Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
Typosquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
Short answer: Brand impersonation defense is a triage problem: you will never stop all permutations, but you can stop the tiny fraction that is weaponized, hosted, and used before your customers are harmed.
The Attack Surface: More Than a Misspelling
The adversary is not just buying yourbrand-coupon.tld. They chain:
- Lookalike domains + typosquatting psychology
- IDN and homoglyph tricks in the user-visible label — IDN homograph phishing
- Search and ad poisoning to surface fakes, covered in malvertising and search poisoning
- Email lures that abuse trust in your brand, related to business email compromise patterns
- Dark web mention and leaked lists when campaigns scale — a primer: dark web brand protection and leaked data
What "Good" Monitoring Looks Like
- Inventory your canonical brands, products, and executive names that attackers spoof
- Generate a permutation set (keyboard proximity, TLD swap, "secure-", "login-", "support-")
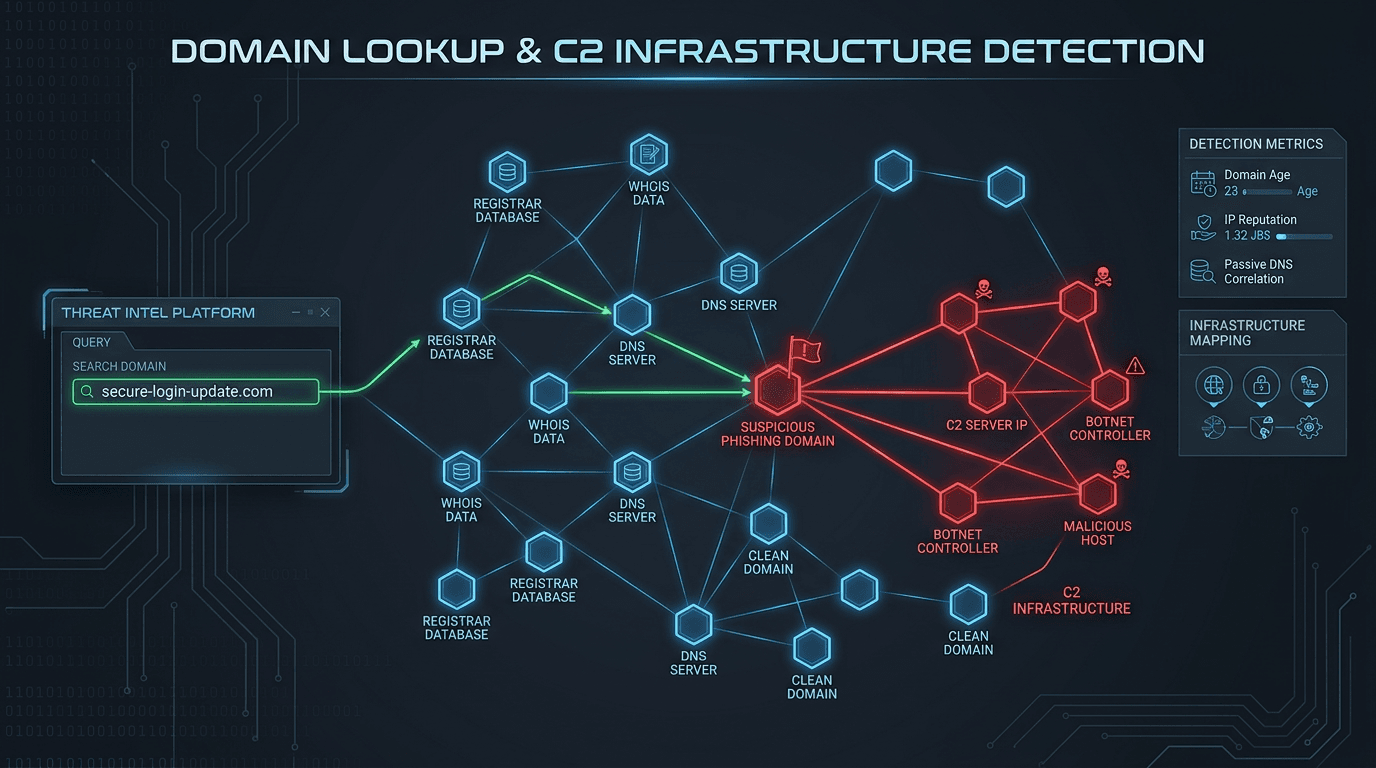
- Enrich each candidate: DNS + hosting + domain reputation and age + landing page heuristics
- Score and cut weekly noise: not every parking page matters
- Route takedowns with evidence packs (screenshots, WHOIS, malware verdicts) — legal loves receipts
Prioritization: A Simple Severity Model
- P0 — live credential phishing, payment flows, or active malware distribution; immediate registrar + hosting abuse, plus customer comms
- P1 — convincing clones without payload yet, or successful SEO/ad placement; fast-track
- P2 — parking/squatting; monitor until weaponized, unless trademark counsel wants proactive claims
- P3 — obviously unrelated lookalikes; close or back-burner
Tie the model to the organization’s risk tolerance and upcoming campaigns (attackers love the SEO noise around a major launch).
Technical Signals That Matter
- CT logs and unexpected certificates for your brand string
- Newly registered domains with high lexical similarity and young WHOIS — a theme we discuss for phishing broadly in phishing with fake and clone domains
- DNS anomalies: fast-flux, shared IPs with known C2 or phishing clusters
- SPF/DMARC alignment failures or suspicious From: domains, cross-read with email authentication in depth
- Reputation lookups for related IPs/URLs using a fast service—see the threat API landscape for 2026
Cross-Team Runbook: Who Does What
| Action | Security | Legal | Comms/Brand | Fraud | | ------------ | ------------------------ | -------------------------- | --------------- | -------------------------- | | Detect | tools + playbooks | trademark watchlists | market intel | ATO/claims routing | | Triage | risk score & infra pivot | UDRP prep if chronic | public FAQ | customer refunds policy | | Takedown | abuse@ packages | legal letters & registrars | customer alerts | blocklists & partner banks |
If you are a smaller org, one owner still documents the lanes—even if the same person wears multiple hats for a day.
Why Fast Enrichment Beats a Spreadsheet of Domains
When you are staring at 400 candidates, you do not need more rows—you need reliable, comparable columns: reputation, first-seen, hosting org, and related hashes if malware is in play. That is the same design philosophy that drives IOC enrichment APIs for SOC work.
isMalicious provides quick IP/domain/URL context so you can separate "someone’s typo blog" from "a hosted phishing kit" before you page legal at midnight.
Related Deep Dives on isMalicious
- How to check malicious domains and IPs — a general workflow
- Domain lookup for phishing and C2 when infrastructure pivots matter
- SIEM+SOAR enrichment design if you automate detection in the SOC
Bottom Line
You cannot out-register every permutation of your brand, but you can run a fast, evidence-driven pipeline that converts noise into takedowns and customer trust. The brands that look "lucky" are usually just instrumented.
When a suspicious host appears in your dashboard, use the isMalicious IP / domain checker to add external reputation context to your abuse ticket the same way you would attach PCAP excerpts—faster to resolve, easier to justify.
Takedown Evidence Pack: What to Attach (Template)
- URL and final redirect chain (not just the first hop)
- Screenshot of the login capture or form fields, with a timestamp
- WHOIS and DNS (registrar, age, nameservers) — you already have strong primers in how to detect malicious domains and IPs
- Relevant malware or phishing family if a payload exists (hash link-out to your sandbox output)
- Your brand’s legitimate domains in a side-by-side comparison table for a rushed lawyer
If you are doing this often, standardize a folder layout so every case has the same file names. Future-you (and the registrar abuse desk) will thank you.
Customer Communications Without Panic
If you are public-facing, avoid posting “there is a malicious domain” without:
- a verifiable customer action (“please never enter credentials on non-
example.comhosts”) - a mechanism to report phish to your team (a mailbox or portal)
- a reassuring line about what is not impacted (e.g., “our SSO provider has not been breached” only if that is provably true)
Phishing and BEC guidance intersect here—see BEC: detection and prevention and anatomy of phishing infrastructure for a deeper dive into how attackers string trust chains together.
Quarterly Review: What to Re-Score in Your Permutation Set
Brands are not static. Revisit your monitoring configuration when:
- you rebrand or launch a new top-level marketing domain
- you acquire a company with a known customer login path
- you add a new product name that becomes a natural typosquat root
- your executive team is targeted in the press (lookalikes spike in the same news cycle)
During the review, delete dead permutations that only create noise, and add the new roots that attackers will buy this quarter. Security is not “set and forget”—it is garden maintenance.
Metrics That Prove the Program (Without Vanity)
- Mean time to first takedown for a confirmed phishing site (hours, not days)
- Customer-reported phish volume trending down after improved monitoring
- Registrar response quality: which providers close abuse fast vs stall
- Repeat offenders: the same reseller or hoster showing up again—those deserve a different relationship, not a new spreadsheet row
For reputation checks during triage, keep domain reputation as a first line of defense in your back pocket: it is not a replacement for takedown, but it is an accelerant for which 10 domains to fight first.
Frequently asked questions
- What is brand impersonation in the domain name context?
- Brand impersonation includes registering or compromising domains that look like a legitimate company—common tactics include misspellings, added hyphens, homoglyphs, extra top-level domains, and confusing subdomains. The goal is usually phishing, ad fraud, or credential theft.
- Should security own brand monitoring?
- It is a shared problem: security handles threat and abuse reporting, marketing/legal manage trademarks and takedown letters, and fraud owns customer impact metrics. A single runbook and prioritization model prevents duplicate tools and warring inboxes.
- What data sources are highest signal?
- Certificate transparency, passive DNS, newly registered domain feeds, and brand-specific permutations, combined with business context (product launches, M&A) that spike registrations. You also need email authentication telemetry for lookalike senders, not just the web landing page.
- How do I avoid endless alerts?
- Score candidates by string distance to your true brands, presence of high-risk TLDs, hosting reputation, and whether the page actually clones your login, not just whether the name looks similar. Pair automated discovery with a weekly human review of the top 20.
- How can isMalicious help during triage?
- When you have a candidate hostname or related IP, isMalicious can help confirm global reputation, linked infrastructure, and provide fast context in parallel with your registrar and hosting abuse workflows.
Related articles
 Jun 4, 2026Shadow AI Governance: How Security Teams Can Detect Risk Without Blocking Innovation
Jun 4, 2026Shadow AI Governance: How Security Teams Can Detect Risk Without Blocking InnovationShadow AI is the new shadow IT: fast adoption, weak visibility, and serious data leakage risk. Security teams need discovery, domain intelligence, policy, training, and monitoring.
 May 4, 2026Security LLM and Agent Workflows: When (and How) to Check Malicious Domains, IPs, and URLs Before Acting
May 4, 2026Security LLM and Agent Workflows: When (and How) to Check Malicious Domains, IPs, and URLs Before ActingAI assistants in SOAR, IDEs, and browser extensions can exfiltrate data or run malicious code if they fetch the wrong link. This guide gives guardrails: schema for tool calls, policy tiers, and where threat intelligence checks belong in the loop.
 May 3, 2026Malicious Infrastructure Clustering: How Passive DNS, TLS Certificates, and ASNs Reveal Shared Campaigns
May 3, 2026Malicious Infrastructure Clustering: How Passive DNS, TLS Certificates, and ASNs Reveal Shared CampaignsA single C2 IP is a clue; shared signing patterns and DNS co-occurrence are a map. This guide explains how defenders cluster infrastructure without chasing ghosts—and how to document findings for IR, threat intel, and law enforcement handoffs.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker