Detecting the Enemy Within: Behavioral Analytics for Insider Threats
 IsMalicious Team
IsMalicious Team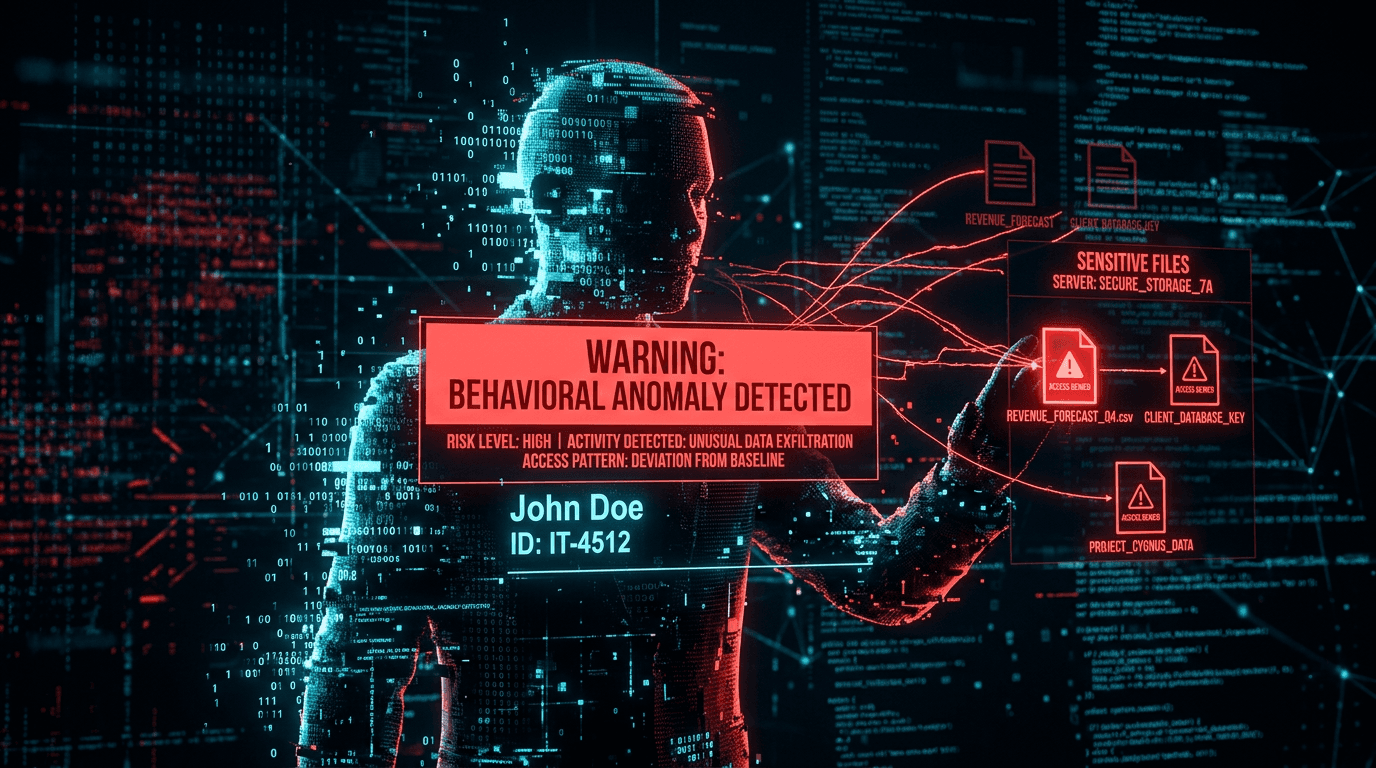
The most dangerous attacker might be sitting in the cubicle next to you. Insider threats—whether malicious employees, negligent contractors, or compromised credentials—pose a unique challenge because they bypass traditional perimeter defenses.
The Challenge of Legitimacy
Insider threats use legitimate credentials to access authorized systems. A firewall won't stop an employee from downloading a customer database they have access to every day.
Enter UEBA (User and Entity Behavior Analytics)
UEBA tools use machine learning to establish a baseline of "normal" behavior for every user and entity (device, server) in the network. When behavior deviates from this baseline, an alert is triggered.
Indicators of Compromise (IoCs) for Insiders
- Abnormal Access Times: Logging in at 3 AM when the user usually works 9-5.
- Data Exfiltration: Downloading large volumes of data to USB drives or cloud storage.
- Privilege Escalation: Attempting to access systems outside their normal job function.
- Lateral Movement: Scanning the internal network for other vulnerable systems.
The Human Element
Technology is only half the battle. A robust insider threat program also involves:
- Background Checks: Thorough vetting of employees.
- Security Awareness Training: Teaching employees to spot phishing and social engineering.
- Exit Procedures: Immediately revoking access when an employee leaves.
Conclusion
Detecting insider threats requires a shift from "signature-based" detection to "behavior-based" detection. By understanding what normal looks like, you can spot the anomaly before it becomes a breach.
Related articles
 Feb 2, 2026Insider Threat Detection: Identifying and Managing Employee Security Risks
Feb 2, 2026Insider Threat Detection: Identifying and Managing Employee Security RisksInsider threats pose unique challenges to organizational security. Learn how to detect malicious insiders, prevent data leakage, and build an effective insider threat program.
 Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network Edge
Apr 9, 2026Real-Time IP Reputation Check: Stop Cyber Threats at the Network EdgeReal-time IP reputation checks give you the power to identify and block malicious actors the moment they connect to your systems. Discover how to implement automated threat detection that works at machine speed, not analyst speed.
 Apr 5, 2026Watering Hole Attacks: Compromising the Sites Your Victims Already Trust
Apr 5, 2026Watering Hole Attacks: Compromising the Sites Your Victims Already TrustInstead of spear-phishing individuals, APTs infect websites their targets routinely visit. Learn how watering hole campaigns work and how to harden web supply chains and detection.
Protect Your Infrastructure
Check any IP or domain against our threat intelligence database with 500M+ records.
Try the IP / Domain Checker