Integrating MITRE ATT&CK with Real-Time Threat Feeds
 IsMalicious Team
IsMalicious Team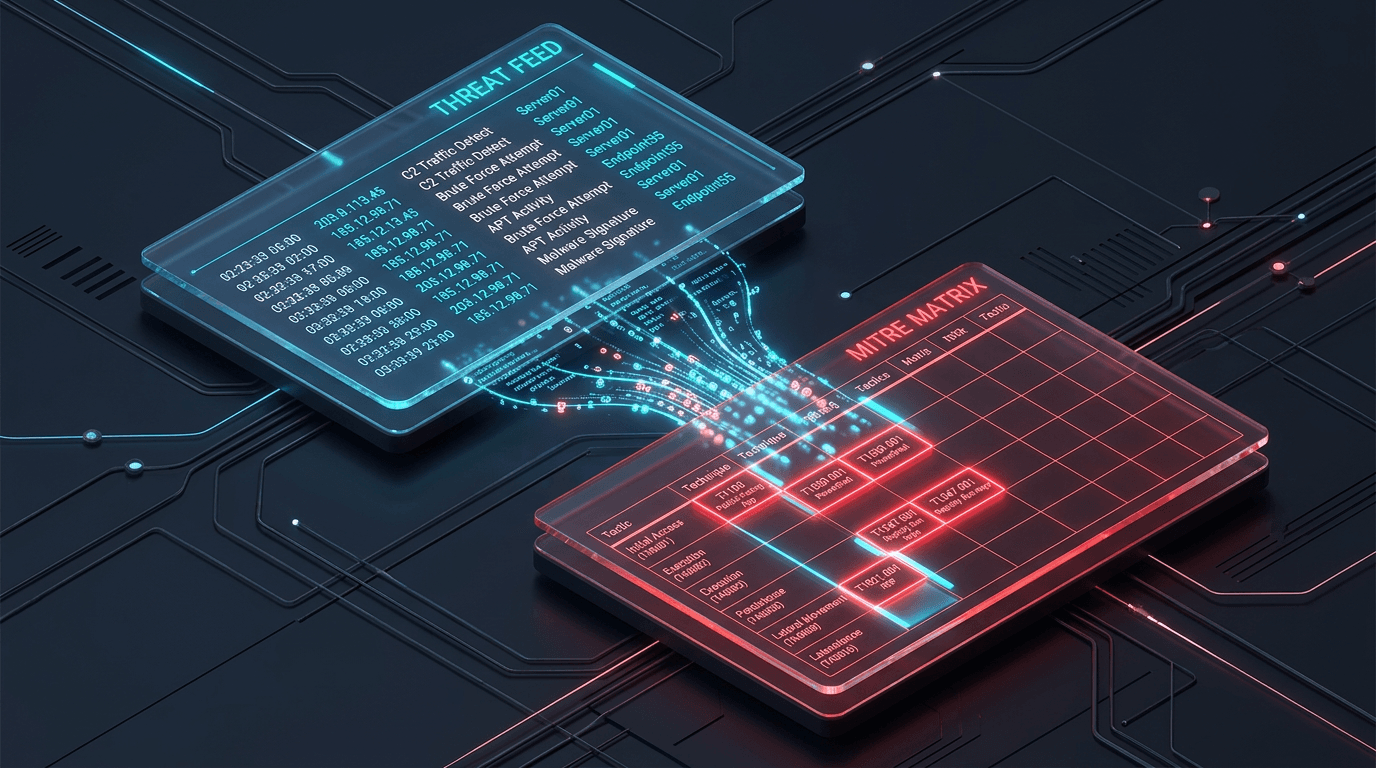
We've discussed the importance of MITRE ATT&CK for strategy and Threat Intelligence for real-time awareness. The real magic happens when you combine them.
The Disconnect
Often, threat feeds (IPs, Domains, Hashes) and the ATT&CK framework (TTPs) live in separate silos.
- Feeds are tactical and ephemeral.
- ATT&CK is strategic and behavioral.
Bridging the Gap
Integrating these two allows you to answer the question: "This specific IP address is associated with which adversary behavior?"
How it Works
- Attributed Feeds: Use threat feeds that provide attribution (e.g., "This IP is a C2 server for APT29").
- Mapping to Techniques: Since we know APT29 uses specific techniques (e.g., T1086 PowerShell), we can infer that activity from this IP might involve those techniques.
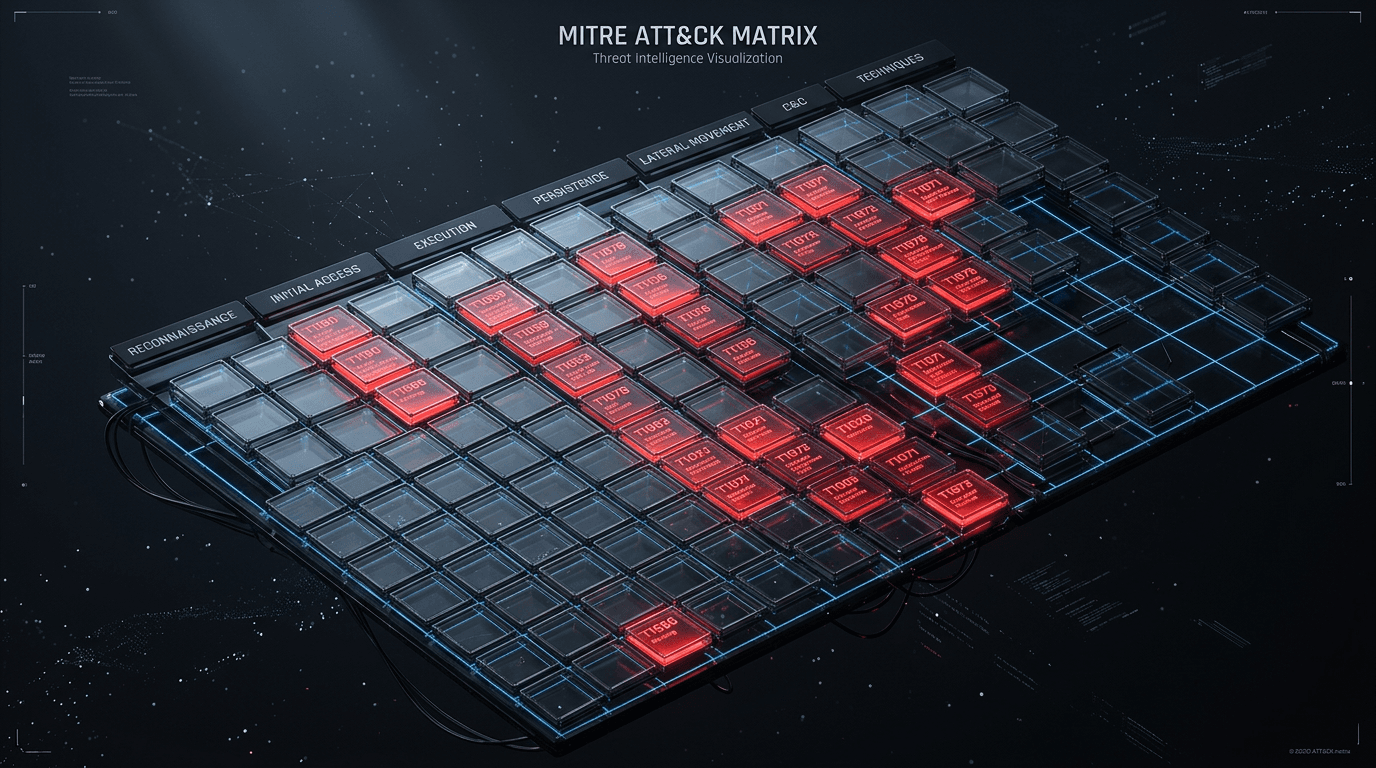
- Dynamic Defense: If a feed indicates a surge in "Credential Dumping" (T1003) across your industry, you can automatically prioritize alerts related to that technique in your SIEM.
Benefits of Integration
- Contextual Alerts: "Blocked connection to malicious IP" becomes "Blocked connection to known Ransomware group using SMB exploitation."
- Proactive Hunting: Use feed data to trigger threat hunting hypotheses based on mapped techniques.
Conclusion
By mapping real-time feeds to the MITRE ATT&CK matrix, you transform raw data into actionable behavioral intelligence, allowing your SOC to defend against the adversary, not just their infrastructure.
Related articles
 Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World Defenses
Apr 20, 2026Threat Actor Attack Vectors in 2026: Mapping TTPs to Real-World DefensesExplore how adversaries gain initial access, move laterally, and exfiltrate data—and how security teams map attack vectors to MITRE ATT&CK, detection engineering, and threat-informed defense.
 Mar 15, 2026Mapping Your Defenses with MITRE ATT&CK
Mar 15, 2026Mapping Your Defenses with MITRE ATT&CKThe MITRE ATT&CK framework is the gold standard for understanding adversary behavior. Discover how to map your defenses to specific techniques.
 Feb 28, 2026Building a Custom SOC Dashboard: Integrating Real-Time Threat Feeds
Feb 28, 2026Building a Custom SOC Dashboard: Integrating Real-Time Threat FeedsEnhance your Security Operations Center visibility. A step-by-step guide to aggregating threat data, enriching logs, and building custom security dashboards using modern Threat Intelligence APIs.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker