Mapping Your Defenses with MITRE ATT&CK
 IsMalicious Team
IsMalicious Team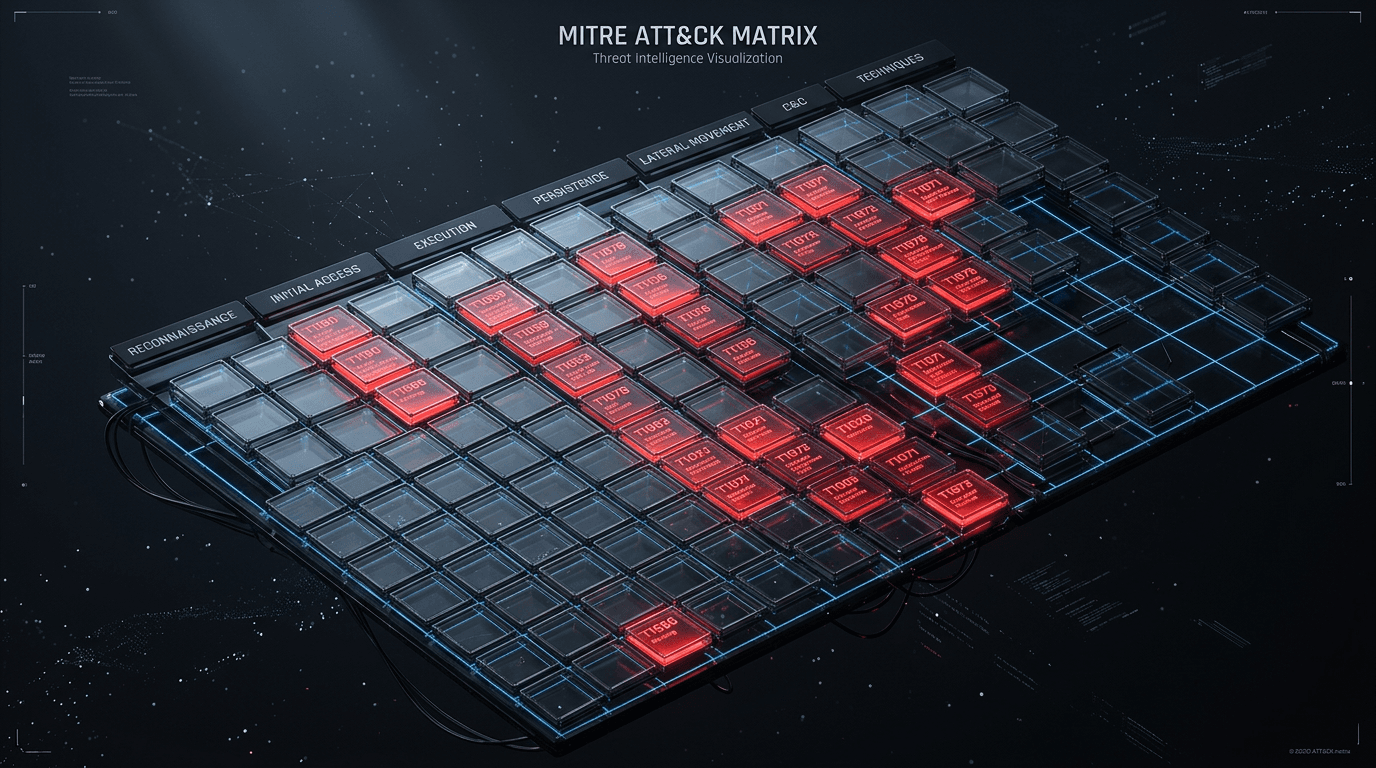
The MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) framework has revolutionized how we think about cyber defense. Instead of focusing solely on indicators of compromise (IoCs) like IP addresses and file hashes, ATT&CK focuses on behavior.
What is MITRE ATT&CK?
It is a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. The framework is organized into a matrix of Tactics (the "why" - e.g., Initial Access, Persistence) and Techniques (the "how" - e.g., Phishing, Scheduled Task).
Why Map Your Defenses?
Mapping your security controls to the ATT&CK matrix allows you to:
- Identify Gaps: Visualize where your defenses are strong and where they are non-existent.
- Test Efficacy: Run simulations (Purple Teaming) to verify if your tools actually detect specific techniques.
- Prioritize Investments: Spend budget on tools that cover the most critical or likely techniques for your industry.
Steps to Start Mapping
- Inventory Your Tools: List all security tools (EDR, Firewall, SIEM, etc.).
- Determine Coverage: For each tool, identify which ATT&CK techniques it can detect or block.
- Visualize the Matrix: Use the MITRE ATT&CK Navigator to create a heatmap of your coverage.
- Analyze and Improve: Focus on the "red" areas—techniques that are relevant to your threat landscape but are currently uncovered.
The Continuous Cycle
Adversaries are constantly updating their tradecraft. Your ATT&CK mapping is not a one-time project; it's a living document that should be updated as you deploy new tools, tune existing ones, or as new threat intelligence becomes available.
Related articles
 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
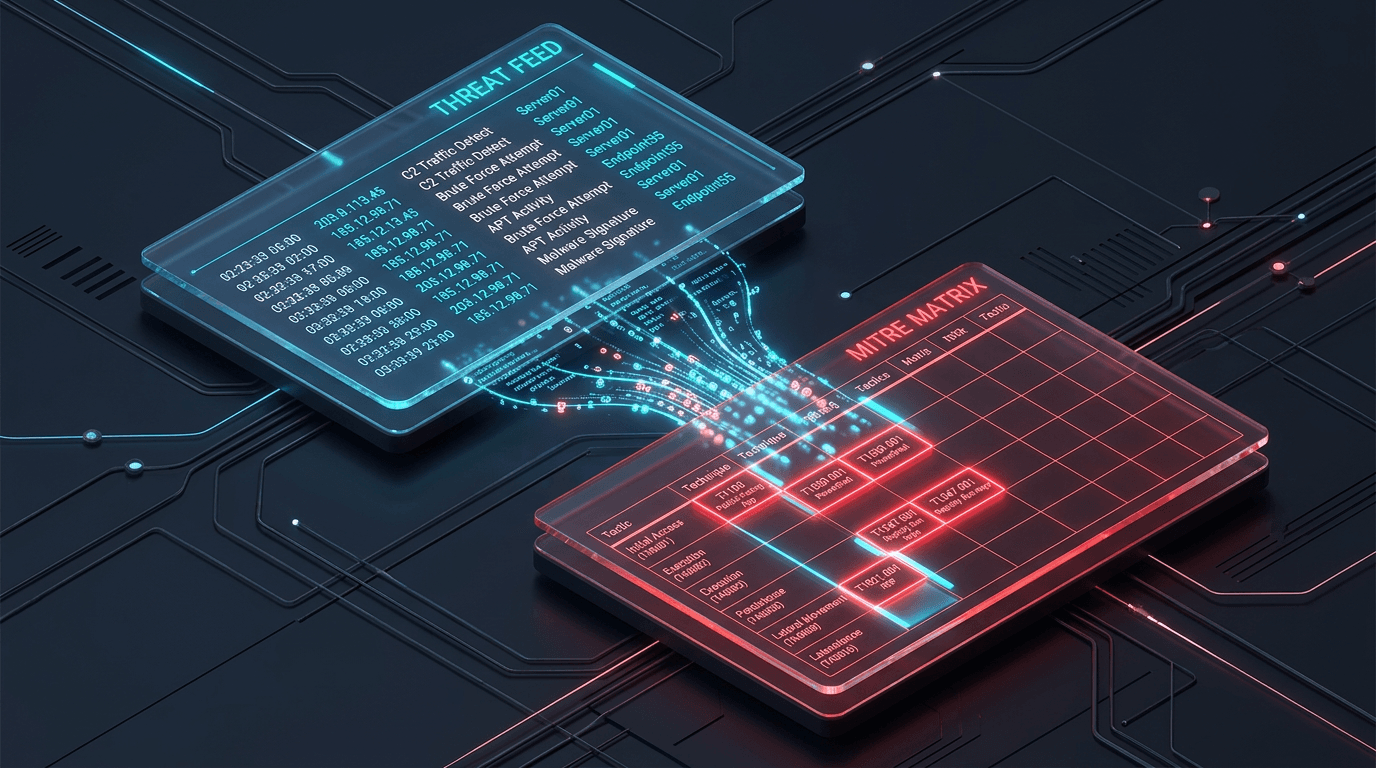 Mar 17, 2026Integrating MITRE ATT&CK with Real-Time Threat Feeds
Mar 17, 2026Integrating MITRE ATT&CK with Real-Time Threat FeedsBridge the gap between strategic frameworks and tactical defense. Learn how to map real-time threat feeds directly to the MITRE ATT&CK matrix.
 Apr 5, 2026Watering Hole Attacks: Compromising the Sites Your Victims Already Trust
Apr 5, 2026Watering Hole Attacks: Compromising the Sites Your Victims Already TrustInstead of spear-phishing individuals, APTs infect websites their targets routinely visit. Learn how watering hole campaigns work and how to harden web supply chains and detection.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker