Ransomware Resilience: Why Immutable Backups Still Matter in 2026
Attackers target backups first. Learn how immutable storage, the 3-2-1 rule, and recovery drills turn ransomware from a business-ending event into a manageable incident.
Ransomware operators no longer stop at encrypting file shares. They hunt for backup consoles, delete snapshots, and abuse privileged accounts to make recovery impossible. Resilience is not about whether you will be targeted; it is about whether you can restore operations when encryption or extortion lands.
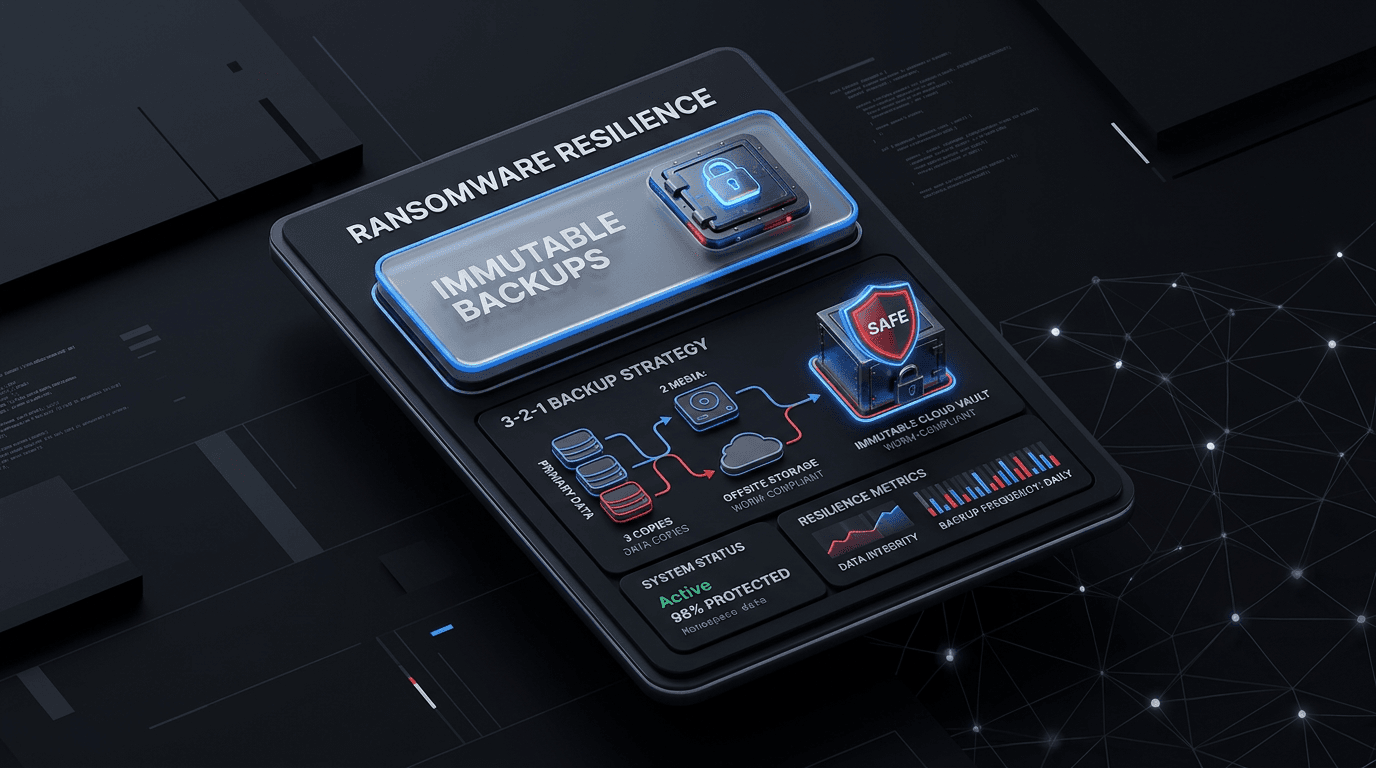
The 3-2-1 Rule (Still the Baseline)
A practical backup strategy keeps three copies of data, on two different media types, with one copy off-site or logically air-gapped. Cloud object storage, tape, or a secondary region can satisfy the off-site requirement, but the critical detail is independence: one copy must survive compromise of your primary environment and identity plane.
Immutability and WORM
Immutable or write-once storage prevents attackers (and rogue admins) from silently overwriting or deleting backups during the dwell time before ransomware detonates. Combine immutability with separate credentials and network segmentation for backup infrastructure so Domain Admin on the corporate LAN cannot reach the immutability controls.
Test Restores, Not Just Backups
Backups that have never been restored are assumptions. Schedule tabletop plus technical exercises: pick random systems, restore to an isolated network, and measure recovery time objective (RTO) and recovery point objective (RPO) against real numbers, not slide decks.
Identity Is Part of Resilience
Modern ransomware chains often start with stolen credentials or phishing. Hardening identity, MFA, and privileged access reduces the odds that an attacker ever reaches your backup tier. Resilience is backup strategy plus least privilege and detection on the path to data destruction.
Conclusion
Immutable, tested, independently secured backups are the difference between paying a ransom and declining with confidence. Invest in recovery before the ransom note appears.
Related articles
 Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply Chain
Apr 24, 2026Initial Access Brokers and Ransomware: Mapping Attack Vectors Across the Cybercrime Supply ChainUnderstand how access brokers monetize footholds, how ransomware affiliates purchase them, and which defensive controls break the supply chain—from phishing to exposed services.
 Apr 11, 2026Ransomware et double extorsion : stratégie de défense
Apr 11, 2026Ransomware et double extorsion : stratégie de défenseChiffrement plus fuite de données : la double extorsion a changé la donne pour les sauvegardes et la communication de crise. Principes de résilience, négociation et préparation réglementaire.
 Oct 3, 2025Ransomware Detection and Prevention: A Comprehensive Defense Strategy
Oct 3, 2025Ransomware Detection and Prevention: A Comprehensive Defense StrategyLearn how to detect ransomware threats before they encrypt your data. Explore proven prevention techniques, early warning signs, and how threat intelligence can protect your organization from costly ransomware attacks.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker