CVE Numbering Authorities and the Vulnerability Disclosure Process: A 2026 Practitioner Guide
Understand how CVEs are born—from initial vulnerability discovery through CNA assignment, coordinated disclosure, and publication—plus how this pipeline shapes defender priorities and SEO-visible vulnerability data.
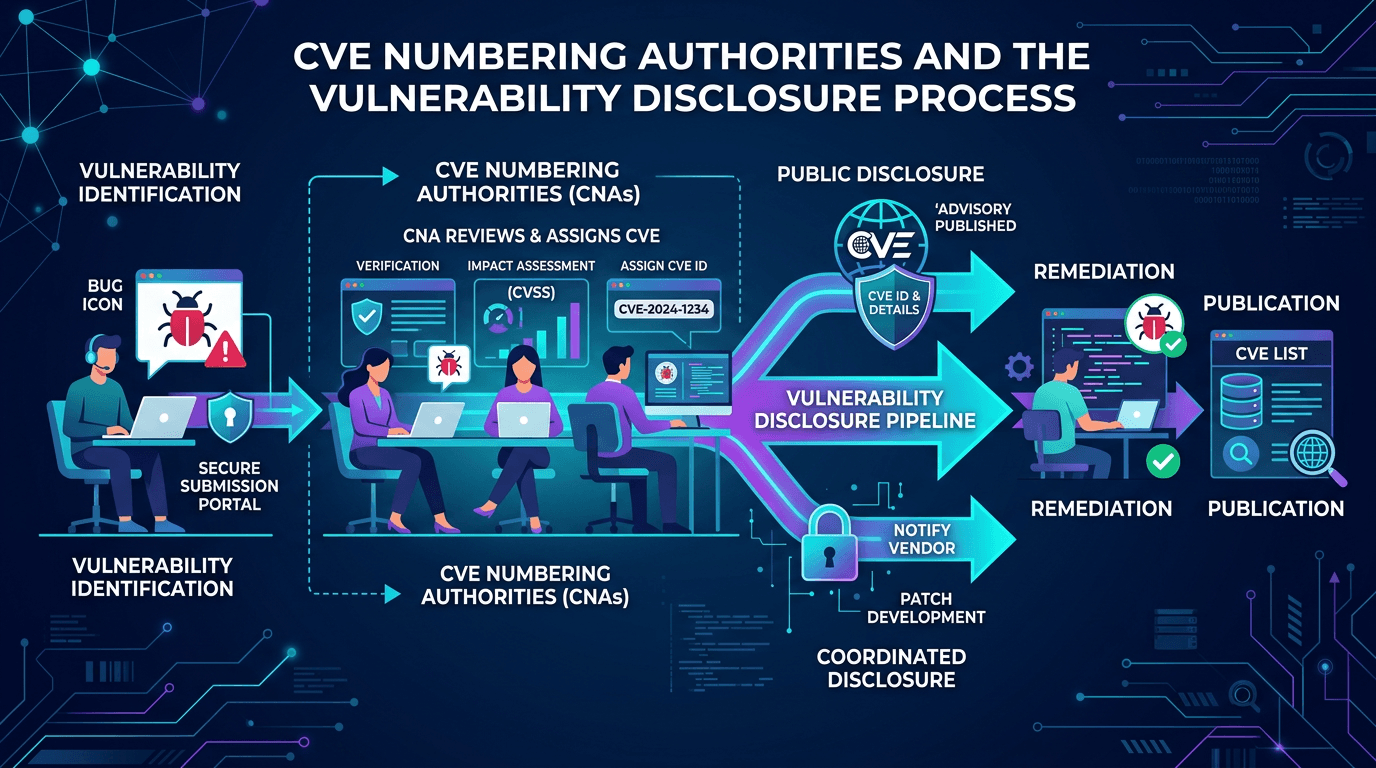
Every published CVE represents a chain of human decisions—by researchers, vendors, coordinators, and the CVE Numbering Authorities (CNAs) who assign identifiers. Yet for most practitioners the CVE record appears as a simple fact, the way a street address appears on a map: permanent, uncontested, immediately available. Understanding how CVEs are actually produced changes how security teams evaluate vulnerability information, participate in disclosure, and communicate with vendors and researchers. This guide walks through the full vulnerability disclosure pipeline—from discovery to publication—with a focus on what defenders, researchers, and product security teams need to know in 2026.
The CVE Program in Plain Terms
The CVE Program, governed by the CVE Board and administered by MITRE, publishes a dictionary of publicly known security vulnerabilities. Each entry has a unique identifier of the form CVE-YYYY-NNNNN, where YYYY is the year the ID was reserved and NNNNN is a sequence. The ID itself is deliberately simple; the value comes from the identifier being universally understood.
Scope is important. A CVE is not the sum of all security knowledge about a flaw. It is a coordination artifact—the shared reference that vendors, researchers, tools, and threat intelligence feeds use when discussing the same issue. Rich detail (severity, exploit availability, remediation guidance) lives in downstream systems such as the National Vulnerability Database (NVD), vendor advisories, and threat intelligence platforms, all of which reference the CVE ID.
What Is a CVE Numbering Authority?
A CVE Numbering Authority (CNA) is an organization authorized to assign CVE IDs within a defined scope. Examples include:
- Vendor CNAs such as Microsoft, Cisco, Red Hat, and Oracle, which assign CVEs for their own products.
- Open source CNAs that cover broad ecosystems (like Python Software Foundation or OpenSSL).
- Coordinator CNAs such as CERT/CC and the national CERT teams that handle cross-vendor or multi-party issues.
- Bug bounty CNAs that assign CVEs for vulnerabilities reported through their platforms.
- Root CNAs and Top-Level Root CNAs that oversee subtrees of the hierarchy.
Each CNA has a published scope statement describing what it will and will not assign IDs for. When a vulnerability falls outside any CNA’s scope, researchers can request an ID directly from MITRE via the CVE Request form.
CNA operations matter to defenders because CNA quality directly affects CVE record quality. A disciplined vendor CNA publishes precise descriptions, version ranges, affected components, and references. A less disciplined CNA may leave the record thin—forcing downstream consumers to rely on vendor advisories or threat intelligence for context.
The Vulnerability Disclosure Lifecycle
Modern coordinated vulnerability disclosure (CVD) follows a relatively consistent lifecycle, though details vary by vendor and legal jurisdiction.
1. Discovery
A vulnerability is discovered by an internal engineer, an external security researcher, an automated scanner, or—unfortunately—an attacker. Discovery may result from deliberate testing, accidental observation, or analysis of telemetry data indicating exploitation.
Discoverers vary widely: independent researchers, bug bounty hunters, academic teams, government labs, vendors’ own red teams, and managed security firms. Each brings different norms, reporting practices, and incentives.
2. Private Reporting
Responsible disclosure norms direct discoverers to report privately to the vendor before publication. Reporting channels include vendor security email addresses (security@...), PSIRT contact forms, bug bounty platforms, and CERT coordinators. Clear vendor reporting policies reduce friction; ambiguous or hostile policies discourage responsible disclosure and push researchers toward public disclosure instead.
The vulnerability disclosure policy (VDP) concept has matured considerably. Well-designed VDPs commit to timelines, provide safe-harbor language, and specify how credit will be given. Organizations without a VDP in 2026 should publish one—it is a trust signal that shapes how the security community engages with them.
3. Triage and Reproduction
Receiving vendors triage the report, attempt reproduction, and assess impact. Triage quality is a meaningful differentiator: organizations with mature PSIRT functions respond within days, communicate status, and engage constructively with researchers. Organizations without that maturity may delay, dismiss valid reports, or escalate unnecessarily.
4. CVE ID Assignment
Once the vulnerability is confirmed, a CVE ID is reserved—often before public details are disclosed. The CNA handling assignment typically has the strongest claim: the vendor for its own products, or a coordinating CNA for cross-vendor issues.
The ID is initially reserved, meaning the ID exists but no public details are published. This lets coordinators reference the issue internally while keeping the embargo. When publication occurs, the CNA populates the record with final details.
5. Patch Development and Coordination
The vendor develops and tests a fix. For complex ecosystems, coordination across downstream consumers (Linux distributions, cloud providers, device manufacturers) can stretch timelines significantly. Some disclosures involve multiple vendors sharing embargoed details for simultaneous patch release.
6. Advisory Drafting
The vendor drafts an advisory covering: affected products and versions, severity, mitigations, workarounds, patches, credits to the reporter, and references. Good advisories are precise about version ranges and include detection guidance; poor advisories leave defenders guessing.
7. Coordinated Publication
On publication day—typically timed to patch availability—the CNA publishes the CVE record, the vendor publishes the advisory, and in many cases the reporter publishes a technical writeup. Coordination minimizes the window between disclosure and patch availability.
8. Post-Publication
After publication, the record continues to evolve:
- NVD enriches with CVSS scores and CPE mappings.
- EPSS calculates exploit probability.
- KEV adds entries when active exploitation is confirmed.
- Researchers publish deeper analyses, proof-of-concept code, and detection signatures.
- Defenders integrate the CVE into their scanning, prioritization, and detection workflows.
Why CVE Quality Varies
Despite the program’s efforts, CVE record quality varies. Common reasons:
- Rushed assignments: During active exploitation, speed may take priority over completeness. Records get enriched later.
- Vendor opacity: Some vendors minimize disclosure detail for marketing reasons. The security community often pushes back, but the public record suffers.
- Scope ambiguity: Multi-vendor issues sometimes land in multiple CVEs, or one CVE gets fragmented across downstream products.
- Missing version ranges: Without clear affected-version data, defenders cannot accurately inventory exposure.
- Insufficient references: Missing research links make independent verification difficult.
The best defensive response is to not rely solely on CVE records. Combine them with vendor advisories, threat intelligence, and your own reproduction when stakes are high.
The Role of Coordinator CNAs
Coordinator CNAs—including CERT/CC, national CERT teams, and industry-specific coordinators—play a critical role in handling disclosures that span multiple vendors or lack a natural home. They:
- Route reports to affected vendors.
- Mediate timeline negotiations.
- Publish combined advisories when issues affect many products.
- Provide safe-harbor and trusted-intermediary services to researchers.
For security teams, coordinator advisories are often the most comprehensive source for cross-vendor issues, synthesizing vendor statements and providing unified remediation guidance.
Public Disclosure Without Coordination
Not every disclosure is coordinated. Reasons include:
- Unresponsive vendors: Researchers who cannot reach a vendor may publish after a reasonable waiting period.
- Active exploitation: If a vulnerability is already being used against victims, immediate publication may protect more people than delay.
- Legal pressure: Researchers sometimes face threats that complicate engagement, leading them to publish defensively.
The impact on defenders is that zero-day or partially-disclosed vulnerabilities sometimes appear without a CVE ID or with incomplete records. Threat intelligence fills this gap, pairing technical indicators with infrastructure reputation from providers like isMalicious to help defenders identify and block active exploitation even before the CVE is fully published.
CVE and SEO: Why Disclosure Pipeline Matters for Content
Security content that explains the CVE disclosure pipeline attracts durable organic search traffic because practitioners, researchers, and procurement teams repeatedly investigate these terms. Useful content categories include:
- Primers on CVE, CNA, and coordinated disclosure for engineering audiences.
- Guides to reporting vulnerabilities responsibly to vendors.
- Explanations of how specific vendor advisories relate to CVE records.
- Comparisons between CVE, CVSS, EPSS, and KEV.
Producing this content as part of your security marketing strategy aligns with what security buyers and practitioners search for during vendor evaluation. It also supports your own team’s consistent vocabulary.
Practical Guidance for Security Teams
If You Are a Defender
- Ingest CVE data directly from MITRE/NVD, enrich with CVSS, EPSS, and KEV.
- Subscribe to vendor advisories in parallel to the CVE feed—vendor-published context often exceeds CVE record content.
- Maintain a software inventory mapped to CPE (Common Platform Enumeration) identifiers so CVE matches translate cleanly to your assets.
- Combine public CVE data with internal telemetry and infrastructure reputation: a CVE plus observations of scanning from known-bad IPs signals active targeting.
If You Are a Vendor
- Publish a clear vulnerability disclosure policy and keep your security contact channels responsive.
- Become a CNA if your product base justifies it; it gives you control over record quality.
- Train PSIRT staff on coordinated disclosure practices and communication.
- Invest in advisory quality—precise versions, clear remediation, transparent credit.
If You Are a Researcher
- Engage vendors through documented channels and respect reasonable embargo periods.
- Keep detailed records of all communications.
- Understand CNA scope—knowing which organization to approach saves time.
- Consider using a coordinator CNA when vendor engagement stalls.
If You Are Executive Leadership
- Fund the PSIRT and disclosure capability explicitly; it is not a side duty.
- Track disclosure metrics (time to triage, time to patch, researcher satisfaction) as security KPIs.
- Position a strong VDP as a trust asset for customers and regulators.
Integrating CVE Disclosure Data With Threat Intelligence
CVE data is one input among many in a mature security program. Integration with threat intelligence amplifies its value:
- Correlate CVEs with actor targeting patterns (“this group actively exploits edge-device CVEs in our sector”).
- Correlate CVEs with KEV and EPSS for prioritization.
- Monitor infrastructure reputation—scanning and exploitation traffic often originates from clusters of IPs and domains with malicious histories. Services like isMalicious expose this reputation data to defenders in real time.
- Feed CVE disclosure timing into detection engineering: rules shipped on disclosure day catch opportunistic exploitation before patches are universally deployed.
Common Pitfalls in CVE-Centric Programs
Repeating issues across organizations:
- Relying on CVE IDs as the only source of truth: Vendor advisories often contain critical context the CVE record lacks.
- Inventorying by CVE count, not by exposure: Counting open CVEs is weak; understanding which CVEs affect your actual deployments matters.
- Ignoring disclosure process nuance: Treating all CVEs as equally reliable misses that some are rushed, partial, or disputed.
- Skipping coordinator advisories: Cross-vendor issues often live most clearly in CERT/CC or ENISA advisories, not in any single CVE.
Conclusion
The CVE disclosure pipeline—from discovery through CNA assignment through coordinated publication—shapes the vulnerability data every defender relies on. Understanding the roles of CNAs, the lifecycle of coordinated disclosure, and the downstream enrichment ecosystem (NVD, CVSS, EPSS, KEV) gives security teams sharper tools for reading vulnerability records accurately and prioritizing responses.
Invest in integration: pull CVE data, vendor advisories, EPSS probabilities, KEV entries, and live threat intelligence into a unified view of exposure. Pair that with infrastructure reputation from providers like isMalicious to see not just what is vulnerable, but what adversarial infrastructure is probing your environment. The organizations that engage with the disclosure process deliberately—as researchers, as vendors, or as defenders—consistently reduce real risk and strengthen the security ecosystem for everyone.
Frequently asked questions
- What is a CVE Numbering Authority (CNA)?
- A CVE Numbering Authority is an organization authorized to assign CVE IDs to vulnerabilities within a defined scope—typically the organization's own products, or products of its customers. CNAs are coordinated by MITRE and operate under the CVE Program's policies and governance.
- Why do some vulnerabilities have CVEs and others do not?
- CVE assignment requires that a vulnerability meets the CVE Program criteria: it must be independently fixable, have a public reference, and affect specific identifiable products. Some issues are configuration problems, design choices, or operational concerns that do not meet the criteria and therefore do not receive a CVE.
- How can security researchers request a CVE for a vulnerability they discovered?
- Researchers can request a CVE through the relevant vendor's CNA if the product is covered, or through MITRE's CVE Request form for vulnerabilities not covered by any other CNA. Responsible disclosure typically follows: researchers coordinate with vendors before requesting publication.
Related articles
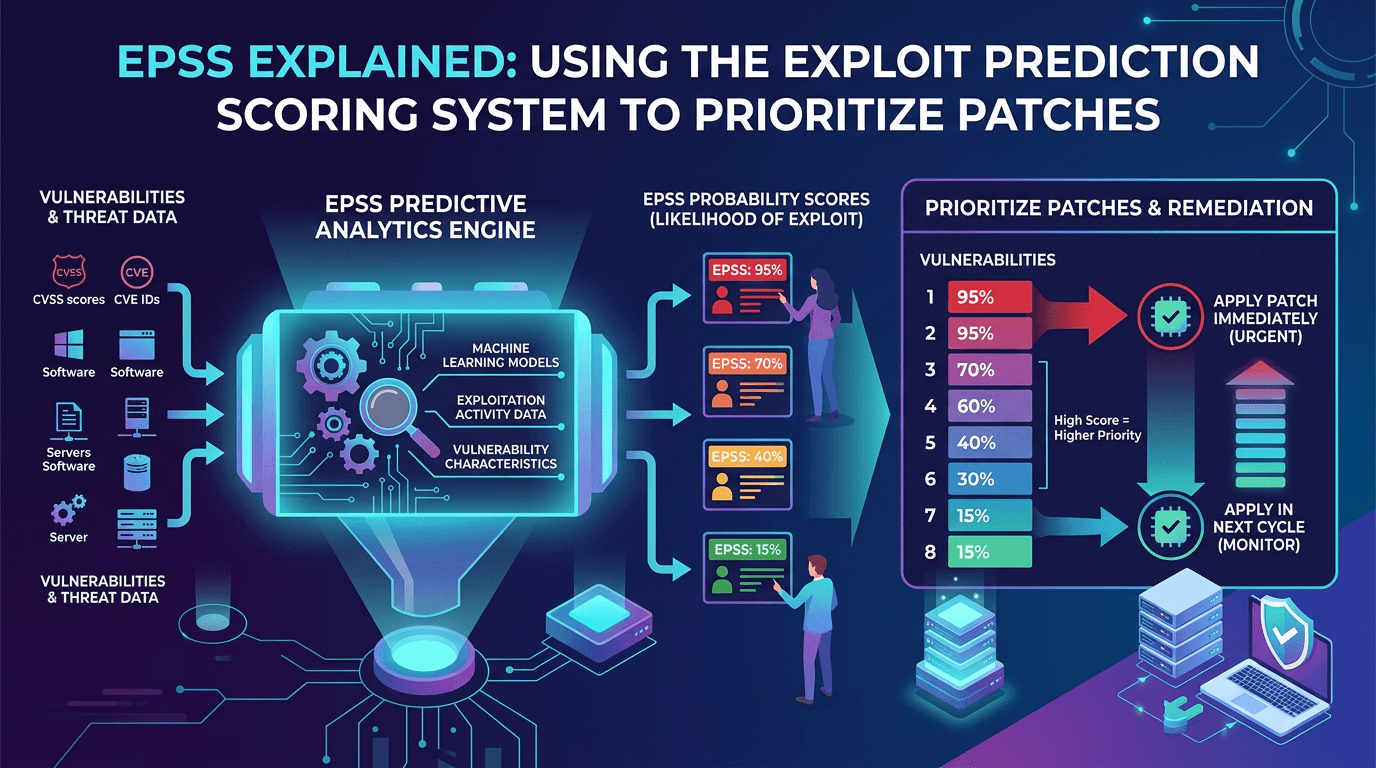 Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026
Apr 21, 2026EPSS Explained: Using the Exploit Prediction Scoring System to Prioritize Patches in 2026A practical guide to the Exploit Prediction Scoring System (EPSS)—how it works, how it complements CVSS and KEV, and how security teams can use EPSS probabilities to prioritize vulnerability management at scale.
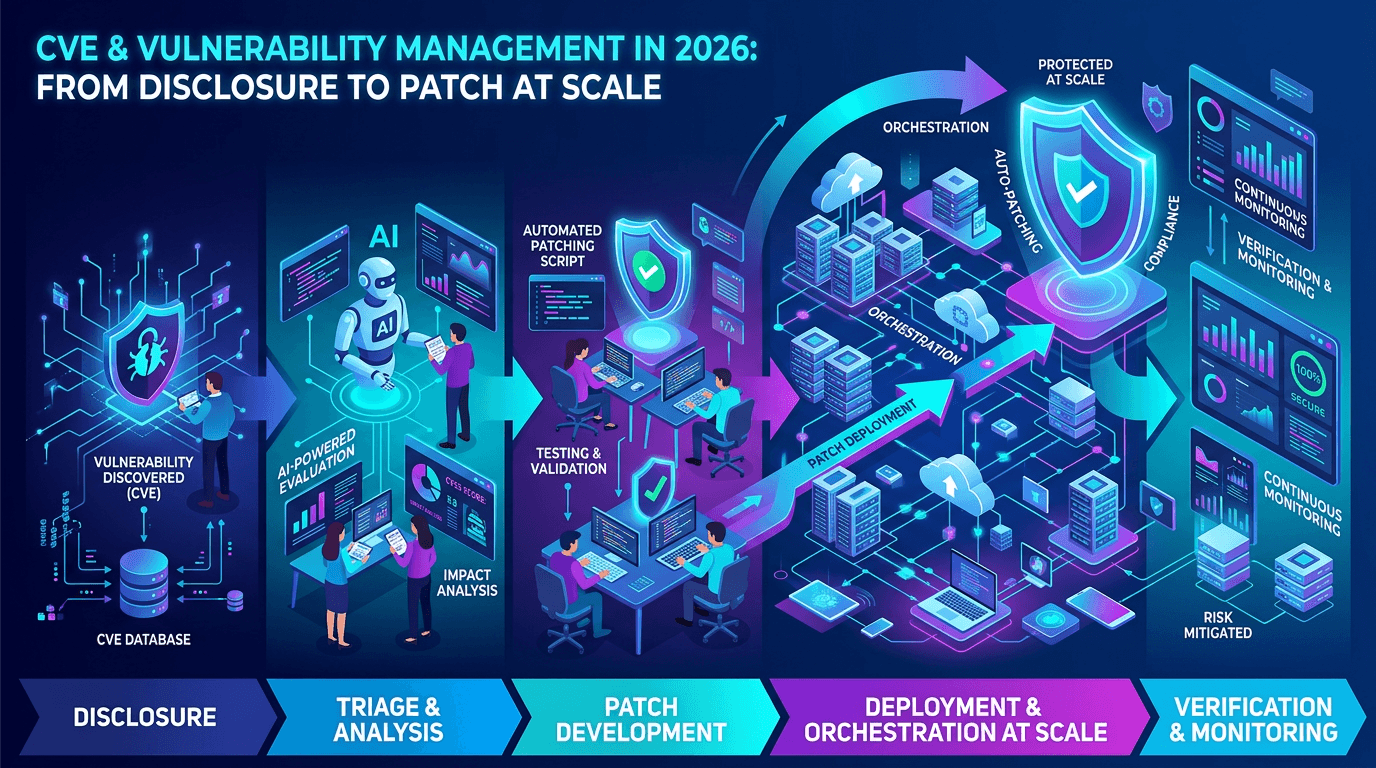 Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at ScaleA practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
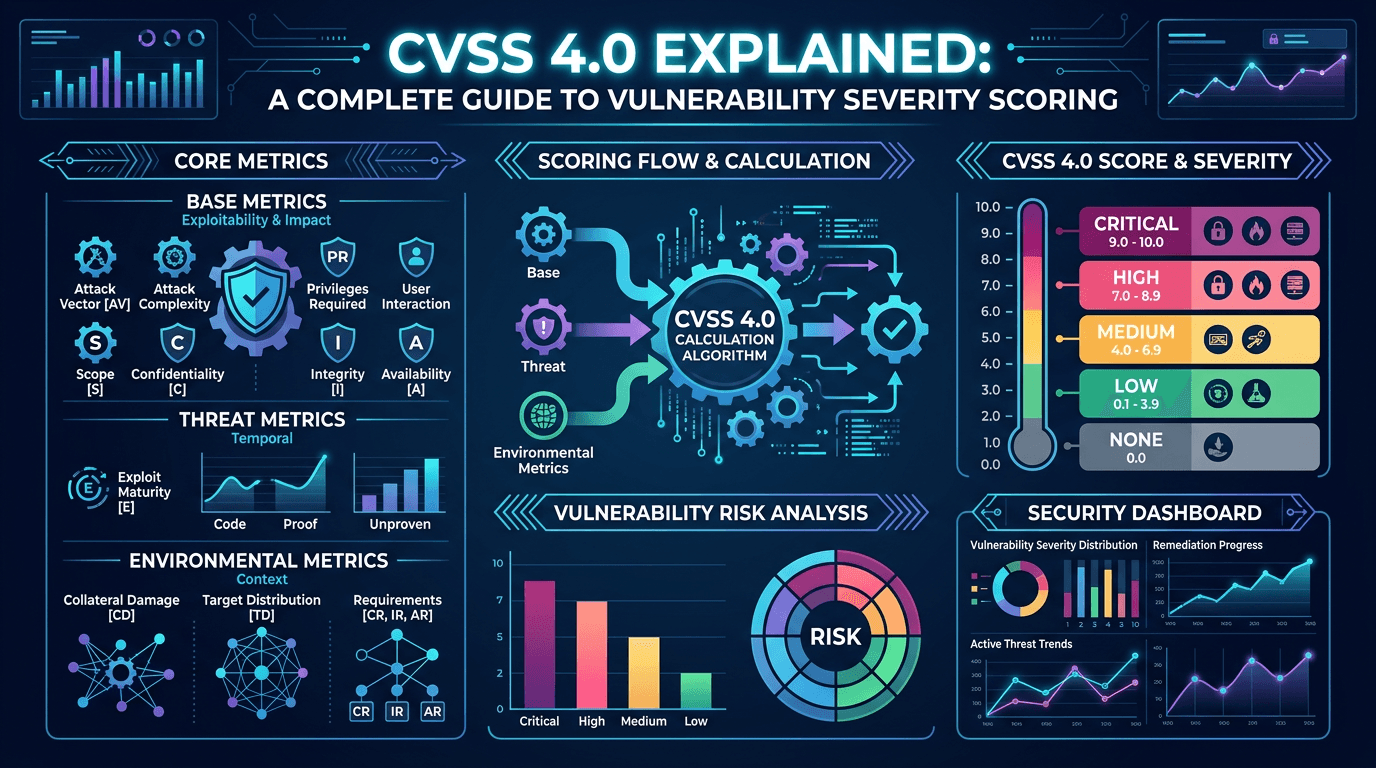 Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026
Apr 17, 2026CVSS 4.0 Explained: A Complete Guide to Vulnerability Severity Scoring in 2026Master the Common Vulnerability Scoring System v4.0 with a practical breakdown of base, threat, environmental, and supplemental metrics—and learn how to translate CVSS into real-world risk decisions.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker