EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Cut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
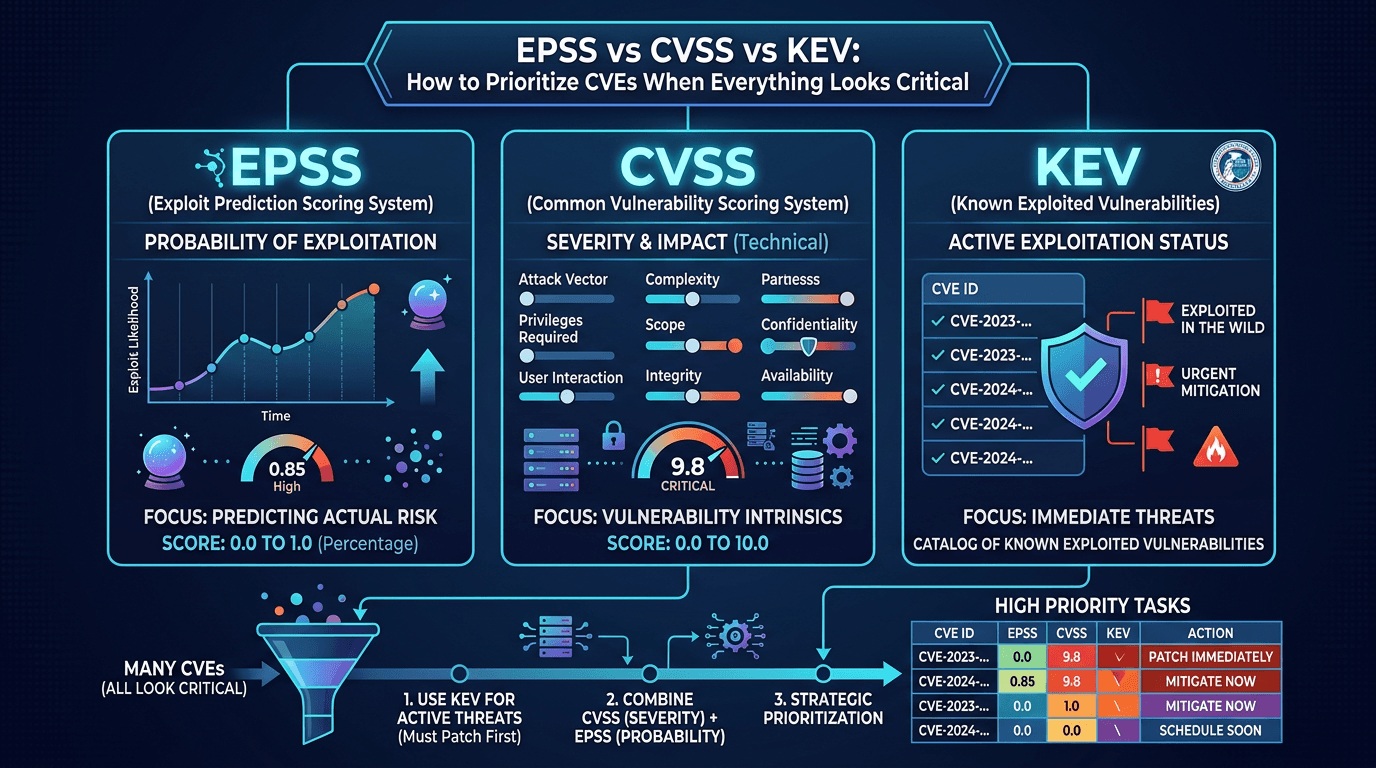
Scanning tools label thousands of findings “high” or “critical,” executives ask for a single risk score, and engineers want a patch order that respects uptime. Meanwhile CVE databases grow daily. The industry’s answer has been layered scoring: CVSS for severity, EPSS for exploitation probability, and KEV for confirmed in-the-wild use. This article compares those frameworks without mythologizing any single number, then proposes a decision workflow vulnerability management and SOC leaders can adopt—aligned with threat intelligence on threat actors and exploit activity.
CVSS: A Severity Baseline, Not a Crystal Ball
The Common Vulnerability Scoring System expresses how bad a flaw could be if successfully exploited, using metrics like attack vector, complexity, privileges required, user interaction, and impacts to confidentiality, integrity, and availability. CVSS v3 and v4 refine how environmental and supplemental metrics can tailor scores—though not every vendor displays the full vector string clearly in dashboards.
Strengths:
- Interoperability: Nearly every scanner exports CVSS, enabling rough triage across vendors.
- Transparency: Vector strings explain why a score is high—helpful for peer review.
Limits:
- Severity ≠ exploitability in the wild. A theoretically devastating bug may never see reliable exploitation, while a medium issue becomes catastrophic on your exact deployment.
- Environmental blindness out of the box. Default base scores do not know your architecture.
For SEO, pages that clearly define CVSS components rank because newcomers constantly search “what is CVSS” and “CVSS vs severity.” Include examples with vector fragments to improve snippet quality.
EPSS: Probability, Not Pain
The Exploit Prediction Scoring System outputs a probability between 0 and 1 (often shown as a percentage) that a CVE will be exploited in the next 30 days (definition subject to model updates—always cite the official specification version in internal policy). EPSS complements CVSS by answering prevalence and attacker interest questions grounded in observed telemetry.
Strengths:
- Prioritization at scale: When tens of thousands of backlog items exist, EPSS helps rank order beyond static severity.
- Dynamic signal: Scores update as the world learns more about exploitation trends.
Limits:
- Model opacity for some users: Practitioners must understand confidence intervals and data limitations—not treat EPSS as deterministic truth.
- Rare assets: Low prevalence CVEs might still matter critically to you if you are the niche target.
Combine EPSS with asset criticality: a moderate EPSS on internet-facing authentication infrastructure may outrank a higher EPSS on an isolated lab cluster.
KEV: Ground Truth on Exploitation
The CISA Known Exploited Vulnerabilities catalog lists CVEs with confirmed exploitation, often with due dates for federal civilian agencies under binding operational directives—private sector organizations increasingly mirror those timelines voluntarily.
Strengths:
- Executive clarity: “On KEV” is a powerful, simple trigger for emergency change windows.
- Alignment with adversary behavior: If threat actors actively use a flaw, theoretical debates about CVSS nuance matter less.
Limits:
- Not exhaustive: Absence from KEV does not prove safety—especially immediately after disclosure.
- Lag potential: Some exploits spread in closed channels before broad confirmation.
Treat KEV as a hard requirement tier in your policy, but maintain rapid response processes for zero-day or private exploit chains not yet cataloged.
Putting the Three Together: A Practical Matrix
Consider a two-axis model:
- Technical severity (CVSS) — how damaging exploitation could be.
- Real-world urgency (EPSS + KEV + threat intel) — how likely you are to face exploitation soon.
Example policy tiers:
- P0 — Emergency: KEV-listed CVE affecting exposed systems, or threat intelligence confirming active campaigns against your sector using the CVE, regardless of EPSS if internal sightings exist.
- P1 — Accelerated: High CVSS plus high EPSS, even if not yet on KEV, on sensitive assets.
- P2 — Planned: Medium scores with compensating controls and available patches within monthly cycles.
- P3 — Backlog: Low immediate risk; track for vendor updates.
Document exceptions with risk acceptance; auditors prefer explicit waivers over silent neglect.
Threat Intelligence Enriches Scoring
Feeds may report exploit modules in Metasploit, sightings in honeypots, or IP addresses scanning for vulnerable services. When such signals align with a CVE, escalate priority even if EPSS lags. Conversely, if threat intelligence shows exploitation confined to unrelated technology stacks, you might downgrade urgency after validation.
Platforms exposing IP and domain reputation help correlate scanning waves with patch deployment timelines—useful when deciding temporary firewall rules while updates propagate.
Organizational Challenges: Change Management and Downtime
Even correct prioritization fails without maintenance windows and testing. DevOps cultures should embed dependency updates into CI/CD with automated tests; legacy environments may require phased rollouts. Communicate that CVSS does not mandate a patch deadline by itself—your SLA derives from policy layered on top.
Vendor and Cloud Nuances
SaaS products may patch transparently; your responsibility shifts to configuration reviews and API key hygiene. IaaS users must track CVEs in guest OS images, Kubernetes node pools, and hypervisor layers—each with different owners. Centralize accountability in a vulnerability council that includes application, platform, and business unit representatives.
Metrics That Matter
- MTTR for KEV-listed CVEs versus non-KEV.
- Percentage of critical assets compliant within SLA.
- Recurrence after failed patch attempts—signals broken pipelines or inventory gaps.
Avoid incentivizing teams purely on “open CVE count down” without context; that encourages hiding findings or gaming scanners.
Communication with Developers
Developers often resent “critical” tickets without context. Provide CVE descriptions, CVSS vectors, EPSS snapshots, and reproduction guidance. Link to official advisories and recommended fixed versions. When file hashes of vulnerable libraries matter (for example, supply chain issues), include SHA-256 identifiers to eliminate ambiguity.
Legal and Disclosure Considerations
Publishing internal prioritization frameworks externally (for example, on a company blog) can aid SEO and customer trust but avoid revealing unfixed critical exposures. Generic methodologies—as in this article—are safer than infrastructure-specific timelines.
Common Mistakes
- Treating CVSS 10 as automatically more urgent than KEV 8—context beats single numbers.
- Ignoring compensating controls like WAF rules that buy time—document them explicitly.
- Failing to revisit priorities after major vendor patches or new exploit releases.
Tabletop: When Scores Disagree
Simulate a scenario where CVSS is moderate, EPSS spikes overnight, and KEV listing is pending. Train stakeholders to decide under uncertainty: temporary network isolation, increased logging, expedited patch testing. These drills reduce panic during real events.
Conclusion
CVSS, EPSS, and KEV answer different questions; mature programs blend them with asset knowledge and threat intelligence. Stop debating which score is “right” and start embedding them into transparent policies developers and operators can execute. The winning organizations measure outcomes—reduced exploitable footprint and faster remediation—not vanity leaderboard positions on vulnerability counts.
For SEO, sustained rankings come from updating this guidance when scoring specifications change and linking to authoritative references. Readers searching “EPSS vs CVSS” want comparison tables and implementation advice—deliver both.
Appendix Mindset: Continuous Improvement
Re-evaluate weightings annually: as attackers automate exploitation, EPSS distributions shift. As your estate moves cloud-native, CVE sources in orchestrators and service meshes gain prominence. Keep an ear to threat actor reporting—ransomware affiliates often cluster around a handful of reliable CVEs until defenses catch up. Your prioritization model is a living document, not a one-time spreadsheet.
Bridging to Broader Risk Registers
Align CVE tiers with enterprise risk management language: tie P0 issues to board-level operational risk categories where appropriate. That alignment secures funding for tooling and headcount—far more effective than technical complaints alone.
CVSS v4 and Supplemental Metrics: Planning Your Toolchain Upgrade
As ecosystems adopt CVSS v4, vendor UIs will surface additional metric groups aimed at finer-grained severity communication. Security architecture teams should plan parser upgrades so ticketing systems continue to ingest vector strings without dropping supplemental context. Regression-test integrations whenever scanners change CVSS versions—misread scores silently skew dashboards.
Training materials should explain v4 concepts in plain language for engineering managers who approve sprint work against CVE backlogs; searchable internal articles reduce repetitive explanations.
SSVC and Stakeholder-Specific Prioritization
CISA’s Stakeholder-Specific Vulnerability Categorization (SSVC) offers decision trees that incorporate mission impact, safety, and exposure—valuable when CVSS alone feels misaligned with societal or operational consequences. You can map SSVC outcomes to the same P0–P3 tiers used for KEV and EPSS-driven workflows, creating a unified vocabulary across infrastructure, OT, and product security teams.
Document when SSVC overrides raw CVSS: medical devices, manufacturing lines, and public safety systems often warrant bespoke logic.
Reducing Scanner Noise Without Hiding Risk
Duplicate findings across tools inflate counts. Deduplicate by normalized CVE ID plus affected component instance. Suppress dev-only environments from production SLAs while still tracking issues—transparency beats shadow backlogs that explode during audits.
Triage automation can label findings with both EPSS and business unit tags so product owners receive filtered queues instead of raw scanner dumps.
CMDB Accuracy as a Force Multiplier
Even perfect CVSS/EPSS/KEV logic fails if configuration management databases list phantom servers. Invest in discovery accuracy; tie ownership fields to on-call rotations. When an emergency KEV patch drops, the first question is “where are we vulnerable?”—inventory answers faster than ad hoc spreadsheets.
Coordinating with Threat Hunting
Hunters proactively search for exploitation artifacts tied to high-EPSS CVEs affecting your stack—even before scanners prove missing patches. Combine hunt hypotheses with IP reputation spikes against perimeter logs. This is where threat intelligence platforms and vulnerability data intersect beyond ticketing.
Publishing Transparency for Customers and Partners
SaaS providers increasingly publish trust-center statements summarizing how they handle emergent CVEs—mean time to remediate, customer notification thresholds, and whether KEV issues trigger automatic maintenance windows. If you operate a platform, align marketing copy with engineering reality; SEO-driven prospects compare those statements side by side when choosing vendors.
Revisit this narrative after major industry incidents; freshness signals competence to readers and search engines alike. Small updates beat stale “ultimate guides” that never reflect new scoring releases.
Frequently asked questions
- What does CVSS measure?
- CVSS measures the technical severity of a vulnerability using standardized metrics like exploitability and impact. It helps compare issues consistently but does not directly measure real-world exploitation likelihood or your specific exposure.
- What is EPSS used for?
- EPSS estimates the probability that a vulnerability will be exploited in the wild in the near term. It helps teams prioritize among many vulnerabilities, especially when combined with business context.
- What is the CISA KEV catalog?
- The Known Exploited Vulnerabilities catalog lists CVEs with confirmed active exploitation. Many organizations treat KEV entries as mandatory fast-track remediation targets, sometimes tied to regulatory or insurance expectations.
Related articles
 May 24, 2026EPSS et CVE : utiliser la probabilité d’exploitation sans perdre le contexte métier
May 24, 2026EPSS et CVE : utiliser la probabilité d’exploitation sans perdre le contexte métierEPSS aide à trier les CVE selon leur probabilité d’exploitation, mais il doit être combiné avec KEV, CVSS, CPE, exposition et criticité métier.
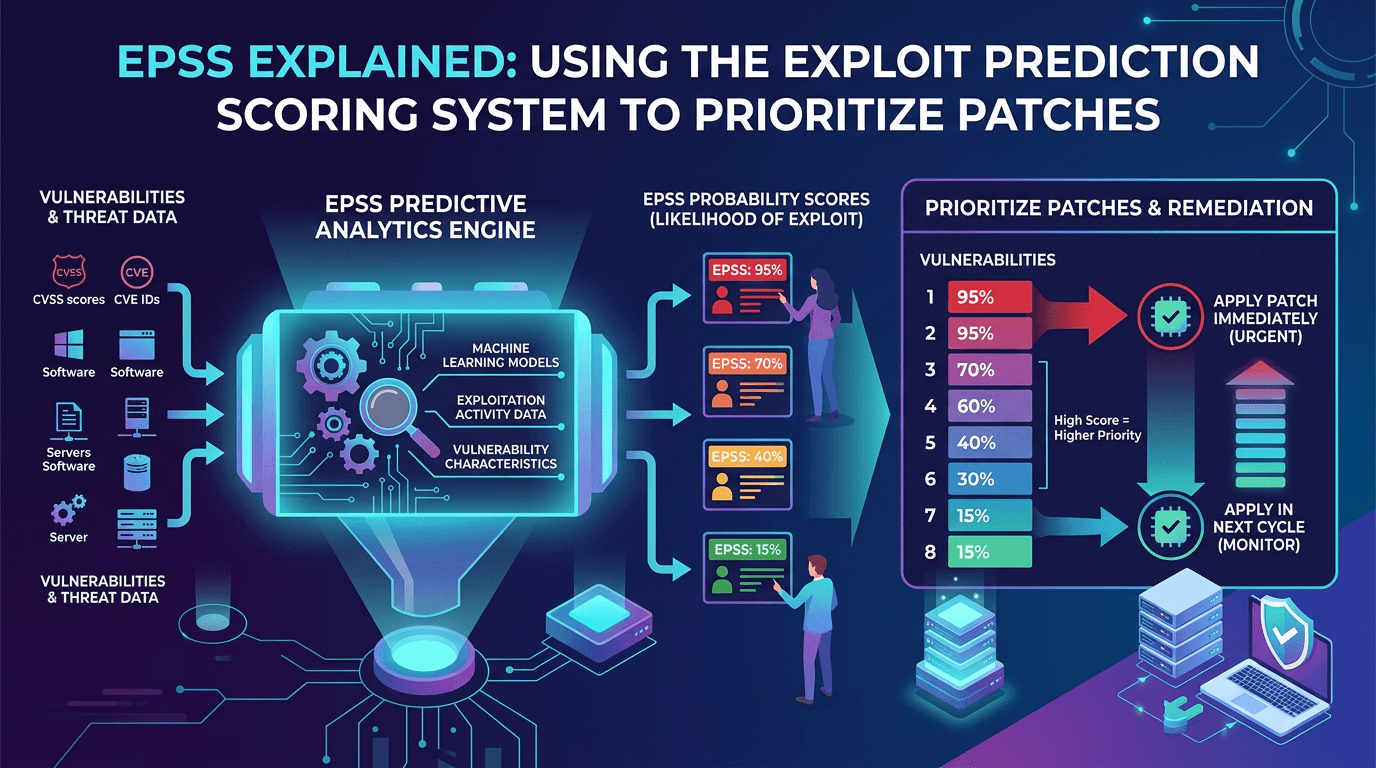 Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
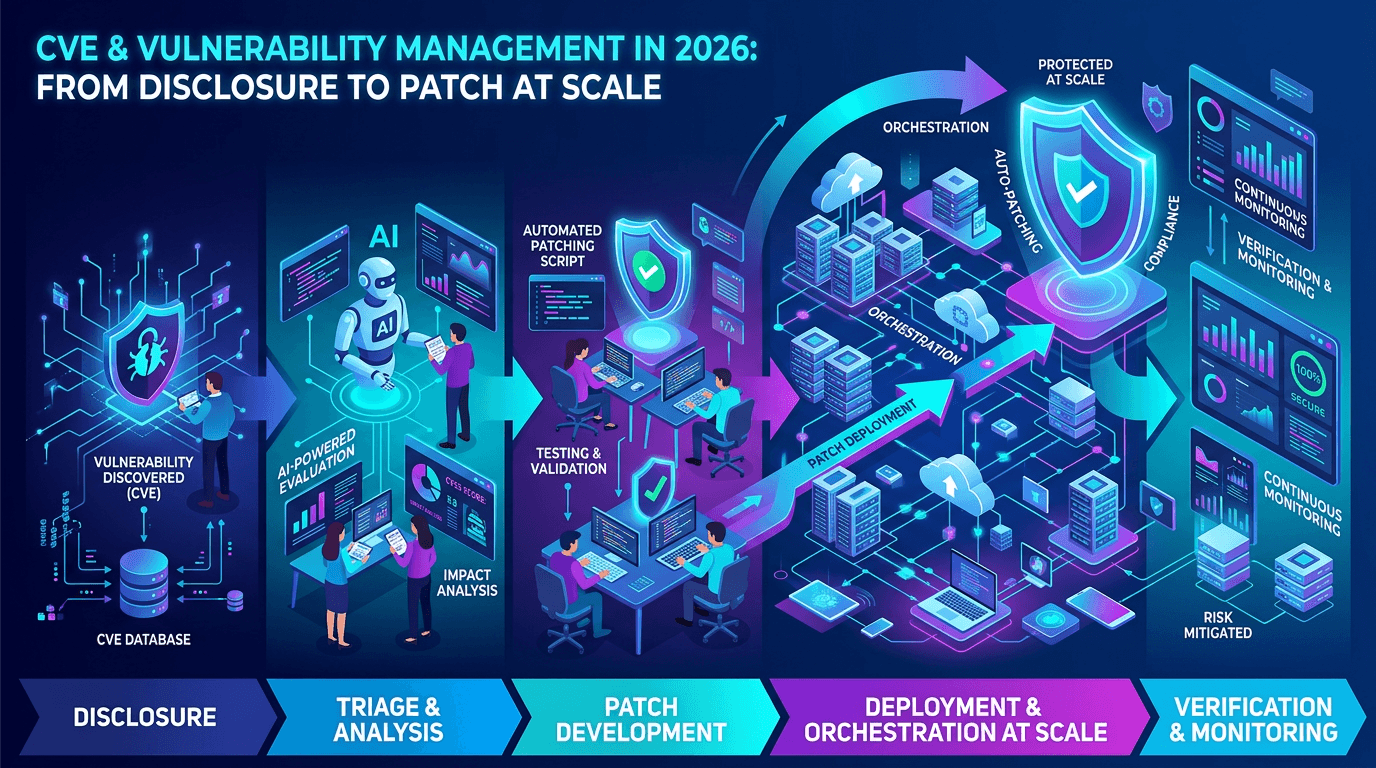 Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at ScaleA practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker