CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
A practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
If your vulnerability management program still treats every critical finding from a scanner as an emergency, you are optimizing for activity, not risk. In 2026, the challenge is not discovering vulnerabilities—modern tools surface thousands of them—but deciding which ones matter this week for your environment. This guide explains how CVE identifiers fit into the broader vulnerability lifecycle, how scoring systems like CVSS and EPSS differ, and how mature teams connect vulnerability data with threat intelligence and operational reality.
What a CVE Actually Tells You (and What It Does Not)
The Common Vulnerabilities and Exposures program provides a dictionary-style identifier (for example, CVE-2024-12345) and a short description for many publicly known issues. A CVE entry is a coordination artifact: it helps the industry speak a common language when discussing flaws across Linux distributions, cloud platforms, appliances, and desktop software.
What a CVE does not automatically provide is your patch timeline, the exploitability of the issue on your specific build, or whether attackers currently care about it. Two organizations can have the same CVE in their inventories and face completely different risk because one exposes the vulnerable component to the internet while the other has layered network segmentation and strict egress filtering.
For SEO and research workflows, security teams often search by CVE ID when correlating vendor advisories, proof-of-concept repositories, and threat actor chatter. That makes consistent CVE hygiene—accurate asset inventory tied to software versions—foundational. If you cannot map “we run this product, this version, on these systems” to a CVE record, every downstream prioritization model will be guesswork.
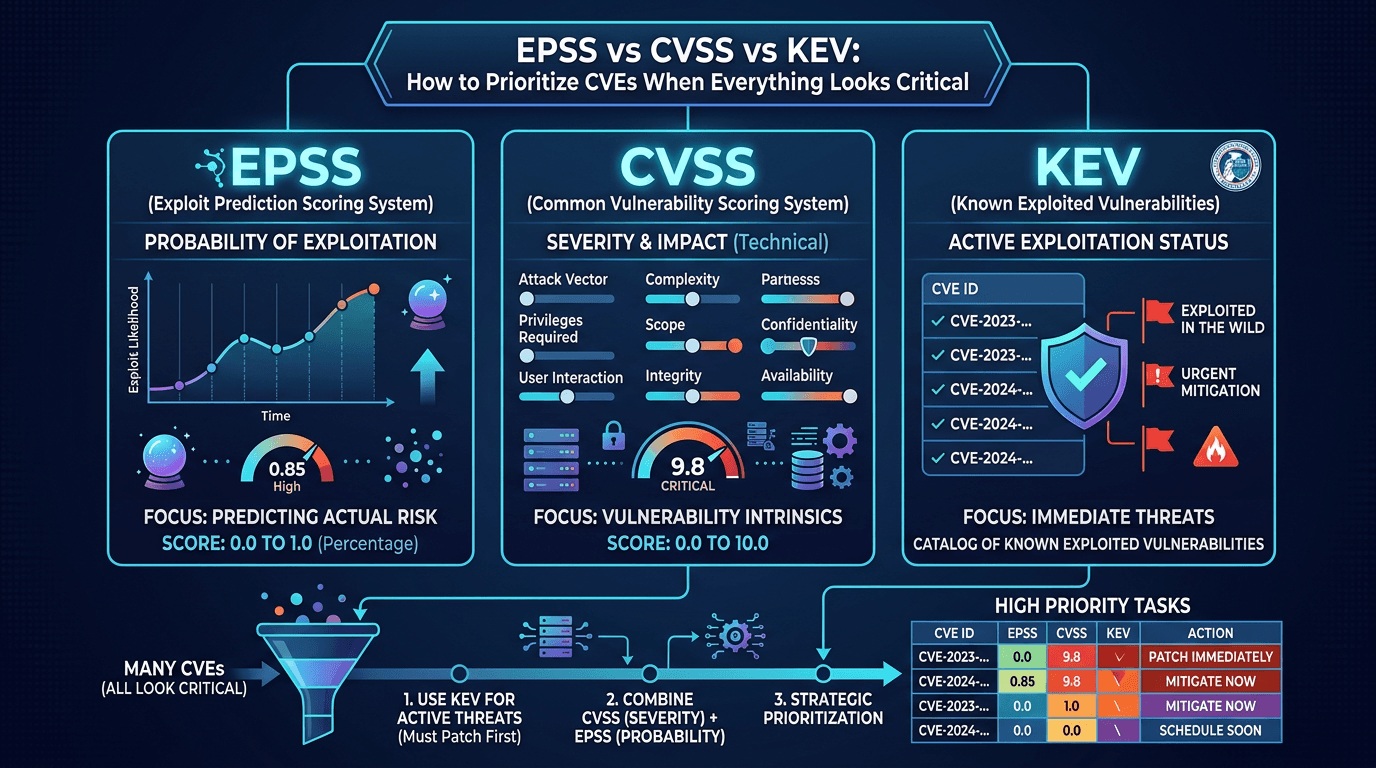
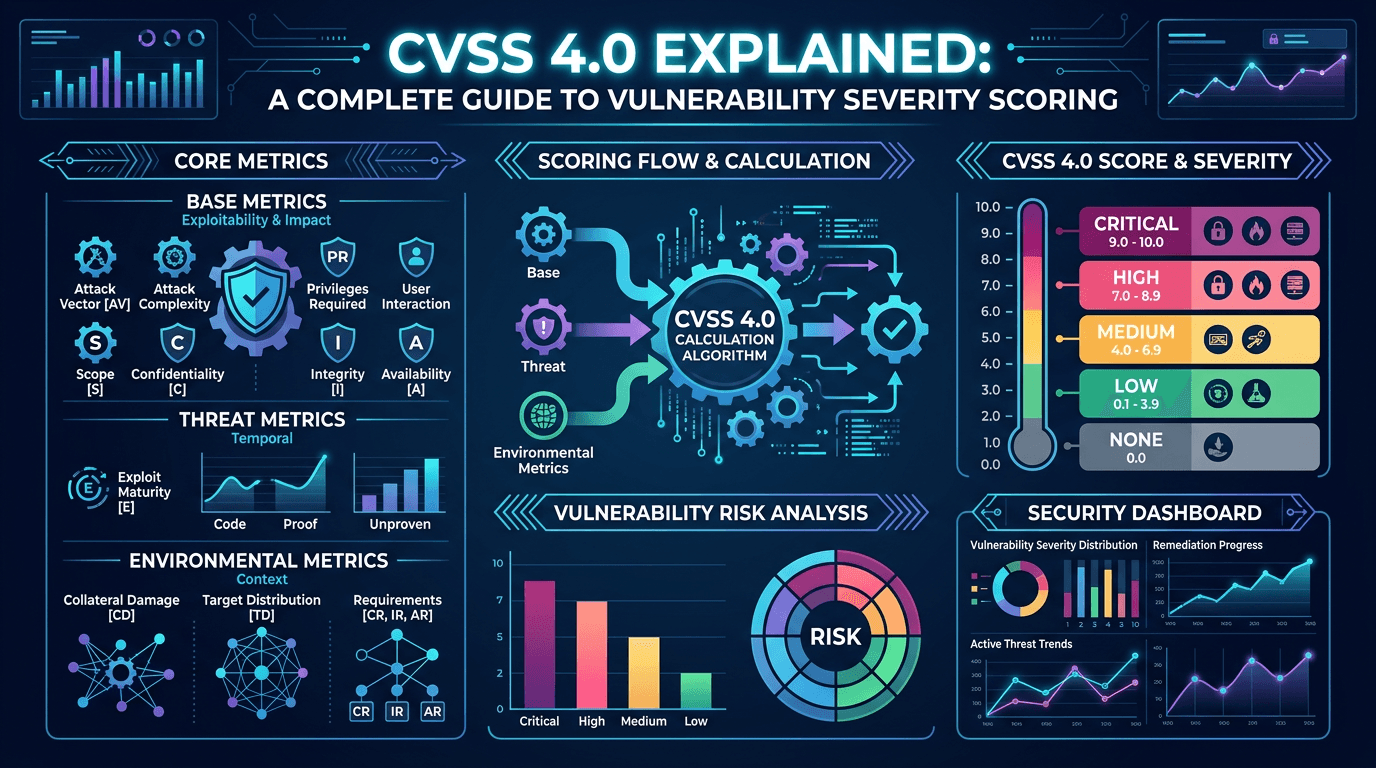
CVSS: Severity, Not Business Impact
The Common Vulnerability Scoring System translates technical characteristics of a vulnerability into a numeric severity score, typically published as a base score alongside vector strings that explain the dimensions (attack complexity, privileges required, user interaction, and so on). CVSS is invaluable for triage at scale because it creates a shared baseline across tools.
The common mistake is treating CVSS as synonymous with “urgency.” A critical CVSS finding on an internal-only management interface that requires authenticated access may still be lower priority than a high CVSS issue on an internet-facing edge service with public exploit code. Mature programs therefore use CVSS as one input among several, not as the entire decision.
Security leaders communicating with non-technical stakeholders should translate CVSS into plain language: what an attacker could do, what must be true for exploitation to succeed, and what detective controls exist today. That narrative connects vulnerability management to business risk far better than a color badge alone.
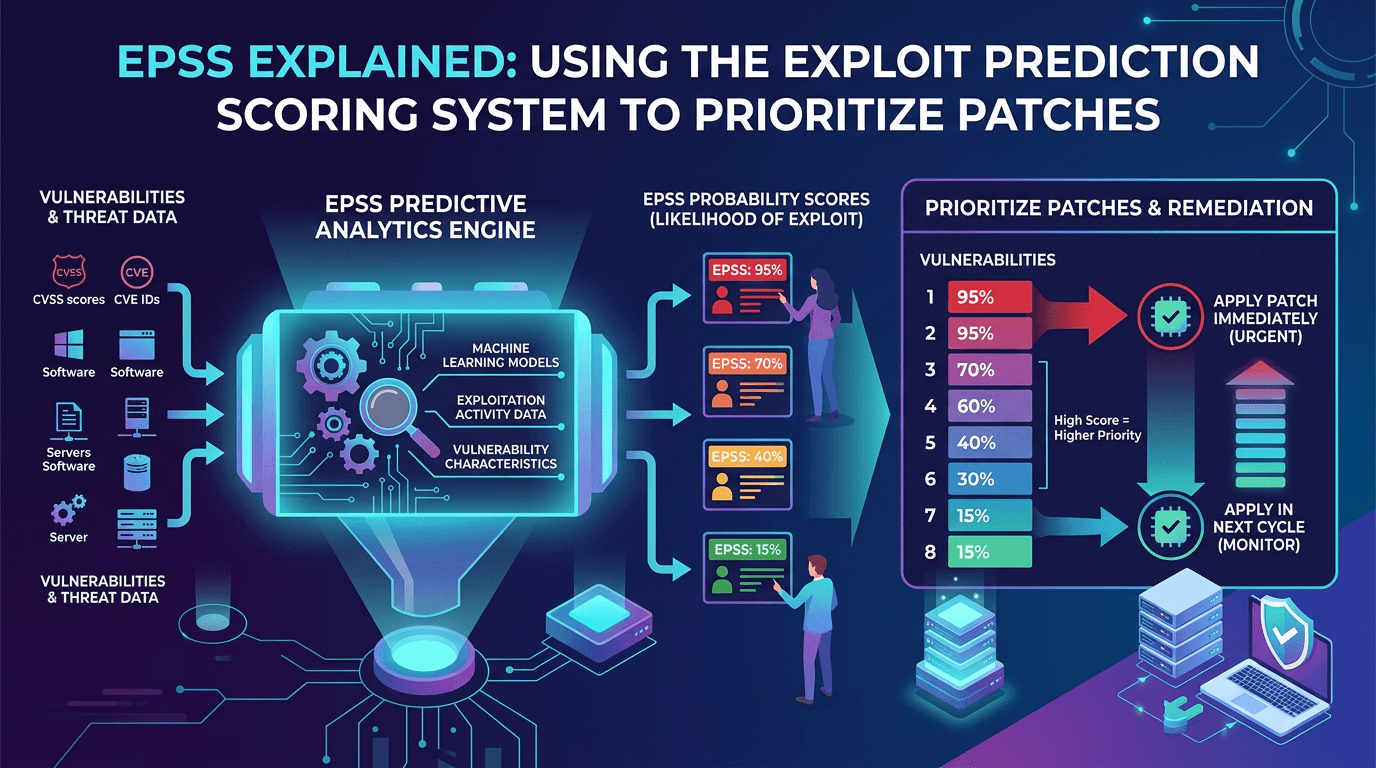
EPSS and Exploit Signals: When Probability Matters
While CVSS focuses on severity, the Exploit Prediction Scoring System (EPSS) estimates the probability that a vulnerability will be exploited in the wild within a defined window. EPSS does not replace CVSS; it answers a different question: “Among thousands of open issues, which are statistically more likely to turn into real incidents soon?”
Another widely used signal is the CISA Known Exploited Vulnerabilities (KEV) catalog, which highlights CVEs with confirmed active exploitation. When a CVE appears on KEV, many regulated environments treat remediation timelines as non-negotiable. Even outside compliance contexts, KEV membership is a strong indicator that threat actors have operationalized the flaw.
For search engine optimization and knowledge-base design, articles that clearly explain the relationship between CVE, CVSS, EPSS, and KEV tend to rank well because practitioners search for those exact comparisons when building programs. Your internal documentation should mirror that clarity so analysts do not confuse “high severity” with “actively exploited.”
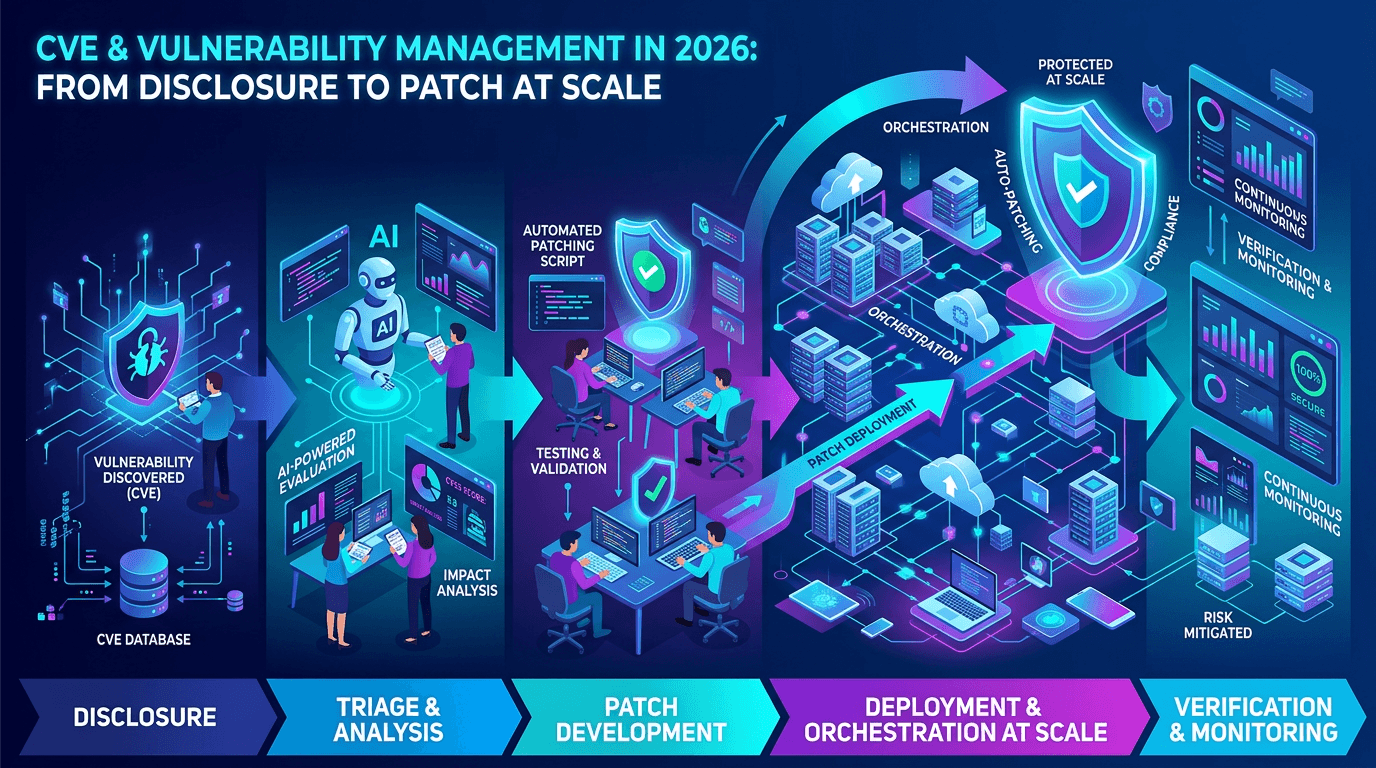
The Vulnerability Lifecycle: From Embargo to Patch
Understanding phases helps you time communications and defensive measures:
- Discovery and private reporting. Researchers or vendors find a flaw. Responsible disclosure often includes an embargo period while patches are prepared.
- CVE reservation and advisory publication. A CVE ID may be reserved before full details are public. Vendor advisories may ship coordinated with or slightly ahead of complete CVE metadata.
- Patch availability. Fixes may appear as operating system packages, container image updates, firmware releases, or SaaS-side changes you do not directly control.
- Exploit development. Public details can accelerate exploit writing. Sometimes exploitation precedes broad public disclosure in targeted campaigns—another reason threat intelligence matters.
- Post-patch verification. Scanning confirms remediation, but configuration drift and shadow IT can reintroduce vulnerable components.
Teams that integrate this lifecycle with change management reduce downtime and avoid “patch thrash,” where emergency changes break production because testing was skipped.
Prioritization Without Paralysis: A Practical Rubric
A workable prioritization model blends technical scores with organizational context. Consider grouping decisions into tiers:
- Tier 0 — Emergency: KEV-listed CVEs affecting internet-facing assets, or flaws with public weaponized exploits targeting your technology stack.
- Tier 1 — High: Critical or high CVSS issues on sensitive systems where exploitation is plausible and compensating controls are weak.
- Tier 2 — Planned: Medium risk with available patches; schedule inside normal maintenance windows with testing.
- Tier 3 — Monitor: Lower immediate likelihood; track for vendor updates and emerging exploit code.
Add explicit criteria for cloud-managed services, where you may rely on the provider’s patch velocity, and for open-source dependencies, where upstream fixes must flow through CI/CD and SBOM-aware pipelines.
Connecting CVEs to Threat Intelligence and Detection
Vulnerability management becomes stronger when linked to threat intelligence feeds that mention CVEs in campaigns, malware families, or ransomware affiliate playbooks. If a CVE appears in reporting about a group targeting your sector, it jumps the queue—even if your CVSS-only ranking would have deferred it.
On the defensive side, ensure your SIEM and EDR content includes detection opportunities tied to high-risk CVEs: suspicious child processes, unexpected DLL loads, or known lateral movement patterns. Prevention matters, but assuming 100% patch coverage is unrealistic; detection extends your safety margin.
Services such as isMalicious focus on actionable reputation and infrastructure intelligence for IPs, domains, and URLs. Pairing that telemetry with a disciplined CVE program gives you both “what is vulnerable” and “what is communicating with known malicious infrastructure”—a fuller picture for incident scoping.
Measurement: KPIs That Reflect Risk Reduction
Scanner counts of open CVEs are easy to game and poor proxies for security outcomes. More meaningful metrics include:
- Mean time to remediate (MTTR) for KEV-listed issues versus standard issues.
- Percentage of critical assets with zero high-risk unpatched CVEs beyond an agreed SLA.
- Recurrence rate after remediation, indicating ineffective fixes or inventory gaps.
- Coverage of application dependencies in your SBOM versus production reality.
Reporting these KPIs quarterly supports budget conversations better than a raw vulnerability count ever will.
Common Pitfalls in CVE Programs
Even experienced teams stumble on a few recurring issues:
- Treating every container base image CVE as equal. Many are in packages not used at runtime; minimal images and distroless builds reduce noise.
- Ignoring transitive dependencies. A vulnerable library deep in a dependency tree may be unreachable in practice—or trivially reachable via a public API.
- Over-relying on network scanners alone. Authenticated scanning and software bills of materials catch issues passive scans miss.
- Failing to document exceptions. Risk acceptance without expiry dates and owners creates silent debt.
Tooling Stacks: ASPM, CSPM, and Traditional VM
Modern enterprises rarely rely on a single “vulnerability scanner.” Application Security Posture Management (ASPM) aggregates findings from static analysis, dynamic testing, and software composition analysis into developer-centric workflows. Cloud Security Posture Management (CSPM) and Kubernetes security tools extend that lens to misconfigurations that might not have a CVE at all—yet still enable breach paths alongside code-level flaws.
The SEO takeaway for buyers researching solutions is that keyword clusters now span “CVE prioritization,” “ASPM,” and “cloud vulnerability management” together. Your internal architecture should define which system is authoritative for which asset class: endpoints, servers, containers, SaaS configurations, and serverless functions may each live in different tools. Without that split, duplicate CVE tickets for the same underlying library waste engineering hours and obscure true exposure.
Integration patterns that work well include: normalizing CVE identifiers into a central ticketing system; attaching business unit and data classification tags; and pushing “patch candidate” groups to CI/CD owners rather than generic infrastructure queues when the fix is a dependency upgrade.
Finally, schedule quarterly tabletop exercises that feature a hypothetical CVE with partial public exploits: validate that monitoring, comms, and patch channels activate as designed before a real emergency.
Regulatory and Insurance Pressure
Cyber insurance questionnaires and frameworks such as NIST, ISO 27001, and sector-specific rules increasingly ask how organizations handle critical vulnerabilities—not merely whether antivirus is installed. Demonstrating a repeatable process for CVE intake, risk scoring, and remediation timelines strengthens audit narratives. When regulators reference KEV-style catalogs, align your internal SLAs to those expectations or document compensating controls explicitly.
Conclusion
CVE identifiers and scoring frameworks are essential scaffolding for modern security, but they are not substitutes for judgment. Combine CVSS severity with exploit prediction, confirmed exploitation signals, asset exposure, and threat intelligence about actor behavior. Build workflows that turn that synthesis into patch schedules, detection coverage, and clear metrics. When your program communicates trade-offs honestly—what you fixed now, what you mitigated, and what you are watching—you earn organizational trust and reduce real risk rather than checkbox risk.
If you are expanding your security content strategy, pages that explain CVE lifecycle, vulnerability management prioritization, and the difference between EPSS and CVSS continue to attract organic search traffic because they map directly to how practitioners research solutions. Keep your published guidance updated as scoring versions and vendor practices evolve—search engines reward freshness in technical categories as much as they reward depth.
Frequently asked questions
- What is a CVE identifier?
- A CVE (Common Vulnerabilities and Exposures) identifier is a standardized name for a publicly disclosed security vulnerability. It helps vendors, researchers, and defenders refer to the same issue across tools, advisories, and threat intelligence feeds.
- Does a high CVSS score always mean I must patch immediately?
- Not necessarily. CVSS describes technical severity in a standardized way, but priority also depends on exposure, asset criticality, compensating controls, and whether the flaw is actively exploited in the wild. Teams should combine CVSS with exploit intelligence and business context.
- What is the difference between a vulnerability and an exploit?
- A vulnerability is a weakness in software or configuration. An exploit is a method or code that takes advantage of that weakness. A CVE can exist for years before reliable public exploits appear—or exploitation can begin within hours of disclosure.
Related articles
 Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks CriticalCut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
 Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
 Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026
Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026Master the Common Vulnerability Scoring System v4.0 with a practical breakdown of base, threat, environmental, and supplemental metrics—and learn how to translate CVSS into real-world risk decisions.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker