Watering Hole Attacks: Compromising the Sites Your Victims Already Trust
Instead of spear-phishing individuals, APTs infect websites their targets routinely visit. Learn how watering hole campaigns work and how to harden web supply chains and detection.
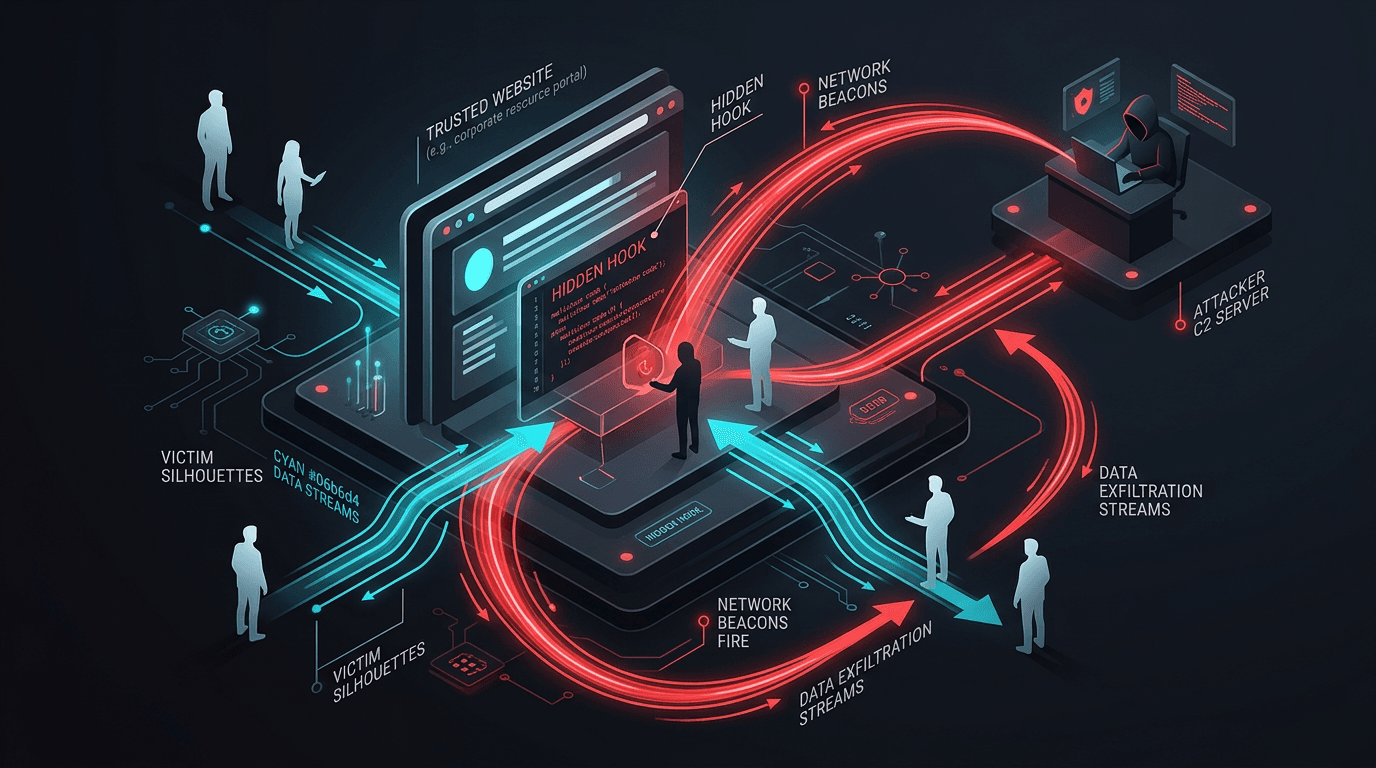
A watering hole attack compromises a third-party website known to be frequented by a specific industry, region, or organization—think industry news, vendor portals, or professional forums. When targets browse the site, their browsers execute malicious scripts, load exploits, or are tricked into downloading trojanized “updates.” The site is the lure; trust in the domain does the attacker’s work.
Why This Matters
Unlike broad drive-by campaigns, watering holes are selective: traffic is often filtered by geolocation, browser fingerprint, or cookie so only intended victims see the payload. Researchers and sandboxes may see a benign page.
Common Technical Patterns
- Compromised CMS or plugin on a legitimate site injecting a script tag.
- Malvertising or third-party widgets (chat, analytics) as the supply-chain entry.
- Fake updates or browser warnings served only to matching visitors.
Defenses for Website Operators
- Patch CMS, themes, and plugins aggressively; remove unused extensions.
- Subresource Integrity (SRI) for third-party scripts where possible.
- CSP and strict Content-Security-Policy to limit script sources.
- Monitor file integrity and outbound beacons from web origin.
Defenses for Enterprises
- Browser isolation or split tunneling for high-risk roles visiting untrusted vertical sites.
- EDR with exploit and script coverage; do not rely solely on network allowlists for “trusted” domains.
- Threat intelligence on compromised but legitimate domains your sector uses.
Conclusion
Watering holes weaponize routine browsing. Operators must treat public web properties as critical infrastructure; defenders must assume any site can be a transient infection point until proven otherwise.
Related articles
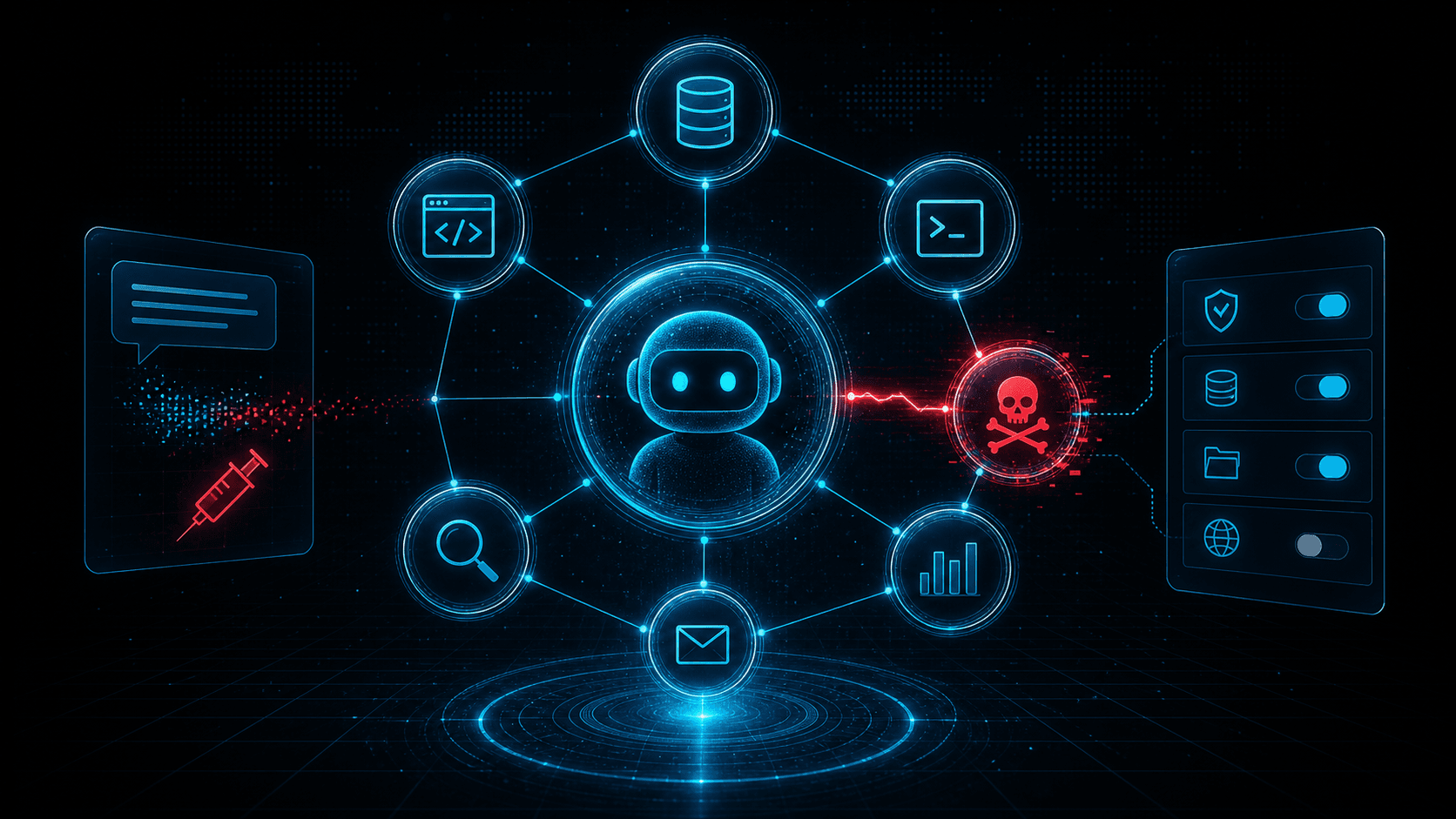 May 9, 2026MCP Security Risks: Tool Poisoning, Prompt Injection, and the New AI Agent Attack Surface
May 9, 2026MCP Security Risks: Tool Poisoning, Prompt Injection, and the New AI Agent Attack SurfaceModel Context Protocol integrations give agents access to tools, files, and services. That power creates new risks: tool poisoning, prompt injection, overbroad permissions, and untrusted server abuse.
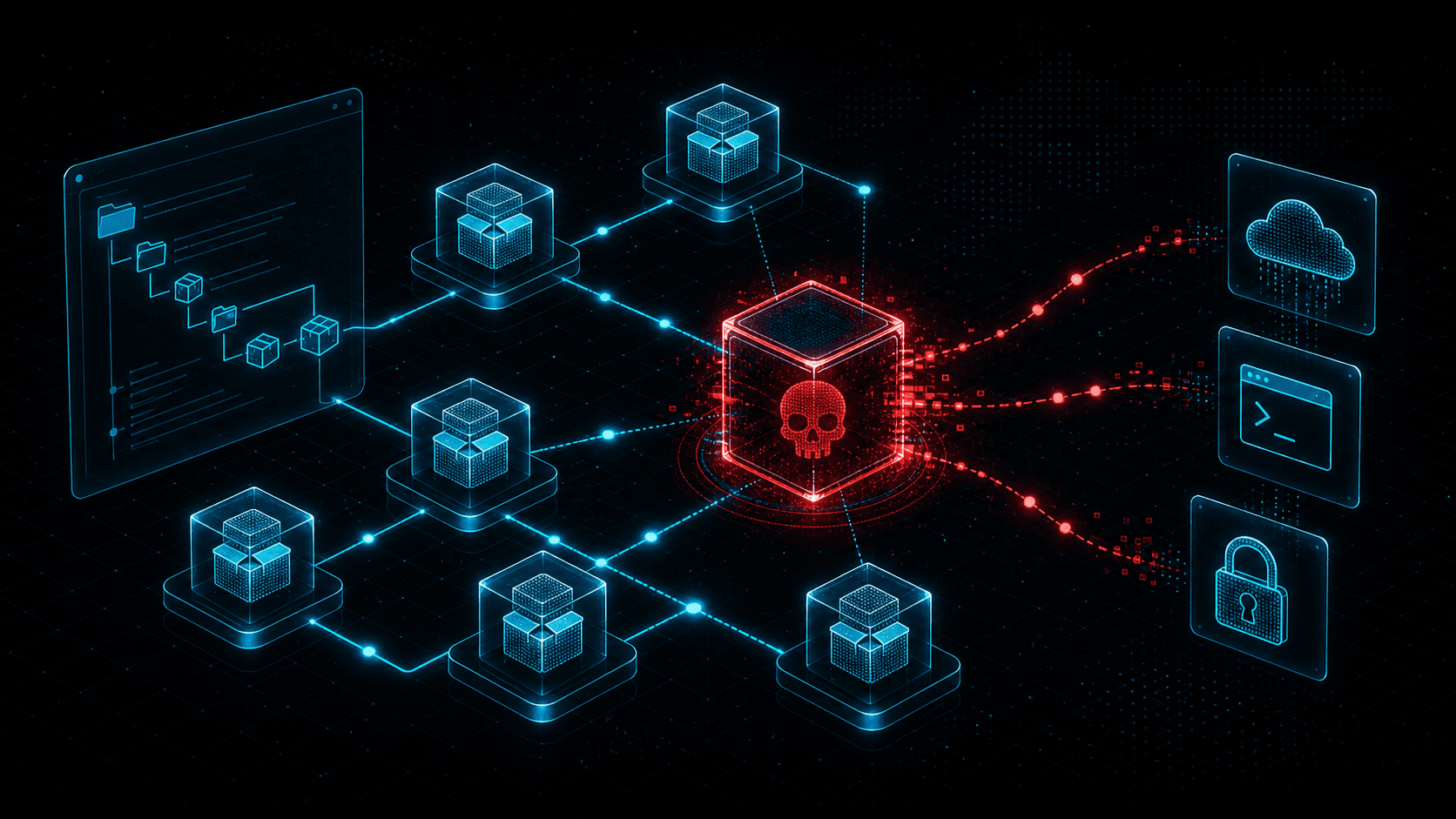 May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain Compromise
May 3, 2026Malicious npm Packages: Detecting Open-Source Supply Chain CompromiseMalicious npm packages use typosquatting, dependency confusion, install scripts, and maintainer compromise to steal secrets and backdoor builds. Learn practical detection and response.
 Apr 25, 2026Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability Disclosure
Apr 25, 2026Supply Chain CVE Response: SBOMs, Dependency Risk, and Coordinated Vulnerability DisclosureBuild a modern supply-chain security program: generate SBOMs, map CVEs to components, integrate EPSS and KEV, and coordinate fixes across vendors and open-source maintainers.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker