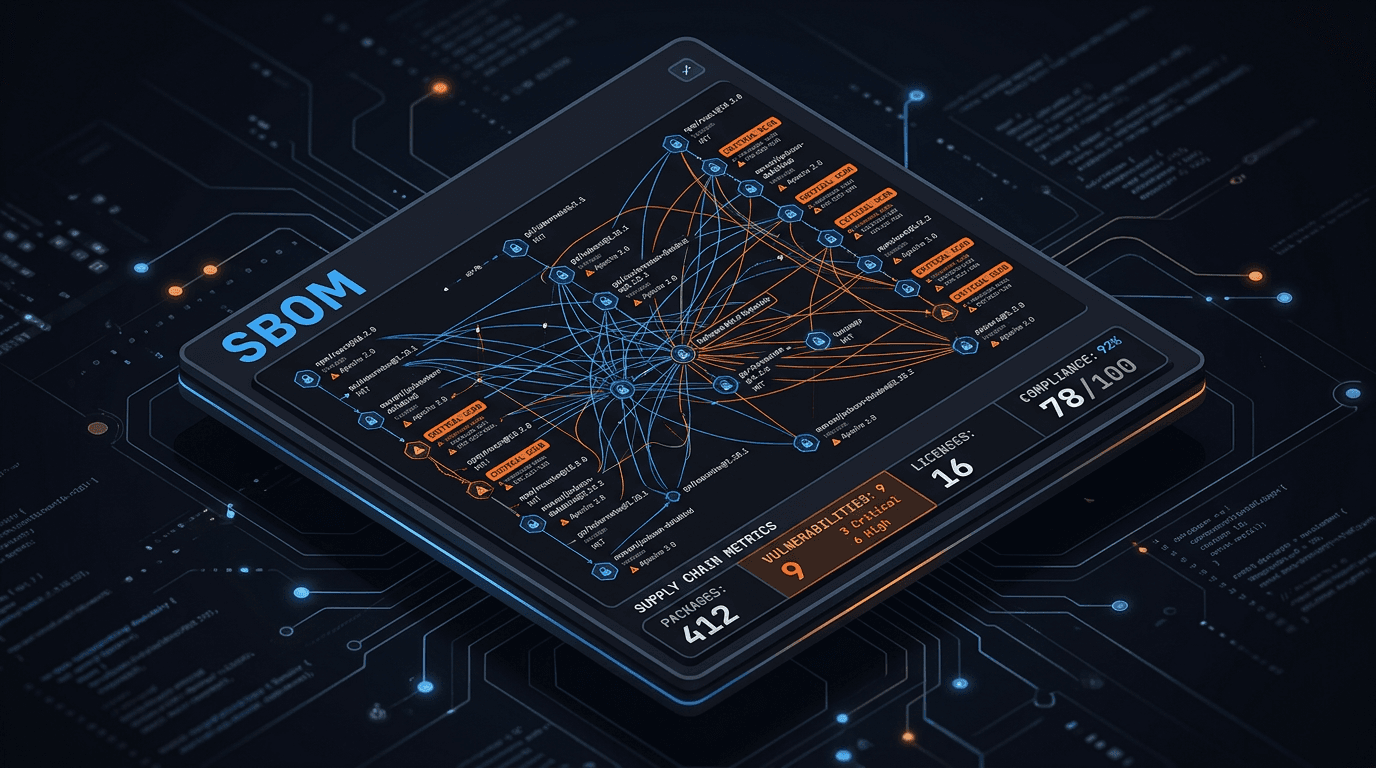
SBOM and Supply Chain Security: What Security Teams Actually Need
Software bills of materials are not paperwork for compliance alone. Learn how SBOMs reduce third-party risk and speed response when a dependency blows up.
Every modern application is a stack of open-source packages, containers, and vendor SDKs. When log4j-style issues or compromised packages hit the news, the winning question is simple: Where do we use this component? A Software Bill of Materials (SBOM) answers that question in minutes instead of weeks.
What an SBOM Is
An SBOM is a structured inventory of components—names, versions, licenses, and often hashes—that describes what shipped in a given build or image. Standards such as SPDX and CycloneDX make SBOMs machine-readable so scanners and CI pipelines can reason about them.
Why It Matters for Security
- Vulnerability response: Map a CVE or malicious package to affected services without guessing.
- License risk: Track obligations before they become legal surprises.
- Incident scope: When a build artifact is suspect, SBOM + provenance narrows blast radius.
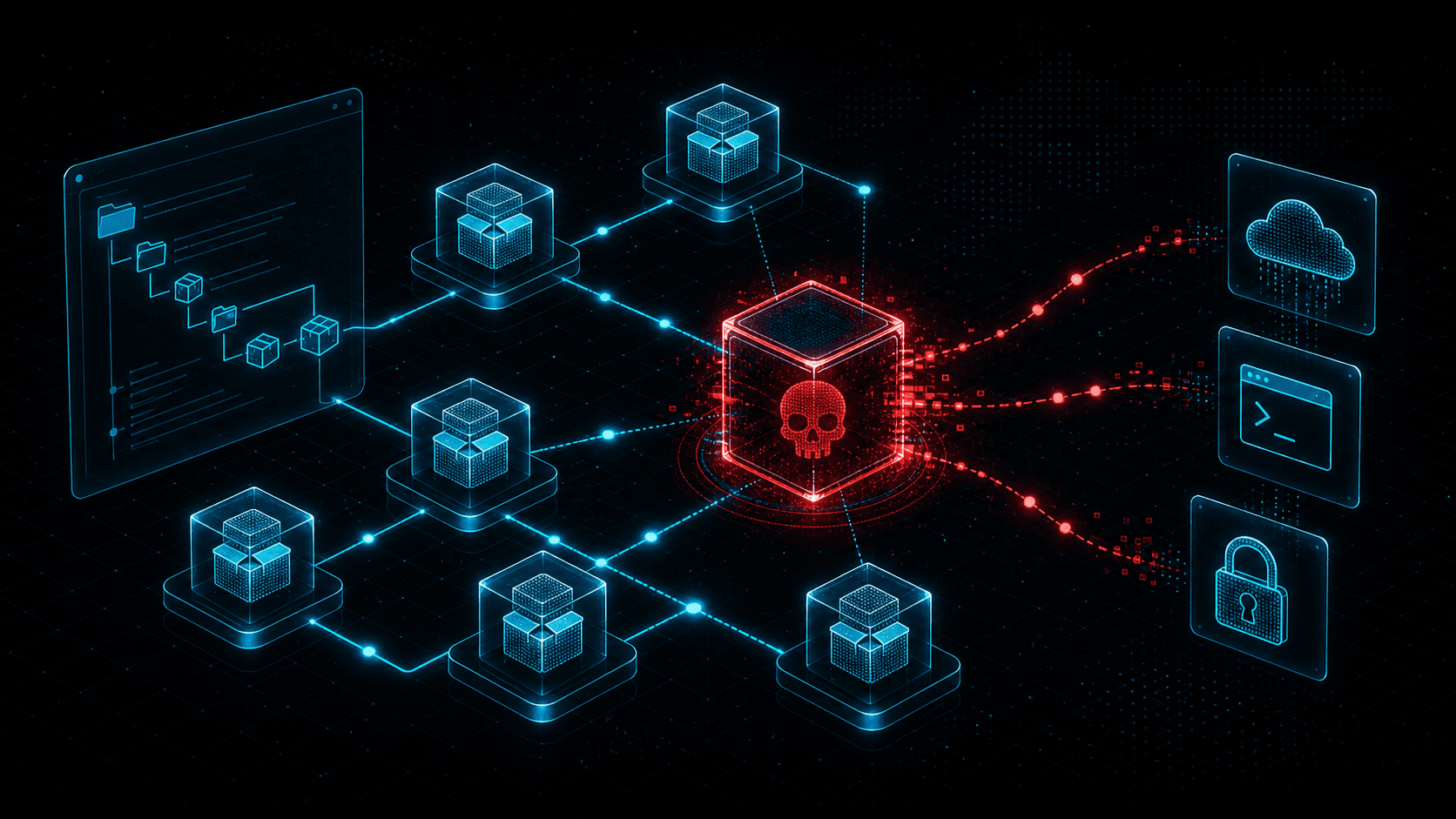
SBOM Alone Is Not Enough
SBOMs must be generated in CI, stored with artifacts, and kept current. Pair them with dependency pinning, signature verification, and provenance (who built what, from which commit) so you trust the inventory itself.
Operationalizing
Start with critical applications and internet-facing images. Integrate SBOM export into release pipelines, attach outputs to version control or artifact storage, and rehearse “dependency X is bad” drills twice a year.
Conclusion
Supply chain security is dependency visibility plus process. SBOMs are the visibility layer; your pipeline and governance turn them into actionable supply chain defense.
Related articles
 May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain Compromise
May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain CompromiseMalicious npm packages use typosquatting, dependency confusion, install scripts, and maintainer compromise to steal secrets and backdoor builds. Learn practical detection and response.
 Apr 25, 2026Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability Disclosure
Apr 25, 2026Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability DisclosureBuild a modern supply-chain security program: generate SBOMs, map CVEs to components, integrate EPSS and KEV, and coordinate fixes across vendors and open-source maintainers.
 Jan 3, 2026Supply Chain Attack Detection: Lessons from SolarWinds to MOVEit
Jan 3, 2026Supply Chain Attack Detection: Lessons from SolarWinds to MOVEitSupply chain attacks have become the weapon of choice for sophisticated threat actors. Learn how to detect compromised vendors, monitor third-party risk, and protect your organization before your suppliers become your vulnerability.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker