DNS Security: Poisoning, Hijacking, and Hardening That Actually Sticks
DNS is easy to ignore until it routes your users to malware. Learn how cache poisoning, hijacking, and secure DNS practices fit together.
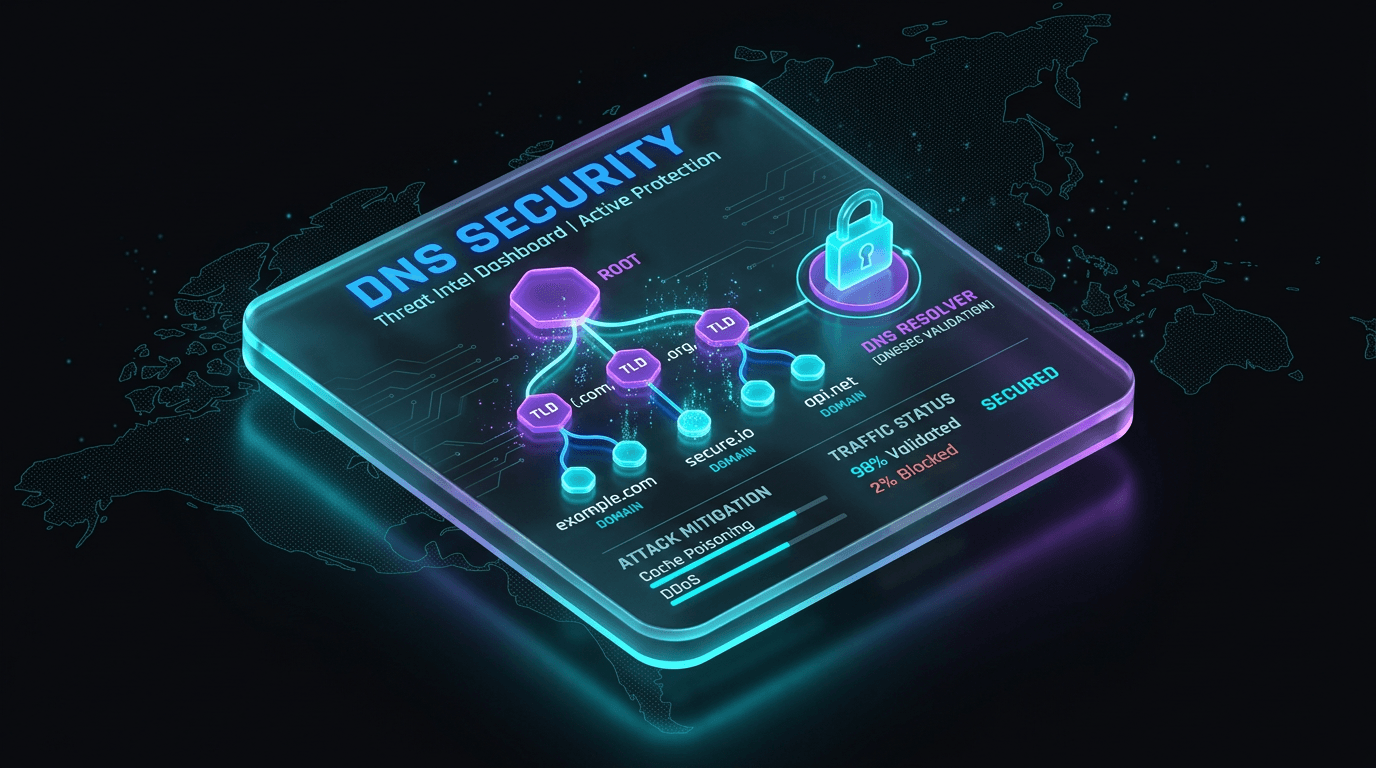
DNS translates names into addresses. Attackers abuse it to redirect users to phishing sites, bypass security controls, and exfiltrate data in plain sight. Defending DNS is less about exotic zero-days and more about architecture, monitoring, and closing obvious gaps.
Cache Poisoning and Resolver Trust
Resolvers that accept spoofed answers can serve wrong IP addresses to clients until caches expire. Use DNSSEC where your zones and providers support it, and prefer trusted recursive resolvers with strong anti-spoofing behavior for client and server workloads.
Domain and Registrar Hygiene
Domain hijacking via stolen registrar credentials or expired domains bypasses most network controls. Lock domains, use registry lock where available, enforce 2FA on registrar accounts, and monitor WHOIS and certificate transparency for unexpected changes.
Encrypted DNS: DNS over HTTPS / TLS
DoH and DoT protect query privacy on the wire and reduce some on-path manipulation, but they also shift policy to which resolver you trust. Corporate environments should explicitly choose resolvers and logging policies instead of defaulting to browser or OS choices.
Monitoring and Threat Intel
Log query patterns for rare resolutions, newly registered domains contacted by endpoints, and DNS tunneling indicators. Correlate DNS telemetry with EDR and firewall data for faster triage.
Conclusion
DNS security is defense in depth: secure zones, secure resolvers, secure accounts, and visibility into what your systems resolve every day.
Related articles
 May 9, 2026MCP Security Risks: Tool Poisoning, Prompt Injection, and the New AI Agent Attack Surface
May 9, 2026MCP Security Risks: Tool Poisoning, Prompt Injection, and the New AI Agent Attack SurfaceModel Context Protocol integrations give agents access to tools, files, and services. That power creates new risks: tool poisoning, prompt injection, overbroad permissions, and untrusted server abuse.
 May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud Teams
May 2, 2026Brand Impersonation and Lookalike Domains: A Practical Monitoring Playbook for Security, Legal, and Fraud TeamsTyposquats and homoglyphs are cheap to register and expensive to ignore. Learn how to discover, prioritize, and remove lookalike infrastructure before it harvests credentials or poisons your customers’ trust in search and email.
 Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROI
Apr 26, 2026IOC Enrichment APIs: A Security Operations Guide to Faster Triage, Fewer False Positives, and Measurable ROIAn indicator without context is a ticket without an owner. Learn how IOC enrichment APIs work, which fields SOC teams need at each tier, and how to wire them into case management without building a data swamp.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker