Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability Disclosure
Build a modern supply-chain security program: generate SBOMs, map CVEs to components, integrate EPSS and KEV, and coordinate fixes across vendors and open-source maintainers.
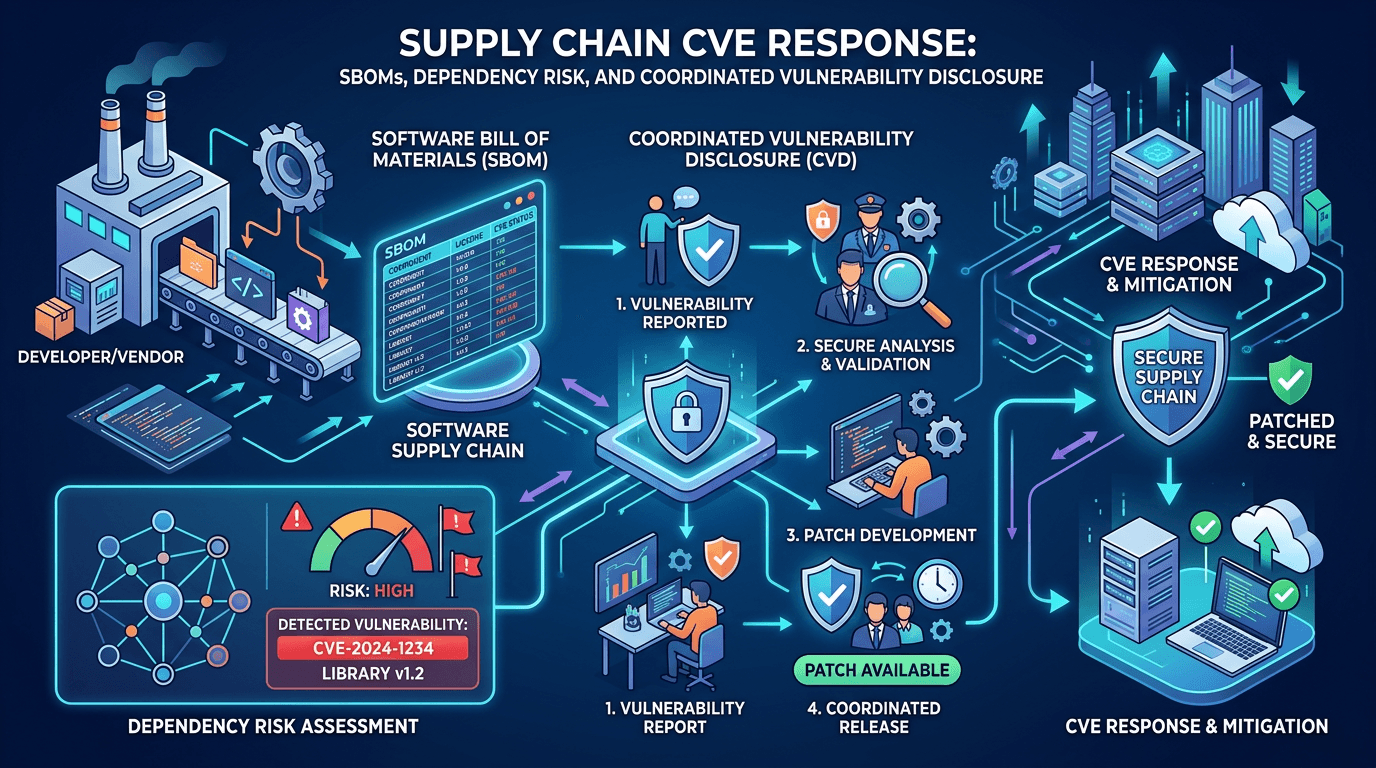
Software today is assembled more than authored. Dependencies nest inside dependencies; a single CVE in a popular open-source library can ripple across ecosystems overnight. Supply chain security programs therefore hinge on visibility (SBOM generation), informed prioritization (CVSS, EPSS, KEV), and coordinated response across engineering, procurement, and legal teams. This article outlines how organizations operationalize vulnerability management for third-party and first-party code—while connecting threat intelligence on exploitation and threat actor interest to separate hype from genuine enterprise risk.
Why Supply Chain Attacks Dominate Headlines
Attackers compromise build pipelines, poison packages in public registries, or steal signing keys—multiplying blast radius beyond any single endpoint. Defenders cannot rely solely on perimeter firewalls; they must know what software they run and where it came from.
Regulatory momentum—executive orders, sector guidance—pushes SBOM adoption, especially in critical infrastructure and federal contracting contexts. Even without mandates, enterprises adopt SBOM practices to reduce audit friction and accelerate CVE response.
SBOM Formats: SPDX, CycloneDX, and Operational Reality
Common formats include SPDX and CycloneDX. The “best” format is the one your toolchain consistently produces and consumes. SBOMs should include component names, versions, hashes (often SHA-256 of packages), licenses, and supplier metadata when available.
Generating SBOMs at build time—embedded in CI/CD—beats manual spreadsheets that rot immediately. Store SBOM artifacts alongside release versions so incident responders can answer “were we affected?” within minutes of a CVE announcement.
For SEO, practitioners search “SBOM CVE workflow” when standing up programs; include implementation steps and tooling categories to match intent.
From SBOM to Impact Analysis When CVEs Drop
When a CVE publishes, teams should:
- Query SBOM repositories for affected components and versions.
- Determine reachability—static imports versus dynamically loaded code paths.
- Assess exposure—internet-facing services, privileged contexts, data sensitivity.
- Apply prioritization frameworks combining CVSS, EPSS, and KEV signals.
- Coordinate upgrades, patches, or compensating controls with owners.
Reachability analysis prevents wasted sprint capacity upgrading dormant dependencies—a common frustration for developers skeptical of security noise.
Vendor Coordination and VEX
Vulnerability Exploitability eXchange (VEX) documents let vendors assert whether products are affected, not affected, or affected under specific configurations—reducing panic upgrades when upstream libraries appear in SBOMs but are not exploitable in context. Pursue VEX from critical vendors; treat absence of VEX as uncertainty requiring deeper analysis.
Open-Source Maintainers and Disclosure Etiquette
Coordinated disclosure timelines respect maintainer capacity. Security teams should participate constructively—clear reports, reproducible tests, and patience—because adversaries rarely wait politely. When exploitation begins before patches land, threat intelligence may surface scanning IPs or exploit file hashes; temporary network blocks and WAF rules can buy hours.
Integrating Binary Analysis and Hash Correlation
For compiled dependencies, file hash comparisons help verify whether shipped artifacts match expected vendor releases—detecting tampering. Pair hash verification with signature checks where publishers sign packages.
Procurement and Contractual Levers
Contracts can require SBOM delivery, CVE notification SLAs, and cooperation during incidents. Legal language should avoid vague “best effort” security without measurable artifacts.
Cloud-Native Supply Chains: Containers and IaC
Container images bundle OS packages and language dependencies—scan both layers. Infrastructure-as-code modules can pull unpinned versions; enforce pinning and review modules like any dependency. Misconfigured Terraform modules have become attack vectors in their own right.
Measuring Program Maturity
Useful metrics:
- SBOM coverage percentage across product lines.
- Mean time to answer SBOM impact queries after CVE publication.
- Percentage of builds producing signed, stored SBOM artifacts.
- Open high-risk supply chain issues aged beyond policy thresholds.
Threat Intelligence: Following Actor Campaigns Against Developers
Threat actors target developers with phishing npm tokens, malicious VS Code extensions, and repository impersonation. Tactical intelligence feeds should inform secure development training and tool allowlists.
Network indicators—malicious domains hosting fake packages—belong in DNS filtering and proxy deny lists; IP reputation enrichment accelerates triage when CI systems make unexpected outbound calls.
Regulatory and Customer Expectations
Customers increasingly request SBOM evidence in RFPs. Maintain customer-facing documentation that explains your supply chain security posture without leaking sensitive architecture—SEO-friendly trust pages help presales teams respond faster.
Common Pitfalls
- Treating SBOM as a checkbox without integration into change management.
- Ignoring dev environments—attackers compromise laptops and CI secrets first.
- Over-automating upgrades without test coverage—availability incidents become supply chain “fixes.”
Tabletop: Upstream Compromise Scenario
Simulate a widely used library compromise. Test communications with product owners, customer notifications, and rollback plans. Measure how long it takes to map impact via SBOM queries—if hours, invest in indexing and search tools.
Conclusion
Supply chain risk is CVE risk at scale. SBOM visibility, disciplined prioritization using EPSS/KEV, and humane coordination with maintainers and vendors turn chaotic disclosures into executable plans. Pair technical measures with threat intelligence that highlights real exploitation—so engineering time chases adversaries, not headlines alone.
Long-form guides that connect SBOM, CVE, and operational workflows capture organic traffic from teams building AppSec programs in 2026 and beyond.
Deep Dive: Monorepos and Shared Libraries
Large engineering orgs centralize code in monorepos; SBOM tools must aggregate subgraphs without double-counting components. Choose scanners that understand workspace boundaries and produce mergeable manifests for enterprise dashboards.
Bridging AppSec and SOC
When a CVE indicates active exploitation, SOC should receive succinct detection guidance—expected file paths, process ancestry, and network indicators—not only library names. Cross-team playbooks prevent “patch ticket open” while intrusions continue.
Economic Incentives for Secure Defaults
Upstream projects adopting memory-safe defaults, signed releases, and reproducible builds reduce downstream incident frequency—support those initiatives via sponsorships and prioritized PR reviews when feasible.
Future Outlook: AI-Generated Code Dependencies
Generative coding assistants may introduce dependencies analysts did not manually vet. Update secure SDLC checkpoints to include AI-assisted change review and automated SBOM diffing on every merge.
Knowledge Management
Maintain an internal glossary linking SBOM, VEX, CVE, CPE, and purl identifiers—onboarding accelerates when terms are consistent across security and engineering.
Partnership with Risk and Audit
Map supply chain controls to control frameworks (NIST SSDF, ISO, SOC 2) to streamline audits—duplicate evidence collection wastes cycles.
Why Search Engines Reward Comprehensive Supply Chain Content
“How to respond to log4j-style events” spikes during incidents; evergreen articles that teach durable processes—not only one CVE name—accumulate authority over years. Update publish dates when methodologies change to signal freshness.
Operationalizing SBOM Storage and Search
Treat SBOM artifacts like security-sensitive configuration: version them, encrypt at rest if policy requires, and index metadata in a query service (often backed by object storage plus a graph or document index). Engineers should query by component name, version range, and product line in seconds—if search is slow, incident response drags.
Role-based access matters: developers see their services; platform security sees global aggregates; auditors receive export bundles—not live database creds.
Patch Orchestration Across Thousands of Microservices
Microservices complicate upgrades: coordinated dependency bumps may require feature flags and progressive rollouts. Establish “security upgrade trains”—scheduled windows where high-priority CVE fixes ship with executive air cover—so product managers cannot indefinitely defer critical patches for roadmap convenience.
Handling Transitive Dependencies
Transitive packages hide beneath direct dependencies. Scanners that visualize trees help teams decide whether upgrading a top-level package resolves nested issues or if overrides/patches are necessary. Document exceptions when upstream maintainers are unresponsive—forking carries governance overhead.
Coordinated Disclosure with Customers
If your product embeds a vulnerable library, customer communications must balance transparency with exploitability nuance. Pre-draft templates for “we are investigating,” “we are not affected,” and “we are affected—patch timeline” scenarios—legal review in calm times prevents scrambled messaging during crises.
Integrating EPSS and KEV into CI Gates
Some teams experiment with gating builds when dependencies exceed EPSS thresholds or appear on KEV—carefully tuned to avoid blocking all development during global internet-wide panics. Prefer advisory modes first, then enforce after tuning false positives.
Threat Actor Interest Versus Media Hype
Not every CVE with a clever logo requires midnight upgrades. Threat intelligence distinguishing opportunistic scanning from targeted threat actor campaigns helps leaders allocate weekend work fairly. Services exposing IP and domain telemetry—such as isMalicious—assist SOC teams watching for exploit infrastructure spinning up post-disclosure.
SBOM in Incident Response Retainers
Contracted IR firms increasingly request SBOM access to accelerate scoping. Include SBOM handoff procedures in retainer documents and annual drills.
Developer Experience: Make the Secure Path the Easy Path
Automated PRs that bump vulnerable dependencies—with tests passing—convert security work from nagging into merge buttons. Invest in test coverage precisely because it unlocks automation confidence.
Measuring Third-Party Risk at Portfolio Level
For private equity and holding companies, aggregate SBOM risk across portfolio firms to prioritize centralized tooling purchases and shared threat intelligence subscriptions—economies of scale matter.
Academic and Standards Participation
Participate in standards bodies and open-source security working groups if capacity allows—early visibility into emerging formats and best practices beats catching up after adoption waves.
Reducing Duplicative Scanning Costs
Multiple teams running overlapping container scans wastes money. Centralize scanning infrastructure while pushing results into developer workflows via PR comments—visibility where code changes happen.
FAQ-Style Summaries for Executives
Maintain a one-page FAQ: what SBOM is, why CVE volume is high, how you prioritize, and what customers should expect during incidents. Executives forward such FAQs to boards; clarity reduces panic questions.
Continuous Monitoring Versus Point-in-Time Scans
Point-in-time scans miss drift in running clusters. Runtime SBOM or continuous image verification approaches close gaps—especially for Kubernetes environments where pods churn frequently.
When Law Enforcement Gets Involved
Supply chain tampering may trigger criminal investigations. Preserve logs, file hashes, and CI pipeline artifacts carefully—chain of custody influences outcomes.
Closing the Loop with Threat Hunting
Hunters search for anomalous package installs or unexpected compiler invocations aligned with CVE exploitation patterns—even before scanners prove missing patches. Combine hunts with network IOC pivots.
Community Responsibility
Report vulnerabilities responsibly; fund critical maintainers; avoid entitlement toward unpaid labor—security is a shared ecosystem problem.
Frequently asked questions
- What is an SBOM?
- A Software Bill of Materials (SBOM) is a structured inventory of software components, libraries, and dependencies used in an application or system—similar to ingredient lists for food.
- Why are supply chain vulnerabilities different from traditional CVEs?
- A flaw in a widely used library can affect thousands of downstream products simultaneously. Coordinated disclosure and dependency updates must propagate through multiple vendors and open-source ecosystems.
- How should teams prioritize supply chain CVEs?
- Combine SBOM reachability analysis, CVSS severity, EPSS exploitation probability, KEV status, and vendor advisory confidence. Prioritize components that are actually loaded in production and internet-exposed services.
Related articles
 May 24, 2026Sources de données CVE : comment construire une vision fiable du risque vulnérabilité
May 24, 2026Sources de données CVE : comment construire une vision fiable du risque vulnérabilitéNVD, OpenCVE, CISA KEV, GCVE, EPSS, CERT-FR, MSRC, GHSA, Exploit-DB, Nuclei et advisories fournisseurs : comprendre le rôle de chaque source dans une plateforme CVE exploitable.
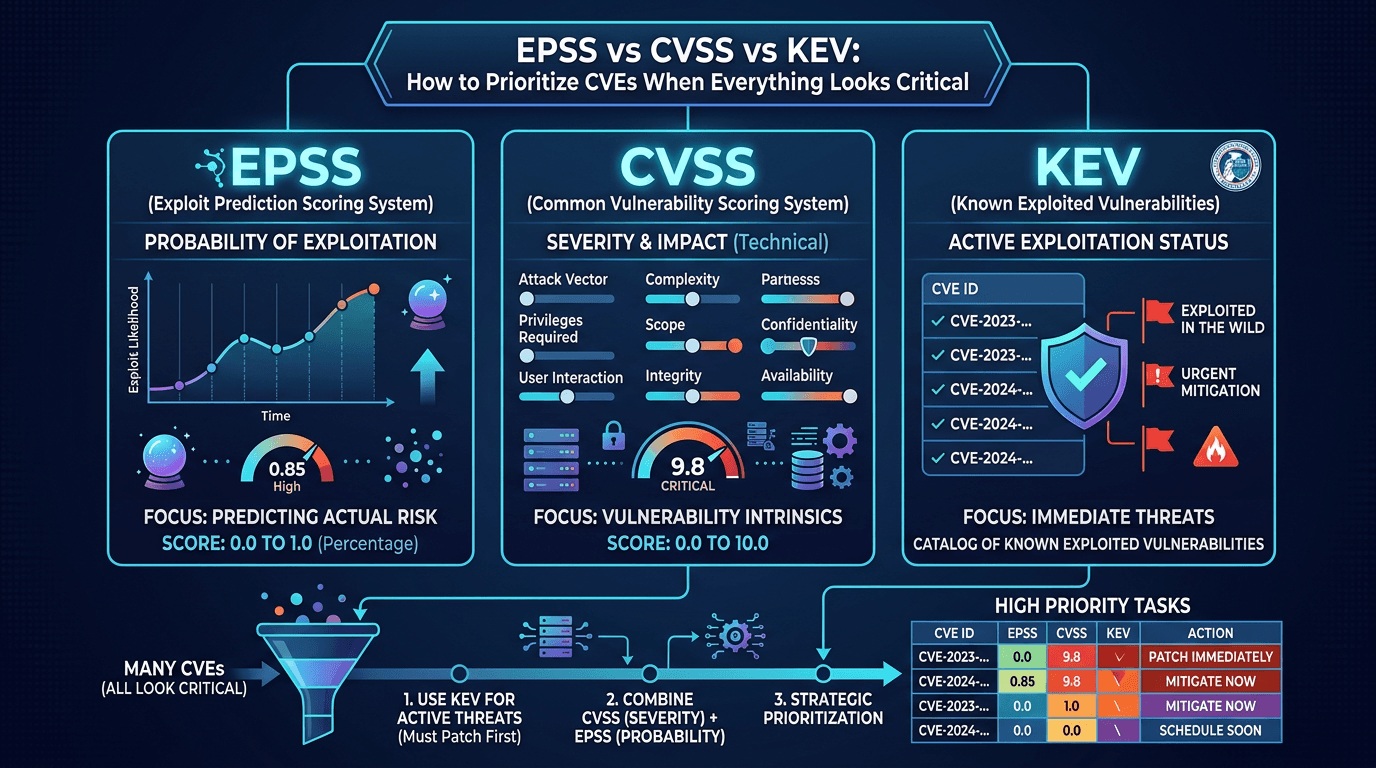 Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks Critical
Apr 21, 2026EPSS vs CVSS vs KEV: How to Prioritize CVEs When Everything Looks CriticalCut through scoring confusion: compare CVSS severity, EPSS exploit probability, and CISA KEV active exploitation—and learn a practical model for patch and compensating-control decisions.
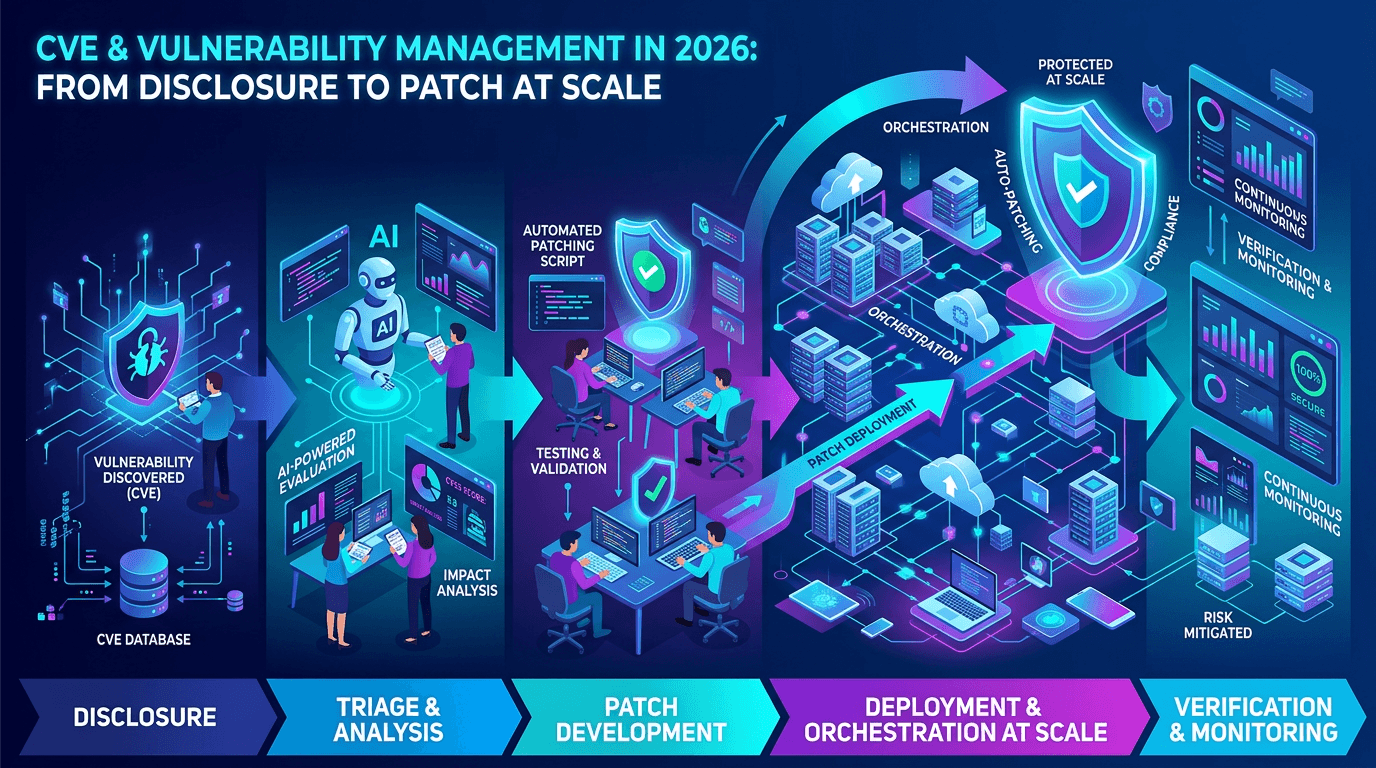 Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at Scale
Apr 17, 2026CVE & Vulnerability Management in 2026: From Disclosure to Patch at ScaleA practical guide to the CVE ecosystem, CVSS scoring, exploitability signals, and how security teams prioritize vulnerabilities without drowning in scanner noise.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker