Understanding Threat Classification: A Guide for Modern SOCs
 IsMalicious Team
IsMalicious Team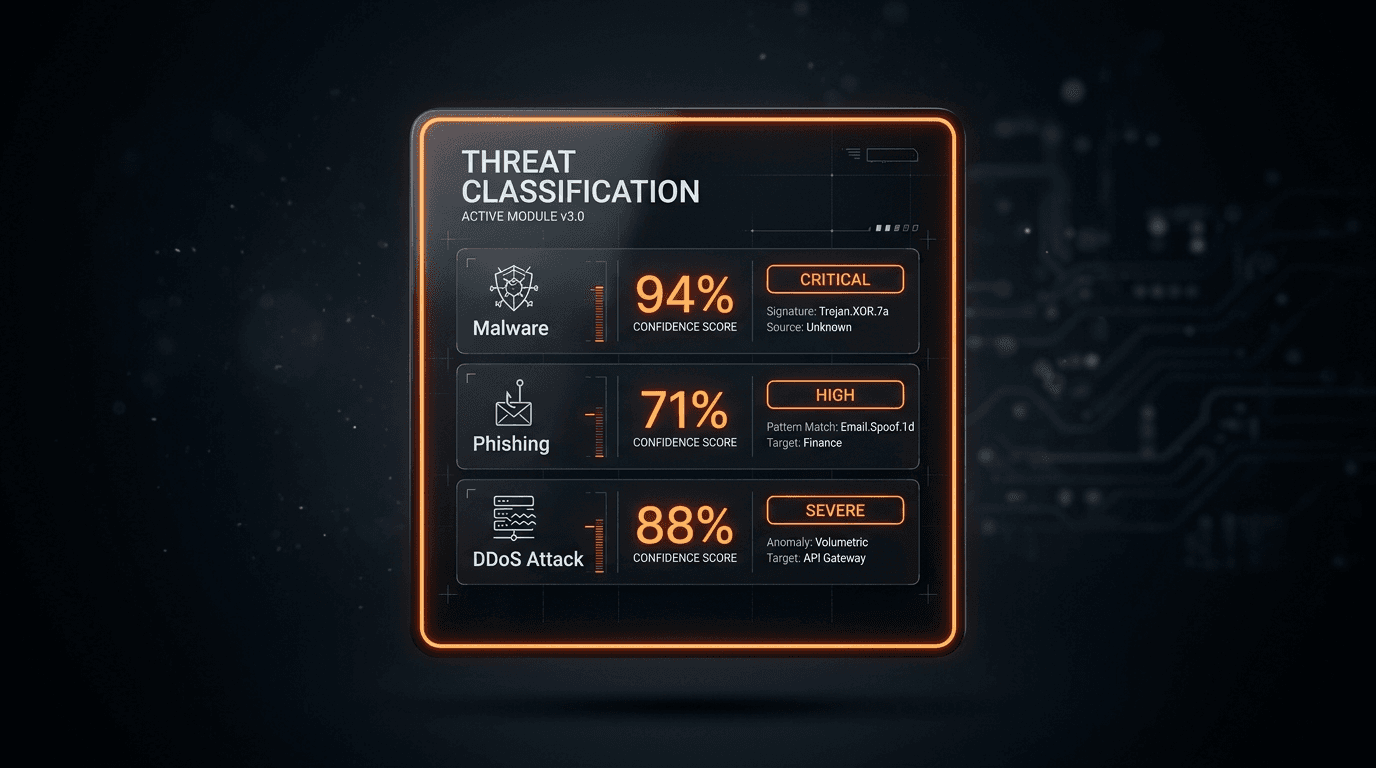
In the chaotic environment of a Security Operations Center (SOC), the ability to quickly identify and categorize threats is paramount. Threat classification is not just about labeling; it's about understanding the nature, severity, and potential impact of an incident to prioritize response efforts effectively.
The Importance of Classification
Without a robust classification system, analysts are often overwhelmed by a flood of alerts. Is that traffic spike a DDoS attack, or just a viral marketing campaign? Is that suspicious email a generic phishing attempt, or a targeted spear-phishing operation?
Proper classification allows for:
- Prioritized Response: Critical threats get immediate attention.
- Automated Playbooks: Specific threat types trigger pre-defined remediation steps.
- Better Reporting: Metrics on threat types help justify security investments.
Key Threat Categories
While taxonomies vary, most modern frameworks include these core categories:
1. Malware
Malicious software designed to disrupt, damage, or gain unauthorized access.
- Ransomware: Encrypts data for extortion.
- Trojans: Disguises as legitimate software.
- Spyware: Steals sensitive information.
2. Network Attacks
Attempts to exploit network vulnerabilities or overwhelm resources.
- DDoS (Distributed Denial of Service): Flooding a target with traffic.
- Man-in-the-Middle (MitM): Intercepting communications.
- SQL Injection: Exploiting database vulnerabilities.
3. Social Engineering
Manipulating individuals into divulging confidential information.
- Phishing: Deceptive emails.
- Pretexting: Creating a fabricated scenario.
Implementing a Classification Framework
To implement effective threat classification, organizations should adopt industry standards like the MITRE ATT&CK framework or the Cyber Kill Chain. These frameworks provide a common language for describing threat behaviors and help in mapping defenses against specific tactics and techniques.
Conclusion
Threat classification is a continuous process. As attackers evolve, so must our definitions and detection logic. By maintaining a dynamic and structured classification system, SOCs can turn chaos into order and respond to threats with precision.
Related articles
 Sep 15, 2025Building a Modern SOC with Threat Intelligence: A Practical Guide
Sep 15, 2025Building a Modern SOC with Threat Intelligence: A Practical GuideLearn how to build an effective Security Operations Center (SOC) powered by threat intelligence. Discover essential tools, processes, and best practices for detecting, analyzing, and responding to cyber threats in real-time.
 Apr 23, 2026OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat Intelligence
Apr 23, 2026OSINT for SOC Analysts: Turning Open Source Intelligence Into Actionable Threat IntelligenceA complete guide to open source intelligence (OSINT) for security operations—tools, techniques, workflows, and legal considerations for collecting, analyzing, and operationalizing open threat data in a modern SOC.
 Feb 28, 2026Building a Custom SOC Dashboard: Integrating Real-Time Threat Feeds
Feb 28, 2026Building a Custom SOC Dashboard: Integrating Real-Time Threat FeedsEnhance your Security Operations Center visibility. A step-by-step guide to aggregating threat data, enriching logs, and building custom security dashboards using modern Threat Intelligence APIs.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker