EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
Patch management in 2026 looks nothing like the quarterly spreadsheet exercise it was a decade ago. Modern security teams face thousands of open CVEs at any given moment, each with a technical severity score, a patch that may or may not exist, and a business context that scanners cannot see. The question is rarely “Should we patch?”—it is “Which of the 12,000 open findings should we patch this week, and which can wait safely?” The Exploit Prediction Scoring System (EPSS) is one of the most important answers the security community has produced. This guide covers EPSS end to end: what it is, how it complements CVSS and KEV, how to operationalize it, and where it fits into a modern vulnerability management program.
What EPSS Is—and What Problem It Solves
Traditional vulnerability prioritization leaned on CVSS severity scores. But CVSS measures the technical potential of a flaw, not the real-world probability it will be exploited. The consequence is familiar: organizations spend enormous effort patching “critical” CVEs that never see a working exploit while lower-scored flaws quietly become the next ransomware access vector.
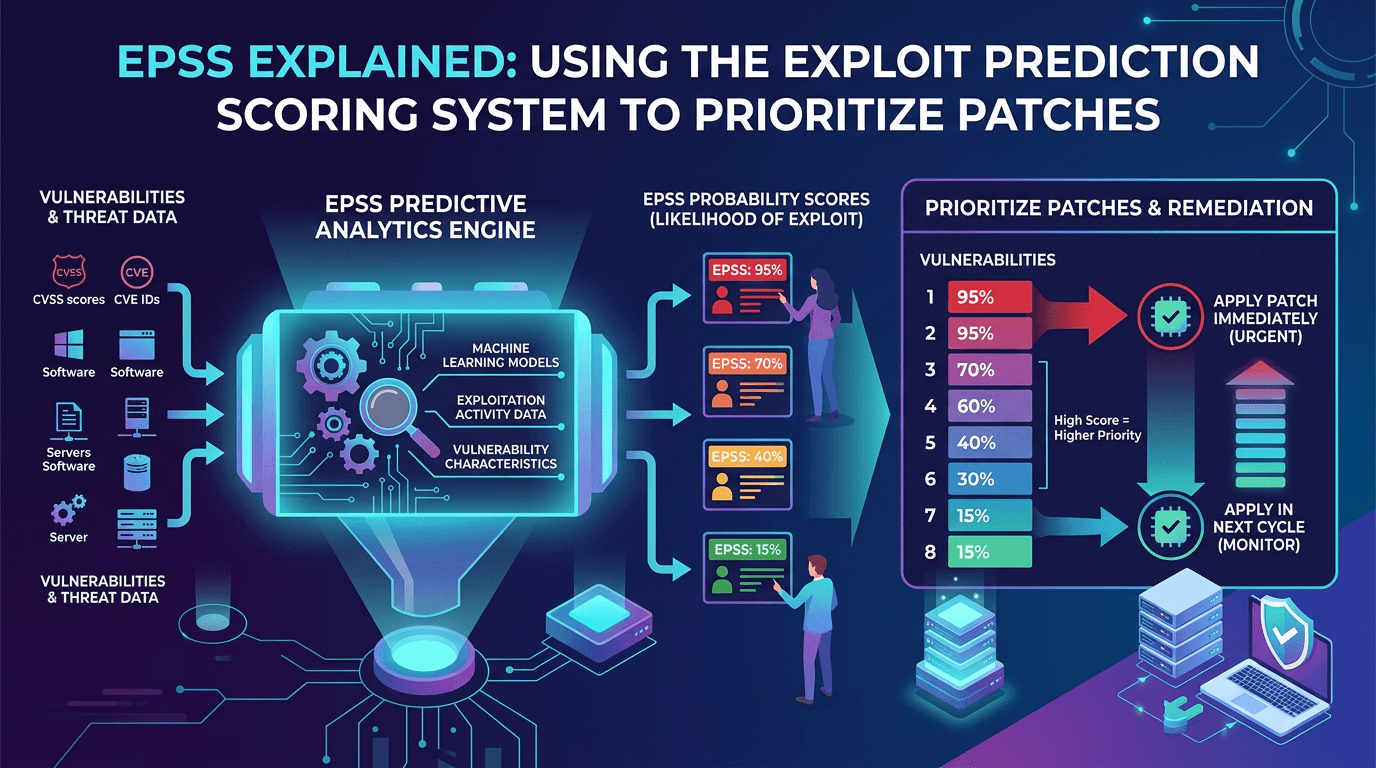
EPSS bridges that gap. Maintained by FIRST (Forum of Incident Response and Security Teams), EPSS produces a daily probability—expressed as a decimal between 0 and 1—that a given CVE will be exploited in the wild within the next 30 days. A CVE with an EPSS score of 0.01 has a 1% probability of exploitation in that window; a CVE with 0.95 has 95%. The percentile alongside each score tells you where that CVE sits among all scored vulnerabilities.
EPSS is not magic. It is a transparent, data-driven machine-learning model trained on real exploitation observations and public vulnerability features. The current production model uses dozens of features—vendor, product, CVE text, CVSS metrics, reference links, exploit code availability, social media and research chatter, among others—and is retrained on fresh telemetry. The model card and performance metrics are published openly, which lets defenders trust the inputs as well as the output.
Why EPSS Complements CVSS and KEV
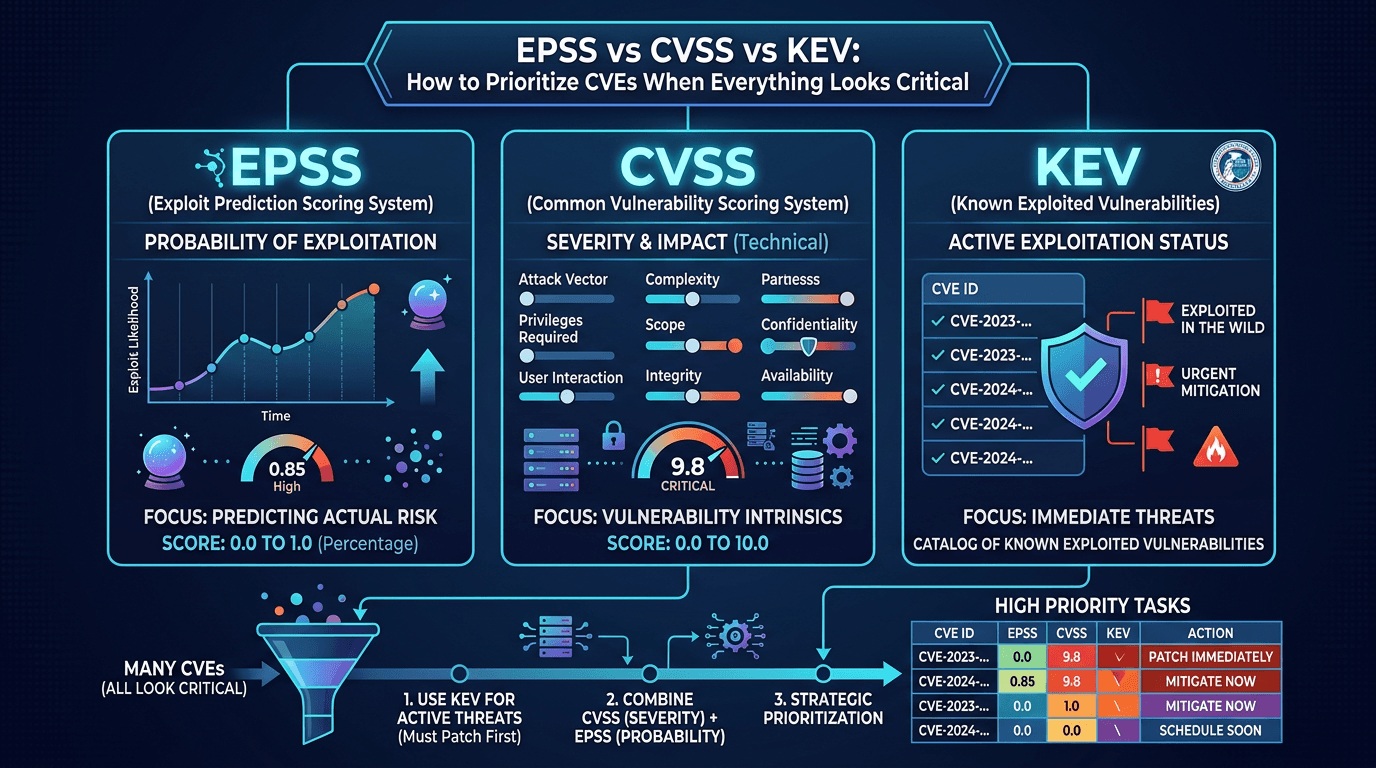
Modern vulnerability management relies on three complementary signals: CVSS, EPSS, and KEV.
- CVSS answers: How severe is this flaw if exploited?
- EPSS answers: How likely is exploitation in the near future?
- KEV (CISA’s Known Exploited Vulnerabilities catalog) answers: Is it confirmed to be actively exploited right now?
Each signal has limits on its own. CVSS alone produces too many critical findings to act on. EPSS alone ignores severity—a 90% exploit probability on a low-impact information disclosure flaw does not warrant the same urgency as a 90% probability on a remote code execution. KEV alone lags reality because it requires confirmed exploitation before inclusion.
Together, the three create a prioritization matrix:
- KEV-listed, high CVSS, high EPSS: Emergency patching.
- High EPSS, high CVSS, not yet KEV: Pre-emergency—patch this week.
- High CVSS, low EPSS, not KEV: Monitor for EPSS movement; patch in normal cadence.
- Low CVSS, low EPSS: Batch with routine maintenance.
For SEO and internal documentation, explaining this matrix explicitly is one of the most requested content formats in vulnerability management circles. Your policy documents benefit from the same clarity.
How EPSS Works Under the Hood
EPSS is a supervised learning model. Training data comes from observed exploitation events contributed by security vendors, government partners, and honeypot networks. The model learns which features of a CVE correlate with exploitation:
- Vendor and product: Some vendors attract more attacker attention than others; certain product categories (VPNs, edge devices, email servers) are consistently higher-risk.
- CVE metadata: Age of the CVE, CVSS metrics, CWE (weakness) categories.
- Code availability: Whether public proof-of-concept code exists.
- References and mentions: Links from security advisories, research blogs, and exploit databases.
- Community chatter: Social media, GitHub repositories, and other public signals of interest.
The model outputs a probability, updated daily. That cadence matters: when exploit code drops for a newly disclosed CVE, EPSS scores rise within 24 hours, giving defenders early warning long before the CVE reaches KEV.
Because EPSS is a model, it has uncertainty. Not every high-EPSS CVE will be exploited, and occasionally a low-EPSS CVE surprises. What EPSS provides is consistently better ranking than CVSS alone—a fact demonstrated repeatedly in independent research.
Operationalizing EPSS in Your Vulnerability Management Program
Step 1: Ingest EPSS Alongside CVSS and KEV
EPSS scores are published daily as CSV and JSON feeds by FIRST, and they are increasingly integrated into commercial scanners, CSPM platforms, and threat intelligence feeds. Your vulnerability data pipeline should pull EPSS daily and store both the probability and the percentile alongside each CVE.
Do not overwrite EPSS history. Trends matter: a CVE whose EPSS doubled in a week deserves attention even if its current absolute value is moderate.
Step 2: Build Prioritization Tiers That Use All Three Signals
A workable tier definition:
- Tier 0 — Emergency: KEV-listed OR (EPSS ≥ 0.5 AND CVSS ≥ 8.0 AND internet-exposed).
- Tier 1 — High: EPSS ≥ 0.1 AND CVSS ≥ 7.0, or any asset-critical system with EPSS ≥ 0.5.
- Tier 2 — Standard: Remaining patchable CVEs handled in normal cadence.
- Tier 3 — Monitor: Low-risk findings with long-tail patch timelines.
Tune thresholds based on your environment, but keep EPSS explicitly in the logic. Teams that quietly default to CVSS-only tiers eventually revert to the old failure mode of over-patching irrelevant flaws.
Step 3: Combine With Asset Context
EPSS tells you about the CVE, not about your deployment. A 0.9 EPSS score on a product you do not use is irrelevant. A 0.2 EPSS score on your primary internet-facing authentication gateway is urgent. Join EPSS data with:
- Asset inventory (which systems run vulnerable versions?).
- Exposure context (is the asset reachable from the internet?).
- Business criticality (revenue impact, data sensitivity).
- Compensating controls (WAF, segmentation, monitoring coverage).
This join is where many programs stumble. Without an accurate, continuously updated software inventory, even perfect EPSS scores produce misaligned work.
Step 4: Automate Reporting and Ticketing
Use EPSS to drive ticket routing automatically. Tier 0 findings should create high-priority tickets with SLAs measured in hours or days, not weeks. Tier 2 findings can batch into sprint backlogs. Embed EPSS and KEV status directly in ticket fields so engineers see the justification without needing to dig.
Dashboards showing percentage of Tier 0 findings remediated within SLA and median time from EPSS spike to patch deployment are more meaningful than raw open-CVE counts.
Step 5: Feed Back Into Detection Engineering
High-EPSS CVEs that you cannot patch immediately deserve compensating detection. Detection engineers should turn EPSS-driven priority into SIEM rules, EDR signatures, and threat hunt hypotheses for exactly those vulnerabilities. This is where vulnerability management and SOC operations converge—EPSS becomes a cross-functional prioritization signal, not a scanner artifact.
Common Misconceptions About EPSS
- “EPSS tells me if I will be breached.” It estimates population-level probability for a CVE, not the risk to your specific environment. Combine with asset context.
- “High EPSS means I must patch today.” Not necessarily. High EPSS + low exposure + strong compensating controls may justify scheduled patching. Document the decision.
- “Low EPSS means I can ignore it.” EPSS is a statistical model with a 30-day window. Flaws outside that window may still warrant remediation on longer timelines.
- “EPSS replaces CVSS.” It does not. The two measure different things.
- “EPSS is proprietary.” FIRST publishes the model specification, feeds, and performance metrics openly.
EPSS and the Broader Threat Intelligence Picture
EPSS is one of the strongest public signals connecting threat intelligence to vulnerability management. It effectively translates attacker behavior into vulnerability priority. But it does not replace other intelligence inputs:
- Threat actor tracking tells you which CVEs a specific group targets (different from general exploitation probability).
- Infrastructure reputation from providers like isMalicious tells you which IPs and domains are actively scanning or exploiting.
- Vendor advisories sometimes include exploit details EPSS has not yet absorbed.
- Internal telemetry occasionally reveals targeted exploitation attempts against your environment that public EPSS cannot see.
A mature program weights all these inputs. EPSS anchors the decision in objective, updated probability while threat intelligence provides color and context.
Measuring the Impact of EPSS Adoption
Programs that integrate EPSS typically observe several benefits over time:
- Reduced patch volume for equivalent risk coverage—patching fewer CVEs while still covering the ones most likely to be exploited.
- Shorter MTTR on Tier 0 findings—because the pipeline surfaces them earlier and with clearer urgency.
- Better cross-functional conversations—engineering teams accept prioritization when it is backed by data rather than fiat.
- Improved audit narrative—regulators and insurers increasingly understand EPSS and credit its use.
Track the ratio of patched vs. exploited CVEs in your environment quarterly. Programs using EPSS tend to see fewer “we had this open and got hit” incidents over time.
When EPSS Will Not Help You
EPSS is a valuable tool, not a universal one. It does not cover:
- Zero-day vulnerabilities before they are assigned CVE IDs.
- Misconfigurations that do not correspond to CVEs.
- Internal-only vulnerabilities where public exploitation signals do not apply.
- Targeted attacker interest—a highly focused adversary may attack a CVE with low public EPSS because it matters to your niche.
For these gaps, lean on internal telemetry, threat modeling, and intelligence about threat actors targeting your sector.
Combining EPSS With Infrastructure Reputation
Threat actors do not only exploit a CVE—they use infrastructure to scan for it, deliver payloads, and exfiltrate data. Pairing EPSS-driven prioritization with real-time reputation data on malicious IPs, domains, and URLs produces the fullest picture. When a high-EPSS CVE is paired with observations of known-bad scanning infrastructure hitting your perimeter, the urgency is unambiguous. Services like isMalicious deliver the reputation layer that transforms EPSS-driven patch queues into confirmed defensive priorities.
Conclusion
EPSS is one of the most important advances in vulnerability management of the last decade. By turning real-world exploitation data into daily probability scores for every CVE, it gives defenders a shared, objective signal to cut through scanner noise. When combined with CVSS severity, KEV confirmation, asset exposure, and live threat intelligence, EPSS transforms patch prioritization from guesswork into a defensible, data-driven discipline.
If your program still prioritizes purely by CVSS, ingest EPSS tomorrow. Build tiers that reference all three scoring systems, tie them to asset context, and measure MTTR against the new priority definitions. The organizations that embrace EPSS now will spend less time patching and more time preventing the attacks that actually matter.
Frequently asked questions
- What is EPSS and who maintains it?
- The Exploit Prediction Scoring System (EPSS) is a data-driven model that estimates the probability a given CVE will be exploited in the wild over the next 30 days. It is maintained by FIRST (the Forum of Incident Response and Security Teams) and updated daily for every published CVE.
- Does EPSS replace CVSS?
- No. CVSS measures technical severity; EPSS estimates exploitation likelihood. They answer different questions and are most powerful when combined. A high-CVSS, low-EPSS vulnerability may be deprioritized; a moderate-CVSS, high-EPSS one may jump the queue.
- How accurate is EPSS?
- EPSS publishes its precision and recall metrics openly, and independent research confirms it outperforms naive approaches like patching by CVSS alone. It is a statistical model, so individual predictions are probabilistic, not guaranteed. The power of EPSS comes from applying it at scale across thousands of vulnerabilities.
Related articles
 Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks CriticalCut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
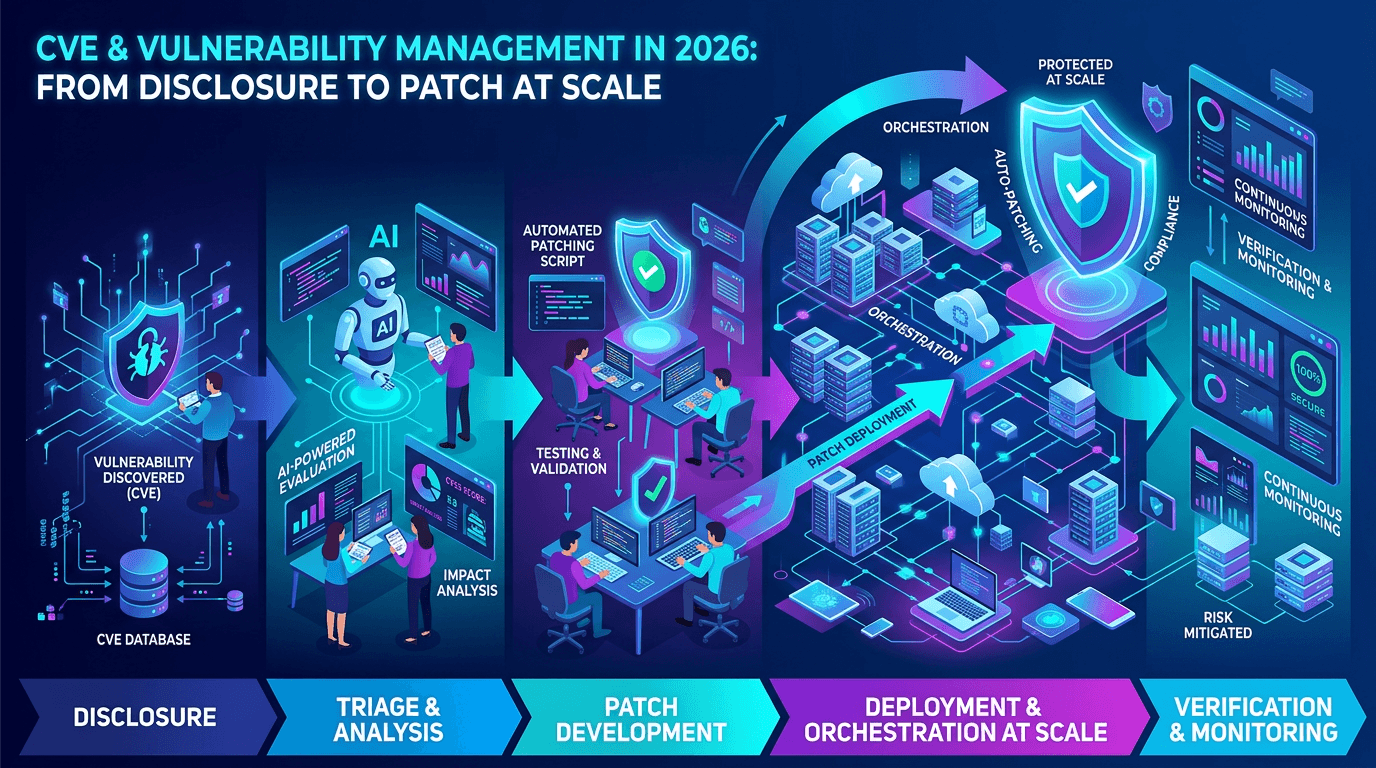 Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at ScaleA practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
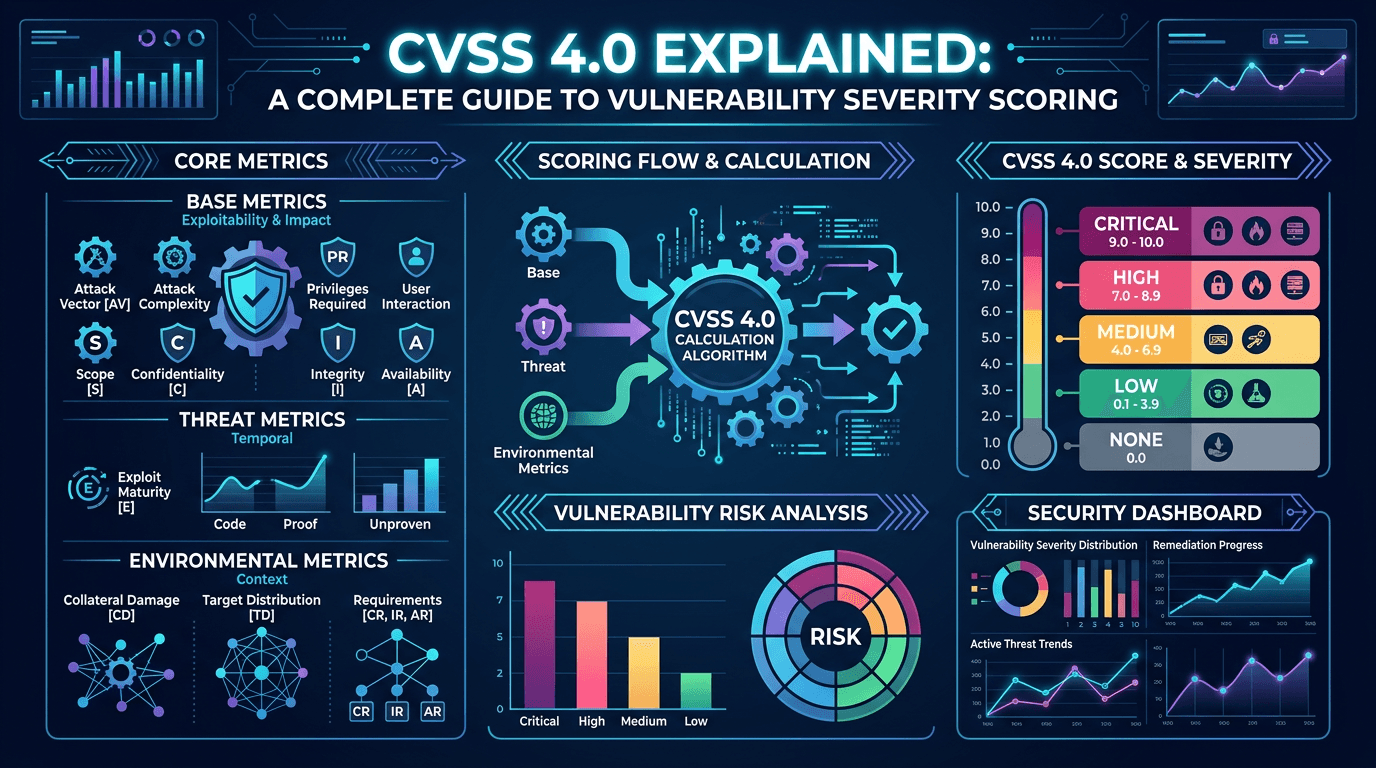 Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026
Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026Master the Common Vulnerability Scoring System v4.0 with a practical breakdown of base, threat, environmental, and supplemental metrics—and learn how to translate CVSS into real-world risk decisions.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker