CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026
Master the Common Vulnerability Scoring System v4.0 with a practical breakdown of base, threat, environmental, and supplemental metrics—and learn how to translate CVSS into real-world risk decisions.
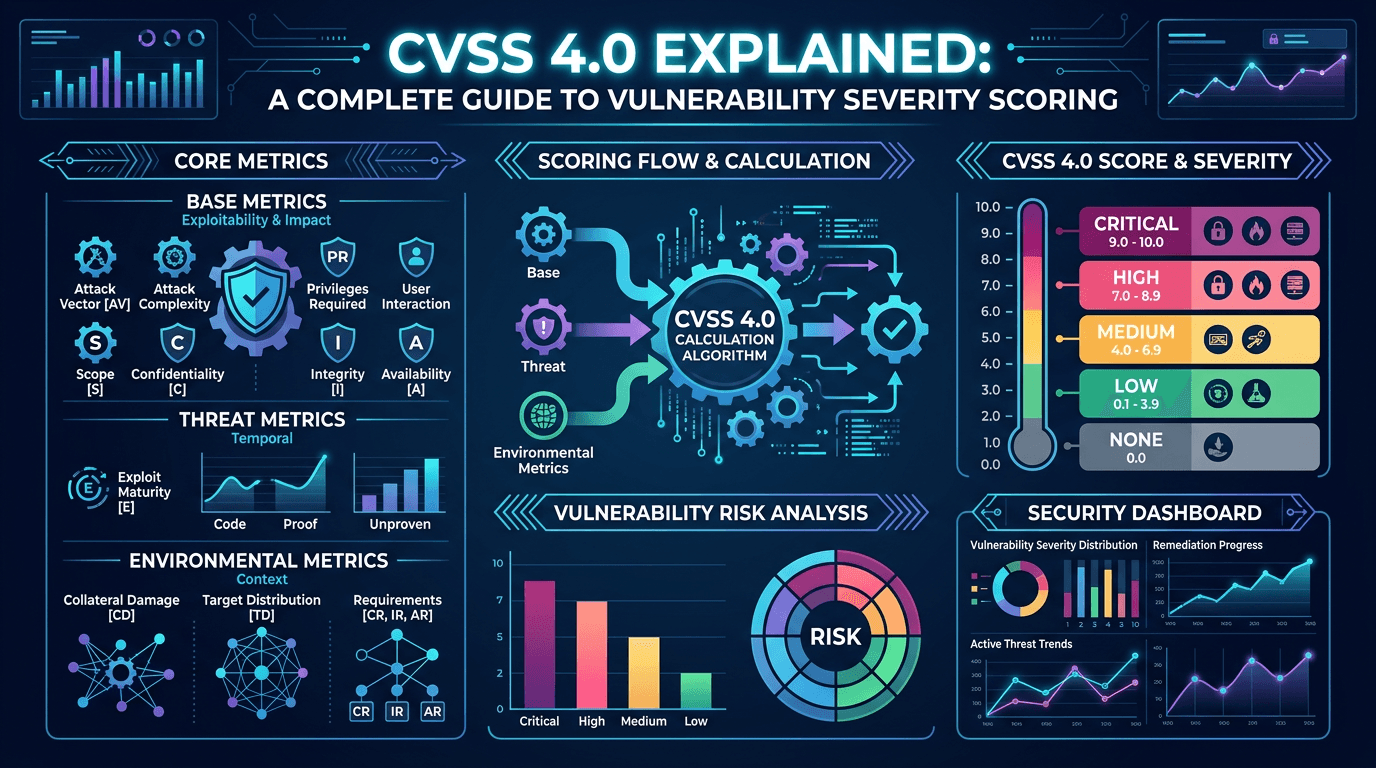
Few acronyms in security have traveled as far as CVSS. The Common Vulnerability Scoring System appears in CVE records, vendor advisories, vulnerability scanners, SIEM dashboards, and board-level risk reports. In 2026, most mature programs have moved—or are actively moving—from CVSS 3.1 to CVSS 4.0, a revision that reshapes how defenders reason about vulnerability severity and priority. This guide walks through CVSS 4.0 end to end: the base metrics, the new threat and supplemental groups, how the environmental lens changes scoring, and how to translate numeric output into defensible patch management decisions.
Why CVSS Matters for CVE and Vulnerability Management
Every published CVE (Common Vulnerabilities and Exposures) entry is a coordination artifact—an industry agreement on a unique identifier for a disclosed flaw. CVSS is the companion language that describes how severe that flaw is in a standardized, vendor-neutral way. Without CVSS, comparing a Linux kernel issue to a web application authentication bypass would require a narrative; with CVSS, both resolve to the same 0–10 scale with a documented vector string.
For security teams, CVSS enables three things at scale: triage (quickly sorting thousands of findings), communication (translating between engineering, leadership, and auditors), and automation (encoding priority rules into ticketing, CI/CD gates, and cloud posture tools). But CVSS alone is not enough. The “S” stands for scoring system, not decision system—and CVSS 4.0 is explicit about that distinction, encouraging teams to combine the base score with temporal threat data and environmental context.
Search demand for CVSS 4.0 has climbed sharply since its finalization, as practitioners compare the new framework with CVSS 3.1 and look for clear guidance on migration. Understanding the nuances now pays dividends across compliance reporting, insurance questionnaires, and customer trust disclosures that increasingly reference CVSS vectors by name.
The CVSS 4.0 Metric Groups at a Glance
CVSS 4.0 organizes information into four complementary metric groups:
- Base metrics: Intrinsic characteristics of the vulnerability that do not change over time or environment.
- Threat metrics: Information about real-world exploitation and maturity that evolves after disclosure.
- Environmental metrics: Overrides reflecting the deploying organization’s unique context.
- Supplemental metrics: Additional descriptors (not folded into the score) that communicate nuances such as safety impact, recovery effort, and response urgency.
This structure replaces the CVSS 3.1 split of “Base / Temporal / Environmental” with a clearer separation between what is known about the flaw and what is known about attackers and your environment. It also introduces CVSS-BT (Base + Threat) and CVSS-BTE (Base + Threat + Environmental) as the canonical scoring variants beyond the raw base score, which makes it easier to describe which layer of context a given score incorporates.
Base Metrics: What the Vulnerability Itself Looks Like
The base group answers: if an attacker tries to exploit this, how hard is it, and what happens when they succeed? CVSS 4.0 keeps familiar dimensions but sharpens several of them.
- Attack Vector (AV): Network, Adjacent, Local, or Physical. This describes how remote the attacker can be.
- Attack Complexity (AC): Low or High. High now explicitly reflects defender-controlled obstacles like ASLR or non-default configurations.
- Attack Requirements (AT): New in 4.0. Captures conditions outside the attacker’s control, such as race windows or required victim network topology.
- Privileges Required (PR): None, Low, or High. Critical for distinguishing pre-auth from post-auth flaws.
- User Interaction (UI): None, Passive, or Active. CVSS 4.0 separates automatic triggers from those needing deliberate user action.
- Vulnerable System Impact (VC/VI/VA): Confidentiality, Integrity, and Availability impact on the vulnerable component.
- Subsequent System Impact (SC/SI/SA): Impact on downstream or otherwise connected systems—effectively a more precise replacement for the old Scope metric.
The split between vulnerable system and subsequent system is one of the most practically useful changes. In CVSS 3.1, the binary Scope metric often collapsed nuance: either a flaw crossed a trust boundary or it did not. CVSS 4.0 lets scorers express that a sandboxed flaw has high impact on the sandboxed component but low impact on the host—or vice versa. This precision is especially valuable for containers, hypervisors, and browser exploitation chains where downstream impact is the whole point.
Threat Metrics: Bringing Exploitation Reality Into the Score
CVSS 3.1 had a Temporal metric group, but it was optional, rarely populated consistently, and often ignored by scanners. CVSS 4.0 elevates this context into a dedicated Threat group and renames the core metric:
- Exploit Maturity (E): Not Defined, Attacked, POC, or Unreported. “Attacked” is the new high-signal state, indicating confirmed exploitation in the wild.
The shift matters for prioritization because a base score is a ceiling, not a live risk indicator. A CVE with a base score of 9.1 but no known exploitation after a year in the wild behaves differently from a 7.8 CVE that appeared last week in ransomware affiliate chatter. Feeding threat metrics into your pipeline—via CISA’s Known Exploited Vulnerabilities (KEV) catalog, EPSS probability scores, vendor threat bulletins, and paid exploit intelligence—is the cleanest way to let your CVSS-BT number track reality.
From an SEO and documentation standpoint, explaining to stakeholders the difference between base score, threat-adjusted score, and environmental score produces lasting content value: practitioners repeatedly search for these comparisons when building or auditing programs.
Environmental Metrics: Your Network Is Not the Reference Machine
Environmental metrics let defenders modify the score based on how a vulnerable asset is actually deployed. In 4.0, you can override base metrics (for example, declaring that in your deployment user interaction is required because a WAF blocks direct exploit paths) and apply asset-importance modifiers for Confidentiality, Integrity, and Availability.
Two environmental additions are especially valuable:
- Modified Attack Requirements (MAT) and Modified Attack Vector (MAV): Useful when compensating controls (network segmentation, jump hosts, service meshes) constrain how reachable the flaw really is.
- CIA requirements (CR/IR/AR): Reflect the classification of data or the criticality of an asset. A low-impact flaw on a healthcare database holding PHI may still warrant a high environmental score; a medium-impact flaw on a stateless test service may not.
Environmental scoring is where CVSS stops being a universal catalog number and starts reflecting your actual risk. Organizations that skip this step consistently find themselves patching the wrong 500 CVEs every quarter while the real exposure sits quietly in an unscored corner of their environment.
Supplemental Metrics: Safety, Automatable, Recovery, and More
CVSS 4.0 introduces supplemental metrics that do not affect the numeric score but do travel with the vector string for downstream decision-making:
- Safety (S): Indicates whether exploitation could cause physical harm—crucial for operational technology, medical devices, automotive, and industrial control systems.
- Automatable (AU): Whether exploitation can be scripted against targets at scale.
- Recovery (R): Whether the system can auto-recover or requires manual restoration.
- Value Density (V): Whether a single compromise yields concentrated or diffuse attacker value.
- Vulnerability Response Effort (RE): Expected effort to remediate.
- Provider Urgency (U): Vendor-communicated urgency (Clear, Green, Amber, Red).
Supplemental metrics let your internal workflow encode context that matters but does not belong in a universal severity number. For example, an Automatable + Attacked vulnerability might trigger an immediate “enterprise-wide detection sweep” pipeline even if the score is only 6.5.
From CVSS 4.0 Score to Risk Decision
A mature process translates CVSS vectors into action through a repeatable rubric. A workable baseline:
- Ingest the vendor base score and store the complete vector string.
- Enrich with threat metrics—KEV listing, EPSS probability, exploit code availability—to compute CVSS-BT.
- Apply environmental modifiers tied to asset inventory: internet exposure, data classification, compensating controls.
- Evaluate supplemental flags, escalating Safety or Automatable concerns even when the numeric score looks moderate.
- Map the final CVSS-BTE score to a tier: emergency (patch inside 24–72h), high (inside SLA), planned, or monitor.
Documenting this rubric inside your vulnerability management policy converts subjective scrum-room debates into deterministic decisions that audit well. It also gives security leadership a clear lever for communicating trade-offs: if the business wants SLAs shortened, the rubric exposes the staffing and tooling that must change to support it.
CVSS 4.0 and the Broader Threat Intelligence Picture
No scoring system exists in a vacuum. Threat intelligence services, ransomware trackers, and infrastructure-reputation tools like isMalicious round out the picture by telling you who is exploiting a CVE and what infrastructure they are using. Even a carefully computed CVSS-BTE score benefits enormously from operational signals: watchlisted domains, malicious IPs, and command-and-control indicators that reveal whether the adversary is already at your gate.
Integrating CVSS-based prioritization with live threat telemetry is a hallmark of modern security operations. It lets a SOC say, “CVE-2026-xxxxx scores 8.7 with attacked exploit maturity, affects our perimeter, and we are currently seeing connections to known C2 infrastructure for the family abusing it—escalate.” That sentence, powered by CVSS 4.0 plus enrichment, is what good vulnerability management sounds like.
Common Pitfalls When Adopting CVSS 4.0
Even teams moving decisively to CVSS 4.0 stumble on recurring issues:
- Treating CVSS-B as the final answer. The base score is deliberately context-free. Use CVSS-BT or CVSS-BTE in prioritization.
- Ignoring supplemental metrics. Safety and Automatable flags sometimes matter more than the headline number for ICS and SaaS environments.
- Not recording vector strings. Store the full vector, not just the numeric score. Audits and re-scoring require the raw data.
- Underestimating migration effort. Dashboards, SLAs, and ticket templates often hardcode CVSS 3.1 thresholds; a 4.0 rollout touches more systems than people expect.
- Overfitting to CVSS. It is one signal. CVE + EPSS + KEV + internal threat modeling remain essential.
CVSS, Compliance, and the 2026 Regulatory Landscape
Regulators and cyber insurance providers increasingly reference specific CVSS thresholds in their expectations. Frameworks like NIST SSDF, ISO 27001 annexes, and sector rules for healthcare, finance, and critical infrastructure now lean on CVSS-based SLA language. CVSS 4.0’s richer environmental layer actually helps defenders here: you can demonstrate to auditors that your prioritization reflects data sensitivity and compensating controls, not just raw severity numbers from a scanner.
If your organization publishes public vulnerability disclosure policies, updating them to reference CVSS 4.0 vectors signals maturity to security researchers, customers, and procurement teams reviewing your posture. It is a small change with measurable trust impact.
Conclusion
CVSS 4.0 is not merely a cosmetic version bump—it is a more expressive, more honest framework for describing vulnerabilities. By separating what the flaw is from what attackers are doing from what your environment looks like, it provides the structure modern vulnerability management programs need to cut through scanner noise. Pair it with threat intelligence, EPSS probabilities, KEV membership, and asset-level context from tools such as isMalicious, and you have a prioritization engine that reflects reality instead of ceremony.
Invest now in the plumbing: update ingestion pipelines to parse CVSS 4.0 vectors, align internal SLAs to CVSS-BTE rather than CVSS-B, and train analysts on the new supplemental metrics. The organizations that internalize CVSS 4.0 early will spend the next decade patching less—because they will be patching what actually matters.
Frequently asked questions
- What is CVSS 4.0 and how is it different from CVSS 3.1?
- CVSS 4.0 is the latest version of the Common Vulnerability Scoring System, published by FIRST. It refines the base metric group, introduces a dedicated Threat metric group for real-world exploitability signals, expands environmental scoring, and adds supplemental metrics such as Safety, Automatable, and Recovery. Compared with CVSS 3.1, it reduces score clustering in the "high/critical" range and better reflects downstream impact beyond the vulnerable component.
- Should I switch from CVSS 3.1 to CVSS 4.0 immediately?
- Most vendors and tools are in a transition period where both scores are published. You should begin ingesting CVSS 4.0 vectors where available, map them into your prioritization workflow, and keep CVSS 3.1 parity for historical reporting. A phased adoption avoids noisy re-prioritization while still capturing the improved signal from 4.0.
- Does a CVSS 4.0 score of 9.8 always mean "patch today"?
- No. CVSS reflects technical severity, not organizational urgency. A 9.8 issue on an internal lab host with no inbound connectivity may be lower priority than a 7.5 issue on an internet-facing authentication gateway. Combine CVSS with exploit intelligence, asset exposure, and business context before declaring an emergency.
Related articles
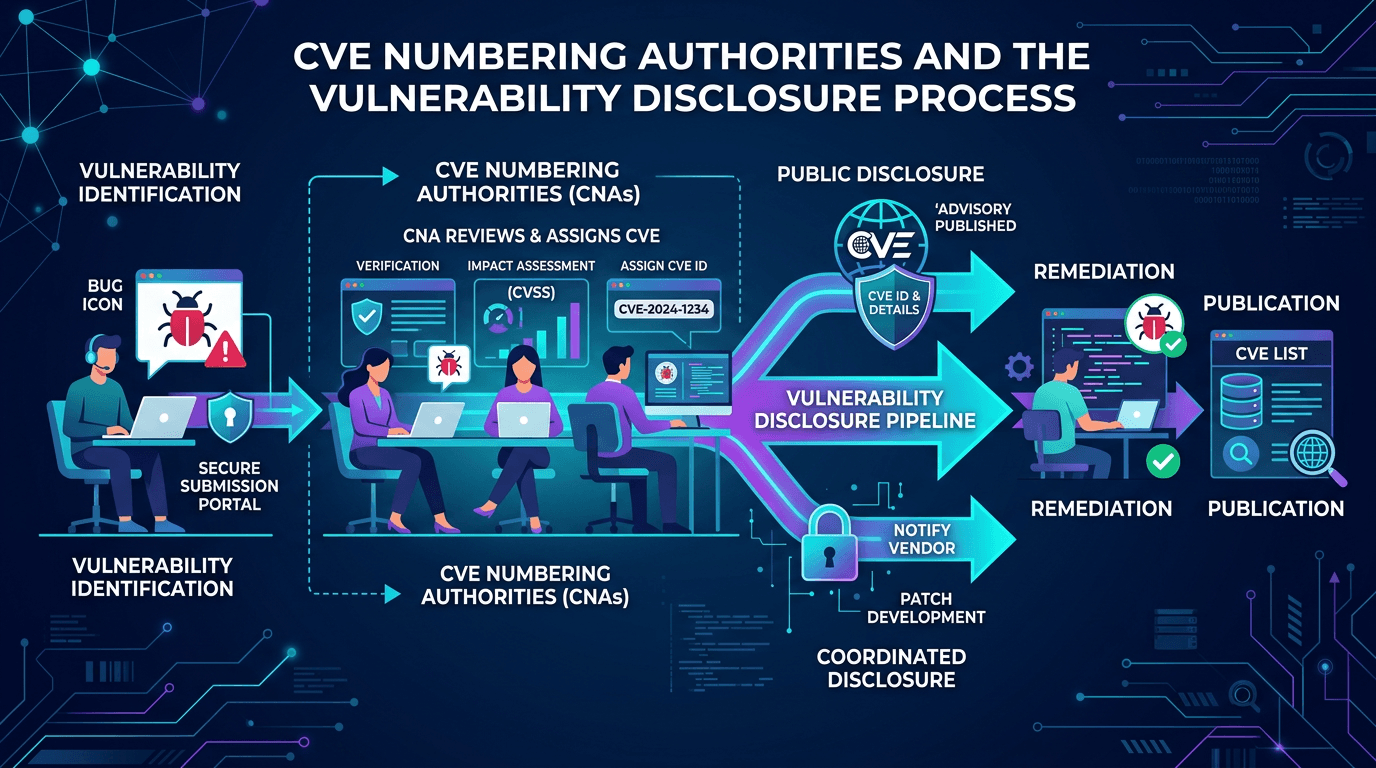 Apr 25, 2026CVE Numbering Authorities and the Vulnerability Disclosure Process: A 2026 Practitioner Guide
Apr 25, 2026CVE Numbering Authorities and the Vulnerability Disclosure Process: A 2026 Practitioner GuideUnderstand how CVEs are born—from initial vulnerability discovery through CNA assignment, coordinated disclosure, and publication—plus how this pipeline shapes defender priorities and SEO-visible vulnerability data.
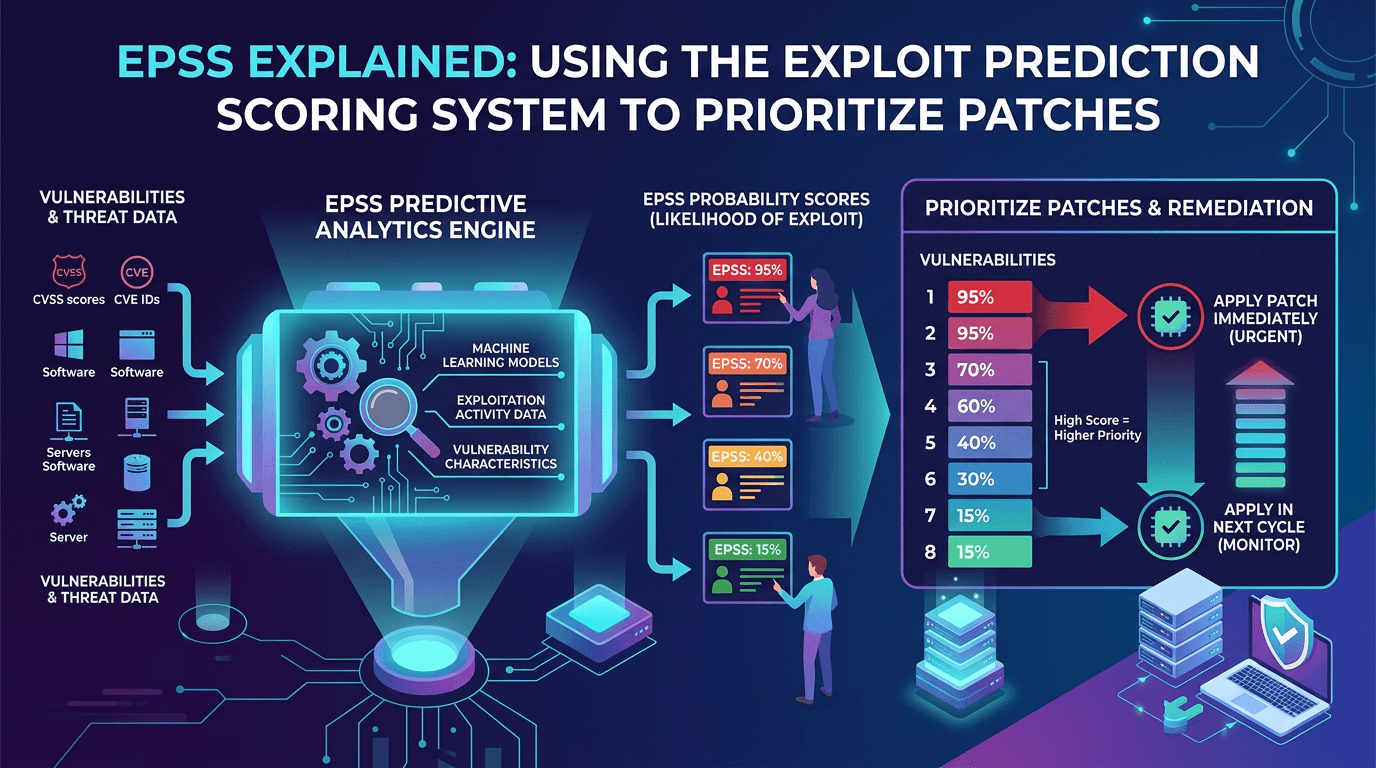 Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
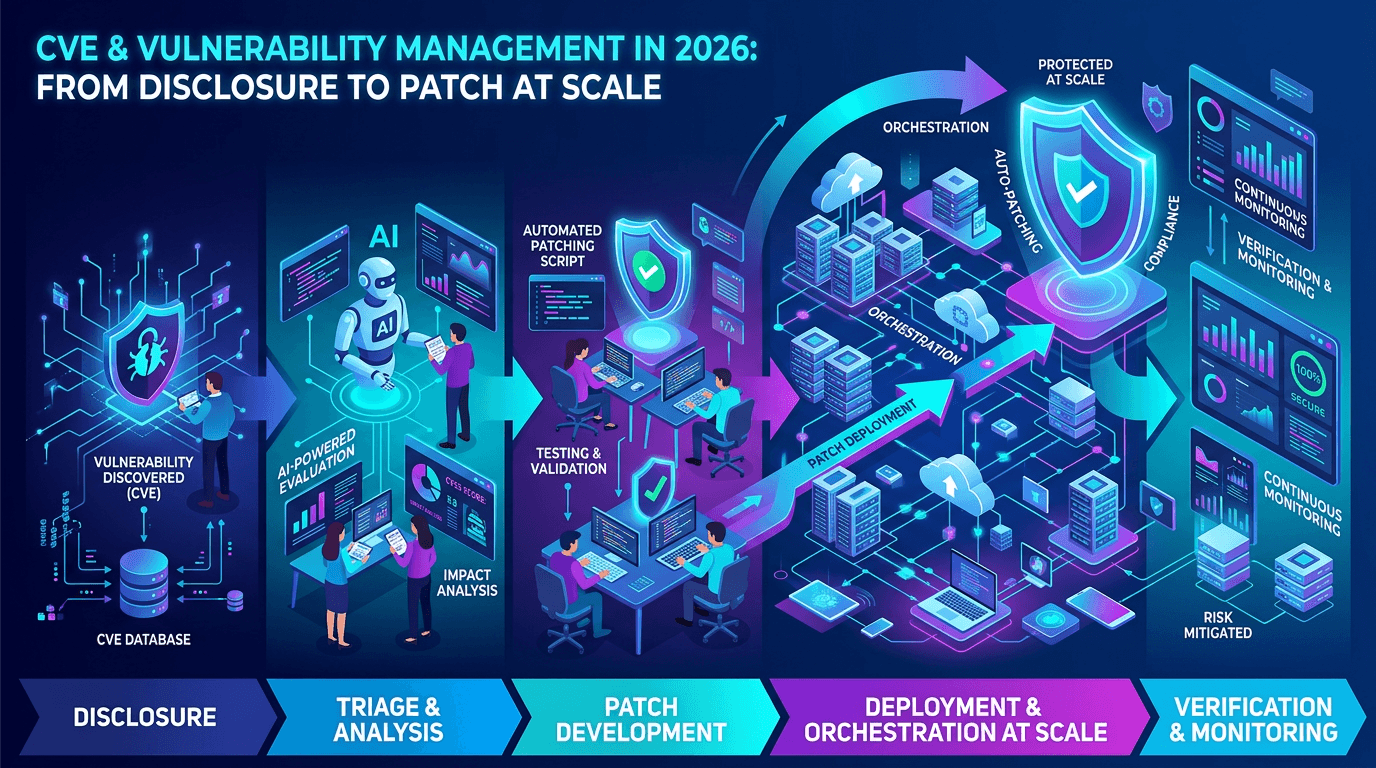 Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at ScaleA practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker