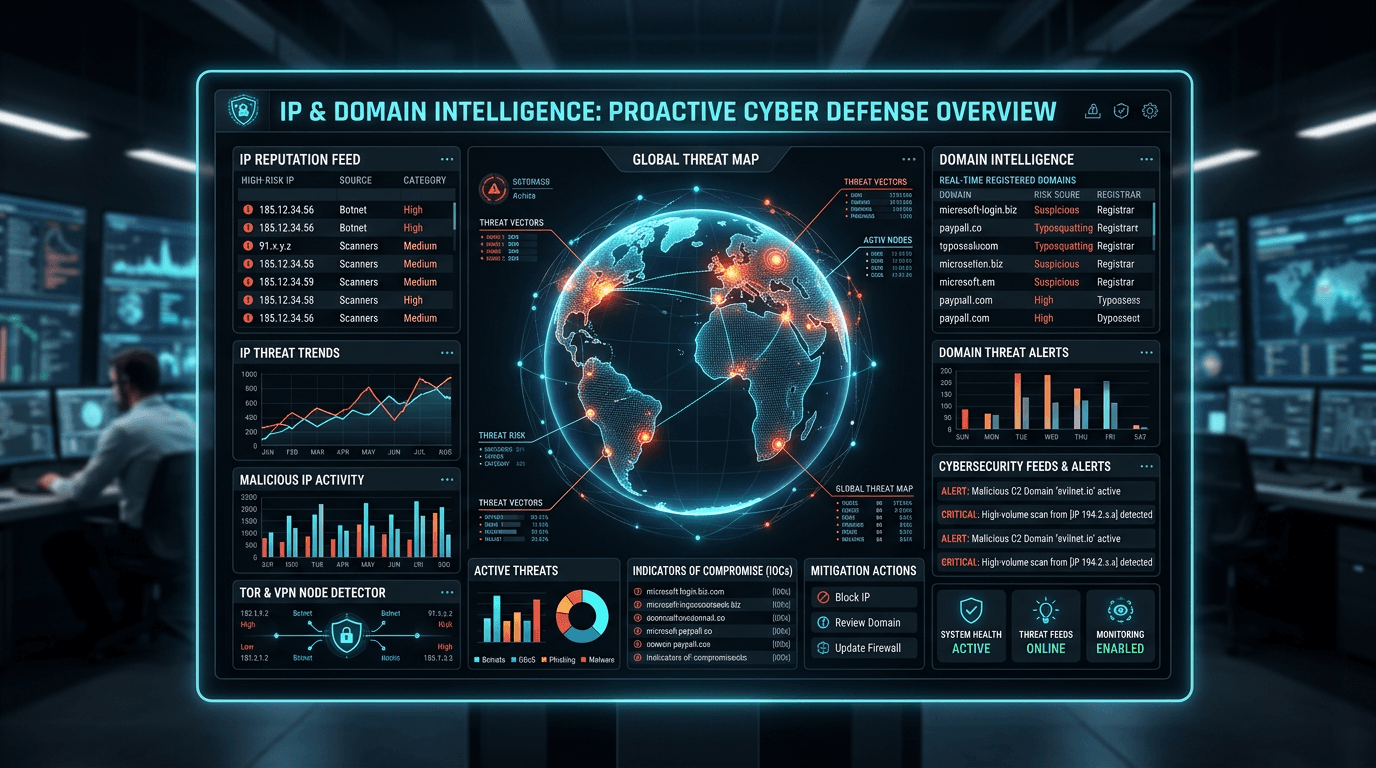
IP and Domain Intelligence: Building a Proactive Cyber Threat Defense
Reactive security leaves organizations perpetually one step behind attackers. Learn how combining IP and domain intelligence transforms your security posture from reactive incident response to proactive threat prevention that stops attacks before they start.
The security industry has spent decades optimizing incident response — getting faster at detecting breaches, containing damage, and recovering from attacks. These capabilities matter, but they are inherently reactive. By the time incident response begins, attackers have already achieved at least partial access to their objectives. The credentials have been harvested. The ransomware has encrypted the first file. The data exfiltration has begun.
Proactive cyber defense inverts this dynamic. Instead of detecting attacks in progress, it identifies the infrastructure attackers depend on before that infrastructure is used against your organization, and blocks or monitors it at the point of first contact. IP and domain intelligence is the foundation of this approach — the data layer that makes proactive defense possible at scale.
The Case for Intelligence-Led Security
Traditional perimeter security defines "trusted" and "untrusted" based on network location. Traffic from inside the network is trusted; traffic from outside is subject to inspection. This model failed long ago as cloud services, remote work, and supply chain compromise eliminated the meaningful distinction between inside and outside.
Intelligence-led security replaces location-based trust with behavior-based trust. No connection is trusted by default. Every external IP and every domain involved in a transaction is evaluated against accumulated threat intelligence before it is allowed to interact with protected systems. The classification is dynamic — an IP that was clean yesterday may be flagged today, and the system adjusts its posture accordingly.
This is not a theoretical model. It is the operating principle behind every effective security program at scale. Financial institutions, cloud providers, and critical infrastructure operators run threat intelligence queries at connection time as standard practice, not as an advanced enhancement.
IP Intelligence: Understanding the Threat Actor's Network Presence
IP intelligence aggregates behavioral signals about specific internet addresses into actionable risk profiles. Understanding what these profiles contain — and how they are built — is essential to using them effectively.
The Signals That Compose IP Reputation
Botnet participation: IPs identified as nodes in botnet networks — whether used for DDoS amplification, spam delivery, or credential stuffing — carry this classification until they demonstrate clean behavior over an extended period. Botnet IPs represent a significant share of credential stuffing traffic against consumer applications.
Scanner activity: Automated vulnerability scanners and reconnaissance tools are detected by honeypot systems and low-interaction sensors globally. IPs running persistent scanning operations are flagged and tracked. While legitimate security researchers conduct scanning, the pattern and volume of scanner IPs typically distinguish malicious reconnaissance from authorized testing.
Spam origination: IPs that have sent high volumes of unsolicited email are tracked by spam monitoring networks. These IPs often appear in credential stuffing, phishing delivery, and malware distribution operations as well, since they represent infrastructure the attacker controls or compromises for multiple purposes.
Brute force and exploitation: IPs observed attempting repeated authentication failures, exploiting known CVEs, or probing for default credentials on exposed services are flagged in threat feeds maintained by security vendors and the research community.
Tor exit nodes and anonymization services: While not inherently malicious, connections through Tor exit nodes and certain VPN services warrant elevated scrutiny for sensitive transactions, since they are commonly used to obscure the origin of automated attacks and fraud operations.
How IP Intelligence Combines Into Actionable Scores
Individual signals are weighted and combined into composite risk scores. An IP appearing on one minor spam feed might score 20 out of 100. The same IP, if it also appears in botnet records and has been observed in recent credential stuffing campaigns, might score 85. The score reflects the full accumulated evidence — and it changes as new evidence arrives.
Domain Intelligence: Understanding the Threat Actor's Infrastructure
Domain intelligence provides a parallel picture at the naming layer. While IP intelligence tracks connections, domain intelligence tracks the names those connections resolve to.
Registration Intelligence
The domain registration record is the first place attackers leave traces. Even with privacy protection enabled, registration metadata reveals:
- Domain age: The single most predictive indicator of phishing risk. Domains less than 30 days old account for a disproportionate share of detected phishing infrastructure.
- Registrar patterns: Certain registrars attract malicious registrations due to permissive policies, low prices, and minimal verification requirements.
- Registration velocity: A burst of newly registered domains with similar naming patterns often signals a campaign in preparation.
- WHOIS consistency: Legitimate businesses maintain consistent, accurate registration records. Malicious operators rotate registrant details across domains to avoid pattern matching.
DNS and Infrastructure Intelligence
Where a domain resolves matters as much as how it is named. DNS intelligence reveals:
- Hosting infrastructure risk: A domain resolving to an IP range associated with bulletproof hosting providers is elevated risk regardless of its name.
- Co-hosting patterns: Shared hosting IPs reveal clusters of related domains. A single malicious domain may share an IP with dozens of other domains operated by the same threat actor.
- Resolution history: Passive DNS captures the history of which IPs a domain has resolved to over time. Infrastructure that changes IPs rapidly — fast flux — is a C2 indicator.
- DNS record anomalies: Maliciously configured MX records, unusual TXT records, and SPF configurations that contradict actual mail flow are all observable through DNS intelligence.
Combining IP and Domain Intelligence for Complete Coverage
IP intelligence and domain intelligence are complementary. Each has blind spots that the other fills.
IP intelligence alone misses: Domain-based threats where the same domain rotates through many IPs (fast flux C2), newly registered domains hosted on clean IPs, and phishing domains that haven't yet generated IP-level abuse reports.
Domain intelligence alone misses: Direct IP-based C2 communication (malware that contacts a raw IP without using a domain name), IP-based scanning and brute force operations, and botnet activity that doesn't involve domain names.
Combined intelligence provides: Complete coverage of the attacker's network footprint. When an unknown IP connects to your application, its domain resolution history from passive DNS can reveal whether it has previously hosted malicious domains. When a domain appears in suspicious traffic, its IP associations reveal the broader infrastructure cluster. Neither analysis alone provides this full picture.
Building a Proactive Defense Architecture
Layer 1: Intelligence at the Network Edge
The first layer of proactive defense operates before any application logic executes. At the CDN, load balancer, or API gateway level, every inbound connection is evaluated against IP reputation data. High-confidence malicious IPs are dropped here — they never consume application resources, never trigger authentication flows, and never generate database load.
This layer requires low-latency access to continuously updated IP reputation data. Static blocklist files refreshed nightly are insufficient; the threat landscape changes too quickly. Real-time API queries against a platform like IsMalicious provide the freshness required for effective edge-layer blocking.
Layer 2: Intelligence at Application Trust Decisions
The second layer operates at every point where the application makes a trust decision: login, registration, password reset, payment authorization, privilege escalation. At each of these points, both IP and domain intelligence inform the decision.
For IP: Is this address associated with credential stuffing tools? Botnet operations? High-risk geographic origins inconsistent with the account's history?
For domain: Is the email address provided at registration from a newly registered, low-reputation domain? Is the referring domain in the request headers a known phishing or malware site?
These checks happen in real time, at millisecond scale, and their results feed graduated response policies rather than binary block/allow decisions.
Layer 3: Intelligence in Monitoring and Detection
The third layer operates in the background, continuously enriching log data and monitoring for emerging threats. DNS query logs are analyzed for connections to high-risk or newly registered domains. Authentication logs are enriched with IP reputation scores and correlated to detect distributed credential stuffing campaigns where each IP makes only a small number of attempts.
Threat intelligence enrichment transforms raw logs into contextual security data. An analyst reviewing a week of authentication logs enriched with IP reputation data can immediately identify the days where high-risk IPs constituted an unusual share of login attempts — a pattern invisible in raw logs that clearly reveals a targeted attack.
Layer 4: Intelligence in Threat Hunting
Proactive threat hunting uses IP and domain intelligence offensively — actively searching for signs of compromise before alerts fire. Threat hunters query historical logs for connections to domains that have since been classified as malicious, identify systems that communicated with IP addresses now known to be C2 infrastructure, and investigate patterns in DNS traffic that match known DGA behaviors.
This retrospective intelligence analysis frequently discovers compromises that evaded real-time detection — either because the threat intelligence wasn't available at the time of the event, or because the attacker's behavior was subtle enough to avoid triggering real-time rules.
IsMalicious: Your Intelligence Foundation
IsMalicious provides the IP and domain intelligence layer that powers each of these defense layers. A single platform aggregates data from dozens of threat feeds, passive DNS networks, abuse reporting systems, and security research sources into a unified, low-latency API.
Query any IP or domain and receive a comprehensive risk profile: reputation score, specific abuse categories, blocklist presence, registration metadata, infrastructure associations, and historical activity. The data is continuously refreshed, so intelligence reflects the current threat environment, not last night's batch update.
For security teams moving from reactive to proactive posture, IsMalicious provides the intelligence foundation that makes the transition possible. Every connection becomes an opportunity to apply threat intelligence. Every domain encountered becomes a data point in a continuously updated picture of the threat landscape.
Start a free lookup and discover what threat intelligence reveals about the IPs and domains connecting to your organization right now.
Frequently asked questions
- What is the difference between IP intelligence and domain intelligence?
- IP intelligence focuses on the behavioral history and current risk profile of specific IP addresses — whether they have been used for spam, DDoS attacks, credential stuffing, or other abuse. Domain intelligence focuses on domains: their registration history, WHOIS data, presence on phishing or malware blocklists, and associated infrastructure. Combined, they provide a complete picture of network-layer threat actors — attackers operate both IP addresses and domains, and correlating the two exposes infrastructure clusters that neither data source reveals alone.
- How does proactive threat defense differ from reactive incident response?
- Reactive incident response acts after an attack has occurred — detecting breaches, containing damage, and remediating compromised systems. Proactive defense uses threat intelligence to identify and block malicious actors before they can execute an attack. IP and domain intelligence enables proactive defense by flagging known bad actors at the point of first contact, before they have a chance to phish credentials, install malware, or exfiltrate data. The goal is to shift the security timeline left — from incident response to prevention.
- How often should IP and domain intelligence data be refreshed?
- For maximum effectiveness, threat intelligence should be queried in real time at the moment of each connection or transaction, not cached from periodic batch updates. IP addresses and domains used in attacks change status rapidly — an IP that was clean this morning may be flagged for botnet activity by afternoon. Platforms like IsMalicious continuously ingest new threat data and reflect it in query results within minutes of initial detection.
Related articles
 Apr 7, 2026IP Lookup for Cyber Threat Detection: A Complete Security Guide
Apr 7, 2026IP Lookup for Cyber Threat Detection: A Complete Security GuideLearn how IP lookup works as a frontline defense against cyber threats. Discover how to use IP reputation data, threat intelligence feeds, and automated checks to block malicious actors before they reach your systems.
 Dec 5, 2025Proactive Threat Defense: Monitoring Malicious IP and Domain Reputation
Dec 5, 2025Proactive Threat Defense: Monitoring Malicious IP and Domain ReputationShift from reactive to proactive cybersecurity. Learn how monitoring malicious IP and domain reputation helps identifying threats early and stopping phishing attacks before they succeed.
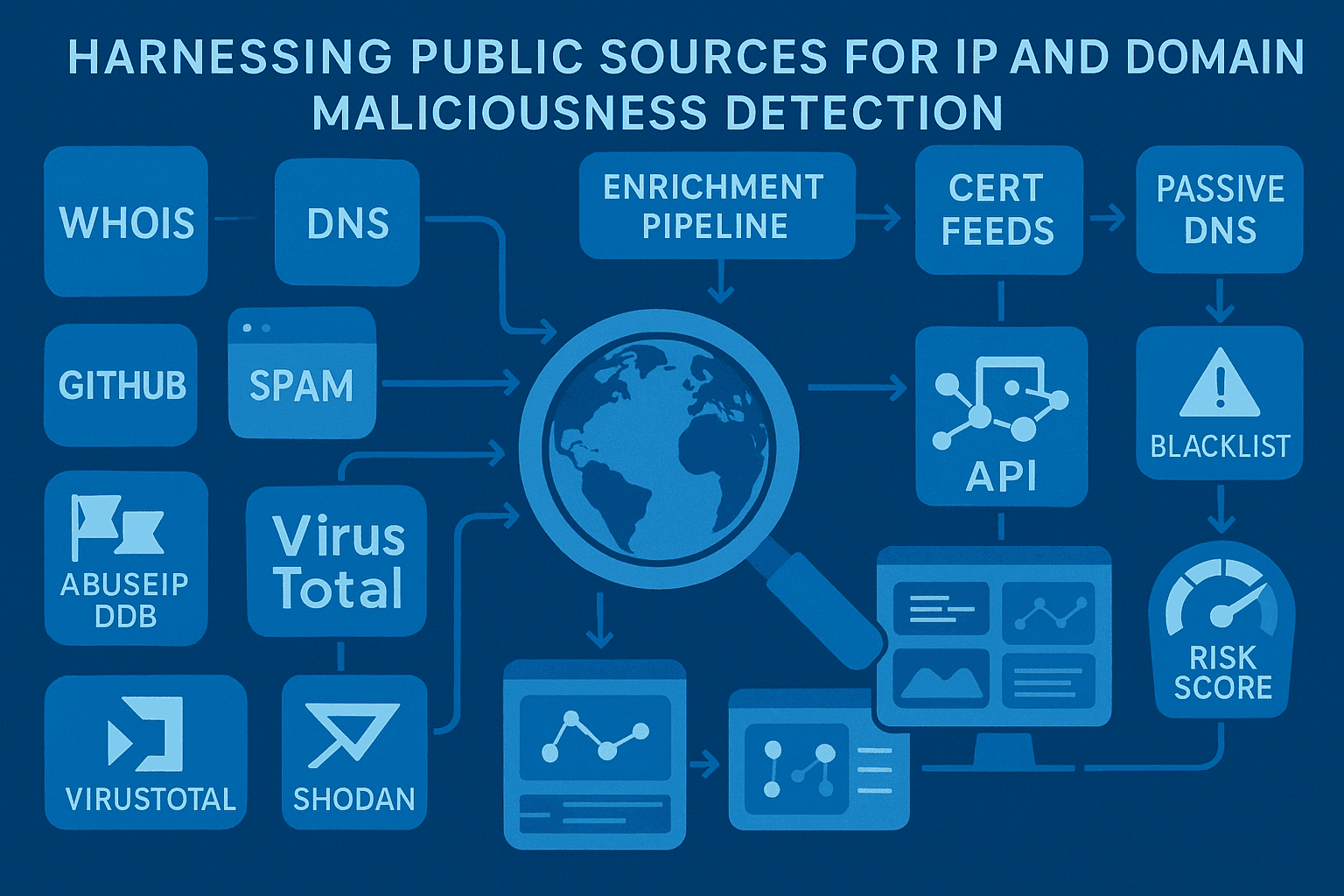 Dec 12, 2024Harnessing Public Sources for IP and Domain Maliciousness Detection
Dec 12, 2024Harnessing Public Sources for IP and Domain Maliciousness DetectionLearn how public sources like IP sets and blocklists can enhance your cybersecurity defenses by providing actionable insights into IP and domain maliciousness. Discover how to integrate these resources into WAF solutions like Fortinet and Imperva.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker