage, or install payloads (
certutil -decode,bitsadmin). - WMI and scheduled tasks for persistence without dropping an obvious
.exe.
Mapping these to MITRE ATT&CK (e.g., Command and Scripting Interpreter, Signed Binary Proxy Execution) helps prioritize detections and purple-team scenarios.
Detection Strategy
- Telemetry everywhere that matters: process ancestry, command lines, network connections from scripting hosts, and module loads where available.
- Baseline normal: what does your IT automation legitimately run? Exclude with care, not by silencing all PowerShell.
- Correlation: rare parent-child pairs (e.g., Office spawning
powershell.exewith encoded commands) are higher signal than either event alone. - EDR + SIEM rules tuned to your stack; generic “block certutil” breaks patching if applied bluntly.
Hardening (Without Breaking the Business)
- Constrained language mode and AppLocker / WDAC where feasible.
- Just enough admin; no standing Domain Admin for daily work.
- Network egress controls so LOTL stages cannot reach arbitrary URLs.
Conclusion
LOTL trades file reputation for stealth. Winning means behavioral detection, strong identity, and least privilege—not hoping a single antivirus signature saves the day.
Related articles
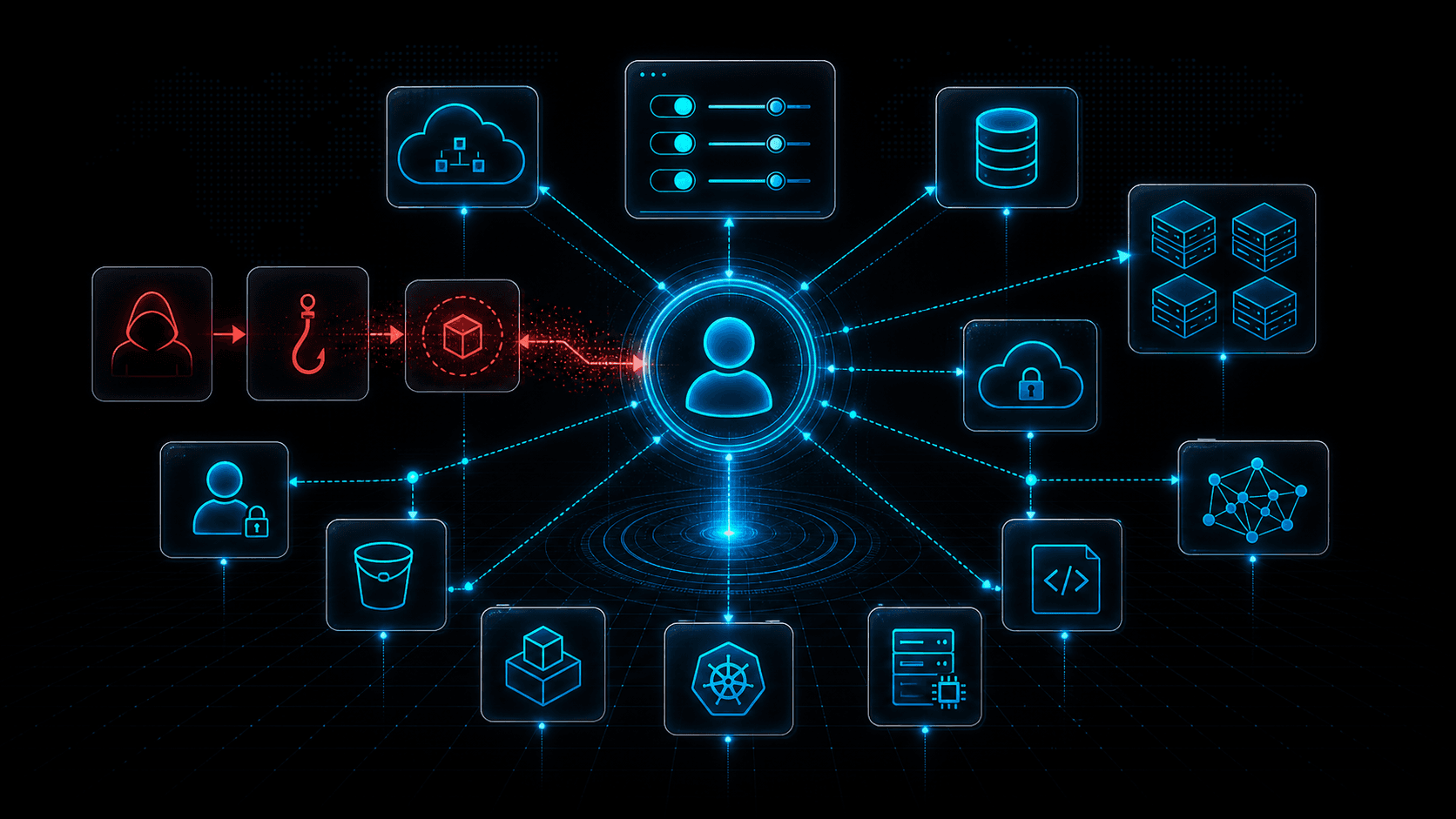 May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill Chain
May 4, 2026Cloud Control Plane Attacks: Why Identity Is the New Kill ChainCloud breaches increasingly target the control plane: identities, tokens, policies, APIs, and automation. Learn how attackers move from one credential to full cloud control.
 Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security Programs
Apr 23, 2026Strategic, Tactical, and Operational Threat Intelligence: Frameworks for Modern Security ProgramsAlign CTI outputs with audience needs: executive risk narratives, SOC-ready IOCs, and MITRE-mapped TTPs—plus governance models that keep intelligence timely and measurable.
 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker